File Systems_PPT_ch04
... Understanding File Systems Functions – Provide a hierarchical structure to organize files • A folder (directory) is an organizational structure that contains files and may additionally contain subfolders (subdirectories) under it. • The folder connects names to the files that are stored on the disk ...
... Understanding File Systems Functions – Provide a hierarchical structure to organize files • A folder (directory) is an organizational structure that contains files and may additionally contain subfolders (subdirectories) under it. • The folder connects names to the files that are stored on the disk ...
Virtualization
... Hardware support for full virtualization and paravirtualization • Recall that the IA-32 (x86) architecture creates some issues when it comes to virtualization. Certain privilegedmode instructions do not trap, and can return different results based upon the mode. For example, the x86 STR instruction ...
... Hardware support for full virtualization and paravirtualization • Recall that the IA-32 (x86) architecture creates some issues when it comes to virtualization. Certain privilegedmode instructions do not trap, and can return different results based upon the mode. For example, the x86 STR instruction ...
Appendix C: Windows 2000
... base priority), and an affinity for one or more processors Threads are the unit of execution scheduled by the kernel’s dispatcher Each thread has its own state, including a priority, processor affinity, and ...
... base priority), and an affinity for one or more processors Threads are the unit of execution scheduled by the kernel’s dispatcher Each thread has its own state, including a priority, processor affinity, and ...
Figure 5.01
... Linux refers to them as tasks rather than threads. Thread creation is done through clone() system call. Clone() allows a child task to share the address space of ...
... Linux refers to them as tasks rather than threads. Thread creation is done through clone() system call. Clone() allows a child task to share the address space of ...
3.5 Interprocess Communication
... – Messages can be passed in one direction at a time • One process is the sender and the other is the receiver – Message passing can be bidirectional • Each process can act as either a sender or a receiver – Messages can be blocking or nonblocking • Blocking requires the receiver to notify the sender ...
... – Messages can be passed in one direction at a time • One process is the sender and the other is the receiver – Message passing can be bidirectional • Each process can act as either a sender or a receiver – Messages can be blocking or nonblocking • Blocking requires the receiver to notify the sender ...
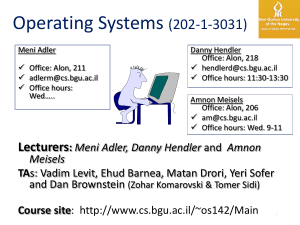
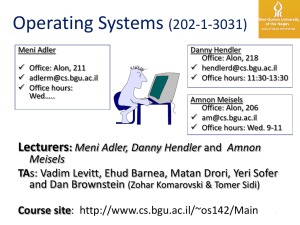
Operating Systems, 082
... file_name into argv and their number to argc Next, the shell uses fork() to create a process (same user ID) Now, it takes the executable name grep and the arguments, all from argv, and uses execvp() (or a similar system call) to run the grep executable On foreground execution, the shell would ...
... file_name into argv and their number to argc Next, the shell uses fork() to create a process (same user ID) Now, it takes the executable name grep and the arguments, all from argv, and uses execvp() (or a similar system call) to run the grep executable On foreground execution, the shell would ...
A Taxonomy of Computer Program Security Flaws, with Examples
... abstracted, could be used to focus efforts to remove security flaws and prevent their introduction. Other taxonomies [5,6,7] have recently been developed for organizing data about software defects and anomalies of all kinds. These are primarily oriented toward collecting data during software develop ...
... abstracted, could be used to focus efforts to remove security flaws and prevent their introduction. Other taxonomies [5,6,7] have recently been developed for organizing data about software defects and anomalies of all kinds. These are primarily oriented toward collecting data during software develop ...
Denali: Lightweight Virtual Machines
... In this paper, we present the design, implementation, and evaluation of the Denali isolation kernel, an x86-based operating system that isolates untrusted software services in separate protection domains. The architecture of Denali is similar to that of virtual machine monitors such as Disco [6], VM ...
... In this paper, we present the design, implementation, and evaluation of the Denali isolation kernel, an x86-based operating system that isolates untrusted software services in separate protection domains. The architecture of Denali is similar to that of virtual machine monitors such as Disco [6], VM ...
Introduction
... file_name into argv and their number to argc Next, the shell uses fork() to create a process (same user ID) Now, it takes the executable name grep and the arguments, all from argv, and uses execvp() (or a similar system call) to run the grep executable On foreground execution, the shell would ...
... file_name into argv and their number to argc Next, the shell uses fork() to create a process (same user ID) Now, it takes the executable name grep and the arguments, all from argv, and uses execvp() (or a similar system call) to run the grep executable On foreground execution, the shell would ...
Proceedings of the 5th Symposium on Operating Systems Design and Implementation USENIX Association
... In this paper, we present the design, implementation, and evaluation of the Denali isolation kernel, an x86-based operating system that isolates untrusted software services in separate protection domains. The architecture of Denali is similar to that of virtual machine monitors such as Disco [6], VM ...
... In this paper, we present the design, implementation, and evaluation of the Denali isolation kernel, an x86-based operating system that isolates untrusted software services in separate protection domains. The architecture of Denali is similar to that of virtual machine monitors such as Disco [6], VM ...
University of Tehran
... Exokernel records the allocator and the permissions and returns a “capability” – an encrypted cypher Every access to this page by the library requires this capability ...
... Exokernel records the allocator and the permissions and returns a “capability” – an encrypted cypher Every access to this page by the library requires this capability ...
UNIX
... When power is initially applied to the computer this triggers the RESET pin on the processor. This causes the processor to read from memory location 0xFFFFFFF0 and begin executing the code located there. This address is mapped to the ReadOnly Memory (ROM) containing the BIOS. The BIOS must poll the ...
... When power is initially applied to the computer this triggers the RESET pin on the processor. This causes the processor to read from memory location 0xFFFFFFF0 and begin executing the code located there. This address is mapped to the ReadOnly Memory (ROM) containing the BIOS. The BIOS must poll the ...
2_threads
... context switch happens after line 2, but before line 3, what is the value of the stored c? Lec 2 ...
... context switch happens after line 2, but before line 3, what is the value of the stored c? Lec 2 ...
Kernel I/O Subsystem
... - driver end interfaces with the device - zero or more STREAM modules between them. Each module contains a read queue and a write queue Message passing is used to communicate between queues ...
... - driver end interfaces with the device - zero or more STREAM modules between them. Each module contains a read queue and a write queue Message passing is used to communicate between queues ...
Berkeley Software Distribution
Berkeley Software Distribution (BSD) is a Unix operating system derivative developed and distributed by the Computer Systems Research Group (CSRG) of the University of California, Berkeley, from 1977 to 1995. Today the term ""BSD"" is often used non-specifically to refer to any of the BSD descendants which together form a branch of the family of Unix-like operating systems. Operating systems derived from the original BSD code remain actively developed and widely used.Historically, BSD has been considered a branch of Unix, Berkeley Unix, because it shared the initial codebase and design with the original AT&T Unix operating system. In the 1980s, BSD was widely adopted by vendors of workstation-class systems in the form of proprietary Unix variants such as DEC ULTRIX and Sun Microsystems SunOS. This can be attributed to the ease with which it could be licensed, and the familiarity the founders of many technology companies of the time had with it.Although these proprietary BSD derivatives were largely superseded by the UNIX System V Release 4 and OSF/1 systems in the 1990s (both of which incorporated BSD code and are the basis of other modern Unix systems), later BSD releases provided a basis for several open source development projects, e.g. FreeBSD, OpenBSD, NetBSD, Darwin or PC-BSD, that are ongoing. These, in turn, have been incorporated in whole or in part in modern proprietary operating systems, e.g. the TCP/IP networking code in Windows NT 3.1 and most of the foundation of Apple's OS X and iOS.