Designing, implementing and evaluating a database for a software
... The objective of this study is to design and implement a database for a software testing team. The previously mentioned design science approach by Hevner et al. (2004) is applied in this study. The database is the design artifact. There are seven guidelines for a successful design science research b ...
... The objective of this study is to design and implement a database for a software testing team. The previously mentioned design science approach by Hevner et al. (2004) is applied in this study. The database is the design artifact. There are seven guidelines for a successful design science research b ...
Database Compatibility for Oracle Developer`s Guide
... the complete library of Advanced Server guides available at: http://www.enterprisedb.com/products-services-training/products/documentation ...
... the complete library of Advanced Server guides available at: http://www.enterprisedb.com/products-services-training/products/documentation ...
Track Data Changes (SQL Server) | Microsoft Docs
... The ability to query for data that has changed in a database is an important requirement for some applications to be efficient. Typically, to determine data changes, application developers must implement a custom tracking method in their applications by using a combination of triggers, timestamp col ...
... The ability to query for data that has changed in a database is an important requirement for some applications to be efficient. Typically, to determine data changes, application developers must implement a custom tracking method in their applications by using a combination of triggers, timestamp col ...
External Procedures, Triggers, and User
... 6.3.2 GENERAL and GENERAL WITH NULLS parameter styles . . . . . . . . . . . . . . . . 6.4 Error handling in Java stored procedures . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 6.5 Retrieving user-defined errors in a client application . . . . . . . . . . . . . . . . . . . . . ...
... 6.3.2 GENERAL and GENERAL WITH NULLS parameter styles . . . . . . . . . . . . . . . . 6.4 Error handling in Java stored procedures . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 6.5 Retrieving user-defined errors in a client application . . . . . . . . . . . . . . . . . . . . . ...
Teradata Studio Express User Guide
... The information contained in this document may contain references or cross-references to features, functions, products, or services that are not announced or available in your country. Such references do not imply that Teradata Corporation intends to announce such features, functions, products, or s ...
... The information contained in this document may contain references or cross-references to features, functions, products, or services that are not announced or available in your country. Such references do not imply that Teradata Corporation intends to announce such features, functions, products, or s ...
Chapter 5: Other Relational Languages
... the relational algebra. The chapter also provides a brief introduction to integrity constraints. ...
... the relational algebra. The chapter also provides a brief introduction to integrity constraints. ...
Oblivious Querying of Data with Irregular Structure(cont`d)
... • Different query semantics admit different levels of incompleteness ...
... • Different query semantics admit different levels of incompleteness ...
ECP2.1 Upgrade Client
... behavior of ECP across all the supported databases. Oracle and PostgreSQL use case sensitive search by default while MySQL and MSSQL are case insensitive. This can lead to some minor issues during message transportation when the message passes through databases with different case sensitivity. Takin ...
... behavior of ECP across all the supported databases. Oracle and PostgreSQL use case sensitive search by default while MySQL and MSSQL are case insensitive. This can lead to some minor issues during message transportation when the message passes through databases with different case sensitivity. Takin ...
Partner Technical Guide
... VARBYTE - Represents a variable-length binary string. BLOB - Represents a large binary string of raw bytes. A binary large object (BLOB) column can store binary objects, such as graphics, video clips, files, and documents. Character and CLOB Data Types In general, CHARACTER, VARCHAR, and CLOB data t ...
... VARBYTE - Represents a variable-length binary string. BLOB - Represents a large binary string of raw bytes. A binary large object (BLOB) column can store binary objects, such as graphics, video clips, files, and documents. Character and CLOB Data Types In general, CHARACTER, VARCHAR, and CLOB data t ...
The Antelope Relational Database Management System
... MATLAB), a command line interface, and GUI interfaces. These provide a wide range of access methods into databases. ...
... MATLAB), a command line interface, and GUI interfaces. These provide a wide range of access methods into databases. ...
RTI Database Integration Service - RTI Community - Real
... embeddable messaging infrastructure, Connext DDS, and integration and data management standards such as SQL, XML, Web services and JMS. This allows developers to benefit from the performance, scalability, Quality of Service (QoS) control and broad platform support provided by RTI's messaging technol ...
... embeddable messaging infrastructure, Connext DDS, and integration and data management standards such as SQL, XML, Web services and JMS. This allows developers to benefit from the performance, scalability, Quality of Service (QoS) control and broad platform support provided by RTI's messaging technol ...
Chapter 9
... To grant a system or object privilege to every user in the database, grant the privilege to the keyword PUBLIC rather than to a specific user. PUBLIC is a special group in an Oracle database that you can use to make a privilege available quickly to every user in the system. However, use this feature ...
... To grant a system or object privilege to every user in the database, grant the privilege to the keyword PUBLIC rather than to a specific user. PUBLIC is a special group in an Oracle database that you can use to make a privilege available quickly to every user in the system. However, use this feature ...
Database Management System
... (C) The database must contain an unmatched foreign key value. (D) An entity can be joined with another entity in the same level entity set. Ans: (A) Disjoint less constraint requires that an entity belongs to no more than one level entity set. (Disjoint less constraint means that an entity can be a ...
... (C) The database must contain an unmatched foreign key value. (D) An entity can be joined with another entity in the same level entity set. Ans: (A) Disjoint less constraint requires that an entity belongs to no more than one level entity set. (Disjoint less constraint means that an entity can be a ...
Oracle Database Administrator`s Reference for HP OpenVMS Itanium
... any programs installed on the hardware, and/or documentation, delivered to U.S. Government end users are "commercial computer software" pursuant to the applicable Federal Acquisition Regulation and agency-specific supplemental regulations. As such, use, duplication, disclosure, modification, and ada ...
... any programs installed on the hardware, and/or documentation, delivered to U.S. Government end users are "commercial computer software" pursuant to the applicable Federal Acquisition Regulation and agency-specific supplemental regulations. As such, use, duplication, disclosure, modification, and ada ...
Strategies and Techniques for Using Oracle7 Replication
... high transaction rate that also serves as a management reporting system. With replication, the data could be owned and maintained by the transaction system and replicated to another database location that could be specially tailored for read-only management reporting. Disaster Site Maintenance. With ...
... high transaction rate that also serves as a management reporting system. With replication, the data could be owned and maintained by the transaction system and replicated to another database location that could be specially tailored for read-only management reporting. Disaster Site Maintenance. With ...
ADO Connection String Samples
... SYSTEM DSN (not a USER DSN) when using ASP. You can also create the DSN via Visual Basic code. 2) Then use the following connection string - with your own DSN name of course. ...
... SYSTEM DSN (not a USER DSN) when using ASP. You can also create the DSN via Visual Basic code. 2) Then use the following connection string - with your own DSN name of course. ...
Composing Schema Mappings - University of California, Santa Cruz
... “Relational completeness of data base sublanguages”, in: Database Systems, ed. by R. Rustin, 1972. ...
... “Relational completeness of data base sublanguages”, in: Database Systems, ed. by R. Rustin, 1972. ...
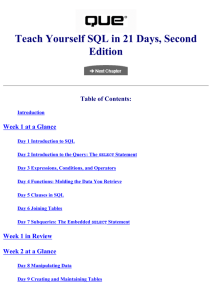
Teach Yourself SQL in 21 Days, Second Edition
... Ryan K. Stephens started using SQL as a programmer/analyst while serving on active duty in the Indiana Army National Guard. Hundreds of programs later, Ryan became a database administrator. He currently works for Unisys Federal Systems, where he is responsible for government-owned databases througho ...
... Ryan K. Stephens started using SQL as a programmer/analyst while serving on active duty in the Indiana Army National Guard. Hundreds of programs later, Ryan became a database administrator. He currently works for Unisys Federal Systems, where he is responsible for government-owned databases througho ...
Relational Databases and Microsoft Access
... However, most students are registered in either a Computer Science major program or the Computer Science minor. Students who enroll in the course obtain: (1) a working knowledge of a personal database system (MS Access), (2) knowledge of SQL (primarily the Select statement), and (3) awareness of con ...
... However, most students are registered in either a Computer Science major program or the Computer Science minor. Students who enroll in the course obtain: (1) a working knowledge of a personal database system (MS Access), (2) knowledge of SQL (primarily the Select statement), and (3) awareness of con ...