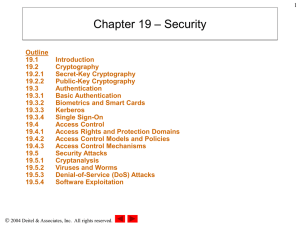
Chapter 19: Security - Murray State University
... • Five fundamental requirements for a successful, secure transaction – Privacy • Ensuring that the information transmitted over the Internet has not been viewed by a third party ...
... • Five fundamental requirements for a successful, secure transaction – Privacy • Ensuring that the information transmitted over the Internet has not been viewed by a third party ...
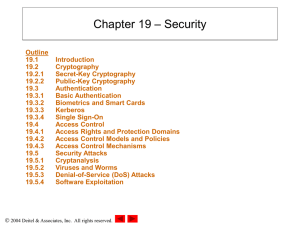
Chapter 19: Security
... • Five fundamental requirements for a successful, secure transaction – Privacy • Ensuring that the information transmitted over the Internet has not been viewed by a third party ...
... • Five fundamental requirements for a successful, secure transaction – Privacy • Ensuring that the information transmitted over the Internet has not been viewed by a third party ...
THESIS NAVAL POSTGRADUATE SCHOOL Monterey, California
... effect on our Navy. Information is becoming the most important factor. Militaries in general are becoming increasingly dependent on computer technology for every facet of their operations in today’s information technology environment. Information security is critical to the success of the RSNF, and ...
... effect on our Navy. Information is becoming the most important factor. Militaries in general are becoming increasingly dependent on computer technology for every facet of their operations in today’s information technology environment. Information security is critical to the success of the RSNF, and ...
SOW
... services that support the Office of Metro IT Security’s mission. This effort encompasses technical, engineering, management, operation, logistical and administrative support for the Office of Metro IT Security. The Contractor shall provide qualified personnel and other resources necessary to perform ...
... services that support the Office of Metro IT Security’s mission. This effort encompasses technical, engineering, management, operation, logistical and administrative support for the Office of Metro IT Security. The Contractor shall provide qualified personnel and other resources necessary to perform ...
Cengage Learning 2013
... • Information security is the protection of information – Information value comes from its characteristics ...
... • Information security is the protection of information – Information value comes from its characteristics ...
location information
... locally stored information that enables it to determine the appropriate ERDB to query for the routing instructions. b. The VPC uses the routing information provided in the received call setup signaling to select the appropriate trunk (group). c. If the VPC receives a Location Key, the VPC obtains th ...
... locally stored information that enables it to determine the appropriate ERDB to query for the routing instructions. b. The VPC uses the routing information provided in the received call setup signaling to select the appropriate trunk (group). c. If the VPC receives a Location Key, the VPC obtains th ...
Introduction
... 99 Commercial-grade firewalls and border routers to resist/ detect IP-based and denial-of-service attacks 99 Anti-tampering controls ...
... 99 Commercial-grade firewalls and border routers to resist/ detect IP-based and denial-of-service attacks 99 Anti-tampering controls ...
Information Technology (IT) Security Policy
... computer systems to aid treatment, expand communications, and improve management and control. This growing dependence comes at a time when the number of threats and actual attacks on these computer systems is constantly increasing. Information is one of our most important assets and each one of us h ...
... computer systems to aid treatment, expand communications, and improve management and control. This growing dependence comes at a time when the number of threats and actual attacks on these computer systems is constantly increasing. Information is one of our most important assets and each one of us h ...
8_19Counter Hack 6 scanning
... Ports like doors on each of machines Port scan knock on each door to see if anyone is listening behind it Someone behind the door, get a response No one behind the door, no answer back ...
... Ports like doors on each of machines Port scan knock on each door to see if anyone is listening behind it Someone behind the door, get a response No one behind the door, no answer back ...
The Difference Between Compliance and Cyber Security
... as Data Diodes. Some think the data diode is the silver bullet in cyber security. A data diode can enhance security in the appropriate environment; however, just adding a data diode to your network does not provide 100 percent protection for the network. A data diode cannot protect from an insider t ...
... as Data Diodes. Some think the data diode is the silver bullet in cyber security. A data diode can enhance security in the appropriate environment; however, just adding a data diode to your network does not provide 100 percent protection for the network. A data diode cannot protect from an insider t ...
Multimedia Application Production
... Denial-of-service attacks System penetration Theft of proprietary information Sabotage Succeeding with Technology ...
... Denial-of-service attacks System penetration Theft of proprietary information Sabotage Succeeding with Technology ...
Security+ Guide to Network Security Fundamentals, Third Edition
... Also called a ____________________ ____________________________________ its contents Can fully decode application-layer network protocols The different parts of the protocol can be analyzed for any suspicious behavior ...
... Also called a ____________________ ____________________________________ its contents Can fully decode application-layer network protocols The different parts of the protocol can be analyzed for any suspicious behavior ...
Security+ Guide to Network Security Fundamentals, Third Edition
... • The main goals of information security are to prevent data theft, thwart identity theft, avoid the legal consequences of not securing information, maintain productivity, and foil cyberterrorism • The types of people behind computer attacks are generally divided into several categories • There are ...
... • The main goals of information security are to prevent data theft, thwart identity theft, avoid the legal consequences of not securing information, maintain productivity, and foil cyberterrorism • The types of people behind computer attacks are generally divided into several categories • There are ...
PPT_ch01 - Mercer University Computer Science Department
... • The main goals of information security are to prevent data theft, thwart identity theft, avoid the legal consequences of not securing information, maintain productivity, and foil cyberterrorism • The types of people behind computer attacks are generally divided into several categories • There are ...
... • The main goals of information security are to prevent data theft, thwart identity theft, avoid the legal consequences of not securing information, maintain productivity, and foil cyberterrorism • The types of people behind computer attacks are generally divided into several categories • There are ...
From Russia with Love: Behind the Trend Micro
... The first thing we had to consider was how the environment was going to be configured. NBC News wanted the experiment to be performed on new gadgets with no security or software updates. The decision to not put basic precautions in place was made because we were supposed to be regular users in Russi ...
... The first thing we had to consider was how the environment was going to be configured. NBC News wanted the experiment to be performed on new gadgets with no security or software updates. The decision to not put basic precautions in place was made because we were supposed to be regular users in Russi ...
Firewalls: An Effective Solution for Internet Security
... Many organizations that employ firewalls feel a false sense of security once the firewalls are in place. Properly designing and implementing firewalls can be difficult, costly, and time consuming. It is critical to remember, however, that firewall design and implementation are simply the beginning p ...
... Many organizations that employ firewalls feel a false sense of security once the firewalls are in place. Properly designing and implementing firewalls can be difficult, costly, and time consuming. It is critical to remember, however, that firewall design and implementation are simply the beginning p ...
Course Overview - Cyber Security Lab
... operation costs. Internet and networking has greatly expanded the way of communicating and sharing data between businesses, providing services to customers and processing data. As computer networks continues to grow to enable more and more applications and are available to more and more users, they ...
... operation costs. Internet and networking has greatly expanded the way of communicating and sharing data between businesses, providing services to customers and processing data. As computer networks continues to grow to enable more and more applications and are available to more and more users, they ...
Governance Guidance - Top Actions
... Does management know where the enterprise is most vulnerable within the IT infrastructure? ...
... Does management know where the enterprise is most vulnerable within the IT infrastructure? ...
Governance Guidance - Top Actions
... Does management know where the enterprise is most vulnerable within the IT infrastructure? ...
... Does management know where the enterprise is most vulnerable within the IT infrastructure? ...
Governance Guidance
... Does management know where the enterprise is most vulnerable within the IT infrastructure? ...
... Does management know where the enterprise is most vulnerable within the IT infrastructure? ...
infosys.richmond.cc.nc.us
... Risk Management, Assessment, and Mitigation • One of the most important assets any organization possesses is its data • Unfortunately, the importance of data is generally underestimated • The first steps in data protection actually begin with understanding risks and risk management ...
... Risk Management, Assessment, and Mitigation • One of the most important assets any organization possesses is its data • Unfortunately, the importance of data is generally underestimated • The first steps in data protection actually begin with understanding risks and risk management ...
Security+ Guide to Network Security Fundamentals, Third Edition
... Risk Management, Assessment, and Mitigation • One of the most important assets any organization possesses is its data • Unfortunately, the importance of data is generally underestimated • The first steps in data protection actually begin with understanding risks and risk management ...
... Risk Management, Assessment, and Mitigation • One of the most important assets any organization possesses is its data • Unfortunately, the importance of data is generally underestimated • The first steps in data protection actually begin with understanding risks and risk management ...
Dr. Clifford Neuman University of Southern California Information
... – Solves n2 problem • Performance – Slower than conventional cryptography – Implementations use for key distribution, then use conventional crypto for data encryption • Trusted third party still needed – To certify public key – To manage revocation – In some cases, third party may be off-line Copyri ...
... – Solves n2 problem • Performance – Slower than conventional cryptography – Implementations use for key distribution, then use conventional crypto for data encryption • Trusted third party still needed – To certify public key – To manage revocation – In some cases, third party may be off-line Copyri ...
Educause Task Force on Systems Security
... – High bandwidth Internet (Fract T3, T3, T3+) – High computing capacity (scientific computing clusters, even web servers, etc.). – “Open” network security environment (no firewalls or only “light” filtering routers on many high bandwidth WANs and LANs) – Trust relationships between departments at va ...
... – High bandwidth Internet (Fract T3, T3, T3+) – High computing capacity (scientific computing clusters, even web servers, etc.). – “Open” network security environment (no firewalls or only “light” filtering routers on many high bandwidth WANs and LANs) – Trust relationships between departments at va ...
Sponsored by: US Department of Housing and
... Notice must specify purposes for PPI collections and must describe all uses/disclosures A program may use/disclosure PPI only if allowed by the standard and described in the privacy ...
... Notice must specify purposes for PPI collections and must describe all uses/disclosures A program may use/disclosure PPI only if allowed by the standard and described in the privacy ...