Intruders and password protection
... Proactive password checker techniques Markov model: generation of guessable passwords, this model shows a language consisting of an alphabet of three characters. The state of the system at any time is the identity of the most recent letter. The value on the transition from one state to another rep ...
... Proactive password checker techniques Markov model: generation of guessable passwords, this model shows a language consisting of an alphabet of three characters. The state of the system at any time is the identity of the most recent letter. The value on the transition from one state to another rep ...
RADIUS Implementation and Deployment Best Practices
... RADIUS Access-Request messages sent by RADIUS clients are not authenticated By default, there is no cryptographic verification of the incoming Access-Request message by the RADIUS server. The RADIUS server verifies that the message originated from an IP address for a configured RADIUS client, but so ...
... RADIUS Access-Request messages sent by RADIUS clients are not authenticated By default, there is no cryptographic verification of the incoming Access-Request message by the RADIUS server. The RADIUS server verifies that the message originated from an IP address for a configured RADIUS client, but so ...
Win2003 Active Directory
... network resource information such as users, printers, files, applications, and even other services. ...
... network resource information such as users, printers, files, applications, and even other services. ...
SNMP (Simple Network Management Protocol)
... •optimized for specific hardware platform and OS •this optimization results in less overhead (memory and system resources) and quicker execution ...
... •optimized for specific hardware platform and OS •this optimization results in less overhead (memory and system resources) and quicker execution ...
LogMeIn Security – an In-Depth Look
... fact, desirable. The real problem is that users do not immediately see the threat inherent in other network-enabled applications, such as an email client, a web server or the operating system itself. Many operating systems include some sort of remote access solution by default. Windows 2000 and 2003 ...
... fact, desirable. The real problem is that users do not immediately see the threat inherent in other network-enabled applications, such as an email client, a web server or the operating system itself. Many operating systems include some sort of remote access solution by default. Windows 2000 and 2003 ...
Slide 1
... • Domain and forest functional levels are new features of Windows Server 2008. – The levels defined for each of these are based on the type of server operating systems that are required by the Active Directory design. – The Windows Server 2003 forest functional level is the highest functional level ...
... • Domain and forest functional levels are new features of Windows Server 2008. – The levels defined for each of these are based on the type of server operating systems that are required by the Active Directory design. – The Windows Server 2003 forest functional level is the highest functional level ...
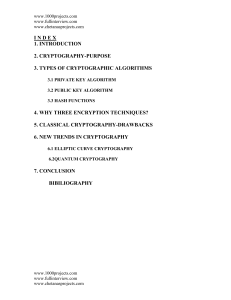
6.1. Elliptic Curve Cryptography
... respective focus on manageability has automated many tasks and simplified administrative functions through easy-to-use interfaces developed through years of customer feedback..And at the end of the document we can conclude that soon we can save secrecy involved in message passing from the dangerous ...
... respective focus on manageability has automated many tasks and simplified administrative functions through easy-to-use interfaces developed through years of customer feedback..And at the end of the document we can conclude that soon we can save secrecy involved in message passing from the dangerous ...
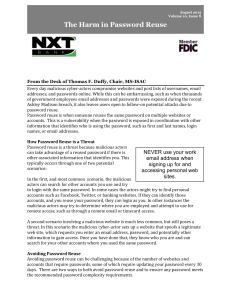
Password Security
... The second technique is to choose a repeatable pattern for your password, such as choosing a sentence that incorporates something unique about the website or account, and then using the first letter of each word as your password. For example the sentence: "This is my August password for the Center f ...
... The second technique is to choose a repeatable pattern for your password, such as choosing a sentence that incorporates something unique about the website or account, and then using the first letter of each word as your password. For example the sentence: "This is my August password for the Center f ...
Click for PDF - Cyber Security Services
... Implementing the Top 4 mitigation strategies can be achieved gradually, firstly on workstations of users who are most likely to be targeted by cyber intrusions, and then implementing them on all workstations and servers. Once this is achieved, organisations can selectively ...
... Implementing the Top 4 mitigation strategies can be achieved gradually, firstly on workstations of users who are most likely to be targeted by cyber intrusions, and then implementing them on all workstations and servers. Once this is achieved, organisations can selectively ...
Security of Cookies in a computer lab setting
... • Disable cookies completely – Provides high security because no cookies are formed – Takes away from the “Full Web Experience” ...
... • Disable cookies completely – Provides high security because no cookies are formed – Takes away from the “Full Web Experience” ...
The Pros and Cons of Open Source Security
... Websites can easily block content originating from a Tor node because the IP addresses of all Tor nodes are easy to obtain through Tor’s own directory servers which are necessary to inform the network about other Tor nodes. All a website administrator has to do is create a simple rule to query a Tor ...
... Websites can easily block content originating from a Tor node because the IP addresses of all Tor nodes are easy to obtain through Tor’s own directory servers which are necessary to inform the network about other Tor nodes. All a website administrator has to do is create a simple rule to query a Tor ...
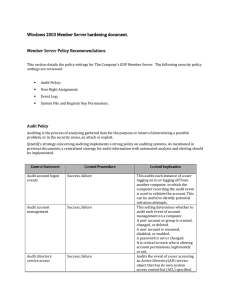
Server hardening - Cisco Security Solutions
... This allows a process to assume the identity of any user and thus gain access to the resources that the user is authorised to access. When a service requires this privilege, configure the service to log on using the local system account, which has this privilege inherently. By default this right doe ...
... This allows a process to assume the identity of any user and thus gain access to the resources that the user is authorised to access. When a service requires this privilege, configure the service to log on using the local system account, which has this privilege inherently. By default this right doe ...
document
... • Investigate what others can find out about you • Filter/monitor traffic on your network ...
... • Investigate what others can find out about you • Filter/monitor traffic on your network ...
A Technical Introduction to NGSCB Security Summit East 2003
... The machine owner sets policy to control which forms of attestation each agent or group of agents can use Secure communications agent provides higher-level services to agent developers Open a secure channel to a service using a secure session key Respond to an attestation challenge from the service ...
... The machine owner sets policy to control which forms of attestation each agent or group of agents can use Secure communications agent provides higher-level services to agent developers Open a secure channel to a service using a secure session key Respond to an attestation challenge from the service ...
Copy area
... On 01/13/13 Oracle released an update, Java 1.7.0_11, to deal with recently identified security vulnerabilities. This vulnerability is not specific to Skillsoft’s use of Java, but with Java in general. Skillsoft does use Java within a number of our products and recommends that our customers upgrade ...
... On 01/13/13 Oracle released an update, Java 1.7.0_11, to deal with recently identified security vulnerabilities. This vulnerability is not specific to Skillsoft’s use of Java, but with Java in general. Skillsoft does use Java within a number of our products and recommends that our customers upgrade ...
Secure Solutions for Wireless, VPN and Perimeter
... Outlook RPC encryption can be enforced centrally ...
... Outlook RPC encryption can be enforced centrally ...
How to project by Ethernet in Mt8000?
... How to download project by Ethernet 1. Connecting Ethernet cable in HMI 2. Going to HMI’s Tool bar screen and selecting ...
... How to download project by Ethernet 1. Connecting Ethernet cable in HMI 2. Going to HMI’s Tool bar screen and selecting ...
New Horizons Courseware Outlines
... minimum of six months programming experience, and want to learn how to develop services and deploy them to hybrid environments. ...
... minimum of six months programming experience, and want to learn how to develop services and deploy them to hybrid environments. ...
Module 7 Active Directory and Account Management
... • Network traffic due to replications is reduced by: – Replicating individual properties instead of entire accounts – Replicating based on the speed of the network link • Replicate more frequently over a LAN than a WAN ...
... • Network traffic due to replications is reduced by: – Replicating individual properties instead of entire accounts – Replicating based on the speed of the network link • Replicate more frequently over a LAN than a WAN ...
NEW YORK TECH-SECURITY CONFERENCE
... Data Connectors’ technology security conferences are focused on providing you with the latest best practices, products and services available to the community right now in an educational environment. Whether you are concerned with information security, cyber security, network security or particular ...
... Data Connectors’ technology security conferences are focused on providing you with the latest best practices, products and services available to the community right now in an educational environment. Whether you are concerned with information security, cyber security, network security or particular ...
Week 3 Chapter 04
... many types of changes that might be made in Active Directory, including when: – There are attribute changes to the schema – Objects are moved, such as user accounts moved from one OU to a different one – New objects are created, such as a new OU – A container or object is deleted and then brought ba ...
... many types of changes that might be made in Active Directory, including when: – There are attribute changes to the schema – Objects are moved, such as user accounts moved from one OU to a different one – New objects are created, such as a new OU – A container or object is deleted and then brought ba ...
windows and linux operating systems from a security perspective
... threads, allocating primary memory to various applications, managing data storage, controlling input and output peripherals, hosting device drivers, and delivering multi-level secure execution platform.Microsoft Windows and Linux are two of the most renowned operating systems that have a widespread ...
... threads, allocating primary memory to various applications, managing data storage, controlling input and output peripherals, hosting device drivers, and delivering multi-level secure execution platform.Microsoft Windows and Linux are two of the most renowned operating systems that have a widespread ...
KaranOberoi
... Sub-Domain must be added to RootDomain – otherwise there will be no tree adiscon.com ...
... Sub-Domain must be added to RootDomain – otherwise there will be no tree adiscon.com ...
CounterACT: Powerful, Automated Network Protection
... When the recent Conficker outbreak wreaked havoc upon Windows-based LANs in enterprises worldwide, CounterACTTM customers called in to say: “our network is perfectly safe – CounterACT’s automatic zero-day threat prevention provided us with the 24/7/365 protection we have come to expect and rely on!” ...
... When the recent Conficker outbreak wreaked havoc upon Windows-based LANs in enterprises worldwide, CounterACTTM customers called in to say: “our network is perfectly safe – CounterACT’s automatic zero-day threat prevention provided us with the 24/7/365 protection we have come to expect and rely on!” ...
Outlook.com
Outlook.com is a free web-based email service run by Microsoft. One of the world's first webmail services, it was founded in 1996 as Hotmail (stylized as HoTMaiL) by Sabeer Bhatia and Jack Smith in Mountain View, California, and headquartered in Sunnyvale. Hotmail was acquired by Microsoft in 1997 for an estimated $400 million and launched as MSN Hotmail, later rebranded to Windows Live Hotmail as part of the Windows Live suite of products.By mid-2011, the service had 360 million users per month, and the final version was released in October that year. It was available in 36 languages.Outlook.com replaced Hotmail in 2013, and follows Microsoft's Metro design language, closely mimicking the interface of Microsoft Outlook. It also features unlimited storage, Ajax, and close integration with Calendar, OneDrive, People, Office Online and Skype.