CCNA2 Chapter 1 Wide Area Networks and Routers
... WAN – Wide Area Networks WAN is a data communications network that operates beyond a LAN’s geographic scope. ...
... WAN – Wide Area Networks WAN is a data communications network that operates beyond a LAN’s geographic scope. ...
Introduction - School of Engineering
... It should be noted that, in practice, the bit rate figures are less than the computed values since they include samples during the retrace times when the beam is switched off. Nevertheless, as we can deduce from the computed values, both the bit rate and the memory requirements are very large for bo ...
... It should be noted that, in practice, the bit rate figures are less than the computed values since they include samples during the retrace times when the beam is switched off. Nevertheless, as we can deduce from the computed values, both the bit rate and the memory requirements are very large for bo ...
Communicating over the Network - Seneca
... • The channel • Message destination – Data or information networks capable of carrying many different types of communications ...
... • The channel • Message destination – Data or information networks capable of carrying many different types of communications ...
Control System Specification
... 2.16. Distributed Control: A system whereby all control processing is decentralized and independent of a central computer. 2.17. Diagnostic Program: A machine-executable program with instructions used to detect and isolate system and component malfunctions. ...
... 2.16. Distributed Control: A system whereby all control processing is decentralized and independent of a central computer. 2.17. Diagnostic Program: A machine-executable program with instructions used to detect and isolate system and component malfunctions. ...
EEE449 Computer Networks - Universiti Sains Malaysia
... broad categories: elastic and inelastic. • Elastic traffic – can adjust, over wide ranges, to changes in delay and throughput across an internet and still meet the needs of its applications. – This is the traditional type of traffic supported on TCP/IP-based internets and is the type of traffic for ...
... broad categories: elastic and inelastic. • Elastic traffic – can adjust, over wide ranges, to changes in delay and throughput across an internet and still meet the needs of its applications. – This is the traditional type of traffic supported on TCP/IP-based internets and is the type of traffic for ...
Wireless/Cellular Technologies
... specific functions for paging and call forwarding termination of SS7 (signaling system no. 7) mobility specific signaling location registration and forwarding of location information provision of new services (fax, data calls) support of short message service (SMS) generation and forwarding of accou ...
... specific functions for paging and call forwarding termination of SS7 (signaling system no. 7) mobility specific signaling location registration and forwarding of location information provision of new services (fax, data calls) support of short message service (SMS) generation and forwarding of accou ...
Slide 1
... Wireless encryption scrambles data transmitted between wireless devices and then unscrambles the data only on devices that have a valid encryption key – WEP (Wired Equivalent Privacy) – WPA (Wi-Fi Protected Access) – WPA2 ...
... Wireless encryption scrambles data transmitted between wireless devices and then unscrambles the data only on devices that have a valid encryption key – WEP (Wired Equivalent Privacy) – WPA (Wi-Fi Protected Access) – WPA2 ...
Chapter 1 Lecture Presentation
... Transfers packets across multiple links and/or multiple networks Addressing must scale to large networks Nodes jointly execute routing algorithm to determine paths across the network Forwarding transfers packet across a node Congestion control to deal with traffic surges Connection setup, maintenanc ...
... Transfers packets across multiple links and/or multiple networks Addressing must scale to large networks Nodes jointly execute routing algorithm to determine paths across the network Forwarding transfers packet across a node Congestion control to deal with traffic surges Connection setup, maintenanc ...
Trust, Privacy, and Security - Computer Science
... China reached 167 million in April, 2002, a rise of 6 million subscribers on March, 2002. ...
... China reached 167 million in April, 2002, a rise of 6 million subscribers on March, 2002. ...
WiMAX
... Sleep mode management: This block handles sleep mode operation and generates management messages related to sleep operation and can communicate with the scheduler block to operate properly according to the sleep ...
... Sleep mode management: This block handles sleep mode operation and generates management messages related to sleep operation and can communicate with the scheduler block to operate properly according to the sleep ...
CORD Fabric, Overlay Virtualization, and Service Composition
... connect to spine switches. The spine switches use all of their ports to connect to the leaves. There is nothing sacred about this arrangement. In smaller deployments, more leaf ports can be used to connect servers, and in the extreme case, the spines can be eliminated altogether. Similarly, other ...
... connect to spine switches. The spine switches use all of their ports to connect to the leaves. There is nothing sacred about this arrangement. In smaller deployments, more leaf ports can be used to connect servers, and in the extreme case, the spines can be eliminated altogether. Similarly, other ...
《Electromagnetic Field and Microwave Technology》 Course syllabus
... One, the nature of the course, the purpose and the task High frequency electronic circuits is a professional basic courses of Communication Engineering Specialty .Through the studying of this course, make students familiar with the course described in various parts of the composition, characteristic ...
... One, the nature of the course, the purpose and the task High frequency electronic circuits is a professional basic courses of Communication Engineering Specialty .Through the studying of this course, make students familiar with the course described in various parts of the composition, characteristic ...
WiMAX Protocol - London South Bank University
... Most WiMax backers, including Clearwire in the United States (which has already built WiMax networks in many US cities), have signalled their intent to move across to LTE. It was never cost effective for WiMax networks to compete effectively against fixed-line broadband networks. What happened w ...
... Most WiMax backers, including Clearwire in the United States (which has already built WiMax networks in many US cities), have signalled their intent to move across to LTE. It was never cost effective for WiMax networks to compete effectively against fixed-line broadband networks. What happened w ...
Sample – Firewall PowerPoint
... – Access control and encryption on the same box – Requires client software or a 2nd gateway on the “far” end – Provides an encrypted session from the client to the gateway • prevents “eavesdropping” • allows the use of public networks like the Internet for private business communications, at signifi ...
... – Access control and encryption on the same box – Requires client software or a 2nd gateway on the “far” end – Provides an encrypted session from the client to the gateway • prevents “eavesdropping” • allows the use of public networks like the Internet for private business communications, at signifi ...
An Overview of Broadband Over Power Line
... upstream but does not come to Tom’s box, so Tom cannot see Harry’s data ...
... upstream but does not come to Tom’s box, so Tom cannot see Harry’s data ...
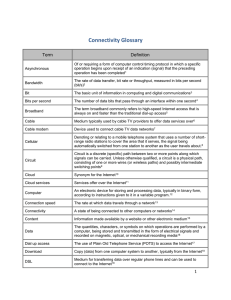
Connectivity Glossary
... The quantities, characters, or symbols on which operations are performed by a computer, being stored and transmitted in the form of electrical signals and recorded on magnetic, optical, or mechanical recording media16 ...
... The quantities, characters, or symbols on which operations are performed by a computer, being stored and transmitted in the form of electrical signals and recorded on magnetic, optical, or mechanical recording media16 ...
Net Tech Job Description
... A. Reviewing and interpreting Work orders, Network and circuit diagrams. B. Ability to troubleshoot using flow charts for power plants and rectifiers. C. Keeping a detailed written and/or mechanized record of work activities. D. Analyzing troubles, testing, repairing and turning up of customer circu ...
... A. Reviewing and interpreting Work orders, Network and circuit diagrams. B. Ability to troubleshoot using flow charts for power plants and rectifiers. C. Keeping a detailed written and/or mechanized record of work activities. D. Analyzing troubles, testing, repairing and turning up of customer circu ...
2. Advantages of Wireless LANs
... more than making an 802.11b device. So why not just wait for 802.11a? The answer is complex. First, there is the question of range. The laws of physics dictate that the range of free-space radio communications decreases with higher frequencies, but indoor propagation differs from free space because ...
... more than making an 802.11b device. So why not just wait for 802.11a? The answer is complex. First, there is the question of range. The laws of physics dictate that the range of free-space radio communications decreases with higher frequencies, but indoor propagation differs from free space because ...
Chapter 9.doc
... 3. With the necessary software, a printer with Internet printing capability can receive print instructions from desktop computers, mobile computers, or mobile devices. 4. A voice mail system seldom provides individual voice mailboxes. 5. In a networked environment, no authorized computer user can ac ...
... 3. With the necessary software, a printer with Internet printing capability can receive print instructions from desktop computers, mobile computers, or mobile devices. 4. A voice mail system seldom provides individual voice mailboxes. 5. In a networked environment, no authorized computer user can ac ...
Total Conversation through ITU
... ITU-T worked to add support for realtime text communication to the popular multimedia systems o Acceptable video support was more of an educational exercise… and the ITU-T has made an effort to educate! ...
... ITU-T worked to add support for realtime text communication to the popular multimedia systems o Acceptable video support was more of an educational exercise… and the ITU-T has made an effort to educate! ...
Total Conversation through ITU-T Standards
... ITU-T worked to add support for realtime text communication to the popular multimedia systems o Acceptable video support was more of an educational exercise… and the ITU-T has made an effort to educate! ...
... ITU-T worked to add support for realtime text communication to the popular multimedia systems o Acceptable video support was more of an educational exercise… and the ITU-T has made an effort to educate! ...
S-38.310 Thesis Seminar on Networking Technology
... band • 802.11a/g standards operate at up to 54Mbps in 5GHz frequency band • All of them follow the same MAC layer protocol • Security is the biggest problem of 802.11 standards. • Here we concentrate more on 802.11b ...
... band • 802.11a/g standards operate at up to 54Mbps in 5GHz frequency band • All of them follow the same MAC layer protocol • Security is the biggest problem of 802.11 standards. • Here we concentrate more on 802.11b ...
ShoreGear-90BRI Installation Guide
... Powering on the ShoreGear Voice Switch After connecting the switch to the network, power on the device by connecting it to an AC power source. 1. Plug an AC surge protector (not provided) into a grounded AC power source. 2. Plug one end of the provided power cord into the receptacle on the back of t ...
... Powering on the ShoreGear Voice Switch After connecting the switch to the network, power on the device by connecting it to an AC power source. 1. Plug an AC surge protector (not provided) into a grounded AC power source. 2. Plug one end of the provided power cord into the receptacle on the back of t ...
Telecommunications in Russia

Russia was among the first countries to introduce radio and television. Due to the enormous size of the country Russia leads in the number of TV broadcast stations and repeaters. There were few channels in the Soviet time, but in the past two decades many new state-run and private-owned radio stations and TV channels appeared.The telecommunications system in Russia has undergone significant changes since the 1980s, resulting in more than 1,000 companies licensed to offer communication services today. The foundation for liberalization of broadcasting was laid by the decree signed by the President of the USSR in 1990. Telecommunication is mainly regulated through the Federal Law ""On Communications"" and the Federal Law ""On Mass Media""The Soviet-time ""Ministry of communications of the RSFSR"" was through 1990s transformed to ""Ministry for communications and informatization"" and in 2004 it was renamed to ""Ministry of information technologies and communications (Mininformsvyazi)"", and since 2008 Ministry of Communications and Mass Media.Russia is served by an extensive system of automatic telephone exchanges connected by modern networks of fiber-optic cable, coaxial cable, microwave radio relay, and a domestic satellite system; cellular telephone service is widely available, expanding rapidly, and includes roaming service to foreign countries. Fiber to the x infrastructure has been expanded rapidly in recent years, principally by regional players including Southern Telecom Company, SibirTelecom, ER Telecom and Golden Telecom. Collectively, these players are having a significant impact of fiber broadband in regional areas, and are enabling operators to take advantage of consumer demand for faster access and bundled services.