Interfacing possibilities in Microsoft Access, using external data
... to create. The subroutine creates two object variables. The first one is of database type and the second one is of table definition type. After this, it sends the database type object to the current database and after that it creates a table definition with the name tblCustomer. For this table defin ...
... to create. The subroutine creates two object variables. The first one is of database type and the second one is of table definition type. After this, it sends the database type object to the current database and after that it creates a table definition with the name tblCustomer. For this table defin ...
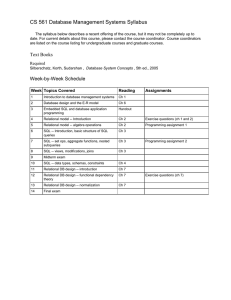
CS 561 Database Management Systems Syllabus
... The syllabus below describes a recent offering of the course, but it may not be completely up to date. For current details about this course, please contact the course coordinator. Course coordinators are listed on the course listing for undergraduate courses and graduate courses. ...
... The syllabus below describes a recent offering of the course, but it may not be completely up to date. For current details about this course, please contact the course coordinator. Course coordinators are listed on the course listing for undergraduate courses and graduate courses. ...
System Design Specification - Project Management
... provides controls such as scrollable lists and tick boxes via ActiveX. HTML editing is now part of the Visual Studio suite from Microsoft. However I have been unable to find any documentation of a library that provides ‘design-time controls’. The currently used DLL file (fpdtc.dll) appears to be sta ...
... provides controls such as scrollable lists and tick boxes via ActiveX. HTML editing is now part of the Visual Studio suite from Microsoft. However I have been unable to find any documentation of a library that provides ‘design-time controls’. The currently used DLL file (fpdtc.dll) appears to be sta ...
Data Warehousing – CG124
... 5. Demonstrate and evaluate procedural and object techniques for server-side programming. 6. Discuss and explain the key principles and techniques involved in building and operating server-side database applications. ...
... 5. Demonstrate and evaluate procedural and object techniques for server-side programming. 6. Discuss and explain the key principles and techniques involved in building and operating server-side database applications. ...
File and Database Design Continued
... File Access Sequential Access Method (all records in sequence, usually by primary key) Random Access Method (any one record) Various programming techniques must be used in non-DBMS systems DBMS is all by key, Sequentially or ...
... File Access Sequential Access Method (all records in sequence, usually by primary key) Random Access Method (any one record) Various programming techniques must be used in non-DBMS systems DBMS is all by key, Sequentially or ...
Building Mission Critical Applications
... Exists operator support for properties (example: public static methods of a Collapsed and expanded shapes .NET class can be called such as ...
... Exists operator support for properties (example: public static methods of a Collapsed and expanded shapes .NET class can be called such as ...
Drive pervasive business performance
... Reporting and Analysis Broad reach tools for insight Analyze information with powerful and familiar tools New Office Excel Pivot Tables for analyzing information using business terms Tight integration between Office Excel and Microsoft SQL Server Analysis Services ProClarity for additional advanced ...
... Reporting and Analysis Broad reach tools for insight Analyze information with powerful and familiar tools New Office Excel Pivot Tables for analyzing information using business terms Tight integration between Office Excel and Microsoft SQL Server Analysis Services ProClarity for additional advanced ...
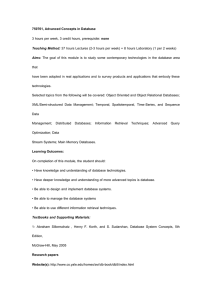
750761, Advanced Concepts in Database
... Aims: The goal of this module is to study some contemporary technologies in the database area that have been adopted in real applications and to survey products and applications that embody these technologies. Selected topics from the following will be covered: Object Oriented and Object Relational ...
... Aims: The goal of this module is to study some contemporary technologies in the database area that have been adopted in real applications and to survey products and applications that embody these technologies. Selected topics from the following will be covered: Object Oriented and Object Relational ...
Slides
... Can be applied to the entire database, at the record level, the attribute level, or level of the individual field ...
... Can be applied to the entire database, at the record level, the attribute level, or level of the individual field ...
TableAdapters and TableAdapterManager
... Is often incorrectly used as a substitute for true n-tier “data access layer” Use of wizard may cause you to overlook other options such as stored procedures ...
... Is often incorrectly used as a substitute for true n-tier “data access layer” Use of wizard may cause you to overlook other options such as stored procedures ...
Access 2013 Unit A EOU Solutions
... SQL: Structured Query Language (SQL) is the most popular computer language used to create, modify and query databases. http://en.wikipedia.org/wiki/SQL database: A database is information set with a regular structure. Its front-end allows data access, searching and sorting routines. Its back-end aff ...
... SQL: Structured Query Language (SQL) is the most popular computer language used to create, modify and query databases. http://en.wikipedia.org/wiki/SQL database: A database is information set with a regular structure. Its front-end allows data access, searching and sorting routines. Its back-end aff ...
DATABASE SECURITY
... that renders the data unreadable by any program without the decryption key. There will be degradation in performance because of the time taken to decode it. It also protects the data transmitted over communication lines. ...
... that renders the data unreadable by any program without the decryption key. There will be degradation in performance because of the time taken to decode it. It also protects the data transmitted over communication lines. ...
Extracting Access Data
... companies generally accept Tex , XML or similar files. o Text File = a file presents each record as a series of fields typically separated by commas o XML = a file that includes information about the contents of the file along with the data; common intercompany exchange format that can be governed b ...
... companies generally accept Tex , XML or similar files. o Text File = a file presents each record as a series of fields typically separated by commas o XML = a file that includes information about the contents of the file along with the data; common intercompany exchange format that can be governed b ...
gatlinburgh - Animated DataBase Courseware
... • design and develop animations in support of key database concepts. Current topics SQL (finished prototypes) Database Design (few prototypes) Concurrency (design, 1st prototype) ...
... • design and develop animations in support of key database concepts. Current topics SQL (finished prototypes) Database Design (few prototypes) Concurrency (design, 1st prototype) ...
Data Modeling Case Study
... The following is description by a pharmacy owner: "Jack Smith catches a cold and what he suspects is a flu virus. He makes an appointment with his family doctor who confirm his diagnosis. The doctor prescribes an antibiotic and nasal decongestant tablets. Jack leaves the doctor's office and drives t ...
... The following is description by a pharmacy owner: "Jack Smith catches a cold and what he suspects is a flu virus. He makes an appointment with his family doctor who confirm his diagnosis. The doctor prescribes an antibiotic and nasal decongestant tablets. Jack leaves the doctor's office and drives t ...
Document
... species lists from database Include links to ancillary information (habitats, voucher specimen, site occurrences, photos, data sets, pubs) ...
... species lists from database Include links to ancillary information (habitats, voucher specimen, site occurrences, photos, data sets, pubs) ...
DATABASE ADMINISTRATOR Driscoll Children`s Hospital located
... procedures analysis; keeping up with new trends and developments in the field of information systems technology; technical troubleshooting, analysis, and problem solving in an enterprise environment. Prior experience working in a healthcare environment is a plus. Bachelor’s degree with 5+ years rela ...
... procedures analysis; keeping up with new trends and developments in the field of information systems technology; technical troubleshooting, analysis, and problem solving in an enterprise environment. Prior experience working in a healthcare environment is a plus. Bachelor’s degree with 5+ years rela ...
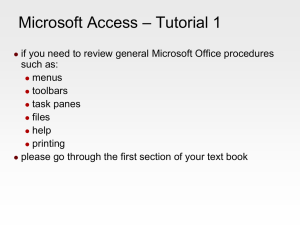
Access tutorial 1
... tables are connected together using common fields common fields appear in more than one table when the primary key from one table appears in another table, it is called a foreign key foreign keys may be repeated note the NAICS field in the Employer Table ...
... tables are connected together using common fields common fields appear in more than one table when the primary key from one table appears in another table, it is called a foreign key foreign keys may be repeated note the NAICS field in the Employer Table ...
Database Communication
... The second method we will use for retrieving data uses ADO. Before using ADO, you need to activate the relevant components in VBA. Go to Tools | References in VBA, then scroll down the list of available references and select the Data references shown below. ...
... The second method we will use for retrieving data uses ADO. Before using ADO, you need to activate the relevant components in VBA. Go to Tools | References in VBA, then scroll down the list of available references and select the Data references shown below. ...
PPT-Lesson 1 - Getting Started with a Database
... Network – each record type can have multiple owners Dimensional – is a relational database that uses a dimensional data model to organize data ...
... Network – each record type can have multiple owners Dimensional – is a relational database that uses a dimensional data model to organize data ...
Introduction to Azure SQL Databases
... Code near data. Guaranteed predictable performance. Easily scalable. Lower price. Built-in HA, backup and restore ...
... Code near data. Guaranteed predictable performance. Easily scalable. Lower price. Built-in HA, backup and restore ...
Introduction to Database
... Skilled software developers and data architects use it to develop powerful, complex applications. Relatively unskilled programmers and non-programmer "power users" can use it to build simple applications without having to deal with features they don't understand. ...
... Skilled software developers and data architects use it to develop powerful, complex applications. Relatively unskilled programmers and non-programmer "power users" can use it to build simple applications without having to deal with features they don't understand. ...
Microsoft Access
Microsoft Access is a DBMS (also known as Database Management System) from Microsoft that combines the relational Microsoft Jet Database Engine with a graphical user interface and software-development tools. It is a member of the Microsoft Office suite of applications, included in the Professional and higher editions or sold separately.Microsoft Access stores data in its own format based on the Access Jet Database Engine. It can also import or link directly to data stored in other applications and databases.Software developers and data architects can use Microsoft Access to develop application software, and ""power users"" can use it to build software applications. Like other Office applications, Access is supported by Visual Basic for Applications (VBA), an object-oriented programming language that can reference a variety of objects including DAO (Data Access Objects), ActiveX Data Objects, and many other ActiveX components. Visual objects used in forms and reports expose their methods and properties in the VBA programming environment, and VBA code modules may declare and call Windows operating-system functions.