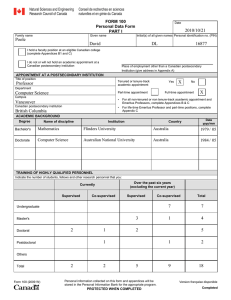
my personal data form - UBC Computer Science
... Invited opening speaker, “Combining logic and probability: a knowledge representation perspective”, Dagstuhl Seminar 05051, Probabilistic, Logical and Relational Learning — Towards a Synthesis, Dagstuhl, Germany, February 2005 Invited speaker, “Relations, generalizations and the reference-class prob ...
... Invited opening speaker, “Combining logic and probability: a knowledge representation perspective”, Dagstuhl Seminar 05051, Probabilistic, Logical and Relational Learning — Towards a Synthesis, Dagstuhl, Germany, February 2005 Invited speaker, “Relations, generalizations and the reference-class prob ...
Call for Participation - Association for the Advancement of Artificial
... after groups of related papers are presented. The emphasis will be understanding issues that are different from traditional AI work and why they are important to solving the knowledge management problem. Three paper copies of papers should be mailed to: Bradley Whitehall, Workshop Chair Johnson Cont ...
... after groups of related papers are presented. The emphasis will be understanding issues that are different from traditional AI work and why they are important to solving the knowledge management problem. Three paper copies of papers should be mailed to: Bradley Whitehall, Workshop Chair Johnson Cont ...
It`s Going to Kill Us! - Information Technology and Innovation
... computing, predicts, “experts of the future will routinely work with learning and reasoning machines to do their day-to-day tasks in a very deep collaborative relationship between people and machines. This is nothing to be fearful of; it is an evolution, and I think it is going to be much better for ...
... computing, predicts, “experts of the future will routinely work with learning and reasoning machines to do their day-to-day tasks in a very deep collaborative relationship between people and machines. This is nothing to be fearful of; it is an evolution, and I think it is going to be much better for ...
"It`s Going to Kill Us!" and Other Myths About the Future of
... computing, predicts, “experts of the future will routinely work with learning and reasoning machines to do their day-to-day tasks in a very deep collaborative relationship between people and machines. This is nothing to be fearful of; it is an evolution, and I think it is going to be much better for ...
... computing, predicts, “experts of the future will routinely work with learning and reasoning machines to do their day-to-day tasks in a very deep collaborative relationship between people and machines. This is nothing to be fearful of; it is an evolution, and I think it is going to be much better for ...
When are tutorial dialogues more effective than reading?
... the opposite of those found by Swanson (1992) and Wood, Wood and Middleton (1978), who also used a high-interaction condition with human tutors who were trained to be interactive. However, in the lowinteraction conditions of the earlier studies, the tutors were instructed to lecture and demonstrate, ...
... the opposite of those found by Swanson (1992) and Wood, Wood and Middleton (1978), who also used a high-interaction condition with human tutors who were trained to be interactive. However, in the lowinteraction conditions of the earlier studies, the tutors were instructed to lecture and demonstrate, ...
Using General-Purpose Planning for Action Selection in
... spoken, non-verbal, and task-based actions should be taken next by the system as a whole. In contrast to more formal, descriptive accounts of dialogue (Asher and Lascarides 2003), which aim to model the full generality of language use, work on interaction management has concentrated primarily on dev ...
... spoken, non-verbal, and task-based actions should be taken next by the system as a whole. In contrast to more formal, descriptive accounts of dialogue (Asher and Lascarides 2003), which aim to model the full generality of language use, work on interaction management has concentrated primarily on dev ...
ppt - MSDL
... identify the primitive components. – Each of the primitive components of a widget are trained with 15-20 examples. – The examples varied in size and drawing direction. 1. Dean Rubine. “The Automatic Recognition of Gestures,” PhD dissertation, Report #CMU-CS-91-202, School of Computer Science, Carneg ...
... identify the primitive components. – Each of the primitive components of a widget are trained with 15-20 examples. – The examples varied in size and drawing direction. 1. Dean Rubine. “The Automatic Recognition of Gestures,” PhD dissertation, Report #CMU-CS-91-202, School of Computer Science, Carneg ...
assessing learning - The Nellie Mae Education Foundation
... research-based understanding of one or more core elements of student-centered approaches to learning. The authors in this series: synthesize and analyze existing research in their areas; identify what is known and where gaps remain related to student-centered approaches to learning; and discuss impl ...
... research-based understanding of one or more core elements of student-centered approaches to learning. The authors in this series: synthesize and analyze existing research in their areas; identify what is known and where gaps remain related to student-centered approaches to learning; and discuss impl ...
The Cambridge Handbook of Artificial Intelligence
... interaction, and foundations of cognitive science. Ron Sun is Professor of Cognitive Sciences at Rensselaer Polytechnic Institute. He is the author of Integrating Rules and Connectionism for Robust Commonsense Reasoning (1994) and Duality of the Mind (2001), and the editor of The Cambridge Handbook ...
... interaction, and foundations of cognitive science. Ron Sun is Professor of Cognitive Sciences at Rensselaer Polytechnic Institute. He is the author of Integrating Rules and Connectionism for Robust Commonsense Reasoning (1994) and Duality of the Mind (2001), and the editor of The Cambridge Handbook ...
A Client-Server Interactive Tool for Integrated
... processing are all essential components of rational agent design, and machine learning techniques are introduced so that the agent can improve performance on tasks with experience. Many studies have been conducted that indicate the value of computer-based multimedia and simulation tools to learning ...
... processing are all essential components of rational agent design, and machine learning techniques are introduced so that the agent can improve performance on tasks with experience. Many studies have been conducted that indicate the value of computer-based multimedia and simulation tools to learning ...
Beyond AI: Multi-Intelligence (MI) Combining Natural and
... leaders and eminent professors that AI can be an existential threat to humanity [1]. However, the framing of much of the debate about AI is narrow and overlooks the potential for multi-intelligence (MI). As summarized in Figure 1, MI concerns multi-intelligence hybrid beings and systems. Examples of ...
... leaders and eminent professors that AI can be an existential threat to humanity [1]. However, the framing of much of the debate about AI is narrow and overlooks the potential for multi-intelligence (MI). As summarized in Figure 1, MI concerns multi-intelligence hybrid beings and systems. Examples of ...
UGrad Handbook 2013-2014
... degrees available to specific disciplines. If a minor will not fit your program of studies, a few or even a single course in computing may be worthwhile addition(s) to your education. Students may declare their intent to enter one of our computer science programs at any point in their course of stu ...
... degrees available to specific disciplines. If a minor will not fit your program of studies, a few or even a single course in computing may be worthwhile addition(s) to your education. Students may declare their intent to enter one of our computer science programs at any point in their course of stu ...
PDF
... autonomous robots. Ambitious projects in this direction are underway, such as the development of a web for robots3, where they would share data and procedures, i.e., maps of visited buildings, acquired manipulation skills, and other learned expertise, in a common hardware-independent format. This we ...
... autonomous robots. Ambitious projects in this direction are underway, such as the development of a web for robots3, where they would share data and procedures, i.e., maps of visited buildings, acquired manipulation skills, and other learned expertise, in a common hardware-independent format. This we ...
University of Bergen - BORA
... many of the characteristics and possibilities of technological devices to be derived from sources that is not representative of the empirical entity. --Humans have attempted to create machines in the image of their own minds and bodies for centuries, and even though robots have not yet overrun human ...
... many of the characteristics and possibilities of technological devices to be derived from sources that is not representative of the empirical entity. --Humans have attempted to create machines in the image of their own minds and bodies for centuries, and even though robots have not yet overrun human ...
The CHREST Architecture of Cognition The Role of
... architectures that closely simulate human behaviour in a variety of domains. Examples of this approach include ACTR (Anderson and Lebière, 1998), Soar (Newell, 1990), and EPAM (Feigenbaum and Simon, 1984). More recently, the computational architecture CHREST (Chunk Hierarchy and REtrieval Structures ...
... architectures that closely simulate human behaviour in a variety of domains. Examples of this approach include ACTR (Anderson and Lebière, 1998), Soar (Newell, 1990), and EPAM (Feigenbaum and Simon, 1984). More recently, the computational architecture CHREST (Chunk Hierarchy and REtrieval Structures ...
pdf
... difficulties in extending formal, symbolic approaches to real-world, embedded systems. It sought to create systems that appeared to be intelligent, without running into the problems associate with AI-completeness. In this section, we reflect on six technical strategies developed in interactionist AI ...
... difficulties in extending formal, symbolic approaches to real-world, embedded systems. It sought to create systems that appeared to be intelligent, without running into the problems associate with AI-completeness. In this section, we reflect on six technical strategies developed in interactionist AI ...
KBMS Requirements of Knowledge
... commercial applications Logic-based systems can also be considered rule-based, where rules and the factual part of the knowledge cannot be distinguished. Our focus then in this section is on rule-based ESs. The commercialization of rule-based ESs has been the source of more research interest, but ne ...
... commercial applications Logic-based systems can also be considered rule-based, where rules and the factual part of the knowledge cannot be distinguished. Our focus then in this section is on rule-based ESs. The commercialization of rule-based ESs has been the source of more research interest, but ne ...
Artificial Intelligence
... Informed Search Games and Adversarial Search Machine Learning & Neural Networks ...
... Informed Search Games and Adversarial Search Machine Learning & Neural Networks ...
Towards a Logic-programming System to Debug ASP Knowledge Bases
... updates of knowledge bases, into a more concise and precise method of updates. In addition to that, it introduces some formal specifications for its implementation on top of an ASP solver called DLV [7], without need to use a total-order semantics. To begin with, one of the latest proposals aiming to ...
... updates of knowledge bases, into a more concise and precise method of updates. In addition to that, it introduces some formal specifications for its implementation on top of an ASP solver called DLV [7], without need to use a total-order semantics. To begin with, one of the latest proposals aiming to ...
Integrating AI Techniques in Requirements Phase: A Literature Review
... Farah NaazRaza focused on techniques, which are developed in AI and their applications in Software Engineering. The researcher proposed a comparative study between the software development and expert system development and also focused that how expert programmers analyze, synthesize, modify, explain ...
... Farah NaazRaza focused on techniques, which are developed in AI and their applications in Software Engineering. The researcher proposed a comparative study between the software development and expert system development and also focused that how expert programmers analyze, synthesize, modify, explain ...
CURRICULUM VITAE Academic Education Academic Employment
... models", Journal of Artificial Intelligence Research, volume 5, pp. 27-52, 1996. 4. Rachel Ben-Eliyahu and Rina Dechter, "On computing minimal models", Annals of Mathematics and Artificial Intelligence, volume 18, pp. 3-27, 1996. 5. Rachel Ben-Eliyahu and Rina Dechter, "Default reasoning using class ...
... models", Journal of Artificial Intelligence Research, volume 5, pp. 27-52, 1996. 4. Rachel Ben-Eliyahu and Rina Dechter, "On computing minimal models", Annals of Mathematics and Artificial Intelligence, volume 18, pp. 3-27, 1996. 5. Rachel Ben-Eliyahu and Rina Dechter, "Default reasoning using class ...
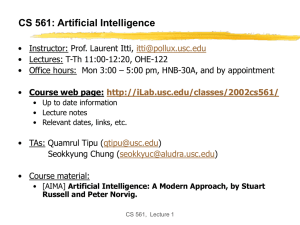
CS 561a: Introduction to Artificial Intelligence
... The right thing: That which is expected to maximize the expected return ...
... The right thing: That which is expected to maximize the expected return ...
CAPTCHA: Using Hard AI Problems For Security
... for practical security, including (but not limited to): – Online Polls. In November 1999, slashdot.com released an online poll asking which was the best graduate school in computer science (a dangerous question to ask over the web!). As is the case with most online polls, IP addresses of voters were ...
... for practical security, including (but not limited to): – Online Polls. In November 1999, slashdot.com released an online poll asking which was the best graduate school in computer science (a dangerous question to ask over the web!). As is the case with most online polls, IP addresses of voters were ...
Captcha
... Bluhm, Nick Hopper and John Langford from Carnegie Mellon School of Computer Science ...
... Bluhm, Nick Hopper and John Langford from Carnegie Mellon School of Computer Science ...
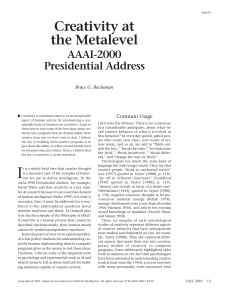
Presidential Address by Bruce Buchanan
... As Johnson-Laird (1999) points out, it is certainly not sufficient: We can be certain that high creativity is not just a matter of “breaking the rules.” … There are many ways to break the rules of any genre: almost all of them are uninteresting and aesthetically unappealing.” Similarly, background k ...
... As Johnson-Laird (1999) points out, it is certainly not sufficient: We can be certain that high creativity is not just a matter of “breaking the rules.” … There are many ways to break the rules of any genre: almost all of them are uninteresting and aesthetically unappealing.” Similarly, background k ...