9781285081953_PPT_ch13 - Business and Computer Science
... – Creates a file if it does not already exist – Opens the file for writing and returns an OutputStream that can be used to write bytes to the file ...
... – Creates a file if it does not already exist – Opens the file for writing and returns an OutputStream that can be used to write bytes to the file ...
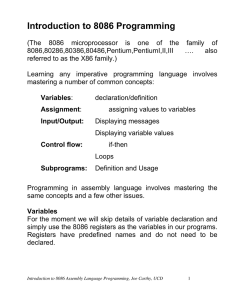
Introduction to 8086
... We are now in a position to write a complete 8086 program. You must use an editor to enter the program into a file. The process of using the editor (editing) is a basic form of word processing. This skill has no relevance to programming. We use Microsoft’s MASM and LINK programs for assembling and l ...
... We are now in a position to write a complete 8086 program. You must use an editor to enter the program into a file. The process of using the editor (editing) is a basic form of word processing. This skill has no relevance to programming. We use Microsoft’s MASM and LINK programs for assembling and l ...
Functional programming languages - Gallium
... Conversion to exception-returning style Goal: get rid of exceptions. Input: a functional language featuring exceptions (raise and try...with). Output: a functional language with pattern-matching but no exceptions. Idea: every expression a evaluates to either V (v ) if a evaluates normally or to E (v ...
... Conversion to exception-returning style Goal: get rid of exceptions. Input: a functional language featuring exceptions (raise and try...with). Output: a functional language with pattern-matching but no exceptions. Idea: every expression a evaluates to either V (v ) if a evaluates normally or to E (v ...
Functional Programming, Parametricity, Types
... theorems about this function can be reliably constructed ...
... theorems about this function can be reliably constructed ...
Chapter 12
... A border is an area that frames a component. Swing provides several different types of borders: » BevelBorder—makes component look raised or lowered » EtchedBorder—similar to BevelBorder but can’t set size » EmptyBorder—extra space around the component » LineBorder—colored border of a given thicknes ...
... A border is an area that frames a component. Swing provides several different types of borders: » BevelBorder—makes component look raised or lowered » EtchedBorder—similar to BevelBorder but can’t set size » EmptyBorder—extra space around the component » LineBorder—colored border of a given thicknes ...
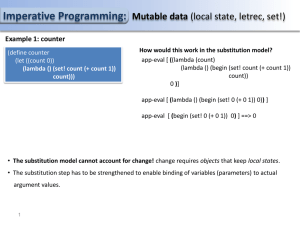
PS14
... Imperative Programming: Mutable data (local state, letrec, set!) Example 2: A chess player object: A chase player object is represent by a dispatch procedure. Based on a given message it invokes internal procedures of the object. total and steps which keep track of the player’s points and the numbe ...
... Imperative Programming: Mutable data (local state, letrec, set!) Example 2: A chess player object: A chase player object is represent by a dispatch procedure. Based on a given message it invokes internal procedures of the object. total and steps which keep track of the player’s points and the numbe ...
IMUSIC - Interdisciplinary Centre for Computer Music Research
... (Remember or Repeat), it plays the relevant riff for that command until the user has entered a second note group indicating the parameter. A Structural Riff comes from commands that would normally create indents in code. The If Equal and Repeat commands effect all following commands until an End co ...
... (Remember or Repeat), it plays the relevant riff for that command until the user has entered a second note group indicating the parameter. A Structural Riff comes from commands that would normally create indents in code. The If Equal and Repeat commands effect all following commands until an End co ...
LOGO - University of North Texas
... used to describe LOGO and LOGO-like environments. An environment for learning in which children are free to experiment, test, and revise theories, and invent their own activities. ...
... used to describe LOGO and LOGO-like environments. An environment for learning in which children are free to experiment, test, and revise theories, and invent their own activities. ...
CS 345 - Programming Languages
... • Evaluate pi in order; each pi evaluates to #t or #f • Value = value of ei for the first pi that evaluates to #t or eN if pN is “else” and all p1 … pN-1 evaluate to #f ...
... • Evaluate pi in order; each pi evaluates to #t or #f • Value = value of ei for the first pi that evaluates to #t or eN if pN is “else” and all p1 … pN-1 evaluate to #f ...
Functional programming in Scheme.
... • Evaluate pi in order; each pi evaluates to #t or #f • Value = value of ei for the first pi that evaluates to #t or eN if pN is “else” and all p1 … pN-1 evaluate to #f ...
... • Evaluate pi in order; each pi evaluates to #t or #f • Value = value of ei for the first pi that evaluates to #t or eN if pN is “else” and all p1 … pN-1 evaluate to #f ...
Evaluation of C# Language
... type system” (Hejlsberg, The A-Z of Programming Languages: C#). He claims that this system is great for teaching because everything is an object. This statement has sparked quite a heated debate in the C# developer community, as it is mostly true, but a bit misleading. The debate revolves around a s ...
... type system” (Hejlsberg, The A-Z of Programming Languages: C#). He claims that this system is great for teaching because everything is an object. This statement has sparked quite a heated debate in the C# developer community, as it is mostly true, but a bit misleading. The debate revolves around a s ...
CS 345 - Programming Languages
... code depends on object and message Fundamental difference between abstract data types and objects! slide 25 ...
... code depends on object and message Fundamental difference between abstract data types and objects! slide 25 ...
Sailing around Java: Experiences implementing SAS/IntrNet software in the global controlling arena
... By default SCL entries which are executed on the application Dispatcher are loaded to the cache of the server the first time they are executed. Therefore they will not be loaded again from disk on subsequent calls. After the first execution of an SCL entry, the catalog it resides in is blocked and c ...
... By default SCL entries which are executed on the application Dispatcher are loaded to the cache of the server the first time they are executed. Therefore they will not be loaded again from disk on subsequent calls. After the first execution of an SCL entry, the catalog it resides in is blocked and c ...
Project Five
... developed for use exclusively on systems with specific hardware configurations, but later were developed for use on a multitude of platforms. These languages were considered Imperative languages, which are designed for sequential execution so no parallel computations were done in these early languag ...
... developed for use exclusively on systems with specific hardware configurations, but later were developed for use on a multitude of platforms. These languages were considered Imperative languages, which are designed for sequential execution so no parallel computations were done in these early languag ...
An Introduction to Control Structures
... Programming I/O • In stream I/O, characters or bytes are read or ...
... Programming I/O • In stream I/O, characters or bytes are read or ...
COMS W1004 Introduction to Computer Science
... LC-3 Instruction Set Architecture (Chp. 4) • Instruction format – Opcode – Operands ...
... LC-3 Instruction Set Architecture (Chp. 4) • Instruction format – Opcode – Operands ...
Lecture slides for Chapter 9
... • Symbolic data – Lists of symbols called atoms – List is ONLY data structure in LISP ...
... • Symbolic data – Lists of symbols called atoms – List is ONLY data structure in LISP ...
Week6 - School of Computing
... E.g.: When you discover a better algorithm for isPrime(int), you just replace that method without affecting any other parts of the program or other programs. ...
... E.g.: When you discover a better algorithm for isPrime(int), you just replace that method without affecting any other parts of the program or other programs. ...
Arrays - CIS @ Temple University
... ISBN 0132162709 © 2012 Pearson Education, Inc., Upper Saddle River, NJ. All Rights Reserved ...
... ISBN 0132162709 © 2012 Pearson Education, Inc., Upper Saddle River, NJ. All Rights Reserved ...
CS Courses from Catalog - Academic Departments for Students
... programming from an object-oriented perspective. Through the study of object design, this course also introduces the basics of human-computer interfaces, graphics, with an emphasis on software engineering. A second operating system/programming platform is introduced. CS 04115: C++ For Java Programme ...
... programming from an object-oriented perspective. Through the study of object design, this course also introduces the basics of human-computer interfaces, graphics, with an emphasis on software engineering. A second operating system/programming platform is introduced. CS 04115: C++ For Java Programme ...
ch12
... If you declare an exception using the class Exception in the heading of a catch block, then that catch block can catch all types of exceptions because the class Exception is the superclass of all exception classes In a sequence of catch blocks following a try block, a catch block that declares a ...
... If you declare an exception using the class Exception in the heading of a catch block, then that catch block can catch all types of exceptions because the class Exception is the superclass of all exception classes In a sequence of catch blocks following a try block, a catch block that declares a ...
Lec. 01: Java Fundamentals
... different point in the program. Using transfer is considered as a poor programming style and makes the code maintenance difficult. Java only supports the forward transfer, which transfer the execution point to a point beyond the current execution point. ...
... different point in the program. Using transfer is considered as a poor programming style and makes the code maintenance difficult. Java only supports the forward transfer, which transfer the execution point to a point beyond the current execution point. ...
Kennesaw State University: AP Computer Science A
... IV. A. Simple data types. IV. B. Classes. III. A. 2. Testing; identify boundary cases, generate appropriate test data. III. A. 3. Testing: perform integration testing. III. C. Understand and modify existing code. I. B. 3. Class design; choose appropriate data representation and algorithms. II. B. 4. ...
... IV. A. Simple data types. IV. B. Classes. III. A. 2. Testing; identify boundary cases, generate appropriate test data. III. A. 3. Testing: perform integration testing. III. C. Understand and modify existing code. I. B. 3. Class design; choose appropriate data representation and algorithms. II. B. 4. ...
Functional programming - University of Cape Town
... want, not the means to calculate it (as in imperative programming) Applicative languages are thought to be easier to use, so most 4GL’s are built in this way The proponents of FL’s say they represent the highest level programming available University of Cape Town ...
... want, not the means to calculate it (as in imperative programming) Applicative languages are thought to be easier to use, so most 4GL’s are built in this way The proponents of FL’s say they represent the highest level programming available University of Cape Town ...