* Your assessment is very important for improving the work of artificial intelligence, which forms the content of this project
Download Core network components - Charles Sturt University
Asynchronous Transfer Mode wikipedia , lookup
Piggybacking (Internet access) wikipedia , lookup
Multiprotocol Label Switching wikipedia , lookup
Power over Ethernet wikipedia , lookup
Network tap wikipedia , lookup
Computer network wikipedia , lookup
Airborne Networking wikipedia , lookup
List of wireless community networks by region wikipedia , lookup
Internet protocol suite wikipedia , lookup
Nonblocking minimal spanning switch wikipedia , lookup
Cracking of wireless networks wikipedia , lookup
Zero-configuration networking wikipedia , lookup
Point-to-Point Protocol over Ethernet wikipedia , lookup
Wake-on-LAN wikipedia , lookup
Recursive InterNetwork Architecture (RINA) wikipedia , lookup
IEEE 802.1aq wikipedia , lookup
ITC242 – Introduction to
Data Communications
Chapter 10
1
Last Week
Internet Operation
• Describe the characteristics of an Internet
Address
• Describe the different classes of IP
addresses
• Explain the purpose of subnet masks.
2
Last Week
LAN architecture and protocols
• Define the various types of Local Area
Networks (LANs)
• Discuss the different types of transmission
media commonly used in LANs.
3
Topic 10 - Ethernet
• Learning Objectives
• Describe the characteristics of Ethernet
networks
• Discuss the operation of CSMA/CD
• Discuss the operation of bridges, hubs,
and switches
• Describe the characteristics of fast
Ethernet standards.
4
The Link Layer
Session
Transport
Network
Link
Physical
The 7-layer OSI Model
TCP
TFTP
HTTP
NNTP
Presentation
Telnet
FTP
SMTP
Application
UDP
IP
LAN-LINK
The 4-layer Internet Model
5
Link Layer: Introduction
Some terminology:
• hosts and routers are
nodes
• communication channels
that connect adjacent
nodes along communication
path are links
– wired links
– wireless links
– LANs
• layer-2 packet is a frame,
encapsulates datagram
data-link layer has responsibility of
transferring datagram from one node
to adjacent node over a link
6
Link layer: context
• datagram transferred transportation analogy
by different link
• trip from Melbourne to Brisbane
protocols over different
– car: Melbourne to Albury
links:
– train : Albury to Sydney
– e.g., Ethernet on first
link, frame relay on
intermediate links,
802.11 on last link
• each link protocol
provides different
services
– e.g., may or may not
provide reliable data
transmission over link
– plane : Sydney to Bridbane
• tourist = datagram
• transport segment =
communication link
• transportation mode = link layer
protocol
• travel agent = routing algorithm
7
Link Layer Services
• framing, link access:
– encapsulate datagram into frame, adding header,
trailer
– channel access if shared medium
– “MAC” addresses used in frame headers to
identify source, dest
• different from IP address!
• reliable delivery between adjacent nodes
– we learned how to do this already!
– seldom used on low bit-error link (fiber, some
twisted pair)
– wireless links: high error rates
• Q: why both link-level and end-end reliability?
8
Link Layer Services (more)
• flow control:
– pacing between adjacent sending and receiving
nodes
• error detection:
– errors caused by signal attenuation, noise.
– receiver detects presence of errors:
• signals sender for retransmission or drops frame
• error correction:
– receiver identifies and corrects bit error(s) without
resorting to retransmission
• half-duplex and full-duplex
– with half duplex, nodes at both ends of link can
transmit, but not at same time
9
Where is the link layer
implemented?
• in each and every host
• link layer implemented in
“adaptor” (aka network
interface card NIC)
– Ethernet card, PCMCI
card, 802.11 card
– implements link,
physical layer
• attaches into host’s
system buses
• combination of hardware,
software, firmware
host schematic
application
transport
network
link
cpu
memory
controller
link
physical
host
bus
(e.g., PCI)
physical
transmission
network adapter
card
10
Adaptors Communicating
datagram
datagram
controller
controller
receiving host
sending host
datagram
frame
• sending side:
– encapsulates
datagram in frame
– adds error checking
bits, rdt, flow control,
etc.
• receiving side
– looks for errors, rdt,
flow control, etc
– extracts datagram,
passes to upper layer
at receiving side
11
Multiple Access Links and Protocols
Two types of “links”:
• point-to-point
– PPP ( point-to-point protocol) for dial-up access
– point-to-point link between Ethernet switch and host
• broadcast (shared wire or medium): multiple sending and
receiving nodes all connected to the same, single, shared
broadcast channel. Any one node transmits a frame, the
channel broadcasts the frame and each of other nodes receives
a copy
– old-fashioned Ethernet
– 802.11 wireless LAN
shared wire (e.g.,
cabled Ethernet)
shared RF
(e.g., 802.11 WiFi)
shared RF
(satellite)
humans at a
cocktail party
(shared air, acoustical)
12
Multiple Access protocols
• single shared broadcast channel
• two or more simultaneous transmissions by
nodes: interference
– collision if node receives two or more signals at the
same time
multiple access protocol
• distributed algorithm that determines how nodes
share channel, i.e., determine when node can
transmit
• communication about channel sharing must use
channel itself!
13
MAC Protocols: a taxonomy
Three broad classes:
• Channel Partitioning
– divide channel into smaller “pieces” (time slots,
frequency, code)
– allocate piece to node for exclusive use
• Random Access
– channel not divided, allow collisions
– “recover” from collisions
• “Taking turns”
– nodes take turns, but nodes with more to send can
take longer turns
14
Random Access Protocols
• When node has packet to send
– transmit at full channel data rate R.
– no a priori coordination among nodes
• two or more transmitting nodes ➜ “collision”,
• random access MAC protocol specifies:
– how to detect collisions
– how to recover from collisions (e.g., via delayed
retransmissions)
• Examples of random access MAC protocols:
– CSMA, CSMA/CD, CSMA/CA
15
CSMA/CD Protocol
All hosts transmit & receive on one channel
Packets are of variable size.
When a host has a packet to transmit:
1. Carrier Sense: Check that the line is quiet before transmitting.
2. Collision Detection: Detect collision as soon as possible. If a
collision is detected, stop transmitting; wait a random time,
then return to step 1.
16
Token Passing
• A token rotates around a ring to each node in
turn.
• All nodes (computers, routers, etc.) copy all data
and tokens, and repeat them along the ring.
• When a node wishes to transmit packet(s), it
grabs the token as it passes.
• It holds the token while it transmits.
• When it is done, it releases the token again and
sends it on its way.
17
“Taking Turns” MAC protocols
Polling:
• master node
“invites” slave nodes
to transmit in turn
• typically used with
“dumb” slave
devices
• concerns:
– polling overhead
– latency
– single point of failure
(master)
data
poll
master
data
slaves
18
“Taking Turns” MAC protocols
Token passing:
• control token
passed from one
node to next
sequentially.
• token message
• concerns:
– token overhead
– latency
– single point of failure
(token)
T
(nothing
to send)
T
data
19
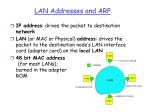
MAC Addresses
• 32-bit IP address:
– network-layer address
– used to get datagram to destination IP subnet
• MAC (or LAN or physical or Ethernet)
address:
– function: get frame from one interface to
another physically-connected interface (same
network)
– 48 bit MAC address (for most LANs)
• burned in NIC ROM, also sometimes software
settable
20
LAN Addresses
Each adapter on LAN has unique LAN address
1A-2F-BB-76-09-AD
( hexadecimal)
71-65-F7-2B-08-53
LAN
(wired or
wireless)
Broadcast address =
FF-FF-FF-FF-FF-FF
= adapter
58-23-D7-FA-20-B0
0C-C4-11-6F-E3-98
21
LAN Address (more)
• MAC address allocation administered by IEEE
• manufacturer buys portion of MAC address
space (to assure uniqueness)
• analogy:
(a) MAC address: like Social Security
Number
(b) IP address: like postal address
• MAC flat address ➜ portability
– can move LAN card from one LAN to another
• IP hierarchical address NOT portable
– address depends on IP subnet to which node is
attached
22
Ethernet Frame Structure
Sending adapter encapsulates IP datagram (or
other network layer protocol packet) in
Ethernet frame
Preamble:
• 7 bytes with pattern 10101010 (“wake up”)
followed by one byte with pattern 10101011
• used to synchronize receiver, sender clock
rates
23
Ethernet Frame Structure (more)
• Addresses: 6 bytes
– if adapter receives frame with matching
destination address, or with broadcast address, it
passes data in frame to network layer protocol
– otherwise, adapter discards frame
• Type: indicates higher layer protocol (mostly IP but
others possible, e.g., Novell IPX, AppleTalk)
• CRC: checked at receiver, if error is detected, frame
is dropped
24
Ethernet: Unreliable,
connectionless
• connectionless: No handshaking between
sending and receiving NICs
• unreliable: receiving NIC doesn’t send acks to
sending NIC
– stream of datagrams passed to network layer can
have gaps (missing datagrams)
– gaps will be filled if app is using TCP
– otherwise, app will see gaps
• Ethernet’s MAC protocol: unslotted CSMA/CD
25
Ethernet CSMA/CD algorithm
1. NIC receives datagram 4. If NIC detects another
from network layer,
transmission while
creates frame
transmitting, aborts and
sends jam signal( to make sure
2. If NIC senses channel
all other transmitters are aware of collision;
idle, starts frame
48 bits)
transmission If NIC
senses channel busy, 5. During aborting, after
waits until channel idle, mth collision, NIC
chooses K at random
then transmits
from{0,1,2,…,2m-1}. NIC
3. If NIC transmits entire
waits K·512 bit times(Bit time:
frame without detecting .1 microsec for 10 Mbps Ethernet ;
another transmission,
for K=1023, wait time is about 50 msec),
26
NIC is done with frame ! returns to Step 2
The Original Ethernet
Repeaters
every
500m
10Mb/s
l 1500m
Thick copper
coaxial cable
In practice, minimum packet size = 512 bits.
• allows for extra time to detect collisions.
• allows for “repeaters” that can boost signal.
27
802.3 Ethernet Standards: Link & Physical
Layers
• many different Ethernet standards
– common MAC protocol and frame format
– different speeds: 2 Mbps, 10 Mbps, 100
Mbps, 1Gbps, 10G bps
– different physical layer media: fiber, cable
application
transport
network
link
physical
MAC protocol
and frame format
100BASE-TX
100BASE-T2
100BASE-FX
100BASE-T4
100BASE-SX
100BASE-BX
copper (twister
pair) physical layer
fiber physical layer
28
802.3 Medium Notation
• Notation format:
<data rate in Mbps><signaling
method><maximum segment length in
hundreds of meters>
• e.g 10Base5 provides 10Mbps baseband,
up to 500 meters
• T and F are used in place of segment
length for twisted pair and fiber
29
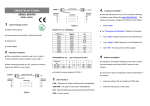
802.3 10BaseX Media Options
30
An Ethernet Network
Problem:
Router
Outside
world
Shared
network limits throughput.
Lots of collisions reduces efficiency.
31
Ethernet Switching
Ethernet
Switch
Benefits:
Number of collisions is reduced. If only one computer per port,
no collisions can take place (each cable is now a self-contained
point-to-point Ethernet link).
Capacity is increased: the switch can forward multiple frames
to different computers at the same time.
Router
Outside
world
32
Switch
• link-layer device: smarter than hubs, take
active role
– store, forward Ethernet frames
– examine incoming frame’s MAC address,
selectively forward frame to one-or-more
outgoing links when frame is to be forwarded
on segment, uses CSMA/CD to access
segment
• transparent
– hosts are unaware of presence of switches
• plug-and-play, self-learning
– switches do not need to be configured
33
One Ethernet Switch in
“Packard”
34
Star topology
• bus topology popular through mid 90s
– all nodes in same collision domain (can collide
with each other)
• today: star topology prevails
– active switch in center
– each “spoke” runs a (separate) Ethernet protocol
(nodes do not collide with each other)
switch
bus: coaxial cable
star
35
Switch: allows multiple simultaneous
transmissions
A
• hosts have dedicated, direct
connection to switch
• switches buffer packets
• Ethernet protocol used on
each incoming link, but no
collisions; full duplex
– each link is its own
collision domain
• switching: A-to-A’ and B-to-B’
simultaneously, without
collisions
– not possible with dumb
hub
C’
B
6
1
5
2
3
4
C
B’
A’
switch with six interfaces
(1,2,3,4,5,6)
36
Switch Table
• Q: how does switch know
that A’ reachable via
interface 4, B’ reachable
via interface 5?
• A: each switch has a
switch table, each entry:
– (MAC address of host,
interface to reach host, time
stamp)
• looks like a routing table!
• Q: how are entries created,
maintained in switch table?
– something like a routing
protocol?
A
C’
B
6
1
5
2
3
4
C
B’
A’
switch with six interfaces
(1,2,3,4,5,6)
37
Switch: self-learning
• switch learns
which hosts can be
reached through
which interfaces
– when frame
received, switch
“learns” location of
sender: incoming
LAN segment
– records
MAC addr
sender/location
A
pair in switch table
Source: A
Dest: A’
A A A’
C’
B
1
6
5
2
3
4
C
B’
A’
interface TTL
1
60
Switch table
(initially empty)
TTL: time-to-live
38
Switch: frame filtering/forwarding
When frame received:
1. record link associated with sending host
2. index switch table using MAC dest address
3. if entry found for destination
then {
if dest on segment from which frame arrived
then drop the frame
else forward the frame on interface indicated
}
forward on all but the interface
else flood
on which the frame arrived
39
Selflearning,
forwarding:
example
Source: A
Dest: A’
A A A’
C’
• frame destination
unknown: flood
• destination A
location known:
selective send
B
A6A’
1
2
4
5
C
A’ A
B’
3
A’
MAC addr interface TTL
A
A’
1
4
60
60
Switch table
(initially empty)
40
Interconnecting switches
• switches can be connected together
S4
S1
S2
A
B
S3
C
F
D
E
I
G
H
• Q: sending from A to F - how does S1 know to
forward frame destined to F via S4 and S3?
• A: self learning! (works exactly the same as in
single-switch case!)
41
Institutional Network
to external
network
mail server
router
web server
IP subnet
42
Switches vs. Routers
• both store-and-forward devices
– routers: network layer devices (examine network
layer headers)
– switches are link layer devices
• routers maintain routing tables, implement routing
algorithms
• switches maintain switch tables, implement filtering,
learning algorithms
43
Hubs
• Alternative to bus topology
• Each station is connected to the hub by two lines
(transmit and receive)
• When a single station transmits, the hub repeats
the signal on the outgoing line to each station.
• Physically a star; logically a bus.
• Hubs can be cascaded in a hierarchical
configuration.
44
Hubs
… physical-layer (“dumb”) repeaters:
– bits coming in one link go out all other links
at same rate
– all nodes connected to hub can collide with
one another
– no frame buffering
– no CSMA/CD at hub: host NICs detect
collisions
twisted pair
hub
45
Interconnecting LANs
• Bridges (aka Ethernet switches) were introduced
to allow the interconnection of several local area
networks (LANs) without a router.
• By partitioning a large LAN into multiple smaller
networks, there are fewer collisions, and more
parallel communications.
• Provide a number of advantages
–
–
–
–
Reliability: Creates self-contained units
Performance: Less contention
Security: Not all data broadcast to all users
Geography: Allows long-distance links
46
Key Aspects of Bridge Function
• Makes no modification to content or format of frames
it receives; simply copies from one LAN and repeats
with exactly the same bit pattern as the other LAN.
• Should contain enough buffer space to meet peak
demands.
• Must contain addressing and routing intelligence.
• May connect more than two LANs.
47
Bridge Operation
48
Bridge Functions
• Read all frames from each network
• Accept frames from sender on one network that are
addressed to a receiver on the other network
• Retransmit frames from sender using MAC protocol
for receiver
• Must have some routing information stored in order
to know which frames to pass
49
Summary comparison
hubs
routers
switches
traffic
isolation
no
yes
yes
plug & play
yes
no
yes
optimal
routing
cut
through
no
yes
no
yes
no
yes
50
Two-Level Hub Topology
51
Summary
Topic 10 - Ethernet
• Describe the characteristics of Ethernet
networks
• Discuss the operation of CSMA/CD
• Discuss the operation of bridges, hubs,
and switches
• Describe the characteristics of fast
Ethernet standards.
52