RFID Malware: Design Principles and Examples,
... drop table
which will delete the specified database table. Many databases also support IF/THEN
constructs, which could destroy the database at a predetermined time, thus allowing the
virus to first spread to other databases. RFID-based exploits can even “steal” data from the
database by ...
... drop table
PersistenceHibernate
... • Hibernate provides a set of Eclipse tools http://www.hibernate.org/255.html – Mapping Editor: An editor for Hibernate XML mapping files, supporting auto-completion and syntax highlighting – Console: a view in Eclipse. Provides a tree overview of console configurations and interactive view of persi ...
... • Hibernate provides a set of Eclipse tools http://www.hibernate.org/255.html – Mapping Editor: An editor for Hibernate XML mapping files, supporting auto-completion and syntax highlighting – Console: a view in Eclipse. Provides a tree overview of console configurations and interactive view of persi ...
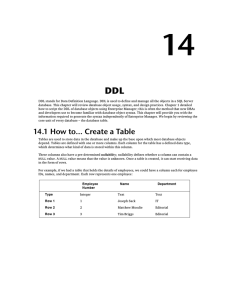
Using DDL Statements Questions
... Answer: A. The p indicates precision,the total number of digits to the left and right of the decimal position, to a maximum of 38 digits; the s, or scale, indicates the number of positions to the right of the decimal.Example: NUMBER7, 2 can store a numeric value up to 99999.99. If precision or scal ...
... Answer: A. The p indicates precision,the total number of digits to the left and right of the decimal position, to a maximum of 38 digits; the s, or scale, indicates the number of positions to the right of the decimal.Example: NUMBER7, 2 can store a numeric value up to 99999.99. If precision or scal ...
Higher Databases Notes
... and 015, and that DVD 003 has been rented by members 1012 and 1056. By looking at the DVD RENTAL entity, we can see that some DVDs (e.g. 003 and 011) are related to more than one member, because each DVD can be rented by many members. By looking at the MEMBER entity, we can see that many members hav ...
... and 015, and that DVD 003 has been rented by members 1012 and 1056. By looking at the DVD RENTAL entity, we can see that some DVDs (e.g. 003 and 011) are related to more than one member, because each DVD can be rented by many members. By looking at the MEMBER entity, we can see that many members hav ...
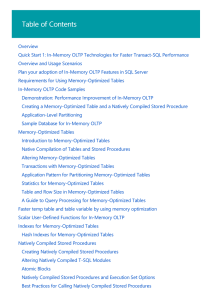
In-Memory OLTP (In-Memory Optimization) | Microsoft Docs
... the hard disk. Each transaction is committed to both representations of the table. Transactions operate against the much faster active memory representation. Memory-optimized tables benefit from the greater speed of active memory versus the disk. Further, the greater nimbleness of active memory make ...
... the hard disk. Each transaction is committed to both representations of the table. Transactions operate against the much faster active memory representation. Memory-optimized tables benefit from the greater speed of active memory versus the disk. Further, the greater nimbleness of active memory make ...
A Strategy for Reducing I/O and Improving Query Processing Time in
... Disk and memory access are the main obstacles on the path to reducing query processing time. Data warehouses systems, known for their immense size and long running queries, can be severely affected by these impediments. As result, a performance improvement strategy is needed which reduces the amount ...
... Disk and memory access are the main obstacles on the path to reducing query processing time. Data warehouses systems, known for their immense size and long running queries, can be severely affected by these impediments. As result, a performance improvement strategy is needed which reduces the amount ...
BSM 9.2x Linux Tips and Tricks
... In Linux there are MANY ways to get to the same result. There are different command shells, graphical interfaces, commands, utilities, packages, tools. Talk to five Linux or Unix people, they know ten different ways to get to the same result, and each way is the best one. All here is based on RHEL 5 ...
... In Linux there are MANY ways to get to the same result. There are different command shells, graphical interfaces, commands, utilities, packages, tools. Talk to five Linux or Unix people, they know ten different ways to get to the same result, and each way is the best one. All here is based on RHEL 5 ...
comlab.ox.ac.uk - Department of Computer Science, Oxford
... nity due to its applications to scientific data management, data cleaning, data integration, and sensor networks. This problem is known to be notoriously hard. A fundamental result concerning its complexity is the dichotomy for conjunctive queries without self-joins on so-called tuple-independent pr ...
... nity due to its applications to scientific data management, data cleaning, data integration, and sensor networks. This problem is known to be notoriously hard. A fundamental result concerning its complexity is the dichotomy for conjunctive queries without self-joins on so-called tuple-independent pr ...
Performance
... SQL Plan Management (1/6) Usual situation: • Plan regression after patch application • Typical of R12 usage of GTT *, when the same program is run for two different workloads from different subsidiaries, depending on the order of company these program are run, the optimizer may choose and hold a pat ...
... SQL Plan Management (1/6) Usual situation: • Plan regression after patch application • Typical of R12 usage of GTT *, when the same program is run for two different workloads from different subsidiaries, depending on the order of company these program are run, the optimizer may choose and hold a pat ...
Subject: Database Management Systems
... for certain specialized applications. Examples include applications with tight real-time constraints or applications with just a few well-designed critical operations for which efficient custom code must be written. Another reason for not using a DBMS is that an application may need to manipulate th ...
... for certain specialized applications. Examples include applications with tight real-time constraints or applications with just a few well-designed critical operations for which efficient custom code must be written. Another reason for not using a DBMS is that an application may need to manipulate th ...
Heuristic Optimization of OLAP Queries in Multidimensionally
... optimizing OLAP queries in databases that are clustered with respect to multiple hierarchical dimensions using multidimensional access methods. The main contributions are the following: We present a multidimensional database architecture based on the star model (called CSB star). The dimension table ...
... optimizing OLAP queries in databases that are clustered with respect to multiple hierarchical dimensions using multidimensional access methods. The main contributions are the following: We present a multidimensional database architecture based on the star model (called CSB star). The dimension table ...
downloading
... PURPOSE. See the GNU General Public License for more details. You should have received a copy of the GNU General Public License along with rasdaman Community. If not, see www.gnu.org/licenses. For more information please see www.rasdaman.org or contact Peter Baumann via [email protected]. Copyrig ...
... PURPOSE. See the GNU General Public License for more details. You should have received a copy of the GNU General Public License along with rasdaman Community. If not, see www.gnu.org/licenses. For more information please see www.rasdaman.org or contact Peter Baumann via [email protected]. Copyrig ...
Efficient Query Evaluation on Probabilistic Databases
... for every relation Rp : this ensures that we don’t associate two different events e1 and e2 to the same tuple t (instead, we may want to associate e1 ∨ e2 to t). In addition to this tabular representation of a probabilistic relation, we consider a functional representation, where a probabilistic ins ...
... for every relation Rp : this ensures that we don’t associate two different events e1 and e2 to the same tuple t (instead, we may want to associate e1 ∨ e2 to t). In addition to this tabular representation of a probabilistic relation, we consider a functional representation, where a probabilistic ins ...
Relation
... 2. A k-ary relation L over the nonempty sets X1, …, Xk is a (1+k)-tuple L = (F(L), X1, …, Xk) where F(L) is a subset of the Cartesian product X1 × … × Xk. If all of the Xj for j = 1 to k are the same set X, then L is more simply called a k-ary relation over X. The set F(L) is called the figure of L ...
... 2. A k-ary relation L over the nonempty sets X1, …, Xk is a (1+k)-tuple L = (F(L), X1, …, Xk) where F(L) is a subset of the Cartesian product X1 × … × Xk. If all of the Xj for j = 1 to k are the same set X, then L is more simply called a k-ary relation over X. The set F(L) is called the figure of L ...
XML Today
... relational data as XML and XML data as relational. The main feature is the XMLType data type. This is a predefined object type that can store an XML document. Like any object type, XMLType can be used as the data type of a column in a table or view. The latter usage is important, as it means that an ...
... relational data as XML and XML data as relational. The main feature is the XMLType data type. This is a predefined object type that can store an XML document. Like any object type, XMLType can be used as the data type of a column in a table or view. The latter usage is important, as it means that an ...
Oracle Migration Workbench Reference Guide for Microsoft SQL
... Oracle Migration Workbench Reference Guide for Microsoft SQL Server and Sybase Adaptive Server Migrations, Release 9.2.0 for Microsoft Windows 98/2000 and Microsoft Windows NT. Part Number: A97248-01 Copyright © 1998, 2002 Oracle Corporation. All rights reserved. The Programs (which include both th ...
... Oracle Migration Workbench Reference Guide for Microsoft SQL Server and Sybase Adaptive Server Migrations, Release 9.2.0 for Microsoft Windows 98/2000 and Microsoft Windows NT. Part Number: A97248-01 Copyright © 1998, 2002 Oracle Corporation. All rights reserved. The Programs (which include both th ...
chapter08-MySQL
... information from which a computer program can quickly access information • Each row in a database table is called a record • A record in a database is a single complete set of related information • Each column in a database table is called a field • Fields are the individual categories of informatio ...
... information from which a computer program can quickly access information • Each row in a database table is called a record • A record in a database is a single complete set of related information • Each column in a database table is called a field • Fields are the individual categories of informatio ...
I Agree - FactSet
... herein are provided in SQL formatted for MSSQL. It may to be necessary adjust the query language to suit a different SQL DBMS. Sample queries should be viewed as possible examples of data calculations and are subject to change. The queries provided should be used as a guide to understand how the und ...
... herein are provided in SQL formatted for MSSQL. It may to be necessary adjust the query language to suit a different SQL DBMS. Sample queries should be viewed as possible examples of data calculations and are subject to change. The queries provided should be used as a guide to understand how the und ...
Log File Viewer | Microsoft Docs
... The transaction log is implemented as a separate file or set of files in the database. The log cache is managed separately from the buffer cache for data pages, which results in simple, fast, and robust code within the Database Engine. The format of log records and pages is not constrained to follow ...
... The transaction log is implemented as a separate file or set of files in the database. The log cache is managed separately from the buffer cache for data pages, which results in simple, fast, and robust code within the Database Engine. The format of log records and pages is not constrained to follow ...