Integrated Modeling Systems - UCLA Anderson School of
... model class (perhaps with minor revisions of the model class in some cases), the second example results in a new specific model within a new model class that is essentially a cross of the original model class with itself. Examples of the first general type can capture much of what typically is meant ...
... model class (perhaps with minor revisions of the model class in some cases), the second example results in a new specific model within a new model class that is essentially a cross of the original model class with itself. Examples of the first general type can capture much of what typically is meant ...
Voltage Secure Stateless Tokenization - HPE Security
... In addition to solving immediate PCI DSS compliance issues, Voltage SecureData is a comprehensive platform for future-proofing the compliance process. A single cloud-ready architecture combines tokenization, end-to-end encryption, structured and unstructured data protection, and data de-identificati ...
... In addition to solving immediate PCI DSS compliance issues, Voltage SecureData is a comprehensive platform for future-proofing the compliance process. A single cloud-ready architecture combines tokenization, end-to-end encryption, structured and unstructured data protection, and data de-identificati ...
SQuirreL, a Universal SQL Client by Gerd Wagner and Glenn Griffin
... driver is, and Define a link to a specific database on a specific machine using that driver. These are referred to as defining the “Driver” and creating an “Alias”, where the “Alias” can be thought of as a specific instance of the more general “Driver” configuration. Every time SQuirreL is started ...
... driver is, and Define a link to a specific database on a specific machine using that driver. These are referred to as defining the “Driver” and creating an “Alias”, where the “Alias” can be thought of as a specific instance of the more general “Driver” configuration. Every time SQuirreL is started ...
Connecting SAS
... SAS is a very powerful analytical tool, but not all data comes as a SAS dataset. Being able to get data into and out of SAS is an integral part of the work we do with clients at the RAND Corporation. Additionally, in our group at RAND, we keep our data warehousing environment and our analytical envi ...
... SAS is a very powerful analytical tool, but not all data comes as a SAS dataset. Being able to get data into and out of SAS is an integral part of the work we do with clients at the RAND Corporation. Additionally, in our group at RAND, we keep our data warehousing environment and our analytical envi ...
AN OVERVIEW OF FRAGMENTATION DESIGN FOR DISTRIBUTED
... The emerging of smart phone and tablet market has generated big volume of data and it grown exponentially in every minute. This gigantic volume of data also has been named as Big Data. The cohesiveness between these data is low as data might or might not be related to each other. Thus, XML is a good ...
... The emerging of smart phone and tablet market has generated big volume of data and it grown exponentially in every minute. This gigantic volume of data also has been named as Big Data. The cohesiveness between these data is low as data might or might not be related to each other. Thus, XML is a good ...
W-7 OMT-II
... The task could be achieved by a two-stage query: first find the maths students and then, knowing the college, look up the relevant principal. A much more efficient method is to use the relational capabilities of Access to run a query on more than one related table The COLLEGES and STUDENTS tables ha ...
... The task could be achieved by a two-stage query: first find the maths students and then, knowing the college, look up the relevant principal. A much more efficient method is to use the relational capabilities of Access to run a query on more than one related table The COLLEGES and STUDENTS tables ha ...
Measuring Recidivism: Definitions, Errors, and Data Sources
... conviction) in a defined amount of time. Therefore, definitions can vary by changing the group, the criteria, or the amount of time for which recidivism is calculated. ...
... conviction) in a defined amount of time. Therefore, definitions can vary by changing the group, the criteria, or the amount of time for which recidivism is calculated. ...
- Arione Consulting
... o Translating a Data Model into a Dataliase Design Using the mysql Command-Line Tool o Running the mysql Client o Customizing the mysql Prompt o mysql Commands o Using the Help Command o Some Useful mysql Options o Working with a Dataliase o Examining Talile Definitions o Other SHOW Options DDL – Da ...
... o Translating a Data Model into a Dataliase Design Using the mysql Command-Line Tool o Running the mysql Client o Customizing the mysql Prompt o mysql Commands o Using the Help Command o Some Useful mysql Options o Working with a Dataliase o Examining Talile Definitions o Other SHOW Options DDL – Da ...
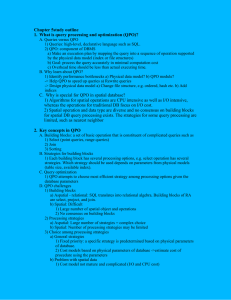
Document
... for spatial DB query processing exists. The strategies for some query processing are limited, such as nearest neighbor 2. Key concepts in QPO A. Building blocks: a set of basic operation that is constituent of complicated queries such as 1) Select (point queries, range queries) 2) Join 3) Sorting B. ...
... for spatial DB query processing exists. The strategies for some query processing are limited, such as nearest neighbor 2. Key concepts in QPO A. Building blocks: a set of basic operation that is constituent of complicated queries such as 1) Select (point queries, range queries) 2) Join 3) Sorting B. ...
View File - University of Engineering and Technology, Taxila
... feedback to the analysts (ICDE users) on their activities. – A direct implication of this is that these tools need access to the events recorded by the ICDE system as they occur. – Hence, some mechanism is needed to distribute ICDE usergenerated events as they are captured in the Data Store. ...
... feedback to the analysts (ICDE users) on their activities. – A direct implication of this is that these tools need access to the events recorded by the ICDE system as they occur. – Hence, some mechanism is needed to distribute ICDE usergenerated events as they are captured in the Data Store. ...
SeaDataNet and EMODNET Vocabularies
... Some data outside the intended scope will be captured (e.g. Methylated arsenic in a trawl designed for organotins) Easy to overlook consequences of any P02 rationalisation P02 list can be tested against P35 (both map to P01) ...
... Some data outside the intended scope will be captured (e.g. Methylated arsenic in a trawl designed for organotins) Easy to overlook consequences of any P02 rationalisation P02 list can be tested against P35 (both map to P01) ...
using-content-providers-U08928-JAN
... Content Providers allow applications to store, and potentially share, data in a standard form. The data is wrapped up so that it looks as if it is in the form of tables (often the data will be stored in an SQLite database, so it actually is in that form, but it doesn’t have to be). Each conten ...
... Content Providers allow applications to store, and potentially share, data in a standard form. The data is wrapped up so that it looks as if it is in the form of tables (often the data will be stored in an SQLite database, so it actually is in that form, but it doesn’t have to be). Each conten ...
Hampton Roads REALTORS ® Association Partners with RPR
... Application. Real Estate Information Network, Inc. (REIN MLS), the multiple listing service for the Hampton Roads area executed RPR’s Data Content License Agreement, which will allow HRRA to begin offering all its REALTOR® members the full features and functionality of RPR’s member benefit applicati ...
... Application. Real Estate Information Network, Inc. (REIN MLS), the multiple listing service for the Hampton Roads area executed RPR’s Data Content License Agreement, which will allow HRRA to begin offering all its REALTOR® members the full features and functionality of RPR’s member benefit applicati ...
Getting Started with Databases
... The files for all the tables belonging to a given database are stored in a directory with the same name as the database All database directories are stored in the data directory within c:\mysql Note: upon completion of the MySQL installation process, there are two databases ...
... The files for all the tables belonging to a given database are stored in a directory with the same name as the database All database directories are stored in the data directory within c:\mysql Note: upon completion of the MySQL installation process, there are two databases ...
Entity SQL Block
... Are elements of the SSDL Are created whenever you map a view into the EDM Are a projection of data and therefore are read only Using stored procedures you can add write functionality You can create your own DefiningQueries ...
... Are elements of the SSDL Are created whenever you map a view into the EDM Are a projection of data and therefore are read only Using stored procedures you can add write functionality You can create your own DefiningQueries ...
Towards a XML Fuzzy Structured Query Language
... Together with the inclusion of the fuzzy paradigm in many aspects of computer science, an easy and efficient way of managing, manipulating and storing fuzzy data is becoming more necessary. This fact makes fuzzy database management systems (FDBMS) an important part of complex soft-computing systems, ...
... Together with the inclusion of the fuzzy paradigm in many aspects of computer science, an easy and efficient way of managing, manipulating and storing fuzzy data is becoming more necessary. This fact makes fuzzy database management systems (FDBMS) an important part of complex soft-computing systems, ...
OBJECT STORAGE ARCHITECTURE
... Distributed Metadata Current storage architectures are designed with a single monolithic metadata server that serves two primary functions. First, it provides the compute node with a logical view of the stored data (the Virtual File System or VFS layer), the list of file names, and typically the dir ...
... Distributed Metadata Current storage architectures are designed with a single monolithic metadata server that serves two primary functions. First, it provides the compute node with a logical view of the stored data (the Virtual File System or VFS layer), the list of file names, and typically the dir ...
New SQL Performance Optimizations to Enhance Your SAS® Client and Solution Access to the Database
... SAS® SQL has been used for years as the way many SAS® products query for their data. Take a look at the new SQL performance optimizations that have been added to this bellwether procedure, optimizations designed to greatly expand query pass-thru capability to data bases and shorten your SAS client a ...
... SAS® SQL has been used for years as the way many SAS® products query for their data. Take a look at the new SQL performance optimizations that have been added to this bellwether procedure, optimizations designed to greatly expand query pass-thru capability to data bases and shorten your SAS client a ...
Getting Oracle Data into SAS® Datasets
... To begin, you will need to know about your SAS licenses, and you will need to find an Oracle subject matter expert who knows the location of your Oracle database. SAS LICENSES There are two SAS licenses that will allow you to access Oracle data in the Windows environment: 1. SAS/ACCESS Interface to ...
... To begin, you will need to know about your SAS licenses, and you will need to find an Oracle subject matter expert who knows the location of your Oracle database. SAS LICENSES There are two SAS licenses that will allow you to access Oracle data in the Windows environment: 1. SAS/ACCESS Interface to ...
Academic Script
... Constraints within a database are rules which control values allowed in columns and also enforce the integrity between columns and tables. Each E-R schema may define some constraints to which the contents of a database must confirm. Some of the commonly used constraints are keys, mapping cardinaliti ...
... Constraints within a database are rules which control values allowed in columns and also enforce the integrity between columns and tables. Each E-R schema may define some constraints to which the contents of a database must confirm. Some of the commonly used constraints are keys, mapping cardinaliti ...
Presentation summary: XML views in relational databases
... The definition of XML view is somewhat the same as the concept of view in the relational databases. However, the result of the XML view is an XML document. The XML view describes the shape of an XML document, even though the XML does not really exist because it is created on the fly from the relatio ...
... The definition of XML view is somewhat the same as the concept of view in the relational databases. However, the result of the XML view is an XML document. The XML view describes the shape of an XML document, even though the XML does not really exist because it is created on the fly from the relatio ...
Supervised Classification Leveraging Refined Unlabeled Data
... which originate from both supervised (e.g. Support Vector Machines) and unsupervised tasks (e.g. clustering). These can be categorized as inductive learning, focused on using the model to learn general rules that can subsequently be used for future predictions, and transductive approaches, learning ...
... which originate from both supervised (e.g. Support Vector Machines) and unsupervised tasks (e.g. clustering). These can be categorized as inductive learning, focused on using the model to learn general rules that can subsequently be used for future predictions, and transductive approaches, learning ...
Record Linkage - Data Cleaning
... link information regarding entities to answer ethically-approved epidemiological, health system or social science research and policy questions. In many research projects it is necessary to collate information about an entity from more than one data source. If a unique identifier or key ...
... link information regarding entities to answer ethically-approved epidemiological, health system or social science research and policy questions. In many research projects it is necessary to collate information about an entity from more than one data source. If a unique identifier or key ...