Programlama ve Nesneler
... • Common problems with growing complexity – Tracking of variables – Control mechanisms ...
... • Common problems with growing complexity – Tracking of variables – Control mechanisms ...
Database Ex
... Data redundancy can be found in some poorly designed databases. This may affect the data integrity of a database. (a) What is the meaning of data redundancy? Data redundancy means storing the same data in multiple locations. (b) What is the meaning of data integrity? Data integrity means that data a ...
... Data redundancy can be found in some poorly designed databases. This may affect the data integrity of a database. (a) What is the meaning of data redundancy? Data redundancy means storing the same data in multiple locations. (b) What is the meaning of data integrity? Data integrity means that data a ...
data migration from rdbms to hadoop
... Thus, the yield will be in different documents. These documents may be delimited content records or paired . In the wake of controlling the foreign records with Hive we will have an outcome information set which you can then fare back to the social database. ...
... Thus, the yield will be in different documents. These documents may be delimited content records or paired . In the wake of controlling the foreign records with Hive we will have an outcome information set which you can then fare back to the social database. ...
Experiment Management System CSE 423
... Create protocol specification for data to be passed between research collection system and the Experiment Management System (EMS). Design a Database for housing the experiment information Install all required support software for the EMS (OS, Web ...
... Create protocol specification for data to be passed between research collection system and the Experiment Management System (EMS). Design a Database for housing the experiment information Install all required support software for the EMS (OS, Web ...
SYSTEMS ANALYST BASIC FUNCTION
... Routinely monitor data quality and ensures that data integrity issues are being addressed. Completes other projects and related duties as assigned. KNOWLEDGE AND ABILITIES: KNOWLEDGE OF: Relational database concepts, methods and techniques. ERP system structures and reporting methods (SunGard Higher ...
... Routinely monitor data quality and ensures that data integrity issues are being addressed. Completes other projects and related duties as assigned. KNOWLEDGE AND ABILITIES: KNOWLEDGE OF: Relational database concepts, methods and techniques. ERP system structures and reporting methods (SunGard Higher ...
Computer Programming
... programmers check its logic. A logic error is a mistake in the way an algorithm solves a problem. Programmers check their algorithms by inputting test data and checking the logic by hand or with a calculator. ...
... programmers check its logic. A logic error is a mistake in the way an algorithm solves a problem. Programmers check their algorithms by inputting test data and checking the logic by hand or with a calculator. ...
Résumé - Hi. I`m Nimesh Desai.
... ➢ BrokenMyth Studios – Intern Programmer: Worked on development of a 3D Training Simulation developed in C# .NET and Unity3D. Another project was the design and development of an e-learning simulation in ActionScript 3 and Flash. Developed company website using CSS, Javascript and jQuery. (December ...
... ➢ BrokenMyth Studios – Intern Programmer: Worked on development of a 3D Training Simulation developed in C# .NET and Unity3D. Another project was the design and development of an e-learning simulation in ActionScript 3 and Flash. Developed company website using CSS, Javascript and jQuery. (December ...
Database System Concepts and Architecture
... change external schemas or application programs. Physical data independence is the capacity to change the internal schema without having to change the conceptual schema. ...
... change external schemas or application programs. Physical data independence is the capacity to change the internal schema without having to change the conceptual schema. ...
All Definitions for
... 1- provides high level view of data and actions on 1-Presentation or user data interface 2- often using an object data model 3- hides details of data storage schema data access layer 1- interfaces between business logic layer and the underlying database 2- provides mapping from object model of busin ...
... 1- provides high level view of data and actions on 1-Presentation or user data interface 2- often using an object data model 3- hides details of data storage schema data access layer 1- interfaces between business logic layer and the underlying database 2- provides mapping from object model of busin ...
Slide 1
... technology over traditional high level networking techniques. Application distributes, collects and filters data from databases over a heterogeneous distributed system. Application could be used as an API. ...
... technology over traditional high level networking techniques. Application distributes, collects and filters data from databases over a heterogeneous distributed system. Application could be used as an API. ...
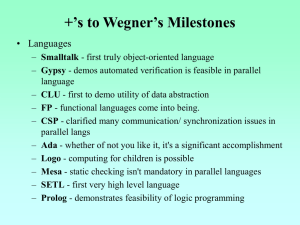
The Introduction to Object
... understand a problem by separating necessary from unnecessary details To define the interface to a data abstraction without specifying implementation detail. ...
... understand a problem by separating necessary from unnecessary details To define the interface to a data abstraction without specifying implementation detail. ...
What is handling information?
... A database is an ordered collection of information which allows searching for specific information and enables individual items to be added and amended. An example of a database is an address book : this contains names, addresses and telephone numbers, normally arranged in alphabetical groups. ...
... A database is an ordered collection of information which allows searching for specific information and enables individual items to be added and amended. An example of a database is an address book : this contains names, addresses and telephone numbers, normally arranged in alphabetical groups. ...
Differential Privacy
... Two Intuitions for Privacy “If the release of statistics S makes it possible to determine the value [of private information] more accurately than is possible without access to S, a disclosure has taken place.” [Dalenius] Learning more about me should be hard Privacy is “protection from being brou ...
... Two Intuitions for Privacy “If the release of statistics S makes it possible to determine the value [of private information] more accurately than is possible without access to S, a disclosure has taken place.” [Dalenius] Learning more about me should be hard Privacy is “protection from being brou ...
cloud computing
... Chicago, Geophysical Center RAS and Space Research Institute RAS have successfully moved 1.4 TB of data in 4.5 hours over a 1 Gbps lightpath between Chicago and Moscow as part of the Teraflow Network initiative • Using NCDM’s open-source UDP-based Data Transfer protocol (UDT), we were able to transf ...
... Chicago, Geophysical Center RAS and Space Research Institute RAS have successfully moved 1.4 TB of data in 4.5 hours over a 1 Gbps lightpath between Chicago and Moscow as part of the Teraflow Network initiative • Using NCDM’s open-source UDP-based Data Transfer protocol (UDT), we were able to transf ...
Resume - UF CISE - University of Florida
... Worked on database integration module which is developed using Hibernate framework. Implemented business logic of system using JSF which produces daily reports on financial transaction performed, usage statistic, admin reports and error logs in various formats. Informatica ‘Extract Transform and ...
... Worked on database integration module which is developed using Hibernate framework. Implemented business logic of system using JSF which produces daily reports on financial transaction performed, usage statistic, admin reports and error logs in various formats. Informatica ‘Extract Transform and ...
PPT - University of Virginia, Department of Computer Science
... iteratively would save time is an obvious and blatant lie.” - p.7 ...
... iteratively would save time is an obvious and blatant lie.” - p.7 ...
1Introduction
... • Additional to disciplinary policies of the institute / university, plagiarism will be strictly dealt with. Cheating any assignment, quiz or exam from any one else may lead to severe penalty of grade. Violation of rules / disturbance in class / involvement in plagiarism may easily lead you to an “F ...
... • Additional to disciplinary policies of the institute / university, plagiarism will be strictly dealt with. Cheating any assignment, quiz or exam from any one else may lead to severe penalty of grade. Violation of rules / disturbance in class / involvement in plagiarism may easily lead you to an “F ...
ODBC-101 - LuisGomez.NET
... Slightly Different steps for each release. These steps are for 2003. Import vs. Link. Queries. Reports. ...
... Slightly Different steps for each release. These steps are for 2003. Import vs. Link. Queries. Reports. ...
SQL Server 7.0 Strategy Deck
... Distributed heterogeneous query support Direct HTTP access into database Multi-tier cache integration with notifications Semi-structured & unstructured search: ...
... Distributed heterogeneous query support Direct HTTP access into database Multi-tier cache integration with notifications Semi-structured & unstructured search: ...
Just-in-time compilation for SQL query processing
... and composable procedural abstractions to evaluate queries. Traditionally, relational database systems have compiled SQL into an intermediate representation: the query plan. The query plan is composed of physical algebraic operators, all communicating through a common interface: the iterator interfa ...
... and composable procedural abstractions to evaluate queries. Traditionally, relational database systems have compiled SQL into an intermediate representation: the query plan. The query plan is composed of physical algebraic operators, all communicating through a common interface: the iterator interfa ...