* Your assessment is very important for improving the work of artificial intelligence, which forms the content of this project
Download Network Coding and Reliable Communications Group
Survey
Document related concepts
Transcript
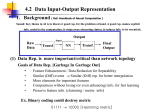
Network Coding and Reliable Communications Group A Multi-hop Multi-source Algebraic Watchdog Muriel Médard† Joint work with MinJi Kim†, João Barros‡ †Massachusetts Institute of Technology ‡University of Porto Network Coding and Reliable Communications Group Background • Secure network coding – Network error correction [Yeung et al. 2006] – Resilient coding in presence of Byzantine adversaries [Jaggi et al. 2007] – Confidential coding scheme [Vilela et al. 2008] – Signature scheme [Charles et al. 2006][Zhao et al. 2007] – Locating attackers [Siavoshani et al. 2008] – NOTE: downstream nodes check for adversaries, the upstream nodes unaware. • Watchdog and pathrater [Marti et al. 2000] – Extensions of Dynamic Source Routing – Detect/mitigate misbehavior of the next node – Use wireless medium: promiscuous monitoring • Algebraic Watchdog [Kim et al. 2009] – Combine the benefits of network coding and watchdog – Extend to multi-hop, multi-source setting Network Coding and Reliable Communications Group Problem Statement Is vm+1 consistent with… • Overheard packets from v2 , v3 ,… vm? • Channel statistics? • Wireless network G = (V, E1,E2). Overhearing with noise in E2 Intended transmission in E1 – V : Set of nodes in the network – E1: Set of hyperedges for connectivity/wireless links – E2: Set of hyperedges for interference • Transition probability known (Binary symmetric channel) Network Coding and Reliable Communications Group Problem Statement Overhearing with noise in E2 Intended transmission in E1 • How can upstream nodes (v1, v2, …,vm) detect misbehaving node (vm+1) with high probability? Routing: Packets individually recognizable Network Coding: Packets are mixed Errors from BSC channel : Probabilistic detection Few bit errors can make dramatic change in the algebraic interpretation Network Coding and Reliable Communications Group Packet Structure coded data xi = Σ αj xj with errorcorrecting code Ci = (n, ki, di) coding coefficients aj’s pi = aj’s h(xj) h(xi) hash of received messages h(xj) xi hash of message h(xi) header: protected with error correction codes • A node vi that receives messages xj ’s and transmits pi – Note: hash is contained in one hop, dependent on in-degree • Goal: If vi transmits xi = e + Σ αj xj where e≠0, detect it with high probability. – Even if |e| small, the algebraic interpretation may change dramatically. Network Coding and Reliable Communications Group Threat Model • Adversary – – – – Eavesdrops its neighbors’ transmissions Injects/corrupts packets Computationally unbounded Knows the channel statistics, but does not know the specific realization of the channel errors • Adversary’s objective: Corrupt information flow without being detected by other nodes • Our objective: limit errors introduced by the adversaries to be at most that of the channel Network Coding and Reliable Communications Group Algebraic Watchdog • Focus on v1 – Listens to neighbors and infer the messages: Using transition matrix T – Combines the inferred messages to “guess” what the next hop node should transmit: Watchdog trellis & Viterbi-like algorithm – Check the “guessed message” with next-hop node’s transmission: Inverse transition matrix T-1 Network Coding and Reliable Communications Group Transition Matrix/List T • Relates the overheard information from source vi to list of candidates (inferred list of xi) Overheard information Start state Overheard information Inferred information xi y Edge iff Edge weight probability of receiving message: proportional to given y is original Network Coding and Reliable Communications Group Watchdog Trellis • Uses overheard & inferred information (candidates) to generate a list of “guesses” on what vm+1 should send Combine information from v2 What v1 already has Layer 1 α1x1 Start state Combine infor- Combine information from vm-1 mation from vm Layer 2 Layer 3 Layer m-1 Layer m α1x1 +α2x2 α1x1 +α2x2 +α3x3 Σ1≤i≤m-1 αixi Σ1≤i≤m αixi “guesses” are states with positive weight at Layer m Network Coding and Reliable Communications Group Inverse Transition Matrix T-1 Overheard information • Using the “guesses” generated, checks that vm+1 is well-behaving • Same as T, just inverse Guesses Σ1≤i≤m αixi Overheard information [xm ̃ +1,h(xm+1)] Edge iff Inferred linear combinations (guesses) Σ1≤i≤m αixi y Edge weight End node probability of receiving original message: proportional to given y is Network Coding and Reliable Communications Group Decision Making Layer 1 α1x1 Layer 2 Layer 3 Layer m-1 Layer m α1x1 +α2x2 α1x1 +α2x2 +α3x3 Σ1≤i≤m-1 αixi Σ1≤i≤m αixi Overheard information [xm ̃ +1,h(xm+1)] End state Start state “Guesses” • Total weight of end state = p* = probability of overhearing given channel statistics • Can use various decision policy, such as threshold decision rule p*>t – Depending on the rule, different false positive/false negative probabilities Network Coding and Reliable Communications Group Simulation Results: Varying adversarial attack Adversarial relay (flips bit with probability padv) • • • • All channel noise: 10%, i.e. BSC(0.1) 3 sources 10-bit field size 2-bit hash size Honest relay (does not inject errors) When adversary injects more than channel noise (10%), the p*adv and p*relay have different distribution! Network Coding and Reliable Communications Group Conclusions • Probabilistically police downstream neighbors in a multi-hop, multi-source network using network coding – Only discussed multi-source, two-hop setting • Trellis-like graphical model: – Capture inference process – Compute/approximate probabilities of consistency within the network (Viterbi-like algorithm) • Preliminary simulation results agree with the intuition Future Work: – Combine with reputation based protocol and some practical considerations Network Coding and Reliable Communications Group EXTRA SLIDES Network Coding and Reliable Communications Group Multi-hop Algebraic Watchdog • As long as the min-cut to any node from the source is not dominated by adversarial node, can detect malicious behavior Network Coding and Reliable Communications Group Multi-hop Algebraic Watchdog S0 v1 S2 v4 S0 monitors v5 S1 monitors v7 S1 monitors v8 v2 v3 v5 v6 S2 monitors v4 v7 v8 S1 edges in E1 • As long as the min-cut to any node from the source is not dominated by adversarial node, can detect malicious behavior Network Coding and Reliable Communications Group Simulation Results: Varying hash size Hash size (in bits) Adversarial relay (flips bit with probability 10%) Honest relay (does not inject errors) Hash size > 1 bit sufficient • All channel noise & adversarial attack level: 10%, i.e. BSC(0.1) • 3 sources • 10-bit field size Network Coding and Reliable Communications Group Simulation Results: Varying channel noise Channel noise between sources • • • • Adversarial relay (flips bit with probability 10%) Honest relay (does not inject errors) When channel noise > Adversarial attack level: 10%, i.e. BSC(0.1) 10% (adversarial attack 3 sources level), then may not be 10-bit field size able to detect the 2-bit hash size adversary! Network Coding and Reliable Communications Group Simulation results: Varying number of sources Number of sources Adversarial relay (flips bit with probability 10%) • All channel noise & adversarial attack level: 10%, i.e. BSC(0.1) • 3 sources • 10-bit field size • 2-bit hash size Honest relay (does not inject errors) When only one source, v1 can detect (even by itself) v1 can detect adversary when there are moderate number of sources with high probability v1 can not detect by itself when many sources • Need more hash or better overhearing channel • Does not take into account other nodes vi’s independent watchdog