Petascale Plan 9 on Blue Gene Research Summary Ron Minnich Eric Van Hensbergen
... Systems with 100,000 cores more closely resemble a distributed system than a single computer in scale and reliability. Even so, we think that at this scale the system must give an application a single consistent interface to resources and services, both local and remote. The system must obviously no ...
... Systems with 100,000 cores more closely resemble a distributed system than a single computer in scale and reliability. Even so, we think that at this scale the system must give an application a single consistent interface to resources and services, both local and remote. The system must obviously no ...
M-GEAR: Gateway-Based Energy-Aware Multi
... Sink stores all information of nodes in Node Data Table Node Data Table includes node ID, Residual Energy, and distance of node from Sink and Gateway node ...
... Sink stores all information of nodes in Node Data Table Node Data Table includes node ID, Residual Energy, and distance of node from Sink and Gateway node ...
F21/1947/2012 ANGELA WAITHERA NABA FEB 116 ASSIGNMENT
... Fifth generation-were developed between 1984 to present day. These computers could perform parallel processing. They used artificial intelligence. They used microprocessors that could process data at very high speeds. 3. Fifth generation computers used artificial intelligence while fourth generation ...
... Fifth generation-were developed between 1984 to present day. These computers could perform parallel processing. They used artificial intelligence. They used microprocessors that could process data at very high speeds. 3. Fifth generation computers used artificial intelligence while fourth generation ...
VCS Communications: GAB and LLT
... How LLT Operates LLT provides kernel-to-kernel communications and monitors network communications. LLT can be configured to: Set system IDs within a cluster. Set cluster IDs for multiple clusters. Tune network parameters such as heartbeat frequency. LLT runs directly on top of the Data Link Protocol ...
... How LLT Operates LLT provides kernel-to-kernel communications and monitors network communications. LLT can be configured to: Set system IDs within a cluster. Set cluster IDs for multiple clusters. Tune network parameters such as heartbeat frequency. LLT runs directly on top of the Data Link Protocol ...
Web Resources for Computer Science Education
... Webquests Designed to use learners’ time well, to focus on using information rather than looking for it Encourages students to analyze, synthesize and evaluate information Webquest Page ...
... Webquests Designed to use learners’ time well, to focus on using information rather than looking for it Encourages students to analyze, synthesize and evaluate information Webquest Page ...
Computer Merit Badge
... code) into binary machine code that the computer understands (object code). • Machine code cannot port to another machine unless it is identical. • A Compiler program is written for each type of computer so programs can be ported. ...
... code) into binary machine code that the computer understands (object code). • Machine code cannot port to another machine unless it is identical. • A Compiler program is written for each type of computer so programs can be ported. ...
john von neumann
... In 1945, mathematician John von Neumann undertook a study of computation that demonstrated that a computer could have a simple, fixed structure, yet be able to execute any kind of computation given properly programmed control without the need for hardware modification. Von Neumann contributed a new ...
... In 1945, mathematician John von Neumann undertook a study of computation that demonstrated that a computer could have a simple, fixed structure, yet be able to execute any kind of computation given properly programmed control without the need for hardware modification. Von Neumann contributed a new ...
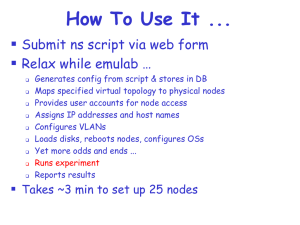
emulab.net: A Network Emulation and Distributed Systems Testbed
... Specify desired device and path properties ...
... Specify desired device and path properties ...
Bisection Bandwidth
... • Suppose half the nodes send to the other half of the nodes (each node sends or receives). What is the minimum bandwidth for any choice of which nodes send or receive? • Bisection bandwidth: sum of the bandwidths of the minimal number of links that are cut when splitting the system into two parts • ...
... • Suppose half the nodes send to the other half of the nodes (each node sends or receives). What is the minimum bandwidth for any choice of which nodes send or receive? • Bisection bandwidth: sum of the bandwidths of the minimal number of links that are cut when splitting the system into two parts • ...
- Connect Innovate UK
... “We were able to combine techniques from mathematics and computational science to substantially improve the efficiency of risk analysis modelling in the reinsurance sector. We look forward to further collaboration through the Willis Research Network." ...
... “We were able to combine techniques from mathematics and computational science to substantially improve the efficiency of risk analysis modelling in the reinsurance sector. We look forward to further collaboration through the Willis Research Network." ...
The Datacenter Needs an Operating System
... cluster software stack (e.g. X-Trace, Dapper) – Replay debugging that takes advantage of limited languages / computational models ...
... cluster software stack (e.g. X-Trace, Dapper) – Replay debugging that takes advantage of limited languages / computational models ...
IOSR Journal of Computer Engineering (IOSRJCE)
... A network interface card that supports a TCP/IP stack Same Linux distribution and version as the server node All clients must have the same architecture Monitors and keyboards may be helpful but not required 1.4 Cluster computing implementation using MPI: Message passing is a model for interactions ...
... A network interface card that supports a TCP/IP stack Same Linux distribution and version as the server node All clients must have the same architecture Monitors and keyboards may be helpful but not required 1.4 Cluster computing implementation using MPI: Message passing is a model for interactions ...
Text S1.
... far less IQV values than 0.8 which is the value achieved when cluster association is randomly assigned. The clusters with which subsets of muscles exhibit single dominant associations are the 12, 21 and 22 clusters. Unlike the other two clusters, these clusters have motor neurons as major members. T ...
... far less IQV values than 0.8 which is the value achieved when cluster association is randomly assigned. The clusters with which subsets of muscles exhibit single dominant associations are the 12, 21 and 22 clusters. Unlike the other two clusters, these clusters have motor neurons as major members. T ...
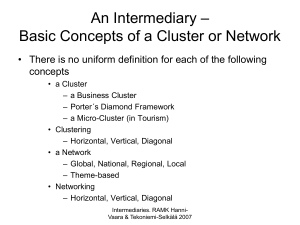
Intermediary - Clustering and Networking
... Intermediaries. RAMK HanniVaara & Tekoniemi-Selkälä 2007 ...
... Intermediaries. RAMK HanniVaara & Tekoniemi-Selkälä 2007 ...
Slide 1
... 800 GB/tape, $100/TB, 120 MB/s – LTO-5, out next year, will double capacity, 1.5x bandwidth: 1600 GB/tape, 180 MB/s – LTO-6 will be out prior to the 12 GeV era 3200 GB/tape, 270 MB/s ...
... 800 GB/tape, $100/TB, 120 MB/s – LTO-5, out next year, will double capacity, 1.5x bandwidth: 1600 GB/tape, 180 MB/s – LTO-6 will be out prior to the 12 GeV era 3200 GB/tape, 270 MB/s ...
Geo-distributed Messaging with RabbitMQ
... – Consistency – roughly meaning that all clients of a data store get responses to requests that ‘make sense’. For example, if Client A writes 1 then 2 to location X, Client B cannot read 2 followed by 1. – Availability – all operations on a data store eventually return successfully. We say that a da ...
... – Consistency – roughly meaning that all clients of a data store get responses to requests that ‘make sense’. For example, if Client A writes 1 then 2 to location X, Client B cannot read 2 followed by 1. – Availability – all operations on a data store eventually return successfully. We say that a da ...
Small-College Supercomputing: Building A Beowulf
... of decisions to be made: 1. What hardware you want for your cluster’s nodes; and 2. How your nodes will communicate (their interconnect). We will treat each of these separately. Nodes. The vast majority of Beowulf cluster nodes have x86 CPUs (e.g., Intel, AMD) that were current when the clusters wer ...
... of decisions to be made: 1. What hardware you want for your cluster’s nodes; and 2. How your nodes will communicate (their interconnect). We will treat each of these separately. Nodes. The vast majority of Beowulf cluster nodes have x86 CPUs (e.g., Intel, AMD) that were current when the clusters wer ...
2. Computers: The Machines Behind Computing
... users share computer resources and performing repetitive tasks for users ...
... users share computer resources and performing repetitive tasks for users ...
Computer cluster

A computer cluster consists of a set of loosely or tightly connected computers that work together so that, in many respects, they can be viewed as a single system. Unlike grid computers, computer clusters have each node set to perform the same task, controlled and scheduled by software.The components of a cluster are usually connected to each other through fast local area networks (""LAN""), with each node (computer used as a server) running its own instance of an operating system. In most circumstances, all of the nodes use the same hardware and the same operating system, although in some setups (i.e. using Open Source Cluster Application Resources (OSCAR)), different operating systems can be used on each computer, and/or different hardware.They are usually deployed to improve performance and availability over that of a single computer, while typically being much more cost-effective than single computers of comparable speed or availability.Computer clusters emerged as a result of convergence of a number of computing trends including the availability of low-cost microprocessors, high speed networks, and software for high-performance distributed computing. They have a wide range of applicability and deployment, ranging from small business clusters with a handful of nodes to some of the fastest supercomputers in the world such as IBM's Sequoia. The applications that can be done however, are nonetheless limited, since the software needs to be purpose-built per task. It is hence not possible to use computer clusters for casual computing tasks.