Protecting against spear-phishing
... layers of defence available – application whitelisting and system restore methods. Working in the opposite way to blacklists, whitelists enable IT managers to identify exactly which programs should be permitted to run, thus providing greater reassurance that unknown malware and viruses will not infi ...
... layers of defence available – application whitelisting and system restore methods. Working in the opposite way to blacklists, whitelists enable IT managers to identify exactly which programs should be permitted to run, thus providing greater reassurance that unknown malware and viruses will not infi ...
NetworkSecurity
... be spyware. This means that the software can gather information about your computer and how you use it and send that information to marketing companies. Those companies can gather information such as your email address, calendar data, web sites you have visited, or what music you listen to. ...
... be spyware. This means that the software can gather information about your computer and how you use it and send that information to marketing companies. Those companies can gather information such as your email address, calendar data, web sites you have visited, or what music you listen to. ...
PROTECTING INFORMATION RESOURCES
... – Type of Trojan program used to release a virus, worm, or other destructive code – Triggered at a certain time or by an event ...
... – Type of Trojan program used to release a virus, worm, or other destructive code – Triggered at a certain time or by an event ...
CRM596 Quiz 1 - Chapters 1-3
... the Assignment Drop Box. The exam is due by midnight Sunday of Week 4. ...
... the Assignment Drop Box. The exam is due by midnight Sunday of Week 4. ...
Security
... Denial of service as long as virus runs Permanently damage hardware Target a competitor's computer – do harm – espionage ...
... Denial of service as long as virus runs Permanently damage hardware Target a competitor's computer – do harm – espionage ...
Word
... - in charge of formatting disks - creates sectors and clusters - creates F.A.T. or V.T.O.C. - sends message when disk is full or there is some other problem with writing data to the disk - virtual memory - CD-ROM, DVD-ROM - Flash drive Provides the Interface for Input and Output Devices ...
... - in charge of formatting disks - creates sectors and clusters - creates F.A.T. or V.T.O.C. - sends message when disk is full or there is some other problem with writing data to the disk - virtual memory - CD-ROM, DVD-ROM - Flash drive Provides the Interface for Input and Output Devices ...
operating system
... operating system to run other programs. Operating systems perform basic tasks, such as recognizing input from the keyboard, sending output to the display screen, keeping track of files and directories on the disk, and controlling peripheral devices such as disk drives and printers. For large systems ...
... operating system to run other programs. Operating systems perform basic tasks, such as recognizing input from the keyboard, sending output to the display screen, keeping track of files and directories on the disk, and controlling peripheral devices such as disk drives and printers. For large systems ...
Operating Systems - Personal Web Server
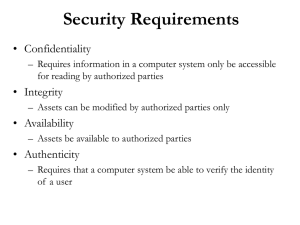
... Adaptability to a specific environment, like Unix can be in Minicomputer or PC Transparency Users are unaware of all details they need not know Security Protecting data from unauthorized access Integrity Protecting itself and users from damage or any other ill effect of other’s error or mali ...
... Adaptability to a specific environment, like Unix can be in Minicomputer or PC Transparency Users are unaware of all details they need not know Security Protecting data from unauthorized access Integrity Protecting itself and users from damage or any other ill effect of other’s error or mali ...
Towards a Trustworthy Android Ecosystem
... – The number is increasing consistently – Anti-malware ineffective at catching zero-day and polymorphic malware ...
... – The number is increasing consistently – Anti-malware ineffective at catching zero-day and polymorphic malware ...
Security - UTRGV Faculty Web
... When a digital signature is encrypted using a private key – it can be read by anyone with a public key. But the message was sent by only one who has the private key. Digital certificates are used to authenticate the source of a file. ...
... When a digital signature is encrypted using a private key – it can be read by anyone with a public key. But the message was sent by only one who has the private key. Digital certificates are used to authenticate the source of a file. ...
Information Security - National University of Sciences and
... • Attaches itself to some host program e.g. a word document • Executes when word document is opened • Make copies of itself by attaching itself by other host programs • Can do all sorts of damage • Fill up storage and memory, modify/destroy data, erase hard disk ...
... • Attaches itself to some host program e.g. a word document • Executes when word document is opened • Make copies of itself by attaching itself by other host programs • Can do all sorts of damage • Fill up storage and memory, modify/destroy data, erase hard disk ...
The Need for Security
... Explores the contents of a web browser’s cache Allows a Web designer to create a malicious form of cookie that is stored on the client’s system Cookie allow designer to collect information on how to access password protected sites ...
... Explores the contents of a web browser’s cache Allows a Web designer to create a malicious form of cookie that is stored on the client’s system Cookie allow designer to collect information on how to access password protected sites ...
Securing a Host Computer
... It is important that system and application updates are done regularly before connecting to the internet. It is also important to configure a current antivirus protection software with all Windows systems due to its high attack rate. ...
... It is important that system and application updates are done regularly before connecting to the internet. It is also important to configure a current antivirus protection software with all Windows systems due to its high attack rate. ...
J. Dizon, Y. Takagi, and G. Megerian
... usually combined with email spoofing to hide attacker’s identity ...
... usually combined with email spoofing to hide attacker’s identity ...
Security - NYU Stern School of Business
... overload for the server • Most server have a capacity that reflects normal use requirements • Tojan horse or worms get distributed onto many machines • At a specific time all infected machines start sending requests to the same server ...
... overload for the server • Most server have a capacity that reflects normal use requirements • Tojan horse or worms get distributed onto many machines • At a specific time all infected machines start sending requests to the same server ...
Weaponized Malware
... A Clear and Present Danger Weaponized malware and advanced persistent threats raise the bar on endpoint security. Originally intended for cyber-espionage and cyber-warfare, these sophisticated attacks are now available to ...
... A Clear and Present Danger Weaponized malware and advanced persistent threats raise the bar on endpoint security. Originally intended for cyber-espionage and cyber-warfare, these sophisticated attacks are now available to ...
Blue Coat Mail Threat Defense
... Secure Email Against Targeted Phishing Attacks Email is one of the most common attack vectors used by hackers to get into your corporate network. Attackers will send targeted communications “phishing” for information they can use to perpetrate other attacks and establish a foothold in your organizat ...
... Secure Email Against Targeted Phishing Attacks Email is one of the most common attack vectors used by hackers to get into your corporate network. Attackers will send targeted communications “phishing” for information they can use to perpetrate other attacks and establish a foothold in your organizat ...
TrendMicro Titanium - A New Concept in Security by Ira Wilsker
... clicking on the Tools button. Some of the other features accessible in this manner are a Secure Erase utility, Data Theft Prevention, Trend Micro Vault, and a Free Tool Center. The Parental Controls utility is intended to protect children from inappropriate websites, control access and online time, ...
... clicking on the Tools button. Some of the other features accessible in this manner are a Secure Erase utility, Data Theft Prevention, Trend Micro Vault, and a Free Tool Center. The Parental Controls utility is intended to protect children from inappropriate websites, control access and online time, ...
Looking into Windows
... From these examples it is apparent that the industrial IT environment is quite vulnerable enough – and without critical Windows XP security updates, PCs are wide open to attack by viruses, spyware and other malicious software that can steal or damage business data and information. Antivirus software ...
... From these examples it is apparent that the industrial IT environment is quite vulnerable enough – and without critical Windows XP security updates, PCs are wide open to attack by viruses, spyware and other malicious software that can steal or damage business data and information. Antivirus software ...
View - Shree Padma Higher Secondary School
... Realize the development process and progress of computers to till this date. Familiarize themselves with different types of computers, different generations of computer and software: System software and Application software. Work efficiently with application software mainly MS-WORD and MS-EXCEL. Use ...
... Realize the development process and progress of computers to till this date. Familiarize themselves with different types of computers, different generations of computer and software: System software and Application software. Work efficiently with application software mainly MS-WORD and MS-EXCEL. Use ...
Dan A CSC 345 Term Paper
... and Trojans. A worm is a malicious program that actively attempts to transmit itself over a network to infect other devices. A virus is a malicious program that spreads itself when it is ...
... and Trojans. A worm is a malicious program that actively attempts to transmit itself over a network to infect other devices. A virus is a malicious program that spreads itself when it is ...
Acceptable Use Policy (AUP)
... With the use of electronic networks, including both the Internet and the Intranet, the Humble Independent School District is expanding learning access for students, staff, parents and the entire Humble ISD community. With this opportunity comes the responsibility for appropriate use. ...
... With the use of electronic networks, including both the Internet and the Intranet, the Humble Independent School District is expanding learning access for students, staff, parents and the entire Humble ISD community. With this opportunity comes the responsibility for appropriate use. ...
Why we need IT security - Department of Computer Science and
... Countermeasures – Firewall • A firewall can be software (e.g. Windows Firewall), hardware or a combination of hardware and software • A firewall is used to: – Inspect all inbound and outbound internet messages (Uses packet filtering to distinguish between legitimate messages that are responses to v ...
... Countermeasures – Firewall • A firewall can be software (e.g. Windows Firewall), hardware or a combination of hardware and software • A firewall is used to: – Inspect all inbound and outbound internet messages (Uses packet filtering to distinguish between legitimate messages that are responses to v ...
Malware

Malware, short for malicious software, is any software used to disrupt computer operation, gather sensitive information, or gain access to private computer systems. Malware is defined by its malicious intent, acting against the requirements of the computer user, and does not include software that causes unintentional harm due to some deficiency. The term badware is sometimes used, and applied to both true (malicious) malware and unintentionally harmful software.Malware may be stealthy, intended to steal information or spy on computer users for an extended period without their knowledge, as for example Regin, or it may be designed to cause harm, often as sabotage (e.g., Stuxnet), or to extort payment (CryptoLocker). 'Malware' is an umbrella term used to refer to a variety of forms of hostile or intrusive software, including computer viruses, worms, trojan horses, ransomware, spyware, adware, scareware, and other malicious programs. It can take the form of executable code, scripts, active content, and other software. Malware is often disguised as, or embedded in, non-malicious files. As of 2011 the majority of active malware threats were worms or trojans rather than viruses.In law, malware is sometimes known as a computer contaminant, as in the legal codes of several U.S. states.Spyware or other malware is sometimes found embedded in programs supplied officially by companies, e.g., downloadable from websites, that appear useful or attractive, but may have, for example, additional hidden tracking functionality that gathers marketing statistics. An example of such software, which was described as illegitimate, is the Sony rootkit, a Trojan embedded into CDs sold by Sony, which silently installed and concealed itself on purchasers' computers with the intention of preventing illicit copying; it also reported on users' listening habits, and unintentionally created vulnerabilities that were exploited by unrelated malware.Software such as anti-virus, anti-malware, and firewalls are used to protect against activity identified as malicious, and to recover from attacks.