Database Users and Administrators
... Pascal etc. These queries are converted into object code to communicate with the database. For example, writing a C program to generate the report of employees who are working in particular department will involve a query to fetch the data from database. It will include a embedded SQL query in the C ...
... Pascal etc. These queries are converted into object code to communicate with the database. For example, writing a C program to generate the report of employees who are working in particular department will involve a query to fetch the data from database. It will include a embedded SQL query in the C ...
(Spatial Association Rule Mining) for Geo
... spatial association the same records are required to be scanned again and again to find out the frequent sets. This becomes cumbersome, as spatial data is already known to be large in size. As far as sparse data is concerned, an Apriori based spatial association rule may even be considered but when ...
... spatial association the same records are required to be scanned again and again to find out the frequent sets. This becomes cumbersome, as spatial data is already known to be large in size. As far as sparse data is concerned, an Apriori based spatial association rule may even be considered but when ...
Distributed Databases
... Starting the execution of transactions that originate at the site. Distributing subtransactions at appropriate sites for execution. Coordinating the termination of each transaction that originates at the site, which may result in the transaction being committed at all sites or aborted at all sites. ...
... Starting the execution of transactions that originate at the site. Distributing subtransactions at appropriate sites for execution. Coordinating the termination of each transaction that originates at the site, which may result in the transaction being committed at all sites or aborted at all sites. ...
Lock
... Also known as Access control This is the granting of rights and privileges that enables a user to have access to the system ...
... Also known as Access control This is the granting of rights and privileges that enables a user to have access to the system ...
Views-basics
... users and user programs are immune to changes in the logical structure of the DB to what extent logical data independence can be guaranteed? ...
... users and user programs are immune to changes in the logical structure of the DB to what extent logical data independence can be guaranteed? ...
Cloud Computing
... are related for sure but they should not be confused for being the same thing. In actual fact, they are not really competing with each other. There are some unique requirements of applications when they do not call for any advance query techniques but rather need fast access to database. In such sce ...
... are related for sure but they should not be confused for being the same thing. In actual fact, they are not really competing with each other. There are some unique requirements of applications when they do not call for any advance query techniques but rather need fast access to database. In such sce ...
Data Clustering for Forecasting - MIT Center for Digital Business
... grades: “what really is the difference between a B+ and an A- ? (useful in evaluations) – When we figure out what to do, we often prioritize by clustering things (important vs. non-important) – We cluster people into multiple dimensions based on appearance, intelligence, character, religion, sexual ...
... grades: “what really is the difference between a B+ and an A- ? (useful in evaluations) – When we figure out what to do, we often prioritize by clustering things (important vs. non-important) – We cluster people into multiple dimensions based on appearance, intelligence, character, religion, sexual ...
An Update on SAS Software and ODBC
... of accessing information from a variety of data sources. ODBC allows applications to access different database file types whose drivers are installed on your machine. Your system comes configured with several standard ODBC drivers. Users can add addition drivers as needed. WHERE ITS AT - ODBC The go ...
... of accessing information from a variety of data sources. ODBC allows applications to access different database file types whose drivers are installed on your machine. Your system comes configured with several standard ODBC drivers. Users can add addition drivers as needed. WHERE ITS AT - ODBC The go ...
PPT - MIT
... only the data that is intended to be exposed. – TCPA is designed so that platform identities and Integrity Metrics can be proven reliably to previously unknown parties. – Secure online discovery of platforms and services: confidence in the information about the software environment and identity of a ...
... only the data that is intended to be exposed. – TCPA is designed so that platform identities and Integrity Metrics can be proven reliably to previously unknown parties. – Secure online discovery of platforms and services: confidence in the information about the software environment and identity of a ...
Symfony2 Tutorial
... associated views and controllers, so that the views can produce updated output, and the controllers to change the available set of commands A view requests from the model information needed to generate an output representation ...
... associated views and controllers, so that the views can produce updated output, and the controllers to change the available set of commands A view requests from the model information needed to generate an output representation ...
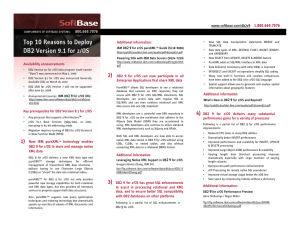
Top 10 Reasons to Deploy DB2 Version 9.1 for z/OS
... management of hierarchical XML data structures without having to use Character Large Objects (CLOBs) or “shred” the data into relational tables. pureXMLTM for DB2 9 for z/OS not only provides powerful new storage capabilities for both relational and XML data types, but also provides all necessary se ...
... management of hierarchical XML data structures without having to use Character Large Objects (CLOBs) or “shred” the data into relational tables. pureXMLTM for DB2 9 for z/OS not only provides powerful new storage capabilities for both relational and XML data types, but also provides all necessary se ...
Receiver mobility
... ignore network topology and requester/data location Firewalls, NATs, proxy servers ISPs: costly (Deep Packet Inspection-DPI) to find type of information ...
... ignore network topology and requester/data location Firewalls, NATs, proxy servers ISPs: costly (Deep Packet Inspection-DPI) to find type of information ...
Question 3: How is the concept of functional
... - Using Functional dependencies, we can define several normal forms that represent “good” database design, and as we know process of putting a database design into normal forms is nothing but normalization. www.geocities.com/ignoumcahelp - Thus, Functional dependency is a central concept of the norm ...
... - Using Functional dependencies, we can define several normal forms that represent “good” database design, and as we know process of putting a database design into normal forms is nothing but normalization. www.geocities.com/ignoumcahelp - Thus, Functional dependency is a central concept of the norm ...
Xml and Relational Databases
... An XML document is well formed if it is syntactically correct. ...
... An XML document is well formed if it is syntactically correct. ...
Chapter 5 Relational Algebra
... In most systems a natural join will require that the attributes have the same name to identify the attribute(s) to be used in the join. This may require a renaming mechanism. If you do use natural joins make sure that the relations do not have two attributes with the same name by accident. ...
... In most systems a natural join will require that the attributes have the same name to identify the attribute(s) to be used in the join. This may require a renaming mechanism. If you do use natural joins make sure that the relations do not have two attributes with the same name by accident. ...
PHP Get,Post,Session
... • PHP provides a large number of predefined variables to any script which it runs. PHP provides an additional set of predefined arrays containing variables from the web server the environment, and user input. • We can access predefined variables in any scope - any if block, any for block. It means e ...
... • PHP provides a large number of predefined variables to any script which it runs. PHP provides an additional set of predefined arrays containing variables from the web server the environment, and user input. • We can access predefined variables in any scope - any if block, any for block. It means e ...
slides - Bio-Ontologies 2017
... of a particular domain of knowledge (e.g. the GO ontology about genes and gene products) – written in a high level ontology language such as OWL (W3C’s Web Ontology Language), which is itself expressed as a set of RDF statements ...
... of a particular domain of knowledge (e.g. the GO ontology about genes and gene products) – written in a high level ontology language such as OWL (W3C’s Web Ontology Language), which is itself expressed as a set of RDF statements ...
XML-OLAP: A Multidimensional Analysis
... for decision-making [11]. It provides an analysis from multiple perspectives or dimensions for a large amount of data residing in a data warehouse. Data warehouses are commonly organized with one large fact table and multiple small dimension tables. The fact and dimension tables are typically the st ...
... for decision-making [11]. It provides an analysis from multiple perspectives or dimensions for a large amount of data residing in a data warehouse. Data warehouses are commonly organized with one large fact table and multiple small dimension tables. The fact and dimension tables are typically the st ...
A Robust System Architecture for Mining Semi
... are considered unstructured components of the document, e.g. abstract, headings, and paragraphs. We define an unstructured concept to be any meaningful word, phrase, acronym, or name extracted from these unstructured blocks of text. Many types of rules can be created using semistructured data. To da ...
... are considered unstructured components of the document, e.g. abstract, headings, and paragraphs. We define an unstructured concept to be any meaningful word, phrase, acronym, or name extracted from these unstructured blocks of text. Many types of rules can be created using semistructured data. To da ...
model-based engineering for laser weapons
... We are currently in the midst of project to extend a commercial multi-physics simulation software framework to support model-based engineering (MBE) of laser weapons systems. MBE has been identified by the National Defense Industry Association (NDIA) [Bergenthal 2011] and by the Office of the Direct ...
... We are currently in the midst of project to extend a commercial multi-physics simulation software framework to support model-based engineering (MBE) of laser weapons systems. MBE has been identified by the National Defense Industry Association (NDIA) [Bergenthal 2011] and by the Office of the Direct ...
Protect your SQL Server database
... Combining the performance of local and remote snapshots with the protection of backups, RMC for SQL Server enables fast, efficient, reliable, and simple protection of Microsoft® SQL Server databases and instances on HPE 3PAR StoreServ and Express Protect backups of SQL Server data volumes on HPE Sto ...
... Combining the performance of local and remote snapshots with the protection of backups, RMC for SQL Server enables fast, efficient, reliable, and simple protection of Microsoft® SQL Server databases and instances on HPE 3PAR StoreServ and Express Protect backups of SQL Server data volumes on HPE Sto ...
Module 1 – Background - Dalhousie University
... match a candidate key value of some tuple in its home relation or the foreign key value must be wholly null ...
... match a candidate key value of some tuple in its home relation or the foreign key value must be wholly null ...
MIS2502: Data Analytics SQL – Putting Information Into a Database
... The database management system stores this information about the table It’s separate from the data in the table (i.e., Customer information) ...
... The database management system stores this information about the table It’s separate from the data in the table (i.e., Customer information) ...
REACH – Annex III
... meet the criterion b(ii), above; that is, it is predicted to be hazardous. The list does not take into account dispersive or diffuse use (this will depend on the particular supply chain). Therefore, the Annex III inventory is essentially a list of potentially hazardous substances. If a substance is ...
... meet the criterion b(ii), above; that is, it is predicted to be hazardous. The list does not take into account dispersive or diffuse use (this will depend on the particular supply chain). Therefore, the Annex III inventory is essentially a list of potentially hazardous substances. If a substance is ...