(PPT, 739KB)
... Given that there is a myriad of clustering algorithms and objectives, it is helpful to reason about clustering independently of any particular algorithm, objective function, or generative data model. This can be achieved by defining a clustering function as one that satisfies a set of properties. Th ...
... Given that there is a myriad of clustering algorithms and objectives, it is helpful to reason about clustering independently of any particular algorithm, objective function, or generative data model. This can be achieved by defining a clustering function as one that satisfies a set of properties. Th ...
using SAP Predictive Analysis
... The authors of this article have closely observed the Predictive Analysis & HANA communities online where members are constantly looking for two important things; 1. How to write back from BI tools to SAP HANA 2. How BI tools can use predictive models created with SAP Predictive Analysis or SAP Infi ...
... The authors of this article have closely observed the Predictive Analysis & HANA communities online where members are constantly looking for two important things; 1. How to write back from BI tools to SAP HANA 2. How BI tools can use predictive models created with SAP Predictive Analysis or SAP Infi ...
Post-mining of Association Rules: Techniques
... amounts of association rules. Different from traditional methods of association rule visualization where association rule extraction and visualization are treated separately in a one-way process, the two proposed approaches that use meta-knowledge to guide the user during the mining process in an in ...
... amounts of association rules. Different from traditional methods of association rule visualization where association rule extraction and visualization are treated separately in a one-way process, the two proposed approaches that use meta-knowledge to guide the user during the mining process in an in ...
Integration Services Transformations | Microsoft Docs
... The number of groups that are expected to result from a Group by operation on the column. The number of distinct values that are expected to result from a Count distinct operation on the column. You can also identify columns as IsBig if a column contains large numeric values or numeric values with h ...
... The number of groups that are expected to result from a Group by operation on the column. The number of distinct values that are expected to result from a Count distinct operation on the column. You can also identify columns as IsBig if a column contains large numeric values or numeric values with h ...
Predictive Analytics
... predictive analytics today predictive analytics data - predictive analytics data mining big data text analytics business intelligence social media analytics cloud digital and emerging technology, who uses predictive analytics fico - predictive analytics is widely used to solve real world problems i ...
... predictive analytics today predictive analytics data - predictive analytics data mining big data text analytics business intelligence social media analytics cloud digital and emerging technology, who uses predictive analytics fico - predictive analytics is widely used to solve real world problems i ...
Clustering
... Phase 1: scan DB to build an initial in-memory CF tree (a multi-level compression of the data that tries to preserve the inherent clustering structure of the data) Phase 2: use an arbitrary clustering algorithm to cluster the leaf nodes of the CF-tree ...
... Phase 1: scan DB to build an initial in-memory CF tree (a multi-level compression of the data that tries to preserve the inherent clustering structure of the data) Phase 2: use an arbitrary clustering algorithm to cluster the leaf nodes of the CF-tree ...
An automatic email mining approach using semantic non
... copyright holder (original author), cannot be used for any commercial purposes, and may not be altered. Any other use would require the permission of the copyright holder. Students may inquire about withdrawing their dissertation and/or thesis from this database. For additional inquiries, please con ...
... copyright holder (original author), cannot be used for any commercial purposes, and may not be altered. Any other use would require the permission of the copyright holder. Students may inquire about withdrawing their dissertation and/or thesis from this database. For additional inquiries, please con ...
Data Mining. Concepts and Techniques, 3rd Edition (The
... permission, further information about the Publisher’s permissions policies and our arrangements with organizations such as the Copyright Clearance Center and the Copyright Licensing Agency, can be found at our website: www.elsevier.com/permissions. This book and the individual contributions containe ...
... permission, further information about the Publisher’s permissions policies and our arrangements with organizations such as the Copyright Clearance Center and the Copyright Licensing Agency, can be found at our website: www.elsevier.com/permissions. This book and the individual contributions containe ...
Data Mining - Lyle School of Engineering
... computational model consisting of five parts: – A starting set of individuals, P. – Crossover: technique to combine two parents to create offspring. – Mutation: randomly change an individual. – Fitness: determine the best individuals. – Algorithm which applies the crossover and mutation techniques t ...
... computational model consisting of five parts: – A starting set of individuals, P. – Crossover: technique to combine two parents to create offspring. – Mutation: randomly change an individual. – Fitness: determine the best individuals. – Algorithm which applies the crossover and mutation techniques t ...
Data Mining - Lyle School of Engineering
... computational model consisting of five parts: – A starting set of individuals, P. – Crossover: technique to combine two parents to create offspring. – Mutation: randomly change an individual. – Fitness: determine the best individuals. – Algorithm which applies the crossover and mutation techniques t ...
... computational model consisting of five parts: – A starting set of individuals, P. – Crossover: technique to combine two parents to create offspring. – Mutation: randomly change an individual. – Fitness: determine the best individuals. – Algorithm which applies the crossover and mutation techniques t ...
Fuzzy Miner A Fuzzy System for Solving Pattern - CEUR
... computations of the components are largely independent of each other. But drawbacks are, the impossibility to extract rules from neurons for interpretation, and that prior knowledge cannot be used to initialize the system. As such, the training of the computer to optimize the classifier is usually m ...
... computations of the components are largely independent of each other. But drawbacks are, the impossibility to extract rules from neurons for interpretation, and that prior knowledge cannot be used to initialize the system. As such, the training of the computer to optimize the classifier is usually m ...
Cooperative Clustering Model and Its Applications
... I hereby declare that I am the sole author of this thesis. This is a true copy of the thesis, including any required final revisions, as accepted by my examiners. I understand that my thesis may be made electronically available to the public. ...
... I hereby declare that I am the sole author of this thesis. This is a true copy of the thesis, including any required final revisions, as accepted by my examiners. I understand that my thesis may be made electronically available to the public. ...
Discovering Multiple Clustering Solutions
... Challenge: High Dimensional Data Considering more and more attributes... Objects become unique, known as the “curse of dimensionality” (Beyer et al., 1999) ...
... Challenge: High Dimensional Data Considering more and more attributes... Objects become unique, known as the “curse of dimensionality” (Beyer et al., 1999) ...
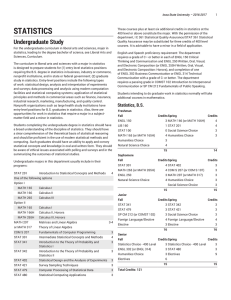
STATISTICS
... Graduates of co-major Ph.D. programs in statistics and an area of theoretical mathematics have mastered basic statistical methods and have studied advanced statistical theory. Students complete a minimum of 72 semester credits. Co-major professors assist the student in preparing a dissertation tha ...
... Graduates of co-major Ph.D. programs in statistics and an area of theoretical mathematics have mastered basic statistical methods and have studied advanced statistical theory. Students complete a minimum of 72 semester credits. Co-major professors assist the student in preparing a dissertation tha ...
Developing Efficient Algorithms for Incremental Mining of Sequential
... Chapter 5 introduces two algorithms ‚Constraint-based sequential pattern mining algorithm incorporating compactness, length and monetary‛ and ‚CFM-PrefixSpan algorithm‛. Both these algorithms are for mining constraint based sequential patterns and are based on projection-based pattern growth approac ...
... Chapter 5 introduces two algorithms ‚Constraint-based sequential pattern mining algorithm incorporating compactness, length and monetary‛ and ‚CFM-PrefixSpan algorithm‛. Both these algorithms are for mining constraint based sequential patterns and are based on projection-based pattern growth approac ...
STATISTICS
... theory and methods. Elective courses in the M.S. program provide an opportunity for students to emphasize particular areas of statistical methods or application in their program. Students complete a minimum of 34 semester credits, including work on a capstone project resulting in a written creativ ...
... theory and methods. Elective courses in the M.S. program provide an opportunity for students to emphasize particular areas of statistical methods or application in their program. Students complete a minimum of 34 semester credits, including work on a capstone project resulting in a written creativ ...
THE APPLICATION OF EXPLORATORY DATA ANALYSIS IN
... EDA techniques, such as descriptive statistics, data transformation, and data visualization, are applied in this credit card retention case. Descriptive statistics can reveal the distribution of the data, and data visualization techniques can display the distribution in an effective way so that audi ...
... EDA techniques, such as descriptive statistics, data transformation, and data visualization, are applied in this credit card retention case. Descriptive statistics can reveal the distribution of the data, and data visualization techniques can display the distribution in an effective way so that audi ...
Nonlinear dimensionality reduction

High-dimensional data, meaning data that requires more than two or three dimensions to represent, can be difficult to interpret. One approach to simplification is to assume that the data of interest lie on an embedded non-linear manifold within the higher-dimensional space. If the manifold is of low enough dimension, the data can be visualised in the low-dimensional space.Below is a summary of some of the important algorithms from the history of manifold learning and nonlinear dimensionality reduction (NLDR). Many of these non-linear dimensionality reduction methods are related to the linear methods listed below. Non-linear methods can be broadly classified into two groups: those that provide a mapping (either from the high-dimensional space to the low-dimensional embedding or vice versa), and those that just give a visualisation. In the context of machine learning, mapping methods may be viewed as a preliminary feature extraction step, after which pattern recognition algorithms are applied. Typically those that just give a visualisation are based on proximity data – that is, distance measurements.