Trustworthy Computing
... that the environment running such programs is trusted not to subvert the program that the media player is trusted by the provider not to leak the media that there is a means to prevent leakage of the ...
... that the environment running such programs is trusted not to subvert the program that the media player is trusted by the provider not to leak the media that there is a means to prevent leakage of the ...
Alpha System Startup Procedure
... as DS10 and ES40 have PCI expansion slots only. As a result, EISA setup options appear in the AlphaBIOS screens for the systems with EISA slots, and not in the AlphaBIOS screens for ISA/PCI systems. In addition, new AlphaBIOS version can ...
... as DS10 and ES40 have PCI expansion slots only. As a result, EISA setup options appear in the AlphaBIOS screens for the systems with EISA slots, and not in the AlphaBIOS screens for ISA/PCI systems. In addition, new AlphaBIOS version can ...
Operating Systems and Computer Organization
... How does it all start? • When the computer is started, the control unit branches to a fixed memory location; e.g. initial PC value hardwired. • The fixed location is a ROM address that contains a the BIOS loader. • The BIOS loader loads a “bootstrap loader” from the disk “boot sector” into memory a ...
... How does it all start? • When the computer is started, the control unit branches to a fixed memory location; e.g. initial PC value hardwired. • The fixed location is a ROM address that contains a the BIOS loader. • The BIOS loader loads a “bootstrap loader” from the disk “boot sector” into memory a ...
Operating System Concepts for System Programmers
... What are the two types of user interfaces provided by the OS, and what are the differences between these two types of interfaces? Is it possible to differentiate the applications that are part of OS, and applications, which are not part of OS? What is the main difference between Kernel and Applicati ...
... What are the two types of user interfaces provided by the OS, and what are the differences between these two types of interfaces? Is it possible to differentiate the applications that are part of OS, and applications, which are not part of OS? What is the main difference between Kernel and Applicati ...
Abstract View of System Components
... What is Memory management? Optimizes the use of random access memory (RAM) allocates or resigns, data and instructions to area of memory while they are being processed monitors contents of memory clears items from memory when processor no ...
... What is Memory management? Optimizes the use of random access memory (RAM) allocates or resigns, data and instructions to area of memory while they are being processed monitors contents of memory clears items from memory when processor no ...
The Fallacy of Software Write Protection in Computer Forensics
... Knowing what a system will do at any given point in time is predictability. A personal computer today is a complex system of components, devices, data and operating and file system software. Within this complex system, an increasing number of autonomous automatic tasks are performed. Some are well k ...
... Knowing what a system will do at any given point in time is predictability. A personal computer today is a complex system of components, devices, data and operating and file system software. Within this complex system, an increasing number of autonomous automatic tasks are performed. Some are well k ...
slides - Caltech
... • Includes a single partition that covers the entire disk • Partition type is set to a value unused by all major OSes • Reason: if a legacy MBR tool is used on the disk, it won’t be as likely to mangle the GUID partition table on the disk • Disks with GUID Partition Tables maintain two GPTs • Identi ...
... • Includes a single partition that covers the entire disk • Partition type is set to a value unused by all major OSes • Reason: if a legacy MBR tool is used on the disk, it won’t be as likely to mangle the GUID partition table on the disk • Disks with GUID Partition Tables maintain two GPTs • Identi ...
lecture6
... MS DOS is an acronym that stands for MicroSoft Disk Operating System. It is often referred to as DOS. It is an old operating system for x86-based personal computers, purchased by Microsoft that manages everything on your computer: hardware, memory, files. It is an operating system that existed prior ...
... MS DOS is an acronym that stands for MicroSoft Disk Operating System. It is often referred to as DOS. It is an old operating system for x86-based personal computers, purchased by Microsoft that manages everything on your computer: hardware, memory, files. It is an operating system that existed prior ...
ARM Based Customizing an Operating System for the Single Board
... This code is common to all of the processor architectures supported by SBC OS. Below this is the architecturedependent code, which forms what is more commonly, called a BSP (Board Support Package). This code serves as the processor and platform-specific code for the given architecture. ...
... This code is common to all of the processor architectures supported by SBC OS. Below this is the architecturedependent code, which forms what is more commonly, called a BSP (Board Support Package). This code serves as the processor and platform-specific code for the given architecture. ...
Formatting and Partitioning Hard Drives, and DOS
... used by the everyday user Accessed in XP by typing CMD in the run dialog box or under the accessories tab on the ...
... used by the everyday user Accessed in XP by typing CMD in the run dialog box or under the accessories tab on the ...
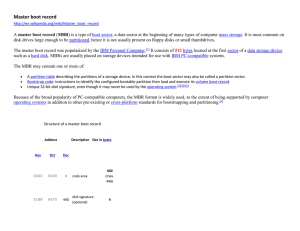
Master boot record
... The master boot record was popularized by the IBM Personal Computer.[1] It consists of 512 bytes located at the first sector of a data storage device such as a hard disk. MBRs are usually placed on storage devices intended for use with IBM PC-compatible systems. The MBR may contain one or more of: ...
... The master boot record was popularized by the IBM Personal Computer.[1] It consists of 512 bytes located at the first sector of a data storage device such as a hard disk. MBRs are usually placed on storage devices intended for use with IBM PC-compatible systems. The MBR may contain one or more of: ...
Unit OS 11: Startup, Crashes, Troubleshooting
... NTLDR loads and executes Ntdetect.com to perform BIOS hardware detection (x86 and x64 only) Later saved into HKLM\Hardware\Description NTLDR loads: Ntoskrnl.exe, Hal.dll, and Bootvid.dll (and Kdcom.dll for XP and later) ...
... NTLDR loads and executes Ntdetect.com to perform BIOS hardware detection (x86 and x64 only) Later saved into HKLM\Hardware\Description NTLDR loads: Ntoskrnl.exe, Hal.dll, and Bootvid.dll (and Kdcom.dll for XP and later) ...
Windows, Linux and Mac Operating system Booting Process: a
... take care of identifying the Master boot record for the initializing the booting process. Step02: Now BIOS will look for the Booting Priority, like from where the computer will get the operating system e.g. from hard-disk, floppy disk, or network. This record in booting process is called MBR (Master ...
... take care of identifying the Master boot record for the initializing the booting process. Step02: Now BIOS will look for the Booting Priority, like from where the computer will get the operating system e.g. from hard-disk, floppy disk, or network. This record in booting process is called MBR (Master ...
Operating Systems [OS]
... Symmetric clustering has multiple nodes running applications, monitoring each other ...
... Symmetric clustering has multiple nodes running applications, monitoring each other ...
BIOS Startup Firmware
... Monitoring firmware operating in SMM can provide a system design with a new capability: secure provisioning. The firmware can hold a list of software objects in the OS and application code that are open for updates. Because the firmware has access to system resources such as the network interfaces a ...
... Monitoring firmware operating in SMM can provide a system design with a new capability: secure provisioning. The firmware can hold a list of software objects in the OS and application code that are open for updates. Because the firmware has access to system resources such as the network interfaces a ...
Quiz 1 - FSU Computer Science
... 46. True/False A program written for the .NET Framework need not worry about the specifics of the hardware or the operating system on which it will run. 47. True/False Many operating system merge I/O devices and files into a combined file because of the similarity of system calls for each. 48. True/ ...
... 46. True/False A program written for the .NET Framework need not worry about the specifics of the hardware or the operating system on which it will run. 47. True/False Many operating system merge I/O devices and files into a combined file because of the similarity of system calls for each. 48. True/ ...
Literatur Computer Systeme und Anwendungen Informatics 3
... Setup of the Memory Management (address mapping table) (virtual Computer) to enable a more flexible use of a computer memory addresses can be translated by a special electronic device in a computer (MMU) before accessing the memory to real memory addresses. This enables a more flexible use of the me ...
... Setup of the Memory Management (address mapping table) (virtual Computer) to enable a more flexible use of a computer memory addresses can be translated by a special electronic device in a computer (MMU) before accessing the memory to real memory addresses. This enables a more flexible use of the me ...
Forensics Book 2: Investigating Hard Disk and File and Operating
... retrieve and load the kernel cache file. The next step is to “decode” the kernel BootX attempts to decode the file as a Mach-O binary If the above fails, BootX gives up, draws the failed boot picture, and goes into an infinite loop If BootX is successful so far, it saves file system cache hi ...
... retrieve and load the kernel cache file. The next step is to “decode” the kernel BootX attempts to decode the file as a Mach-O binary If the above fails, BootX gives up, draws the failed boot picture, and goes into an infinite loop If BootX is successful so far, it saves file system cache hi ...
UNIX
... the boot loader begins execution. In the case of a hard drive, this first sector is referred to as the Master Boot Record (MBR). The MBR contains the partition table describing the partitions defined on the hard drive. It also contains a program, the boot loader, which will load the first sector of ...
... the boot loader begins execution. In the case of a hard drive, this first sector is referred to as the Master Boot Record (MBR). The MBR contains the partition table describing the partitions defined on the hard drive. It also contains a program, the boot loader, which will load the first sector of ...
BIOS (Basic Input Output Service)
... cards in the ISA and PCI buses are queried and distributed. • Onboard hardware, located on motherboard and in its ISA/PCI slots, are configured for operation. ...
... cards in the ISA and PCI buses are queried and distributed. • Onboard hardware, located on motherboard and in its ISA/PCI slots, are configured for operation. ...
2. Operating System Structure
... System calls provide an interface to the OS services. These calls are usually C or C++ routines, but can also be in assembly for low-level tasks of HW. Even simple programs may use the OS heavily, thousands of system calls per second. Example: a program reading data from one file and copy them to an ...
... System calls provide an interface to the OS services. These calls are usually C or C++ routines, but can also be in assembly for low-level tasks of HW. Even simple programs may use the OS heavily, thousands of system calls per second. Example: a program reading data from one file and copy them to an ...
Lecture10c,Boot,process
... Changing Startup Behavior Using the Boot.ini File When you install Windows XP Professional, the Boot.ini file is automatically created in the root directory of the system partition. A system partition contains the hardware-specific files necessary to start the operating system, including the Boot.i ...
... Changing Startup Behavior Using the Boot.ini File When you install Windows XP Professional, the Boot.ini file is automatically created in the root directory of the system partition. A system partition contains the hardware-specific files necessary to start the operating system, including the Boot.i ...
Chapter 1 Bootstrap
... A computer’s CPU (central processing unit, or processor) runs a conceptually simple loop: it inspects the value of a register called the program counter, reads a machine instruction from that address in memory, advances the program counter past the instuction, and executes the instruction. Repeat. I ...
... A computer’s CPU (central processing unit, or processor) runs a conceptually simple loop: it inspects the value of a register called the program counter, reads a machine instruction from that address in memory, advances the program counter past the instuction, and executes the instruction. Repeat. I ...
Booting

In computing, booting (or booting up) is the initialization of a computerized system. The system can be a computer or a computer appliance. The booting process can be ""hard"", after electrical power to the CPU is switched from off to on (in order to diagnose particular hardware errors), or ""soft"", when those power-on self-tests (POST) can be avoided. Soft booting can be initiated by hardware such as a button press, or by software command. Booting is complete when the normal, operative, runtime environment is attained.A boot loader is a computer program that loads an operating system or some other system software for the computer after completion of the power-on self-tests; it is the loader for the operating system itself, which has its own loader for loading ordinary user programs and libraries. Within the hard reboot process, it runs after completion of the self-tests, then loads and runs the software. A boot loader is loaded into main memory from persistent memory, such as a hard disk drive or, in some older computers, from a medium such as punched cards, punched tape, or magnetic tape. The boot loader then loads and executes the processes that finalize the boot. Like POST processes, the boot loader code comes from a ""hard-wired"" and persistent location; if that location is too limited for some reason, that primary boot loader calls a second-stage boot loader or a secondary program loader.On modern general purpose computers, the boot up process can take tens of seconds, and typically involves performing a power-on self-test, locating and initializing peripheral devices, and then finding, loading and starting an operating system. The process of hibernating or sleeping does not involve booting. Minimally, some embedded systems do not require a noticeable boot sequence to begin functioning and when turned on may simply run operational programs that are stored in ROM. All computing systems are state machines, and a reboot may be the only method to return to a designated zero-state from an unintended, locked state.Boot is short for bootstrap or bootstrap load and derives from the phrase to pull oneself up by one's bootstraps. The usage calls attention to the requirement that, if most software is loaded onto a computer by other software already running on the computer, some mechanism must exist to load the initial software onto the computer. Early computers used a variety of ad-hoc methods to get a small program into memory to solve this problem. The invention of read-only memory (ROM) of various types solved this paradox by allowing computers to be shipped with a start up program that could not be erased. Growth in the capacity of ROM has allowed ever more elaborate start up procedures to be implemented.




![Operating Systems [OS]](http://s1.studyres.com/store/data/003405497_1-fcdfdf12ca283ac50da021c971edcf1f-300x300.png)