ITE PC v4.0 Chapter 1 - Marion County Public Schools
... and last addresses cannot be assigned to hosts Loopback address - 127.0.0.1 a special address that hosts use to direct traffic to themselves (addresses 127.0.0.0 to 127.255.255.255 are reserved) Link-Local address - 169.254.0.0 to 169.254.255.255 (169.254.0.0/16) addresses can be automatically a ...
... and last addresses cannot be assigned to hosts Loopback address - 127.0.0.1 a special address that hosts use to direct traffic to themselves (addresses 127.0.0.0 to 127.255.255.255 are reserved) Link-Local address - 169.254.0.0 to 169.254.255.255 (169.254.0.0/16) addresses can be automatically a ...
Class Power Points Gaz on Firewalls for Chapter #10
... Discuss characteristics of NAT and PAT Explain the benefits of NAT Explain how to configure NAT and PAT, including static translation, dynamic translation, and overloading Identify the commands used to verify NAT and PAT configuration List the steps used to troubleshoot NAT and PAT configuration Dis ...
... Discuss characteristics of NAT and PAT Explain the benefits of NAT Explain how to configure NAT and PAT, including static translation, dynamic translation, and overloading Identify the commands used to verify NAT and PAT configuration List the steps used to troubleshoot NAT and PAT configuration Dis ...
dynamic metric in ospf networks
... The massive growth of the Internet has led to increased requirements for reliable network infrastructure. The effectiveness of network communication depends on the ability of routers to determine the best path to send and forward packets to the desired destination. Open Shortest Path First (OSPF) pr ...
... The massive growth of the Internet has led to increased requirements for reliable network infrastructure. The effectiveness of network communication depends on the ability of routers to determine the best path to send and forward packets to the desired destination. Open Shortest Path First (OSPF) pr ...
Lecture 8 - cda college
... ATM High-Speed LAN Access to Servers Alternative when Fast Ethernet no longer able to handle traffic to heavily used LAN servers Benefits of a “server farm” Easy to connect to ATM switches on network backbone Cheaper and easier bandwidth upgrades Easier for administrator to control access to server ...
... ATM High-Speed LAN Access to Servers Alternative when Fast Ethernet no longer able to handle traffic to heavily used LAN servers Benefits of a “server farm” Easy to connect to ATM switches on network backbone Cheaper and easier bandwidth upgrades Easier for administrator to control access to server ...
Avoiding traceroute anomalies with Paris traceroute - Events
... the problem for skitter [7], but they do not report a solution. In practice, the arts++ tool for reading skitter data reports only the first address obtained for each hop. With Rocketfuel [8], Spring et al. attribute a lower confidence level to links inferred from hops that respond with multiple addre ...
... the problem for skitter [7], but they do not report a solution. In practice, the arts++ tool for reading skitter data reports only the first address obtained for each hop. With Rocketfuel [8], Spring et al. attribute a lower confidence level to links inferred from hops that respond with multiple addre ...
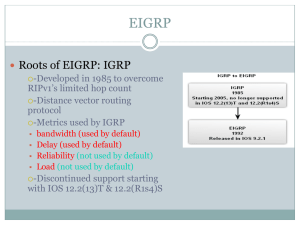
EIGRP
... a route becomes unavailable, DUAL will search its topology table for a valid backup path. • If one exists, that route is immediately entered into the routing table. • If one does not exist, DUAL performs a network discovery process to see if there happens to be a backup path that did not meet the re ...
... a route becomes unavailable, DUAL will search its topology table for a valid backup path. • If one exists, that route is immediately entered into the routing table. • If one does not exist, DUAL performs a network discovery process to see if there happens to be a backup path that did not meet the re ...
HP 12500 Switch Series
... Compartmentalization • Department protection: using network virtualization standards (QinQ, VRF, and MPLS), the 12500 switch allows organizations to isolate different business units with different resources (VRFs); using standard-based mechanisms, the network is completely virtualized, reducing cost ...
... Compartmentalization • Department protection: using network virtualization standards (QinQ, VRF, and MPLS), the 12500 switch allows organizations to isolate different business units with different resources (VRFs); using standard-based mechanisms, the network is completely virtualized, reducing cost ...
IPv6: New Plumbing for the Internet
... • IPv6 is a patch to IPv4 with more addresses • Flag Day for IPv6 activation to be announced • The drive for IPv6 starts in the backbone/Telco • IPv6 is too complex, it can break IPv4 networks ...
... • IPv6 is a patch to IPv4 with more addresses • Flag Day for IPv6 activation to be announced • The drive for IPv6 starts in the backbone/Telco • IPv6 is too complex, it can break IPv4 networks ...
draft-tosca-nfv-v1.0-wd04-rev05-ChangeMark
... any patent claims that would necessarily be infringed by implementations of this specification by a patent holder that is not willing to provide a license to such patent claims in a manner consistent with the IPR Mode of the OASIS Technical Committee that produced this specification. OASIS may inclu ...
... any patent claims that would necessarily be infringed by implementations of this specification by a patent holder that is not willing to provide a license to such patent claims in a manner consistent with the IPR Mode of the OASIS Technical Committee that produced this specification. OASIS may inclu ...
Class Power Points Gaz on NAT and PAT for Chapter #10
... Discuss characteristics of NAT and PAT Explain the benefits of NAT Explain how to configure NAT and PAT, including static translation, dynamic translation, and overloading Identify the commands used to verify NAT and PAT configuration List the steps used to troubleshoot NAT and PAT configuration Dis ...
... Discuss characteristics of NAT and PAT Explain the benefits of NAT Explain how to configure NAT and PAT, including static translation, dynamic translation, and overloading Identify the commands used to verify NAT and PAT configuration List the steps used to troubleshoot NAT and PAT configuration Dis ...
Hash-Based IP Traceback - Events
... Figure 1: An attack graph containing attack paths for two identical packets injected by A1 and A2 and received by the victim, V . The arrows indicate links traversed by the packet; nodes on an attack path are shaded: {A1 , R1 , R4 , R7 , R9 , V } and {A2 , R2 , R5 , R7 , R9 , V }. ...
... Figure 1: An attack graph containing attack paths for two identical packets injected by A1 and A2 and received by the victim, V . The arrows indicate links traversed by the packet; nodes on an attack path are shaded: {A1 , R1 , R4 , R7 , R9 , V } and {A2 , R2 , R5 , R7 , R9 , V }. ...
ppt
... • Many Service Providers have deployed IPv4 MPLS backbone for various reasons. • Here IPv6 can be deployed without upgrading MPLS core. • The edge routers of MPLS backbone should be dual stacked. • Native IPv6 MPLS require full network upgrade. ...
... • Many Service Providers have deployed IPv4 MPLS backbone for various reasons. • Here IPv6 can be deployed without upgrading MPLS core. • The edge routers of MPLS backbone should be dual stacked. • Native IPv6 MPLS require full network upgrade. ...
MPLS QoS - Lyle School of Engineering
... • 6 bits used for Differentiated Service Code Point (DSCP) and determine PHB that the packet will receive • 2 bits are currently unused ...
... • 6 bits used for Differentiated Service Code Point (DSCP) and determine PHB that the packet will receive • 2 bits are currently unused ...
OfficeServ 7400 GWIMT/GWIM User Manual
... − GWIMT: 3-10/100/1000 Ethernet ports: For WAN or LAN interfaces − GWIM: 3-Gigabit Ethernet ports: For WAN or LAN interfaces − 2-Serial WAN ports: For hooking up data private lines via a DSU or CSU which supports V.35 1 port or HSSI 1 ...
... − GWIMT: 3-10/100/1000 Ethernet ports: For WAN or LAN interfaces − GWIM: 3-Gigabit Ethernet ports: For WAN or LAN interfaces − 2-Serial WAN ports: For hooking up data private lines via a DSU or CSU which supports V.35 1 port or HSSI 1 ...
Chapter27(IPv6 and ICMPv6)
... RARP, and IGMP, were either deleted or included in the ICMP protocol. Routing protocols, such as RIP and OSPF, were also slightly modified to accommodate these changes. ...
... RARP, and IGMP, were either deleted or included in the ICMP protocol. Routing protocols, such as RIP and OSPF, were also slightly modified to accommodate these changes. ...
Integrating Cisco Press Resources into the
... • Link-state routing algorithms, also known as shortest path first (SPF) algorithms, build a complex database of topology information – The algorithms compute the shortest path between nodes – Maintains full knowledge of distant routers and how they interconnect www.ciscopress.com ...
... • Link-state routing algorithms, also known as shortest path first (SPF) algorithms, build a complex database of topology information – The algorithms compute the shortest path between nodes – Maintains full knowledge of distant routers and how they interconnect www.ciscopress.com ...
“Networking is IPC”: A Guiding Principle to a
... • if found2 , establish the communication channel and allocate resources required to meet the desired properties3 , ...
... • if found2 , establish the communication channel and allocate resources required to meet the desired properties3 , ...
MPLS Bandwidth Assured Layer 2 Services
... • Transparent LAN service (pointto-point TLS or EWS - EoMPLS) • VPLS • Switched backbone • Point-to-point TLS (Ethernet Wire Service) • Multipoint TLS over L2 core (EMS) • Ethernet access into MPLS/VPN supported in the MPLS VPN Application MPLS Oct Announcement ...
... • Transparent LAN service (pointto-point TLS or EWS - EoMPLS) • VPLS • Switched backbone • Point-to-point TLS (Ethernet Wire Service) • Multipoint TLS over L2 core (EMS) • Ethernet access into MPLS/VPN supported in the MPLS VPN Application MPLS Oct Announcement ...
ppt
... “In telecommunications, connectionless describes communication between two network end points in which a message can be sent from one end point to another without prior arrangement. The device at one end of the communication transmits data to the other, without first ensuring that the recipient is a ...
... “In telecommunications, connectionless describes communication between two network end points in which a message can be sent from one end point to another without prior arrangement. The device at one end of the communication transmits data to the other, without first ensuring that the recipient is a ...
PDF
... For flexibility, the EHWIC includes one SFP slot, which supports a Cisco SFP (see Table 1 later in this document) and a copper RJ-45 port, where either the SFP port (operating at 100/1000 Mbps) or the RJ-45 (operating at 10/100/1000 Mbps) port can be active at one time. The SFP port supports digital ...
... For flexibility, the EHWIC includes one SFP slot, which supports a Cisco SFP (see Table 1 later in this document) and a copper RJ-45 port, where either the SFP port (operating at 100/1000 Mbps) or the RJ-45 (operating at 10/100/1000 Mbps) port can be active at one time. The SFP port supports digital ...
BACnet in China
... • BACnet’s advantage is that the same protocol can operate at multiple levels ― from the field, to the automation and up to the enterprise • At the automation level there are operator workstations, building controllers and advanced application controllers running BACnet/IP • At the field level there ...
... • BACnet’s advantage is that the same protocol can operate at multiple levels ― from the field, to the automation and up to the enterprise • At the automation level there are operator workstations, building controllers and advanced application controllers running BACnet/IP • At the field level there ...
CS610 Final term MAGA file.. all paperz are in 1 file
... communicate and exchange information. The PDU information is only read by the peer layer on the receiving device and then stripped off, and data is handed over to the next upper layer. FINALTERM EXAMINATION Fall 2008 CS610- Computer Network Ref No: 325806 Time: 120 min Marks: 70 Question No: 1 ( Mar ...
... communicate and exchange information. The PDU information is only read by the peer layer on the receiving device and then stripped off, and data is handed over to the next upper layer. FINALTERM EXAMINATION Fall 2008 CS610- Computer Network Ref No: 325806 Time: 120 min Marks: 70 Question No: 1 ( Mar ...