faculty.elgin.edu
... • User Account Control (UAC) • Feature implemented in Windows 7 to control malware • Prompts users when software attempts to take administrative control • Windows Defender • A real-time spyware monitor to prevent the installation of and ...
... • User Account Control (UAC) • Feature implemented in Windows 7 to control malware • Prompts users when software attempts to take administrative control • Windows Defender • A real-time spyware monitor to prevent the installation of and ...
Threats To Windows Users and Countermeasures
... because it originated from a familiar address. Also, malicious codes can be distributed in amusing or attractive programs. And the recent example is the wide spread of W32SIRCAM worm, discovered in July 2001, which propagates via Microsoft Outlook email programs and comes in various attractive attac ...
... because it originated from a familiar address. Also, malicious codes can be distributed in amusing or attractive programs. And the recent example is the wide spread of W32SIRCAM worm, discovered in July 2001, which propagates via Microsoft Outlook email programs and comes in various attractive attac ...
File
... LDAP: Strengths, Weaknesses, and AD Integration Lightweight Directory Access Protocol (LDAP) is “a set of open protocols used to access centrally stored information over a network,” and “runs on a layer above the TCP/IP stack” (Red Hat, Inc., 2011) (Mcirosoft Corporation, 2011). The use of directory ...
... LDAP: Strengths, Weaknesses, and AD Integration Lightweight Directory Access Protocol (LDAP) is “a set of open protocols used to access centrally stored information over a network,” and “runs on a layer above the TCP/IP stack” (Red Hat, Inc., 2011) (Mcirosoft Corporation, 2011). The use of directory ...
Event Title - Microsoft Center
... Notes: Update as of 1/13/2010. Vulnerabilities are included for SQL Server 2000 , SQL Server 2005 , SQL Server 2008. Oracle (8i, 9i, 9iR2, 10g, 10gR2,11g), IBM DB2 (8.0, 8.1, 8.2, 9.0, 9.5), Query for Oracle was run with vendor name: ‘Oracle’ , and product name: ‘any’ (all database product name va ...
... Notes: Update as of 1/13/2010. Vulnerabilities are included for SQL Server 2000 , SQL Server 2005 , SQL Server 2008. Oracle (8i, 9i, 9iR2, 10g, 10gR2,11g), IBM DB2 (8.0, 8.1, 8.2, 9.0, 9.5), Query for Oracle was run with vendor name: ‘Oracle’ , and product name: ‘any’ (all database product name va ...
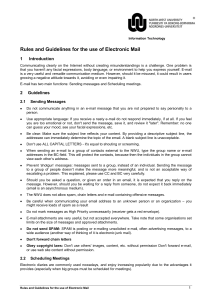
Rules and guideline for the use of Electronic Mail
... When sending an e-mail to a group of contacts external to the NWU, type the group name or e-mail addresses in the BC-field. This will protect the contacts, because then the individuals in the group cannot view each other’s address. Prevent ‘shotgun’ messages: messages sent to a group, instead of an ...
... When sending an e-mail to a group of contacts external to the NWU, type the group name or e-mail addresses in the BC-field. This will protect the contacts, because then the individuals in the group cannot view each other’s address. Prevent ‘shotgun’ messages: messages sent to a group, instead of an ...
Sentinel SuperPro™
... SuperPro allows you to use the Advanced Encryption Standard (AES) to secure your applications. Support for the AES-based algorithm engine enables use of this industry leading algorithm to generate unique query/responses. AES fortifies your defenses against today’s most common hacking threats such as ...
... SuperPro allows you to use the Advanced Encryption Standard (AES) to secure your applications. Support for the AES-based algorithm engine enables use of this industry leading algorithm to generate unique query/responses. AES fortifies your defenses against today’s most common hacking threats such as ...
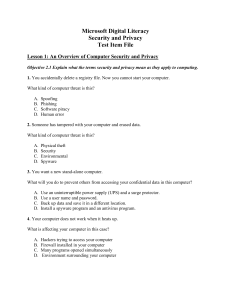
Question Info
... Which of the following methods will you suggest to her? Select two. A. Check history files. B. Disable Automatic Updates. C. Enable Windows Firewall. D. Use strong passwords. ...
... Which of the following methods will you suggest to her? Select two. A. Check history files. B. Disable Automatic Updates. C. Enable Windows Firewall. D. Use strong passwords. ...
VIRTUAL PRIVATE NETWORK
... Data Encryption Data sent and received over the Internet must be encrypted for privacy Microsoft Implementation of these protocols uses IPSec encryption to protect the data stream from the client to the tunnel server. ...
... Data Encryption Data sent and received over the Internet must be encrypted for privacy Microsoft Implementation of these protocols uses IPSec encryption to protect the data stream from the client to the tunnel server. ...
FAKEM RAT: Malware Disguised as Windows Messenger and
... The network communication between the compromised computer and the RAT controller is encrypted. The encryption is the same across variants and done at the bit level. Each byte is XOR-ed by every letter in the string, YHCRA, and rotated 3 bits to the right after every XOR operation. Encrypting the co ...
... The network communication between the compromised computer and the RAT controller is encrypted. The encryption is the same across variants and done at the bit level. Each byte is XOR-ed by every letter in the string, YHCRA, and rotated 3 bits to the right after every XOR operation. Encrypting the co ...
Blue Coat Mail Threat Defense
... cloud-based service or an on-premises appliance. It is typically positioned behind the firewall, after the SPAM filter, to ensure it can inspect all mail before it is delivered to the user. Note, the solution can also be deployed passively, alerting you as soon as email malware is detected. It seaml ...
... cloud-based service or an on-premises appliance. It is typically positioned behind the firewall, after the SPAM filter, to ensure it can inspect all mail before it is delivered to the user. Note, the solution can also be deployed passively, alerting you as soon as email malware is detected. It seaml ...
From Russia with Love: Behind the Trend Micro
... Further research on the domain revealed that it has been actively distributing Android malware, none of which, however, infected our phone during the experiment. It appears to exploit the common CVE-2012-0158 vulnerability, which works against unpatched versions of Microsoft Office 2003, 2007, and 2 ...
... Further research on the domain revealed that it has been actively distributing Android malware, none of which, however, infected our phone during the experiment. It appears to exploit the common CVE-2012-0158 vulnerability, which works against unpatched versions of Microsoft Office 2003, 2007, and 2 ...
SRA Customized Web Portal | Secure Remote Access | SonicWALL
... based on corporate policy, and second, it provides an easy to use interface to make the end-user experience simple and straightforward. ...
... based on corporate policy, and second, it provides an easy to use interface to make the end-user experience simple and straightforward. ...
Windows Server 2012 Dynamic Access Control Deep Dive for Active
... Selected AD user/computer attributes are included in the security token Claims can be used directly in file server permissions Claims are consistently issued to all users in a forest Claims can be transformed across trust boundaries Enables newer types of policies that weren’t possible before: • Exa ...
... Selected AD user/computer attributes are included in the security token Claims can be used directly in file server permissions Claims are consistently issued to all users in a forest Claims can be transformed across trust boundaries Enables newer types of policies that weren’t possible before: • Exa ...
Abstract - Compassion Software Solutions
... attacks emerge as spoofed E-Mails appearing as legitimate ones which make the users to trust and divulge into them by clicking the link provided in the E-Mail. Detection of malicious URLs and identification of threat types are critical to thwart these attacks. Knowing the type of a threat enables es ...
... attacks emerge as spoofed E-Mails appearing as legitimate ones which make the users to trust and divulge into them by clicking the link provided in the E-Mail. Detection of malicious URLs and identification of threat types are critical to thwart these attacks. Knowing the type of a threat enables es ...
Defending Office 365 Against Denial-of-Service Attacks
... often using bots (a software application that runs automated tasks over the Internet). As a result of Microsoft’s Digital Crimes Unit’s work both in cyberspace and with the justice system, Microsoft has successfully disabled significant numbers of bots, while at the same time building a vast databas ...
... often using bots (a software application that runs automated tasks over the Internet). As a result of Microsoft’s Digital Crimes Unit’s work both in cyberspace and with the justice system, Microsoft has successfully disabled significant numbers of bots, while at the same time building a vast databas ...
Fraudulent Emails, Websites and Phishing Variations Fraudulent
... coming from a legitimate company. Fraudsters may also have identifying customer information, such as your name, which they may use to make the call appear more authentic. If you are uncomfortable with a phone call that was not initiated by you, hang up or ask for the purpose of the call. Then, conta ...
... coming from a legitimate company. Fraudsters may also have identifying customer information, such as your name, which they may use to make the call appear more authentic. If you are uncomfortable with a phone call that was not initiated by you, hang up or ask for the purpose of the call. Then, conta ...
OSCAR-ENGAGE Refactoring – Progress and Future Work
... But not sacrifice demonstration of features Provide pre-installed demonstrations of software using real scientific applications Straightforward, minimum number of steps to use ...
... But not sacrifice demonstration of features Provide pre-installed demonstrations of software using real scientific applications Straightforward, minimum number of steps to use ...
Guidance on the Use of E-Mail when Sending Person
... Microsoft Exchange (which is usually accessed through Outlook) is the most widely used email system at Trusts across the NHS, (at NUH this is the normal email system with an address type of [email protected]) NHSmail (or nhs.net email as it’s commonly referred to) is a separate email system whic ...
... Microsoft Exchange (which is usually accessed through Outlook) is the most widely used email system at Trusts across the NHS, (at NUH this is the normal email system with an address type of [email protected]) NHSmail (or nhs.net email as it’s commonly referred to) is a separate email system whic ...
Our Guidelines to Email and SMS Communications
... sensitive information, such as usernames, passwords and credit card details, by masquerading as a trustworthy entity in an electronic communication. SMS/Text message: The Short Message Service (SMS), often called text messaging is a means of sending short messages, to and from mobile phones. Secure ...
... sensitive information, such as usernames, passwords and credit card details, by masquerading as a trustworthy entity in an electronic communication. SMS/Text message: The Short Message Service (SMS), often called text messaging is a means of sending short messages, to and from mobile phones. Secure ...
090923-eNMR-Barcelona
... HADDOCK: Structure Prediction of Protein-Protein Complexes CYANA: NMR Structure Calculations XPLOR-NIH: NMR Structure Calculations csRosetta: NMR Structure Calculations ...
... HADDOCK: Structure Prediction of Protein-Protein Complexes CYANA: NMR Structure Calculations XPLOR-NIH: NMR Structure Calculations csRosetta: NMR Structure Calculations ...
CEH
... You can get details like residential addresses, contact numbers, date of birth, and change of location You can get satellite pictures of private residences ...
... You can get details like residential addresses, contact numbers, date of birth, and change of location You can get satellite pictures of private residences ...
Outlook.com
Outlook.com is a free web-based email service run by Microsoft. One of the world's first webmail services, it was founded in 1996 as Hotmail (stylized as HoTMaiL) by Sabeer Bhatia and Jack Smith in Mountain View, California, and headquartered in Sunnyvale. Hotmail was acquired by Microsoft in 1997 for an estimated $400 million and launched as MSN Hotmail, later rebranded to Windows Live Hotmail as part of the Windows Live suite of products.By mid-2011, the service had 360 million users per month, and the final version was released in October that year. It was available in 36 languages.Outlook.com replaced Hotmail in 2013, and follows Microsoft's Metro design language, closely mimicking the interface of Microsoft Outlook. It also features unlimited storage, Ajax, and close integration with Calendar, OneDrive, People, Office Online and Skype.