6LoWPAN: The Wireless Embedded Internet
... the Copyright, Designs and Patents Act 1988. All rights reserved. No part of this publication may be reproduced, stored in a retrieval system, or transmitted, in any form or by any means, electronic, mechanical, photocopying, recording or otherwise, except as permitted by the UK Copyright, Designs a ...
... the Copyright, Designs and Patents Act 1988. All rights reserved. No part of this publication may be reproduced, stored in a retrieval system, or transmitted, in any form or by any means, electronic, mechanical, photocopying, recording or otherwise, except as permitted by the UK Copyright, Designs a ...
2e_06_6_4_2_vlsm_instr
... All contents are Copyright © 1992–2007 Cisco Systems, Inc. All rights reserved. This document is Cisco Public Information. ...
... All contents are Copyright © 1992–2007 Cisco Systems, Inc. All rights reserved. This document is Cisco Public Information. ...
A. IMS/Internet interworking scenario.
... integrity, integrity mechanisms always provide some type of proof of data origin. Knowing that a message has not been modified without knowing who initially created the message would be useless. Confidentiality mechanisms keep unauthorized parties from getting access to the contents of a message. Co ...
... integrity, integrity mechanisms always provide some type of proof of data origin. Knowing that a message has not been modified without knowing who initially created the message would be useless. Confidentiality mechanisms keep unauthorized parties from getting access to the contents of a message. Co ...
Host-to-host congestion control for TCP
... To resolve the congestion collapse problem, a number of solutions have been proposed. All of them share the same idea, namely of introducing a network-aware rate limiting mechanism alongside the receiver-driven flow control. For this purpose the congestion window concept was introduced: a TCP sender ...
... To resolve the congestion collapse problem, a number of solutions have been proposed. All of them share the same idea, namely of introducing a network-aware rate limiting mechanism alongside the receiver-driven flow control. For this purpose the congestion window concept was introduced: a TCP sender ...
Seahorse XFp Analyzer User Guide
... Safe operation of the XFp Analyzer requires that all covers be securely attached and plate tray door is closed. This also prevents heat loss and system cooling, which can affect data quality. The door opens automatically when the tray is extended, allowing the operator to insert or remove the assay ...
... Safe operation of the XFp Analyzer requires that all covers be securely attached and plate tray door is closed. This also prevents heat loss and system cooling, which can affect data quality. The door opens automatically when the tray is extended, allowing the operator to insert or remove the assay ...
Module 1: Allocating IP Addressing by using Dynamic Host
... Broadcast a request for the IP address associated with a given MAC address RARP server responds with an IP address Only assigns IP address (not the default router and ...
... Broadcast a request for the IP address associated with a given MAC address RARP server responds with an IP address Only assigns IP address (not the default router and ...
Deploy services faster with Dell Active System Manager
... deployment such as a vSphere cluster deployment. Dell ASM comes with built-in templates you can use to customize a service to meet your specific needs. While Dell ASM required administrator time and effort to configure the initial deployment templates, administrators can later use these templates re ...
... deployment such as a vSphere cluster deployment. Dell ASM comes with built-in templates you can use to customize a service to meet your specific needs. While Dell ASM required administrator time and effort to configure the initial deployment templates, administrators can later use these templates re ...
Offset Time-Emulated Architecture for Optical Burst Switching - Modelling and Performance Evaluation
... The evolution of the transport networking is driven by continuously increasing traffic demand due to the introduction of broadband Internet access and new end-user business applications as well as the continuing paradigm shift from voice to data services. These trends have emerged at the same time a ...
... The evolution of the transport networking is driven by continuously increasing traffic demand due to the introduction of broadband Internet access and new end-user business applications as well as the continuing paradigm shift from voice to data services. These trends have emerged at the same time a ...
dynamic metric in ospf networks
... The massive growth of the Internet has led to increased requirements for reliable network infrastructure. The effectiveness of network communication depends on the ability of routers to determine the best path to send and forward packets to the desired destination. Open Shortest Path First (OSPF) pr ...
... The massive growth of the Internet has led to increased requirements for reliable network infrastructure. The effectiveness of network communication depends on the ability of routers to determine the best path to send and forward packets to the desired destination. Open Shortest Path First (OSPF) pr ...
Integrating Cisco Press Resources into the
... • The router ospf command takes a process identifier as an argument: – Router (config)# router ospf process-id – The process ID is a locally significant number between 1 and 65,535 that you select to identify the routing process • It does not need to match the OSPF process ID on other OSPF routers ...
... • The router ospf command takes a process identifier as an argument: – Router (config)# router ospf process-id – The process ID is a locally significant number between 1 and 65,535 that you select to identify the routing process • It does not need to match the OSPF process ID on other OSPF routers ...
Preparing for an IPv6 World with LXI Instruments
... LXI sticks with most useful IPv6 core capabilities. tm ...
... LXI sticks with most useful IPv6 core capabilities. tm ...
document
... Network infrastructure where all data are being transmitted and received use radio signals over the air instead of wires. ...
... Network infrastructure where all data are being transmitted and received use radio signals over the air instead of wires. ...
CCNPv5 Module 5 Lesson 10
... To control access to NTP services, in addition to packet authentication, a NTP access group can be created and a basic IP ACL applied to it To control access to NTP services, use the ntp access-group command in global configuration mode The access group options are scanned in the following order, fr ...
... To control access to NTP services, in addition to packet authentication, a NTP access group can be created and a basic IP ACL applied to it To control access to NTP services, use the ntp access-group command in global configuration mode The access group options are scanned in the following order, fr ...
CIS 175 Lecture Notes
... 2 Explosive growth 3 Internet 4 Economic impact 5 Complexity 6 Abstractions and concepts 7 On-line resources ...
... 2 Explosive growth 3 Internet 4 Economic impact 5 Complexity 6 Abstractions and concepts 7 On-line resources ...
Computer Networks and Internets By Douglas E Comer
... 2 Explosive growth 3 Internet 4 Economic impact 5 Complexity 6 Abstractions and concepts 7 On-line resources ...
... 2 Explosive growth 3 Internet 4 Economic impact 5 Complexity 6 Abstractions and concepts 7 On-line resources ...
Secure and Distributed Multicast Address Allocation on IPv6 Networks M. L. Slaviero
... made since the ISP does not, in general, provide multicast services to users. Why is the exploitation of a resource which promised so much, so limited? A common argument made is that many devices do not support multicast, and this is examined in a later chapter. Jonathan Barter, a self-proclaimed mu ...
... made since the ISP does not, in general, provide multicast services to users. Why is the exploitation of a resource which promised so much, so limited? A common argument made is that many devices do not support multicast, and this is examined in a later chapter. Jonathan Barter, a self-proclaimed mu ...
Putting BGP on the Right Path: Better Performance via Next-Hop Routing
... Today’s interdomain routing system does not perform well, because the BGP protocol converges slowly, selects paths without regard for performance, does not support multipath routing, and has numerous security vulnerabilities. Rather than adding mechanisms to an already complex protocol, or redesigni ...
... Today’s interdomain routing system does not perform well, because the BGP protocol converges slowly, selects paths without regard for performance, does not support multipath routing, and has numerous security vulnerabilities. Rather than adding mechanisms to an already complex protocol, or redesigni ...
Avaya Session Border Controller for Enterprise
... Avaya is not responsible for the contents or reliability of any linked websites referenced within this site or documentation provided by Avaya. Avaya is not responsible for the accuracy of any information, statement or content provided on these sites and does not necessarily endorse the products, se ...
... Avaya is not responsible for the contents or reliability of any linked websites referenced within this site or documentation provided by Avaya. Avaya is not responsible for the accuracy of any information, statement or content provided on these sites and does not necessarily endorse the products, se ...
cis82-mod7-DistanceVectorRouting-RIP
... Question: Why does RIP use a hop count as the route metric, and why is its maximum value limited to 15? Answer: “When RIP was designed and implemented, dynamic routing protocols were not widely used. Instead, networks relied mostly on static routing. RIP, even with its hop-count-metric – which seems ...
... Question: Why does RIP use a hop count as the route metric, and why is its maximum value limited to 15? Answer: “When RIP was designed and implemented, dynamic routing protocols were not widely used. Instead, networks relied mostly on static routing. RIP, even with its hop-count-metric – which seems ...
Chapter 7
... Question: Why does RIP use a hop count as the route metric, and why is its maximum value limited to 15? Answer: “When RIP was designed and implemented, dynamic routing protocols were not widely used. Instead, networks relied mostly on static routing. RIP, even with its hop-count-metric – which seems ...
... Question: Why does RIP use a hop count as the route metric, and why is its maximum value limited to 15? Answer: “When RIP was designed and implemented, dynamic routing protocols were not widely used. Instead, networks relied mostly on static routing. RIP, even with its hop-count-metric – which seems ...
Serial Server Installation Guide
... terminal protocol, supported on most UNIX systems, is an easy-touse interface that creates terminal connections to any network host supporting Telnet. Rlogin is a protocol that allows users to initiate a TCP/IP login session. UDP (User Datagram Protocol) is a connectionless protocol that results in ...
... terminal protocol, supported on most UNIX systems, is an easy-touse interface that creates terminal connections to any network host supporting Telnet. Rlogin is a protocol that allows users to initiate a TCP/IP login session. UDP (User Datagram Protocol) is a connectionless protocol that results in ...
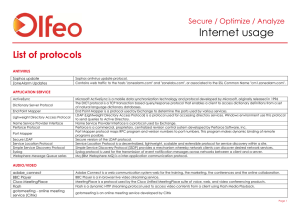
Internet usage
... Contains web traffic to the hosts "i711.com" and "vrsws.hovrs.com", or associated to the SSL Common Name "vrsws.hovrs.com". IBM Lotus Sametime is a client-server application and middleware platform that provides real-time, unified communications and collaboration for enterprises. Contains web traffi ...
... Contains web traffic to the hosts "i711.com" and "vrsws.hovrs.com", or associated to the SSL Common Name "vrsws.hovrs.com". IBM Lotus Sametime is a client-server application and middleware platform that provides real-time, unified communications and collaboration for enterprises. Contains web traffi ...
ITU ngn-fg-book-2 http://Certificate.Moscow
... To support these features, the network operator provides network connectivity services to its end users. A service level agreement (SLA) is a formal definition of the contractual relationship between service provider and its end user [14]. It specifies what the end user wants and what the supplier c ...
... To support these features, the network operator provides network connectivity services to its end users. A service level agreement (SLA) is a formal definition of the contractual relationship between service provider and its end user [14]. It specifies what the end user wants and what the supplier c ...
ATIS IPTV Standards Development via ATIS IPTV
... Description: Building upon the system requirements given in ATIS0800010, Emergency Alert Service Provisioning Specifications, the IPTV Emergency Alert System Metadata Specification in this document defines an XML schema used for delivery of emergency alert signaling and information to the IPTV ser ...
... Description: Building upon the system requirements given in ATIS0800010, Emergency Alert Service Provisioning Specifications, the IPTV Emergency Alert System Metadata Specification in this document defines an XML schema used for delivery of emergency alert signaling and information to the IPTV ser ...
dell poweredge vrtx and m-series compute nodes configuration study
... management tools, each potentially from different vendors. Disparate tools mean added complexity and administrative time when performing various configuration and management tasks such as updating firmware, making configuration changes, or troubleshooting issues. Among the other management headaches ...
... management tools, each potentially from different vendors. Disparate tools mean added complexity and administrative time when performing various configuration and management tasks such as updating firmware, making configuration changes, or troubleshooting issues. Among the other management headaches ...