Query Processing Principles & Tuning Queries
... Scan Reserves: 1000 page I/Os, 100*1000 tuples. For each Reserves tuple: 1.2 I/Os to get data entry in index, plus 1 I/O to get (the exactly one) matching Sailors tuple. Total: 220,000 I/Os. Hash-index (Alt. 2) on sid of Reserves (as inner): Scan Sailors: 500 page I/Os, 80*500 tuples. For ea ...
... Scan Reserves: 1000 page I/Os, 100*1000 tuples. For each Reserves tuple: 1.2 I/Os to get data entry in index, plus 1 I/O to get (the exactly one) matching Sailors tuple. Total: 220,000 I/Os. Hash-index (Alt. 2) on sid of Reserves (as inner): Scan Sailors: 500 page I/Os, 80*500 tuples. For ea ...
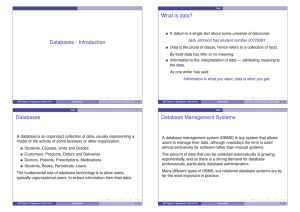
DBMS - Department of Higher Education
... History behind DBMS The problems with conventional file systems Advantages of DBMS Levels of abstraction ...
... History behind DBMS The problems with conventional file systems Advantages of DBMS Levels of abstraction ...
Chapter 10_Database_Space_Management
... information in the SYSTEM tablespace o Separate an application's table data from index data o Separate the system's transaction rollback data from other types of data o Separate temporary data used during internal system processing from permanently stored data For example, suppose you are planning t ...
... information in the SYSTEM tablespace o Separate an application's table data from index data o Separate the system's transaction rollback data from other types of data o Separate temporary data used during internal system processing from permanently stored data For example, suppose you are planning t ...
php - Anselm Spoerri
... Which symbol is used to preface all PHP variables? What can a variable store? What is the difference between $variable = 1 and $variable == 1? Why do you suppose that an underscore is allowed in variable names ($current_user) whereas hyphens are not ($current-user) ? Are variable names case-sensitiv ...
... Which symbol is used to preface all PHP variables? What can a variable store? What is the difference between $variable = 1 and $variable == 1? Why do you suppose that an underscore is allowed in variable names ($current_user) whereas hyphens are not ($current-user) ? Are variable names case-sensitiv ...
Database Cracking
... section. With cracking, the way data is physically stored self-organizes according to query workload. Even with a huge data set, only tuples of interest are touched, leading to significant gains in query performance. In case the focus shifts to a different part of the data, the cracker index automat ...
... section. With cracking, the way data is physically stored self-organizes according to query workload. Even with a huge data set, only tuples of interest are touched, leading to significant gains in query performance. In case the focus shifts to a different part of the data, the cracker index automat ...
DBA Guide to Databases on VMware
... failures do occur, the DBA needs to know how to use the backups to return the database to operational status as quickly as possible, without losing any transactions that were committed. There are several ways a database can fail, and the DBA must have a strategy to recover from each type of failure. ...
... failures do occur, the DBA needs to know how to use the backups to return the database to operational status as quickly as possible, without losing any transactions that were committed. There are several ways a database can fail, and the DBA must have a strategy to recover from each type of failure. ...
Slide: Temporal Databases
... storing complex temporal information. An example of this shortcoming is that the relational model does not support automatic merging of temporally overlapping data. ...
... storing complex temporal information. An example of this shortcoming is that the relational model does not support automatic merging of temporally overlapping data. ...
The Design and Implementation of a Self
... Intrusion detection. One critical step towards intrusion-tolerant database systems is intrusion detection (ID), which has attracted many researchers [13, 37, 21, 18, 39, 43, 38, 26, 28]. The existing methodology of ID can be roughly classed as anomaly detection, which is based on profiles of normal ...
... Intrusion detection. One critical step towards intrusion-tolerant database systems is intrusion detection (ID), which has attracted many researchers [13, 37, 21, 18, 39, 43, 38, 26, 28]. The existing methodology of ID can be roughly classed as anomaly detection, which is based on profiles of normal ...
HP 3PAR Recovery Manager 4.6.0 Software for Microsoft SQL
... 7 Recovery for Microsoft SQL Server..............................................................78 Microsoft SQL Server Recovery Models......................................................................................78 Recovering Data with HP 3PAR Recovery Manager.............................. ...
... 7 Recovery for Microsoft SQL Server..............................................................78 Microsoft SQL Server Recovery Models......................................................................................78 Recovering Data with HP 3PAR Recovery Manager.............................. ...
5.3 Domain Constraint Experiments - Computer Science
... 5.3.1.1.1 Analysis of Error Messages (String Tests) ................................................................. 21 5.3.1.1.2 Analysis of Actions (String Tests) .............................................................................. 22 5.3.1.2 Integer Tests and Results .................. ...
... 5.3.1.1.1 Analysis of Error Messages (String Tests) ................................................................. 21 5.3.1.1.2 Analysis of Actions (String Tests) .............................................................................. 22 5.3.1.2 Integer Tests and Results .................. ...
Using the ORACLE LIBNAME Engine to Reduce the Time it Takes to Extract Data From an ORACLE Database
... database is used for its ability to store, process, and retrieve data. Access to the database, however, is provided through a series of consolidated SAS® datasets. Consolidated SAS data combine data from an ORACLE parent table with information from multiple child tables. These SAS datasets are the p ...
... database is used for its ability to store, process, and retrieve data. Access to the database, however, is provided through a series of consolidated SAS® datasets. Consolidated SAS data combine data from an ORACLE parent table with information from multiple child tables. These SAS datasets are the p ...
Metadata Repository Design Concepts
... of immediate interest include Data Definitions (elements identified as having strategic value to the institution), Relational Database Metadata (RDBMS systems, tables, and columns), ETL metadata (data warehousing jobs and sequences), and Reporting Elements metadata (OBIEE presentation elements). Add ...
... of immediate interest include Data Definitions (elements identified as having strategic value to the institution), Relational Database Metadata (RDBMS systems, tables, and columns), ETL metadata (data warehousing jobs and sequences), and Reporting Elements metadata (OBIEE presentation elements). Add ...
course: database management system
... This course is primarily to be studied by students who are already graduates or post graduates in any field of study. Students who had not had exposure to computer science in their first degrees need to put in extra effort to grasp this course properly. This course guide takes you through the nature ...
... This course is primarily to be studied by students who are already graduates or post graduates in any field of study. Students who had not had exposure to computer science in their first degrees need to put in extra effort to grasp this course properly. This course guide takes you through the nature ...
Installing Acronis Recovery for MS SQL Server
... compression rates reduce the amount of data to store and transfer, leading to direct cost savings in storage and labor. Faster Disaster Recovery One-step Recovery and Automated Recovery to the Point-of-Failure make recovery faster and help organizations meet superior Recovery Time Objective (RTO). R ...
... compression rates reduce the amount of data to store and transfer, leading to direct cost savings in storage and labor. Faster Disaster Recovery One-step Recovery and Automated Recovery to the Point-of-Failure make recovery faster and help organizations meet superior Recovery Time Objective (RTO). R ...
XML datu glab**anas varianti Oracle XML DB datu b*z*
... include near-relational query and update performance, optimized memory management, reduced storage requirements, B-tree indexing, and in-place updates. These advantages are at a cost of increased processing overhead during ingestion and full retrieval of XML data, and reduced flexibility in the stru ...
... include near-relational query and update performance, optimized memory management, reduced storage requirements, B-tree indexing, and in-place updates. These advantages are at a cost of increased processing overhead during ingestion and full retrieval of XML data, and reduced flexibility in the stru ...
Relational Algebra
... shared data banks”, CACM), as a theory of a database model Spurred tremendous research in the database field and became the most popular logical data model - many relational DBMSs are today available on nearly all platforms A relational database is a set of relations RELATION: A table of values. Eac ...
... shared data banks”, CACM), as a theory of a database model Spurred tremendous research in the database field and became the most popular logical data model - many relational DBMSs are today available on nearly all platforms A relational database is a set of relations RELATION: A table of values. Eac ...
XML and DB2
... Data management functionalities (integrity, security, recoverability and management). User has the option to store the entire document as an column or decomposed into multiple tables and columns. Users can retrieve the entire document or extract XML elements and attributes dynamically in an SQ ...
... Data management functionalities (integrity, security, recoverability and management). User has the option to store the entire document as an column or decomposed into multiple tables and columns. Users can retrieve the entire document or extract XML elements and attributes dynamically in an SQ ...
A Workflow to Support Forensic Database Analysis
... or part of this thesis may be copied without infringement of copyright where such a reproduction is for the purposes of study and research. ...
... or part of this thesis may be copied without infringement of copyright where such a reproduction is for the purposes of study and research. ...