Managing Expressions as Data in Relational Database
... attributes such as type of insurance, coverage level, and geographical location. Now, a table holding the list of Insurance agents can store expressions defined on policyholder’s attributes to maintain an N-to-M relationship between the insurance agents and the corresponding policyholders. By using ...
... attributes such as type of insurance, coverage level, and geographical location. Now, a table holding the list of Insurance agents can store expressions defined on policyholder’s attributes to maintain an N-to-M relationship between the insurance agents and the corresponding policyholders. By using ...
Extreme Database programming with MUMPS Globals
... In this example, the data items that make up the employee details (name, position, telephone number) have been appended together with the back-apostrophe character as a delimiter. MUMPS does not impose any controls or rules over how you construct your data structures : there’s no schema or data dict ...
... In this example, the data items that make up the employee details (name, position, telephone number) have been appended together with the back-apostrophe character as a delimiter. MUMPS does not impose any controls or rules over how you construct your data structures : there’s no schema or data dict ...
Administering Websense Databases
... Data Security Contains information about DLP and discovery transactions that resulted in incidents, such as the contents of an email body, including the From:, To:, and Cc: fields, as well as actual attachments. Transactions can also include Web posts, endpoint operations, and discovered as well as ...
... Data Security Contains information about DLP and discovery transactions that resulted in incidents, such as the contents of an email body, including the From:, To:, and Cc: fields, as well as actual attachments. Transactions can also include Web posts, endpoint operations, and discovered as well as ...
MySQL Chapter 3
... • Can correct errors by dropping (deleting) a table and starting over • Useful when table is created before errors are discovered • Command is followed by the table to be dropped and a semicolon • Any data in table also deleted A Guide to MySQL ...
... • Can correct errors by dropping (deleting) a table and starting over • Useful when table is created before errors are discovered • Command is followed by the table to be dropped and a semicolon • Any data in table also deleted A Guide to MySQL ...
Press Release
... Accountability Act (HIPAA), Payment Card Industry (PCI) Data Security Standard (DSS). This latest release introduces additional pre-built reports, and now captures before-and-after changes to sensitive data to help organization save time and costs related to compliance reporting. Oracle Audit Vault ...
... Accountability Act (HIPAA), Payment Card Industry (PCI) Data Security Standard (DSS). This latest release introduces additional pre-built reports, and now captures before-and-after changes to sensitive data to help organization save time and costs related to compliance reporting. Oracle Audit Vault ...
Advanced Database Techniques 2009
... JoinABprime - a simple join of relations A and Bprime where the cardinality of the Bprime relation is 10% that of the A relation. JoinASelB - this query is composed of one join and one selection. A and B have the same number of tuples. The selection on B has a 10% selectivity factor, reducing B to t ...
... JoinABprime - a simple join of relations A and Bprime where the cardinality of the Bprime relation is 10% that of the A relation. JoinASelB - this query is composed of one join and one selection. A and B have the same number of tuples. The selection on B has a 10% selectivity factor, reducing B to t ...
Install and configure Tivoli Common Reporting Cognos-based reports within IBM Tivoli
... Allowing customers access (via upgrade) to IBM Cognos advanced analytics modules for advanced reporting capabilities that were not possible with TCR 1.2. ...
... Allowing customers access (via upgrade) to IBM Cognos advanced analytics modules for advanced reporting capabilities that were not possible with TCR 1.2. ...
Creating a Standby Database using RMAN and Tivoli Storage
... recovery MANUALLY via the following command: SQL> RECOVER STANDBY DATABASE ( apply the required archive log file when prompted) This example will put the standby database in MAXIMUM PERFORMANCE mode. In case we wish to configure the standby database for MAXIMUM AVAILABILITY or MAXIMUM PROTECTION we ...
... recovery MANUALLY via the following command: SQL> RECOVER STANDBY DATABASE ( apply the required archive log file when prompted) This example will put the standby database in MAXIMUM PERFORMANCE mode. In case we wish to configure the standby database for MAXIMUM AVAILABILITY or MAXIMUM PROTECTION we ...
Creating a Standby Database using RMAN and Tivoli Storage
... recovery MANUALLY via the following command: SQL> RECOVER STANDBY DATABASE ( apply the required archive log file when prompted) This example will put the standby database in MAXIMUM PERFORMANCE mode. In case we wish to configure the standby database for MAXIMUM AVAILABILITY or MAXIMUM PROTECTION we ...
... recovery MANUALLY via the following command: SQL> RECOVER STANDBY DATABASE ( apply the required archive log file when prompted) This example will put the standby database in MAXIMUM PERFORMANCE mode. In case we wish to configure the standby database for MAXIMUM AVAILABILITY or MAXIMUM PROTECTION we ...
Chapter 21:Application Development and Administration
... That is, once the server replies to a request, the server closes the connection with the client, and forgets all about the request In contrast, Unix logins, and JDBC/ODBC connections stay connected until the client disconnects retaining user authentication and other information ...
... That is, once the server replies to a request, the server closes the connection with the client, and forgets all about the request In contrast, Unix logins, and JDBC/ODBC connections stay connected until the client disconnects retaining user authentication and other information ...
Introducing Microsoft SQL Server 2016
... Hardware Security Module (HSM), or the Azure Key Vault. The application that is encrypting the data uses the column master key to protect the various column encryption keys that handle the encryption of the data within the columns of a database table. Note Using an HSM, also known as an Enterprise K ...
... Hardware Security Module (HSM), or the Azure Key Vault. The application that is encrypting the data uses the column master key to protect the various column encryption keys that handle the encryption of the data within the columns of a database table. Note Using an HSM, also known as an Enterprise K ...
Advanced Databases - Work To Do Home page
... The main difference between storing your data in a spreadsheet and storing it in a database is in how the data is organized. A relational database holds its data over a number of tables not just one. Records within the table are linked (related) to data held in other tables. ...
... The main difference between storing your data in a spreadsheet and storing it in a database is in how the data is organized. A relational database holds its data over a number of tables not just one. Records within the table are linked (related) to data held in other tables. ...
Kroenke-Auer-DBP-e12-PPT-Chapter-04
... • They are used for querying, reporting, and data mining applications. • They are never updated (in the operational database sense—they may have new data imported from time to time). KROENKE AND AUER - DATABASE PROCESSING, 12th Edition © 2012 Pearson Prentice Hall ...
... • They are used for querying, reporting, and data mining applications. • They are never updated (in the operational database sense—they may have new data imported from time to time). KROENKE AND AUER - DATABASE PROCESSING, 12th Edition © 2012 Pearson Prentice Hall ...
Dynamic Query Forms for Database Queries
... Recently proposed automatic approaches to generate the database query forms without user participation presented a data-driven method. It first finds a set of data attributes, which are most likely queried based on the database schema and data instances. Then, the query forms are generated based on ...
... Recently proposed automatic approaches to generate the database query forms without user participation presented a data-driven method. It first finds a set of data attributes, which are most likely queried based on the database schema and data instances. Then, the query forms are generated based on ...
Microsoft SQL Server - SafeNet
... secure solution because the encryption keys do not reside with encryption data. Data can be encrypted by using encryption keys that only the database user has access to on the external EKM/HSM module. SafeNet provides Luna EKM which includes the EKM Provider Library for SafeNet Luna HSM that can be ...
... secure solution because the encryption keys do not reside with encryption data. Data can be encrypted by using encryption keys that only the database user has access to on the external EKM/HSM module. SafeNet provides Luna EKM which includes the EKM Provider Library for SafeNet Luna HSM that can be ...
Introduction to Python programming for biologists
... • Introduction and Examples • Relational Database Design by Example • entities and relational diagrams ...
... • Introduction and Examples • Relational Database Design by Example • entities and relational diagrams ...
Introduction to JDBC - Dr. Ramesh R. Manza
... • Lets programmers connect to a database, query it or update through a Java application. • Programs developed with Java & JDBC are platform & vendor independent. • JDBC library is implemented in java.sql package. ...
... • Lets programmers connect to a database, query it or update through a Java application. • Programs developed with Java & JDBC are platform & vendor independent. • JDBC library is implemented in java.sql package. ...
A Bootstrapping Architecture for Integration of Relational Databases to the Semantic Web
... The vision of the Semantic Web is to create a web of data with well-defined meaning. Most data in the current web is managed by relational databases. Thus, it is imperative for the Semantic Web community to offer easily implemented solutions to bridging relational database content and RDF. Direct ma ...
... The vision of the Semantic Web is to create a web of data with well-defined meaning. Most data in the current web is managed by relational databases. Thus, it is imperative for the Semantic Web community to offer easily implemented solutions to bridging relational database content and RDF. Direct ma ...
The Terrestrial BR IFIC Workshop
... Queries written in SQL Saved queries Export the results of a query to a MS Access container in addition to SQLite container BR IFIC Database Manager: To select an existing version of the BR IFIC database or an extract of it BR IFIC Format Converter: Possibility to create a bridge MS Access® database ...
... Queries written in SQL Saved queries Export the results of a query to a MS Access container in addition to SQLite container BR IFIC Database Manager: To select an existing version of the BR IFIC database or an extract of it BR IFIC Format Converter: Possibility to create a bridge MS Access® database ...
KYMENLAAKSON AMMATTIKORKEAKOULU University of Applied Sciences
... database. Query language is offered in most of the object databases, although no practical language is available. Object Query Language (OQL) was developed to fix this problem, but due complexity of object databases, no vendor fully implemented this language. There is no need of joins in accessing d ...
... database. Query language is offered in most of the object databases, although no practical language is available. Object Query Language (OQL) was developed to fix this problem, but due complexity of object databases, no vendor fully implemented this language. There is no need of joins in accessing d ...
PPT file
... • Describe the basic principals of the relational model of data • Define the modeling concepts and notation of the relational model • Learn about the relational constraints • Define the update operations of the relational model • Handling the violations of the integrity constraints • Learn about rel ...
... • Describe the basic principals of the relational model of data • Define the modeling concepts and notation of the relational model • Learn about the relational constraints • Define the update operations of the relational model • Handling the violations of the integrity constraints • Learn about rel ...
Mini-MSDD - Relational Databases
... repeating groups are not allowed vectors are not allowed pointers and other abstract references are not allowed values for a particular attribute come from a specified pool of values (called its domain) ...
... repeating groups are not allowed vectors are not allowed pointers and other abstract references are not allowed values for a particular attribute come from a specified pool of values (called its domain) ...
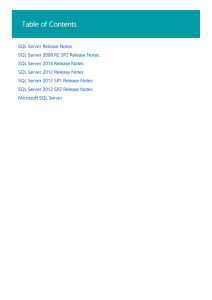
SQL Server Release Notes | Microsoft Docs
... cannot be used for the query, SQL Server 2014 will not always report a missing index in SHOWPLAN_XML and in the DMV sys.dm_db_missing_index_details. In particular, if a query contains equality predicates that involve a subset of the index key columns or if it contains inequality predicates that invo ...
... cannot be used for the query, SQL Server 2014 will not always report a missing index in SHOWPLAN_XML and in the DMV sys.dm_db_missing_index_details. In particular, if a query contains equality predicates that involve a subset of the index key columns or if it contains inequality predicates that invo ...