Data Mining
... The nontrivial extraction of hidden, previously unidentified, and potentially valuable knowledge from data A variety of techniques such as neural networks, decision trees or standard statistical techniques to identify nuggets of information or decision-making knowledge in bodies of data, and extract ...
... The nontrivial extraction of hidden, previously unidentified, and potentially valuable knowledge from data A variety of techniques such as neural networks, decision trees or standard statistical techniques to identify nuggets of information or decision-making knowledge in bodies of data, and extract ...
Questions and Answers
... With hundreds of sophisticated tools for map automation, data conversion, database management, map overlay and spatial analysis, interactive display and query graphic editing, and address geocoding ...
... With hundreds of sophisticated tools for map automation, data conversion, database management, map overlay and spatial analysis, interactive display and query graphic editing, and address geocoding ...
Data Integration - The ETL Process
... A data warehousing process that consists of extraction (i.e., reading data from a database), transformation (i.e., converting the extracted data from its previous form into the form in which it needs to be so that it can be placed into a data warehouse or simply another database), and load (i.e., pu ...
... A data warehousing process that consists of extraction (i.e., reading data from a database), transformation (i.e., converting the extracted data from its previous form into the form in which it needs to be so that it can be placed into a data warehouse or simply another database), and load (i.e., pu ...
Programming Languages
... you into a particular machine and compiler because no one else recognizes those extensions. Why might a compiler developer do that? ...
... you into a particular machine and compiler because no one else recognizes those extensions. Why might a compiler developer do that? ...
Research online and look for three (3) functional programming
... compiled into a format called bytecode, which can then be executed by a Java interpreter. Compiled Java code can run on most computers because Java interpreters and runtime environments exist for most operating systems. C++ is a programming language that was built off the C language. The syntax of C ...
... compiled into a format called bytecode, which can then be executed by a Java interpreter. Compiled Java code can run on most computers because Java interpreters and runtime environments exist for most operating systems. C++ is a programming language that was built off the C language. The syntax of C ...
Dyanmic SQL Field Type
... Populates a drop-down list of choices by querying the REDCap tables using SELECT queries only. The database table being queried must exist in the same MySQL database as the REDCap tables. ONLY REDCap Super Users may add/modify this field type. Advantage of this field type is that it allows you to po ...
... Populates a drop-down list of choices by querying the REDCap tables using SELECT queries only. The database table being queried must exist in the same MySQL database as the REDCap tables. ONLY REDCap Super Users may add/modify this field type. Advantage of this field type is that it allows you to po ...
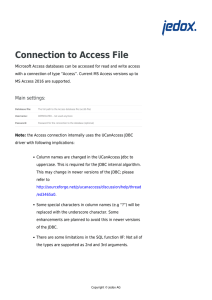
Connection to Access file
... Microsoft Access databases can be accessed for read and write access with a connection of type “Access”. Current MS Access versions up to MS Access 2016 are supported. ...
... Microsoft Access databases can be accessed for read and write access with a connection of type “Access”. Current MS Access versions up to MS Access 2016 are supported. ...
May 11 - 15 Lesson Plan
... 130.277. C.8 The student codes a computer application. The student is expected to: (A) apply programming language concepts; (C) articulate the concept of data representation ...
... 130.277. C.8 The student codes a computer application. The student is expected to: (A) apply programming language concepts; (C) articulate the concept of data representation ...
Three tier achitecture
... – The three-tier architecture supports dataoriented web sites – The open-source XAMPP package contains the necessary software – PHP server scripting is embedded within HTML code to program the system. ...
... – The three-tier architecture supports dataoriented web sites – The open-source XAMPP package contains the necessary software – PHP server scripting is embedded within HTML code to program the system. ...
Data Warehousing
... Transactional systems are optimized primarily for the here and now • They allow for constant change • Don’t record all previous data states ...
... Transactional systems are optimized primarily for the here and now • They allow for constant change • Don’t record all previous data states ...
Logic Programming Languages
... Proposition – a logical statement that may or may not be true Atomic ...
... Proposition – a logical statement that may or may not be true Atomic ...
Model Paper Computer Applications BCOM Part I
... a) A query enables people to enter or view data in your database easily. b) A query summarizes and prints data. c) A query retrieves data that satisfies conditions that you set. d) None of the above Q 3) This type of database contains multiple tables that are connected to produce combined output fro ...
... a) A query enables people to enter or view data in your database easily. b) A query summarizes and prints data. c) A query retrieves data that satisfies conditions that you set. d) None of the above Q 3) This type of database contains multiple tables that are connected to produce combined output fro ...
Data Management File Note
... Investigator to complete this file note if there is no study-specific Data Management SOP. ...
... Investigator to complete this file note if there is no study-specific Data Management SOP. ...
Abstract
... values or relationships. This paper tackles the problem of processing top-K queries over uncertain data with the help of crowdsourcing for quickly converging to the realordering of relevant results. Several offline and online approaches for addressing questions to a crowd are defined and contrasted ...
... values or relationships. This paper tackles the problem of processing top-K queries over uncertain data with the help of crowdsourcing for quickly converging to the realordering of relevant results. Several offline and online approaches for addressing questions to a crowd are defined and contrasted ...
MQP Projects - Rundensteiner
... Futuristic Monitoring Queries … Track a smoke cloud (moving cluster) in terms of its speed and severity ? Find the scope and direction of fire spreads ? Match given sensors readings of fire with a fire stream simulation to determine similarity ? Is this a prank (outlier), or an actual fire ? What p ...
... Futuristic Monitoring Queries … Track a smoke cloud (moving cluster) in terms of its speed and severity ? Find the scope and direction of fire spreads ? Match given sensors readings of fire with a fire stream simulation to determine similarity ? Is this a prank (outlier), or an actual fire ? What p ...
Protection of outsou..
... • Confidenciality constraint c over relation R(A1,…,An) can be a singleton or an association. • c0= {SSN} is a singleton. The values of this attribute should be encrypted. • c1= {Name, Ilness} is an association. The attributes should not appear together as plaintext. ...
... • Confidenciality constraint c over relation R(A1,…,An) can be a singleton or an association. • c0= {SSN} is a singleton. The values of this attribute should be encrypted. • c1= {Name, Ilness} is an association. The attributes should not appear together as plaintext. ...
Oracle Data Mart Suite Tutorial
... columns you want from the source (SQL Query) Transformation: calculation, aggregation, rename etc. Transportation: load data into data mart ...
... columns you want from the source (SQL Query) Transformation: calculation, aggregation, rename etc. Transportation: load data into data mart ...
Introduction to Database Systems CSSE 370 Fall Quarter 2008 SQL
... satisfy the following statements. Feel free to add data to the database to get a result for each query to aid in deciding if it was done correctly. The database can be used to work on the query. When it is correct, cut and paste the resulting SQL statement into a Word document. You will be turning i ...
... satisfy the following statements. Feel free to add data to the database to get a result for each query to aid in deciding if it was done correctly. The database can be used to work on the query. When it is correct, cut and paste the resulting SQL statement into a Word document. You will be turning i ...
Model Paper Computer Application In Business
... a) A query enables people to enter or view data in your database easily. b) A query summarizes and prints data. c) A query retrieves data that satisfies conditions that you set. d) None of the above Q 3) This type of database contains multiple tables that are connected to produce combined output fro ...
... a) A query enables people to enter or view data in your database easily. b) A query summarizes and prints data. c) A query retrieves data that satisfies conditions that you set. d) None of the above Q 3) This type of database contains multiple tables that are connected to produce combined output fro ...
shyamala kunjithapatham - SMAST
... system was coded in Java and HTML. Operating system concepts like CPU scheduling, Page replacement, Disk scheduling were implemented. 7) Library database management system: Development of library database management system in Oracle, with the back end programming in PL/SQL and front end implemented ...
... system was coded in Java and HTML. Operating system concepts like CPU scheduling, Page replacement, Disk scheduling were implemented. 7) Library database management system: Development of library database management system in Oracle, with the back end programming in PL/SQL and front end implemented ...