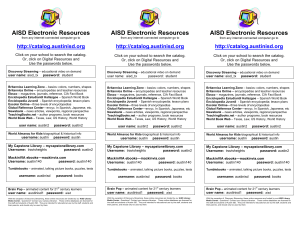
AISD Electronic Resources 2016 - Travis Heights Elementary School
... user name: austinisd1 password: aisd ...
... user name: austinisd1 password: aisd ...
Virtual Private Network (VPN)
... because the resulting network is completely private. • The chief advantage of using Internet connections is low cost. • Unfortunately, the Internet cannot guarantee confindentiality. As it travels from source to destination, a datagram passes across intermediate networks that may be shared. As a con ...
... because the resulting network is completely private. • The chief advantage of using Internet connections is low cost. • Unfortunately, the Internet cannot guarantee confindentiality. As it travels from source to destination, a datagram passes across intermediate networks that may be shared. As a con ...
The Top Six Risks of Employee Internet Use and How
... Phishing is a relatively new tool used by criminals to drive unsuspecting email users to fake sites for the purpose of retrieving personal information. Phishing exploits use emails designed to mimic legitimate sites such as wellknown banks, or popular sites like eBay, Amazon, and others. These offic ...
... Phishing is a relatively new tool used by criminals to drive unsuspecting email users to fake sites for the purpose of retrieving personal information. Phishing exploits use emails designed to mimic legitimate sites such as wellknown banks, or popular sites like eBay, Amazon, and others. These offic ...
www.yorktech.com
... masquerading, a technique that maps unregistered IP addresses to a single registered IP address combined with a port number. ...
... masquerading, a technique that maps unregistered IP addresses to a single registered IP address combined with a port number. ...
Comprehension
... Comprehension * What methods does Chinese government employ to exorcise “bad speech” from the Internet? Governments employ a number of methods to exorcise "bad speech" from the Internet. Real name registration is just one tool of the trade. Some might suggest that real name registration and other m ...
... Comprehension * What methods does Chinese government employ to exorcise “bad speech” from the Internet? Governments employ a number of methods to exorcise "bad speech" from the Internet. Real name registration is just one tool of the trade. Some might suggest that real name registration and other m ...
Train Machine Learning Models
... language patterns associated with suicide risk and sexual predation are more easily detected in online messages. However, bullying language is highly subjective and continuously evolving. The company was having difficulty building algorithms that could accurately and systematically identify true onl ...
... language patterns associated with suicide risk and sexual predation are more easily detected in online messages. However, bullying language is highly subjective and continuously evolving. The company was having difficulty building algorithms that could accurately and systematically identify true onl ...
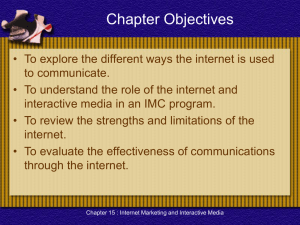
Promotion Management
... • Disseminate information – Primary objective for using the web is to provide indepth information about the company. – Having a website has become a necessity in B2B ...
... • Disseminate information – Primary objective for using the web is to provide indepth information about the company. – Having a website has become a necessity in B2B ...
ch15 - Home - KSU Faculty Member websites
... Reproduction or translation of this work beyond that permitted in Section 117 of the 1976 United States Copyright Act without the express written permission of the copyright owner is unlawful. Request for further information should be addressed to the Permissions Department, John Wiley & Sons, Inc. ...
... Reproduction or translation of this work beyond that permitted in Section 117 of the 1976 United States Copyright Act without the express written permission of the copyright owner is unlawful. Request for further information should be addressed to the Permissions Department, John Wiley & Sons, Inc. ...
Users - Makerere University E
... Auctioning Cars – Auto dealers (autobytel.com) have a websites where consumers are able to see the pictures of cars they are interested in. Cost of the cars and transportation costs are quoted online. Art auctions – art work is sold online at various sites such as onlineart.com Airlines – several ai ...
... Auctioning Cars – Auto dealers (autobytel.com) have a websites where consumers are able to see the pictures of cars they are interested in. Cost of the cars and transportation costs are quoted online. Art auctions – art work is sold online at various sites such as onlineart.com Airlines – several ai ...
Document
... personal information to people who claim to need it Security concerns is fear of unauthorized access and manipulation of data by people who does not have a legitimate need of it ...
... personal information to people who claim to need it Security concerns is fear of unauthorized access and manipulation of data by people who does not have a legitimate need of it ...
Research Paper
... security, such as drug smuggling or trafficking. The potentially useful data is then being saved. However strictly classified, information about this program leaked due to a whistleblower and former intelligence contractor Edward Snowden. In the weeks since the PRISM documents leaked, a widespread i ...
... security, such as drug smuggling or trafficking. The potentially useful data is then being saved. However strictly classified, information about this program leaked due to a whistleblower and former intelligence contractor Edward Snowden. In the weeks since the PRISM documents leaked, a widespread i ...
Mapping - Syslab
... on an Internet, we can build a good picture of the center of the Internet. Large intranets are hard to manage and offer many security problems. They discovered that mapping is a more useful pursuit for an intranet. ...
... on an Internet, we can build a good picture of the center of the Internet. Large intranets are hard to manage and offer many security problems. They discovered that mapping is a more useful pursuit for an intranet. ...
Safe internet Network Base for schools and business use: Οδηγός
... kind of software on the school’s computers or other devices. In this way, the entire school network is secure and protected even when visitors, students and/or members of personnel are connected wirelessly through the school’s connection. According to the needs of each particular school, user profil ...
... kind of software on the school’s computers or other devices. In this way, the entire school network is secure and protected even when visitors, students and/or members of personnel are connected wirelessly through the school’s connection. According to the needs of each particular school, user profil ...
McGill University Monday, Sept 21 st 2009
... segmented in to packets and transported by the network as fast as possible via best effort, with minimal redundancy checks, and coherence checks were left for higher level applications. The second most important design goal was that the internet had to support many types of communication services wi ...
... segmented in to packets and transported by the network as fast as possible via best effort, with minimal redundancy checks, and coherence checks were left for higher level applications. The second most important design goal was that the internet had to support many types of communication services wi ...
What is the time-interval threshold to determine whether we consider
... S. Felix Wu Presented by Zhenzhen Yan April. 11, 2007 ...
... S. Felix Wu Presented by Zhenzhen Yan April. 11, 2007 ...
here - Penndel Mental Health Center
... The Information Technology Department shall periodically review and recommend changes to web and protocol filtering rules. Human Resources shall review these recommendations and decide if any changes are to be made. Changes to web and protocol filtering rules will be recorded in the Internet Use Mon ...
... The Information Technology Department shall periodically review and recommend changes to web and protocol filtering rules. Human Resources shall review these recommendations and decide if any changes are to be made. Changes to web and protocol filtering rules will be recorded in the Internet Use Mon ...
Internet Techniques
... IMS. Cyber threats and cyber defence. Internet based social networking (e.g. Twitter, Youtube). Military networks, cyber warfare. Semantic Web and Web 2.0. SOA. IoS. P2P. Cloud computing. Laboratories exercises are relevant to the issues raised at the lecture. Students learn the practical use of too ...
... IMS. Cyber threats and cyber defence. Internet based social networking (e.g. Twitter, Youtube). Military networks, cyber warfare. Semantic Web and Web 2.0. SOA. IoS. P2P. Cloud computing. Laboratories exercises are relevant to the issues raised at the lecture. Students learn the practical use of too ...
View Report - PDF
... Information Technology in writing or by email. Information Technology will unblock that site or category for that associate only. Information Technology will track approved exceptions and report on them upon request. 4.0 Enforcement The IT Security Officer will periodically review Internet use monit ...
... Information Technology in writing or by email. Information Technology will unblock that site or category for that associate only. Information Technology will track approved exceptions and report on them upon request. 4.0 Enforcement The IT Security Officer will periodically review Internet use monit ...
Proposed Differentiated Services on the Internet
... of various types of data into the web published documents HTTP makes it possible for web sites to offer binary files, images, and multimedia documents to the users with the click of a button HTTP has also resulted in making the Internet very popular. Internet continues to expand in number of web ...
... of various types of data into the web published documents HTTP makes it possible for web sites to offer binary files, images, and multimedia documents to the users with the click of a button HTTP has also resulted in making the Internet very popular. Internet continues to expand in number of web ...
Challenges of protecting safety internet enviroment for children in
... Forum and Chat room are comfortable communication channels for all children, Easy to build, so many dangerous website, forum and chat room are propagating unsuitable information for children. These channels allows criminals to hide effectively their traces. But It’s very difficulty to censor a ...
... Forum and Chat room are comfortable communication channels for all children, Easy to build, so many dangerous website, forum and chat room are propagating unsuitable information for children. These channels allows criminals to hide effectively their traces. But It’s very difficulty to censor a ...
Teenager in virtual reality
... a source of information for somebody, i.e. anything that might inform a person about something or provide knowledge to somebody. ...
... a source of information for somebody, i.e. anything that might inform a person about something or provide knowledge to somebody. ...
Online shaming

Online shaming is a form of Internet vigilantism in which targets are publicly humiliated using technology like social and new media. Proponents of shaming see it as a form of online participation that allows hacktivists and cyber-dissidents to right injustices. Critics see it as a tool that encourages online mobs to destroy the reputation and careers of people who made perceived slights.Online shaming frequently involves the publication of private information on the Internet (called doxing), which can frequently lead to hate messages and death threats being used to intimidate that person. The ethics of public humiliation has been a source of debate over privacy and ethics.