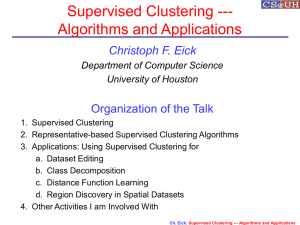
Nearest Neighbour - Department of Computer Science
... • Surprisingly, many UCI datasets can be compressed by just using a single representative per class without a significant loss in accuracy. • SCE tends to pick representatives that are in the center of a region that is dominated by a single class; it removes examples that are classified correctly as ...
... • Surprisingly, many UCI datasets can be compressed by just using a single representative per class without a significant loss in accuracy. • SCE tends to pick representatives that are in the center of a region that is dominated by a single class; it removes examples that are classified correctly as ...
978-1-59994-827-0 Getting Started with SAS® Enterprise Miner™ 5.3
... After you have completed the assessment phase of the SEMMA process, you apply the scoring formula from one or more champion models to new data that might or might not contain the target. The goal of most data mining tasks is to apply models that are constructed using training and validation data in ...
... After you have completed the assessment phase of the SEMMA process, you apply the scoring formula from one or more champion models to new data that might or might not contain the target. The goal of most data mining tasks is to apply models that are constructed using training and validation data in ...
Patterns Relevant to the Temporal Data-Context
... and complexity of data (typically collected from more than one database) have made the analysis and decomposition a very laborious task. It is possible to identify frequent patterns on the basis of event changes over time by using temporal windows. However, a typical chemical alarm database is chara ...
... and complexity of data (typically collected from more than one database) have made the analysis and decomposition a very laborious task. It is possible to identify frequent patterns on the basis of event changes over time by using temporal windows. However, a typical chemical alarm database is chara ...
Genetic and Evolutionary Computation Conference 2008
... Dr. Maarten Keijzer to thank for ensuring that everyone stuck with their deadlines. The third, and most important part of GECCO’s success is its attendees. A conference can only be as good as those attending it, and GECCO has been fortunate enough to attract a wonderful mix of innovation, curiosity ...
... Dr. Maarten Keijzer to thank for ensuring that everyone stuck with their deadlines. The third, and most important part of GECCO’s success is its attendees. A conference can only be as good as those attending it, and GECCO has been fortunate enough to attract a wonderful mix of innovation, curiosity ...
Flexible Fault Tolerant Subspace Clustering for Data with Missing
... groups of similar objects while separating dissimilar ones. However, as applications provide more and more attributes, meaningful clusters are hidden in projections of the data that use only subsets of the given attributes. This challenge for cluster detection is tackled by a recent paradigm: Subspa ...
... groups of similar objects while separating dissimilar ones. However, as applications provide more and more attributes, meaningful clusters are hidden in projections of the data that use only subsets of the given attributes. This challenge for cluster detection is tackled by a recent paradigm: Subspa ...
Data mining pilot – evaluation report
... testing of the databases and processes. Data mining would require a central organisation to be responsible for managing the connection between national data holding organisations and undertaking data processing work. Cabinet Office undertook this role for this pilot. The need for a central coordinat ...
... testing of the databases and processes. Data mining would require a central organisation to be responsible for managing the connection between national data holding organisations and undertaking data processing work. Cabinet Office undertook this role for this pilot. The need for a central coordinat ...
Similarity Processing in Multi-Observation Data
... of search and mining tasks resulting in a significant efficiency gain. As feature vectors are potentially of high dimensionality, this part introduces indexing approaches for the high-dimensional space for the full-dimensional case as well as for arbitrary subspaces. The second part of this thesis f ...
... of search and mining tasks resulting in a significant efficiency gain. As feature vectors are potentially of high dimensionality, this part introduces indexing approaches for the high-dimensional space for the full-dimensional case as well as for arbitrary subspaces. The second part of this thesis f ...
A Comparison of Educational Statistics and Data Mining
... In the last 20 years, there has been an explosion of online instructional material of various forms—from simple passive content in the form of web pages to sophisticated learning objects (LOs) that integrate interactive instruction, practice exercises and assessment components that promote active le ...
... In the last 20 years, there has been an explosion of online instructional material of various forms—from simple passive content in the form of web pages to sophisticated learning objects (LOs) that integrate interactive instruction, practice exercises and assessment components that promote active le ...
Frequent Closed Sequence Mining without Candidate
... Jianyong Wang, Senior Member, IEEE, Jiawei Han, Senior Member, IEEE, and Chun Li Abstract—Previous studies have presented convincing arguments that a frequent pattern mining algorithm should not mine all frequent patterns but only the closed ones because the latter leads to not only a more compact y ...
... Jianyong Wang, Senior Member, IEEE, Jiawei Han, Senior Member, IEEE, and Chun Li Abstract—Previous studies have presented convincing arguments that a frequent pattern mining algorithm should not mine all frequent patterns but only the closed ones because the latter leads to not only a more compact y ...
distributed incremental data stream mining for wireless sensor
... FWI SYSTEM........................................................................................................................... 138 ...
... FWI SYSTEM........................................................................................................................... 138 ...
A 1 - DidaWiki
... An itemset X is closed if X is frequent and there exists no super-pattern Y כX, with the same support as X (proposed by Pasquier, et al. @ ICDT’99) An itemset X is a max-pattern if X is frequent and there exists no frequent super-pattern Y כX (proposed by ...
... An itemset X is closed if X is frequent and there exists no super-pattern Y כX, with the same support as X (proposed by Pasquier, et al. @ ICDT’99) An itemset X is a max-pattern if X is frequent and there exists no frequent super-pattern Y כX (proposed by ...
A Systematic Approach for Optimizing Complex Mining Tasks on
... . Furthermore, as the number of datasets and the complexity of the query condition increases, the number of possible evaluation plans can also grow. Thus, there is a need for techniques for enumerating different query plans and choosing the one with the least cost, similar to what have been develope ...
... . Furthermore, as the number of datasets and the complexity of the query condition increases, the number of possible evaluation plans can also grow. Thus, there is a need for techniques for enumerating different query plans and choosing the one with the least cost, similar to what have been develope ...
Predictive Analytics: The Hurwitz Victory Index Report
... As end users grow to understand the value of predictive analytics, the market itself is evolving to include solutions targeted at different kinds of users and to deal with more data, and different deployment models. Hurwitz & Associates sees the following trends in the predictive analytics market: • ...
... As end users grow to understand the value of predictive analytics, the market itself is evolving to include solutions targeted at different kinds of users and to deal with more data, and different deployment models. Hurwitz & Associates sees the following trends in the predictive analytics market: • ...
knowledge discovery in a service-oriented data mining - SLAIS
... The term data mining denotes the activity of extracting new, valuable and nontrivial information from large volumes of data (Cios et al., 2010; Fayyad et al., 1996). Most commonly, the aim is to find patterns or build models using specific algorithms from various scientific disciplines including art ...
... The term data mining denotes the activity of extracting new, valuable and nontrivial information from large volumes of data (Cios et al., 2010; Fayyad et al., 1996). Most commonly, the aim is to find patterns or build models using specific algorithms from various scientific disciplines including art ...
Redescription Mining Over non-Binary Data Sets Using Decision
... Beside this, redescription mining using decision trees with a modification such that it can work with numerical entries (at least on the one side) might perform well and become a competitive alternative to aforementioned techniques. However, it is not implemented so far. Thus, this is a starting poi ...
... Beside this, redescription mining using decision trees with a modification such that it can work with numerical entries (at least on the one side) might perform well and become a competitive alternative to aforementioned techniques. However, it is not implemented so far. Thus, this is a starting poi ...
- D-Scholarship@Pitt
... An important goal of knowledge discovery is the search for patterns in the data that can help explaining its underlying structure. To be practically useful, the discovered patterns should be novel (unexpected) and easy to understand by humans. In this thesis, we study the problem of mining patterns ...
... An important goal of knowledge discovery is the search for patterns in the data that can help explaining its underlying structure. To be practically useful, the discovered patterns should be novel (unexpected) and easy to understand by humans. In this thesis, we study the problem of mining patterns ...
Nonlinear dimensionality reduction

High-dimensional data, meaning data that requires more than two or three dimensions to represent, can be difficult to interpret. One approach to simplification is to assume that the data of interest lie on an embedded non-linear manifold within the higher-dimensional space. If the manifold is of low enough dimension, the data can be visualised in the low-dimensional space.Below is a summary of some of the important algorithms from the history of manifold learning and nonlinear dimensionality reduction (NLDR). Many of these non-linear dimensionality reduction methods are related to the linear methods listed below. Non-linear methods can be broadly classified into two groups: those that provide a mapping (either from the high-dimensional space to the low-dimensional embedding or vice versa), and those that just give a visualisation. In the context of machine learning, mapping methods may be viewed as a preliminary feature extraction step, after which pattern recognition algorithms are applied. Typically those that just give a visualisation are based on proximity data – that is, distance measurements.