* Your assessment is very important for improving the work of artificial intelligence, which forms the content of this project
Download Datasheet - EnOcean Alliance
Multiprotocol Label Switching wikipedia , lookup
IEEE 802.1aq wikipedia , lookup
Network tap wikipedia , lookup
Computer network wikipedia , lookup
Parallel port wikipedia , lookup
Power over Ethernet wikipedia , lookup
Point-to-Point Protocol over Ethernet wikipedia , lookup
Asynchronous Transfer Mode wikipedia , lookup
Recursive InterNetwork Architecture (RINA) wikipedia , lookup
Serial port wikipedia , lookup
Airborne Networking wikipedia , lookup
Deep packet inspection wikipedia , lookup
Wake-on-LAN wikipedia , lookup
UniPro protocol stack wikipedia , lookup
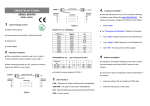
Seite 1 of 8 Product Brief EnOcean Web2.0-Based Sniffer „EWBS“ Steinbeis Transfer Centre Embedded Design and Networking, University of Cooperative Loerrach, Germany http://www.stzedn.de Prof.Dr.-Ing. Axel Sikora, Dipl.-Ing. Dipl. Wirt.-Ing. Doc. No. 10178002, 17.12.2008 Seite 2 of 8 1 Version History version date Changes source 1.0 17.12.2008 first release sa 2 Abstract This product brief describes a new sniffer platform for wireless networks. This platform combines the feature rich possibilities of Web2.0 functionality with the versatile capabilities of an embedded infrastructure. It is hosted on the emBetter webserver [1] and is targeted – in this first release – for the EnOcean Radio Protocol [2]. Table of Contents 1 2 3 3.1 3.1.1 3.1.2 3.1.3 3.2 4 5 Version History.........................................................................................................................................................2 Abstract ......................................................................................................................................................................2 System Architecture..................................................................................................................................................3 Elements ....................................................................................................................................................................3 TCM Module.............................................................................................................................................................3 emBetter.....................................................................................................................................................................3 Client ..........................................................................................................................................................................4 Functionality..............................................................................................................................................................4 Getting into Operation ............................................................................................................................................7 Sources .......................................................................................................................................................................8 Seite 3 of 8 3 3.1 System Architecture Elements 3.1.1 Overview Figure 1 shows the system components of the sniffer platform, which is connected to a TCM130-.module, talking and understanding EnOcean Radio Protocol (ERP). The sniffer platform communicates with the TCM130-module via the EnOcean Serial Protocol (ESP). It can then be accessed from a web client via HTTP with help of a LAN or WAN-based the deployment support network (DSN). Figure 1 Component diagram 3.1.2 TCM Module The TCM 130 module is a transceiver node. It is controlled by a PIC8F452 16-Bit microcontroller. This microcontroller contains of 32KB Flash, 1,5KB RAM and 0,25KB EEPROM. It holds firmware which was enhanced with a routing algorithm and modified for debugging purposes. Therefore it's able to forward the received telegrams via an UART interface. As default, the TCM works in promiscuous mode. Consequently it accepts all radio telegrams regardless of destination address. The only restriction is that it discards all telegrams with an invalid checksum. 3.1.3 emBetter The central element of the sniffer is the microcontroller board, which is equipped with a ColdFire MCF52235 controller. This controller consists of 256KB Flash, 32KB RAM, a 10/100Mbit/s Ethernet and 3 RS232 interfaces. It has a clock rate of 60MHz and a Real-Time-Clock with a resolution of 31.25 µs, which is high enough to generate a unique timestamp for every telegram in the ring buffer. The ring buffer is also implemented on this controller as a temporary storage for up to 256 telegrams. The web server software can gain access to these telegrams via an exposed API, which allows for retrieval of specific telegrams as well as initialization of the buffer and deletion of the content. Seite 4 of 8 3.1.4 Client The emBetter delivers a web application which is written completely in Javascript. This means it transfers all performance intensive computing onto the client platform while remaining completely platform independent. The application is built with respect to standard conformity and is therefore supported by most AJAX-capable Browsers including Internet Explorer 7, Firefox3, Safari3, Opera9, Google Chrome and Safari on iPhone. AJAX is utilized to get the telegrams from the sniffer in an efficient way since not all files have to be fetched from the server on refresh but only the telegram data.. This data is then interpreted and presented in a table structure, where it can easily be sorted, filtered or exported. Additionally all operations are executed on an in-browser data object which is refreshed periodically. Therefore all user input is followed by a direct output without any waiting time This architecture also has the big advantage, that the sniffer can be used from anywhere in the network and even remote locations. Since the used AJAX technology keeps the transferred traffic on a minimum (around 10KB for a complete ring buffer with 256 telegrams), the application can even be used on a UMTS or GPRS connected device. 3.2 Functionality The Web-Interface provides the basic functionality of a network sniffer. While capturing, the table is instantly updated with the newest telegrams being fetched from the ring buffer. Additionally the telegrams are coloured in the table corresponding to the type. The main interface features a control panel and a table showing all the captured packets. Figure 2 Main sniffer interface (simple mode) On the left side there is an indicator appearing while the sniffer is running. The buttons in the panel are to start and stop the sniffer, clear results and only show new packets, switch to csv mode, enter a filter criterion and switch to advanced mode. The advanced mode displays optional routing information which isn't present on every packet. The table headlines are also clickable for sorting the table after the respective criteria. Seite 5 of 8 Figure 3 Main sniffer interface (advanced mode) When a filter criterion is entered, which is of the format “columnheadline value”, only packets fulfilling the criteria are shown. Figure 4 Filtered sniffer output In the picture above, there are only packets shown, which correspond to the type “r_end”. Figure 5 Raw packet display When a packet in the table is marked, an info box in the header panel appears, which shows the raw packet including timestamp and header. For exporting the captured packets to disk, there is the “csv mode”. This stops the capturing and displays the packets in csv manner. From there the output can be copied and saved to a file. Seite 6 of 8 Figure 6 CSV output Finally there is also the possibility to only display packets which are new. The “Clear Results” button provides this functionality. Upon click the table is cleared and an URL parameter is set, so that only packets, which are newer than the momentary last one, are fetched. Figure 7 Clear results to fetch only new packets Seite 7 of 8 4 Getting into Operation The whole platform is bundled in a small (12,4x6,6x3,6cm) box, which features a power and Ethernet port for operation and a serial port for configuration and maintenance of the device itself. Figure 8 Ethernet and power socket on the sniffer box Figure 9 Serial port on the other side of the box After connecting the box via the serial interface, it is possible to configure it over telnet on the connected computer. The configuration parameters for the serial are as follows: 57600 baud, 8 data bits, 1 stop bit and no hardware flow control. The start-screen of the telnet application is pictured in Figure 10. With help of this console you are able to get the current IP address of the sniffer (command: ip). You can also set the ip-address manually or automatically via DHCP with the commands “ip set” and “ip auto”. Seite 8 of 8 Figure 10: Startscreen of the console Furthermore, it is possible to get information about the ethernet state with the command “eth”. This command displays information about the Coldfire Fast Ethernet Controller (FEC) for example a Frame transmit/receive statistic or the ARP table information for network interfaces. 5 References [1] http://www.stzedn.de/stzedn/files/embetter_flyer_en.pdf [2] http://www.enocean.com/en/radio-technology/