Document
... – Downstream routers make an “all nodes” multicast – All clients get new IP addresses – IPv6 address changes rare but normal ...
... – Downstream routers make an “all nodes” multicast – All clients get new IP addresses – IPv6 address changes rare but normal ...
Session MI.1 - PW/MPLS
... Scale VLL and VPLS services over a multi-area network or between providers Remove the need for a full mesh of Targeted LDP sessions between PEs Remove the need for a full mesh of RSVP-TE tunnels between PEs Minimise number of tunnels terminating on access/aggregation 4 | PW/MPLS | April 2008 ...
... Scale VLL and VPLS services over a multi-area network or between providers Remove the need for a full mesh of Targeted LDP sessions between PEs Remove the need for a full mesh of RSVP-TE tunnels between PEs Minimise number of tunnels terminating on access/aggregation 4 | PW/MPLS | April 2008 ...
The Internet and Its Uses
... •If a device detects a signal from another device, it waits before attempting to transmit. •When there is no traffic detected, a device transmits its message. •While this transmission is occurring, the device continues to listen for traffic on the LAN. •After the message is sent, the device returns ...
... •If a device detects a signal from another device, it waits before attempting to transmit. •When there is no traffic detected, a device transmits its message. •While this transmission is occurring, the device continues to listen for traffic on the LAN. •After the message is sent, the device returns ...
Business Roles and Architecture to realize MUSE
... Centralized subscriber and QoS policy system is distributed in a few Super Nodes, which are used to configure and push necessary policy data to the Border Nodes (ANs & ENs). A virtual control network is created between the Super Nodes & the Border Nodes. Some aspects of the local resource quota for ...
... Centralized subscriber and QoS policy system is distributed in a few Super Nodes, which are used to configure and push necessary policy data to the Border Nodes (ANs & ENs). A virtual control network is created between the Super Nodes & the Border Nodes. Some aspects of the local resource quota for ...
PDF - Complete Book (2.34 MB)
... You apply the per-topology configuration in router address family configuration mode of the global routing process (router configuration mode). The address family and subaddress family are specified when the device enters address family configuration mode. You specify the topology name and topology ...
... You apply the per-topology configuration in router address family configuration mode of the global routing process (router configuration mode). The address family and subaddress family are specified when the device enters address family configuration mode. You specify the topology name and topology ...
Ch-5 Presentation
... This situation is analogous to a number of cars all trying to access a one-lane road at the same time. Because the road has only one lane, only one car can access it at a time. The introduction of hubs into a network resulted in more users competing for the same bandwidth. Collisions are a by-produc ...
... This situation is analogous to a number of cars all trying to access a one-lane road at the same time. Because the road has only one lane, only one car can access it at a time. The introduction of hubs into a network resulted in more users competing for the same bandwidth. Collisions are a by-produc ...
PDF
... an additive to the path’s composite metric. Higher jitter or higher energy usage will result in paths which are worse than those paths that either do not monitor these attributes, or which have lower values. EIGRP will not send these attributes if the router does not provide them. If the attributes ...
... an additive to the path’s composite metric. Higher jitter or higher energy usage will result in paths which are worse than those paths that either do not monitor these attributes, or which have lower values. EIGRP will not send these attributes if the router does not provide them. If the attributes ...
Slides for Chapter 3: Networking and
... Protocols at this level transmit data in a network representation that is independent of the representations used in individual computers, which may differ. Encryption is also performed in this layer, if required. At this level reliability and adaptation are performed, such as detection of failures ...
... Protocols at this level transmit data in a network representation that is independent of the representations used in individual computers, which may differ. Encryption is also performed in this layer, if required. At this level reliability and adaptation are performed, such as detection of failures ...
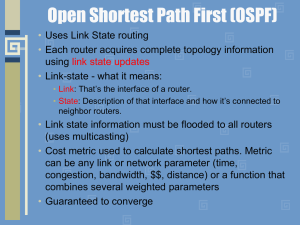
module10b
... network it doesn't know about. The other neighbor replies with the LSUs (Link State Updates) which contain information about requested links. After all the requested information has been received, the other neighbor goes through the same process • Full state (adjacency) - both routers have the synch ...
... network it doesn't know about. The other neighbor replies with the LSUs (Link State Updates) which contain information about requested links. After all the requested information has been received, the other neighbor goes through the same process • Full state (adjacency) - both routers have the synch ...
DutyCon: A dynamic duty-cycle control approach to end
... disjoint flows. In the disjoint flow model, the set of nodes on the route of one flow is disjoint with that of any other flow. Disjoint flows are widely used in multipath routing to enhance the system’s fault tolerance [Wang et al. 2009; Maimour 2008]. The second type of topology is tree-based topol ...
... disjoint flows. In the disjoint flow model, the set of nodes on the route of one flow is disjoint with that of any other flow. Disjoint flows are widely used in multipath routing to enhance the system’s fault tolerance [Wang et al. 2009; Maimour 2008]. The second type of topology is tree-based topol ...
MIDAS 4x System Design 1.5 MB
... See the Comtech EF Data website at http://www.comtechefdata.com for contact information for a Factory Authorized Service Center. Contact the Factory Authorized Service Center for: • Product support • Information on upgrading or returning a product Contact the Comtech EF Data Customer Support Depart ...
... See the Comtech EF Data website at http://www.comtechefdata.com for contact information for a Factory Authorized Service Center. Contact the Factory Authorized Service Center for: • Product support • Information on upgrading or returning a product Contact the Comtech EF Data Customer Support Depart ...
6LoWPAN: The Wireless Embedded Internet
... the Copyright, Designs and Patents Act 1988. All rights reserved. No part of this publication may be reproduced, stored in a retrieval system, or transmitted, in any form or by any means, electronic, mechanical, photocopying, recording or otherwise, except as permitted by the UK Copyright, Designs a ...
... the Copyright, Designs and Patents Act 1988. All rights reserved. No part of this publication may be reproduced, stored in a retrieval system, or transmitted, in any form or by any means, electronic, mechanical, photocopying, recording or otherwise, except as permitted by the UK Copyright, Designs a ...
ATF_Best Practice Design for an Avaya Fabric Connect Campus
... Avoid putting CVLANs on NNI ports Except where needed during conventional network to Fabric migration Network Edge connectivity and protection Spanning Tree Fast Learning or MSTP Edge-Port SLPP and SLPP Guard Can use SLPP even in some non-traditional locations VLACP Use is optional, ...
... Avoid putting CVLANs on NNI ports Except where needed during conventional network to Fabric migration Network Edge connectivity and protection Spanning Tree Fast Learning or MSTP Edge-Port SLPP and SLPP Guard Can use SLPP even in some non-traditional locations VLACP Use is optional, ...
LABEL SPACE REDUCTION IN GMPLS AND ALL-OPTICAL LABEL SWAPPING NETWORKS
... Generic Multi-Protocol Label Switching (GMPLS) protocol, and many standards have been settled up to that point so far. The tendency of adopting GMPLS as the protocol leading the control plane had motivated many vendors to deployed most of GMPLS functionalities directly “burn-in” chip, as a way to sp ...
... Generic Multi-Protocol Label Switching (GMPLS) protocol, and many standards have been settled up to that point so far. The tendency of adopting GMPLS as the protocol leading the control plane had motivated many vendors to deployed most of GMPLS functionalities directly “burn-in” chip, as a way to sp ...
Cookbook for IPv6 Renumbering in ISP and Enterprise
... Our main focus in this document is to report the findings of experiments in enterprise renumbering For Münster, renumbering of DNS and server undertaken at Southampton and Münster. subnets/links (and applications) are considered. For Southampton, a complete enterprise renumbeing is effected, which i ...
... Our main focus in this document is to report the findings of experiments in enterprise renumbering For Münster, renumbering of DNS and server undertaken at Southampton and Münster. subnets/links (and applications) are considered. For Southampton, a complete enterprise renumbeing is effected, which i ...
Ch05 ver 1.1
... Example 5.19 Figure 5.24 shows the same network in Figure 5.23 after subnetting. The whole network is still connected to the Internet through the same router. However, the network has used a private router to divide the network into four subnetworks. The rest of the Internet still sees only one net ...
... Example 5.19 Figure 5.24 shows the same network in Figure 5.23 after subnetting. The whole network is still connected to the Internet through the same router. However, the network has used a private router to divide the network into four subnetworks. The rest of the Internet still sees only one net ...
Lab – Configuring Dynamic and Static NAT (Instructor Version)
... Inside global / local: ________________ 1034, answers will vary. Outside global / local: ________________ 23 d. Because static NAT was configured for PC-A, verify that pinging from ISP to PC-A at the static NAT public address (209.165.200.225) is successful. e. On the Gateway router, display the NAT ...
... Inside global / local: ________________ 1034, answers will vary. Outside global / local: ________________ 23 d. Because static NAT was configured for PC-A, verify that pinging from ISP to PC-A at the static NAT public address (209.165.200.225) is successful. e. On the Gateway router, display the NAT ...
Intelligent Environments
... Every bit requires a full 60 Hertz cycle and thus the X10 transmission rate is limited to only 60 bps Usually a complete X10 command consists of two packets with a 3 cycle gap between each packet ...
... Every bit requires a full 60 Hertz cycle and thus the X10 transmission rate is limited to only 60 bps Usually a complete X10 command consists of two packets with a 3 cycle gap between each packet ...
8.2.5.4 Lab – Identifying IPv6 Addresses
... Select the item Internet Protocol Version 6 (TCP/IPv6) and click Properties. You should see the IPv6 settings for your network interface. Your IPv6 properties window is likely set to Obtain an IPv6 address automatically. This does not mean that IPv6 relies on the Dynamic Host Configuration Protocol ...
... Select the item Internet Protocol Version 6 (TCP/IPv6) and click Properties. You should see the IPv6 settings for your network interface. Your IPv6 properties window is likely set to Obtain an IPv6 address automatically. This does not mean that IPv6 relies on the Dynamic Host Configuration Protocol ...