ITS Communications Update.
... – The error rate for vehicle safety data communications probably needs to be better than 10-7 – To achieve this error rate, safety data messages should be sent using at least two different media with substantially different characteristics, e.g., microwave (5.9 GHz) and millimeter (62-63 GHz) ...
... – The error rate for vehicle safety data communications probably needs to be better than 10-7 – To achieve this error rate, safety data messages should be sent using at least two different media with substantially different characteristics, e.g., microwave (5.9 GHz) and millimeter (62-63 GHz) ...
Ch10
... sent, and information on IP activity and addressing. 17. Describe a rod antenna and its RF patter. The type of antenna that is most typically used on a wireless LAN is a rod antenna. A rod antenna for an access point looks like a slim rod approximately half an inch in diameter and may vary in length ...
... sent, and information on IP activity and addressing. 17. Describe a rod antenna and its RF patter. The type of antenna that is most typically used on a wireless LAN is a rod antenna. A rod antenna for an access point looks like a slim rod approximately half an inch in diameter and may vary in length ...
1 - nptel
... Many of the signals encountered in practice behave randomly in part or as a whole in the sense that they cannot be explicitly described by deterministic mathematical functions such as a sinusoid or an exponential function. Randomness arises because of the random nature of the generation mechanism. S ...
... Many of the signals encountered in practice behave randomly in part or as a whole in the sense that they cannot be explicitly described by deterministic mathematical functions such as a sinusoid or an exponential function. Randomness arises because of the random nature of the generation mechanism. S ...
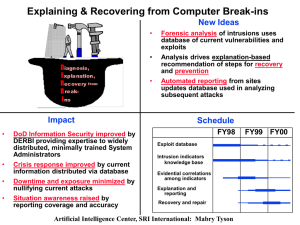
Talk2 - Computer Science
... qualification as attacks. Excellent at detecting known attacks. Requires the signatures to be created and entered into the sensor’s database before operation. May generate false alarms (False Positives). Problem: ...
... qualification as attacks. Excellent at detecting known attacks. Requires the signatures to be created and entered into the sensor’s database before operation. May generate false alarms (False Positives). Problem: ...
CATCHING EXCEPTIONS
... • - Passed into a process • - Errors that happen internal to a process • - User-defined signals ...
... • - Passed into a process • - Errors that happen internal to a process • - User-defined signals ...
PPT26 - SOEST
... in frequency. That is, an integrator should modify the spectrum by -6dB/octave. Thus, to integrate a signal, all you need to do it to move it to the frequency domain, subtract 6 dB/octave (with 0 dB at =1) and return to the time domain. Similarly, to differentiate a signal, ADD 6dB/octave in the fr ...
... in frequency. That is, an integrator should modify the spectrum by -6dB/octave. Thus, to integrate a signal, all you need to do it to move it to the frequency domain, subtract 6 dB/octave (with 0 dB at =1) and return to the time domain. Similarly, to differentiate a signal, ADD 6dB/octave in the fr ...
Types of Surveillance Technology Currently Used by Governments
... Aggregates numerous government watch-lists In 2005, TSDB had over 200,000 names, ranging from known terrorists to persons suspected of having some ties to terrorism Each name receives one of 28 codes, describing person’s connection to terrorism Names are categorized according to the actions users sh ...
... Aggregates numerous government watch-lists In 2005, TSDB had over 200,000 names, ranging from known terrorists to persons suspected of having some ties to terrorism Each name receives one of 28 codes, describing person’s connection to terrorism Names are categorized according to the actions users sh ...
9/13 Binary Numbers, Digital Signals, & Binary Code
... • Codes (lookup tables) in the computer. • Each character corresponds to a byte. • As we type, the keystrokes are translated into bytes by the computer. • The computer reverse-translates to show the characters on the monitor. • Common code sets: ASCII, UNICODE, EBCDIC ...
... • Codes (lookup tables) in the computer. • Each character corresponds to a byte. • As we type, the keystrokes are translated into bytes by the computer. • The computer reverse-translates to show the characters on the monitor. • Common code sets: ASCII, UNICODE, EBCDIC ...
DOWNLOAD FULL SEMINAR TOPICS ON `Portable wireless eye
... HCIs can be divided into cortical (all interfaces that exploit information collected from the human brain cortical relays) and non-cortical (all interfaces that do not access the signals generated by the human cortex directly). In the present study, we describe a novel portable wireless eye movemen ...
... HCIs can be divided into cortical (all interfaces that exploit information collected from the human brain cortical relays) and non-cortical (all interfaces that do not access the signals generated by the human cortex directly). In the present study, we describe a novel portable wireless eye movemen ...
Melissa Freeman
... but instant and text messaging are not addressed Instant messages are typically archived by service providers Text messages are sometimes saved on servers, but only temporarily ...
... but instant and text messaging are not addressed Instant messages are typically archived by service providers Text messages are sometimes saved on servers, but only temporarily ...
Multiple Intelligence - Include
... • Highly developed oral and written communication skills • Knowledge of grammar rules and when it is appropriate to disregard those rules • Sensitivity to the musical qualities and rhythms of words • Knowledge of the many different uses for language, such as persuasion, information, or pleasure ...
... • Highly developed oral and written communication skills • Knowledge of grammar rules and when it is appropriate to disregard those rules • Sensitivity to the musical qualities and rhythms of words • Knowledge of the many different uses for language, such as persuasion, information, or pleasure ...
MultipleIntelligences
... •Able to express what is on your mind (it’s easy to communicate) •Adept with words • “Word Smart” ...
... •Able to express what is on your mind (it’s easy to communicate) •Adept with words • “Word Smart” ...
Trudi NIIR №2 2011
... Analysis of process of voice signal transmission through new generation distributed packet network with losses. Keywords: voice message transmission; quality of voice transmission; next generation network (NGN); hierarchic requirements to quality of service; multiprotocol label switching (MPLS L3VPN ...
... Analysis of process of voice signal transmission through new generation distributed packet network with losses. Keywords: voice message transmission; quality of voice transmission; next generation network (NGN); hierarchic requirements to quality of service; multiprotocol label switching (MPLS L3VPN ...
Analog Signals
... • A lot of our personal world is transmitted digitally in our cellphones: texts, selfies, and emails, but are all waves digital? • Lets see what Tim and Moby have to say about this • https://www.brainpop.com/technolog y/scienceandindustry/analoganddigita lrecording/ ...
... • A lot of our personal world is transmitted digitally in our cellphones: texts, selfies, and emails, but are all waves digital? • Lets see what Tim and Moby have to say about this • https://www.brainpop.com/technolog y/scienceandindustry/analoganddigita lrecording/ ...
Journal Information Sheet - Society for Industrial and Applied
... Provides coverage of the most significant work taking place in the mathematical and formal aspects of computer science and nonnumerical computing. Topics include but are not limited to analysis and design of algorithms, algorithmic game theory, data structures, computational complexity, computationa ...
... Provides coverage of the most significant work taking place in the mathematical and formal aspects of computer science and nonnumerical computing. Topics include but are not limited to analysis and design of algorithms, algorithmic game theory, data structures, computational complexity, computationa ...
Verbal Attestation of Standard form SF
... oral communications, that is classified under the standards of Executive Order 12356, or under any other Executive order or statute that prohibits the unauthorized disclosure of information in the interest of national security; and unclassified information that meets the standards of classification ...
... oral communications, that is classified under the standards of Executive Order 12356, or under any other Executive order or statute that prohibits the unauthorized disclosure of information in the interest of national security; and unclassified information that meets the standards of classification ...
customized Microsoft Word 2007 chapter abstract template
... Keywords: keyword1; keyword2; keyword3; keyword4; keyword5 ...
... Keywords: keyword1; keyword2; keyword3; keyword4; keyword5 ...
Gardner’s EIGHT INTELLIGENCES
... • is the ability to use one's mental abilities to coordinate one's own bodily movements. This intelligence challenges the popular belief that mental and physical activity are unrelated. • The ability to use your body skillfully to solve problems, create products or present ideas and emotions. • An a ...
... • is the ability to use one's mental abilities to coordinate one's own bodily movements. This intelligence challenges the popular belief that mental and physical activity are unrelated. • The ability to use your body skillfully to solve problems, create products or present ideas and emotions. • An a ...
Document
... Issues with just increasing frequency: Increasing frequency requires increase in processing speed → higher cost → 3.2 GHz CPU costs more than 2.4 GHz CPU → e.g., Intel Core 2 Another key factor: wireless → above 10 GHz requires line-of-sight (LOS) ...
... Issues with just increasing frequency: Increasing frequency requires increase in processing speed → higher cost → 3.2 GHz CPU costs more than 2.4 GHz CPU → e.g., Intel Core 2 Another key factor: wireless → above 10 GHz requires line-of-sight (LOS) ...
... What is the basic difference between coherent binary FSK and non-coherent binary FSK (i.e. what does coherent or non-coherent mean)? Please draw the block diagram of the binary FSK receiver for coherent and non-coherent binary FSK respectively. (4%) (c) Considering the coherent binary FSK system, as ...
MULTIPLE INTELLIGENCES (2)
... Other intelligences • Existential Intelligence (cosmic smart): The ability to be sensitive to, or have the capacity for, conceptualizing or tackling deeper or larger questions about human existence. • In the Moral Intelligence of Children, Robert Coles (1997) notes that it is not enough for childre ...
... Other intelligences • Existential Intelligence (cosmic smart): The ability to be sensitive to, or have the capacity for, conceptualizing or tackling deeper or larger questions about human existence. • In the Moral Intelligence of Children, Robert Coles (1997) notes that it is not enough for childre ...
Physical layer
... voice not very sensitive to most noise and distortion; for this and other reasons, local telco loops not well suited to modern data networks However, the local telco networks are one of few comm. links between homes, businesses and rest of the world Structure of U S Telephone networks /companies l ...
... voice not very sensitive to most noise and distortion; for this and other reasons, local telco loops not well suited to modern data networks However, the local telco networks are one of few comm. links between homes, businesses and rest of the world Structure of U S Telephone networks /companies l ...
Signals intelligence

Signals intelligence (SIGINT) is intelligence-gathering by interception of signals, whether communications between people (communications intelligence—abbreviated to COMINT) or from electronic signals not directly used in communication (electronic intelligence—abbreviated to ELINT). Signals intelligence is a subset of intelligence collection management.As sensitive information is often encrypted, signals intelligence often involves the use of cryptanalysis to decipher the messages. Traffic analysis—the study of who is signaling whom and in what quantity—is also used to derive information.