* Your assessment is very important for improving the work of artificial intelligence, which forms the content of this project
Download Expanded Notes: Network Monitoring Parts 1 and 2
Policies promoting wireless broadband in the United States wikipedia , lookup
Recursive InterNetwork Architecture (RINA) wikipedia , lookup
Computer network wikipedia , lookup
Zero-configuration networking wikipedia , lookup
Deep packet inspection wikipedia , lookup
Wake-on-LAN wikipedia , lookup
Distributed firewall wikipedia , lookup
Wireless security wikipedia , lookup
Airborne Networking wikipedia , lookup
Piggybacking (Internet access) wikipedia , lookup
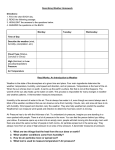
Network Monitoring Lesson overview. In this lesson, we will cover: ● ● ● ● ● The why of network monitoring. Logging tools for monitoring a network. Active network monitoring tools. Wireless monitoring tools. Environmental monitoring tools. The why of network monitoring. How do you know what is going on in your network? Is it healthy or is it about to crash? Network administrators hate to be surprised by failures in their networks—especially ones that could have been foreseen and, therefore, forestalled. How do they keep from being surprised? They enact a variety of procedures and implement a number of tools that help to monitor their networks and keep track of how they are behaving. Logging tools for monitoring a network. One of the main tools used by network administrators to monitor their networks is reviewing log files. All operating systems offer a means of viewing events that occur to that specific machine. This also includes networking equipment. A number of applications have been developed to monitor systems and networks that, among other actions, also generate log files. Log files can be used to help pinpoint when a problem occurred and help narrow down the possible causes of that problem. Log files can also be used to help create a baseline of network behavior, so that administrators know what to expect from a network. Log files can usually be classified as being system logs, general logs, or history logs. As a general rule, log files are an after-the-fact means of monitoring a network and they are not very helpful for real time analysis. This is partially due to the sheer volume of information that log files can generate; it is just too difficult to keep track of that much information in real time. Highlights: ● ● ● All operating systems offer a means of viewing events that occur to that specific machine. Some applications have been developed to monitor systems and networks that also generate log files (among other actions). Log files can be used to help pinpoint when a problem occurred and help narrow down the cause of an issue. ● ● Log files can also be used to help create a baseline of network behavior. Log files are an after-the-fact means of monitoring a network. Event viewer. There are a number of logging tools that can be used. Event Viewer is not a log file in itself; it comes with Windows server and most other Windows operating systems and this tool can be used to review Windows log files. The most important log files that can be viewed from Event Viewer are application, security, and system logs. Application logs. Application logs contain events that are triggered by the actions of an application. For example, when Live Update or another application performs an action, that action will be entered into the application log. Security logs. Security logs contain events that are triggered by actions that the operating considers to be security issues. For example, some logs are created for successful and unsuccessful logon attempts. System logs. System logs contain events triggered by Windows system components. For example, it will create an entry for when a driver starts or fails to start. In either situation, a log entry will be created. Highlights: ● ● ● ● Event Viewer can be used to view application, security, and system logs. Application logs contain events triggered by the actions of applications. Security logs contain events triggered by security events. System logs contain events triggered by Windows system components. Syslog. Syslog is a non-Microsoft log that was developed in the 1980s. It provides devices that normally wouldn't be able to communicate with the means of delivering performance and problem information to system administrators. This permits there to be separation between the software that generates the message, the storage of that message, and the software that analyzes the generated message. This separation of function allows Syslog to be highly configurable and has also allowed it to continue to be a vital tool for monitoring networks even today. As a matter of fact, the Internet Engineering Task Force (IETF) likes Syslog so much that it standardized it in 2009. Syslog can generate log messages based on the types of services that are running and includes a severity level that ranges from zero, the most severe, up through seven, the least severe. Syslog can generate a lot of log messages. Most network administrators configure it so that they only get alerted when a minimum severity level has been reached. As a matter of fact, administrators almost never want to capture debug log events, unless they are actively debugging an application or a service. Because it generates so much information, Syslog can be configured so that network administrators receive their alerts via text message or SMS message, or by email, or they may even receive a voicemail message. Highlights: ● ● ● ● Syslog provides devices that normally would not be able to communicate with a means of delivering performance and problem information to system administrators. It permits there to be separation between the software that generates the message, the storage of the message, and the software that analyzes the generated message. It generates log messages based on the types of service and includes a severity level from zero (most severe) to seven (least severe). Most network administrators configure Syslog so that they only get alerted when a minimum severity level has been reached. SNMP. SNMP (Simple Network Management Protocol) is an application layer (OSI model Layer 7) protocol used to monitor and manage a network’s health. Network or system administrators configure monitors (often called traps) on devices that view the operation of specific aspects of the device. SNMP is useful for viewing real time performance and operations of critical areas of a network. For example, SNMP can be set to monitor the status of a router's interface (it can determine if the interface is in an up or down state). The monitors periodically communicate with a network management station (NMS) through Get messages that the NMS sends out. The response from the monitors is stored in a management information base (MIB), which is a type of log file. The administrator can custom-configure the monitors with Set messages sent from the NMS. When an event occurs—such as the router’s interface going down—the trap is tripped and the event is logged. SNMP, just like Syslog, can be configured to just log the event or it can be configured to contact the network administrator. SNMP gives network and system administrators the ability to provide more real time monitoring of a network’s performance and health. Highlights: ● ● ● ● ● ● SNMP is an application layer protocol used to monitor and manage a network’s health. Network or system administrators configure monitors on devices that view a specific aspect of its operation (e.g., is the interface up or down?). The monitors periodically communicate with a network management station (NMS) through Get messages that the NMS sends out. The response from the monitors is stored in a management information base (MIB), which is a type of log file. The administrator can configure the monitors with Set messages sent from the NMS. SNMP can be configured to just log the event or it can be configured to contact a network administrator (via email or SMS). SIEM. SIEM (security information and event management) is a term for software products and services that combine SIM (security information management) and SEM (security event management). SIEM may be provided by a software package, a network appliance, or as a third party cloud service. SIEM is used as a means of monitoring and providing real time analysis of security alerts—an example of the SEM function. It can also be used as a tool to analyze long term data and log files—an example of the SIM function. SIEM is highly configurable to meet the needs of an individual network. ● ● ● ● SIEM is a term for software products and services that combine SIM and SEM. It is used as a means of monitoring and providing real-time analysis of security alerts. It can be used to as a tool to analyze long-term data and log files. It is highly configurable to the needs of an individual network. Active network monitoring tools. Port scanners. Port scanners are used to scan a network for open ports and protocols. The information gathered is then used to harden the network. Port scanners are a great method of finding vulnerabilities in the network infrastructure and plugging them before a security breach can occur. A word of caution: only use a port scanner on a network or system that you are authorized to scan. Port scanning is a possible sign of someone trying to breach a system and can lead to problems if you are not authorized to scan that system. Highlights: ● ● Port scanners are used to scan a network for open ports and protocols identifying possible vulnerabilities in the network. Port scanning is a possible sign of an attempt to breach a system. Authorization is required before using port scanning to avoid possible repercussions. Packet sniffers/protocol analyzer tools. Slightly different than port scanners, are applications that use interface monitoring or packet flow monitoring. These applications are usually deployed as an active software tool to monitor and analyze network traffic within a network segment. They are commonly called packet sniffers or protocol analyzers. Such applications provide an in depth look at what traffic is on a network and may reveal security issues that a network administrator can then mitigate. They help to identify top talkers on a network segment. Top talkers are those nodes or applications that generate the most amount of traffic. Packet sniffers can also help to identify top listeners on a network segment. A top listener is that interface or those interfaces that are receiving the most network traffic or—put in another way— those interfaces that are utilizing the most bandwidth for receiving packets. This information can help administrators determine if load balancing is needed and where to place the balancing if it is. Microsoft Message Analyzer and Wireshark are examples of free packet sniffing tools. Highlights: ● ● ● Packet sniffers/protocol analyzers are active software tools that monitor and analyze network traffic within a network segment. Packet sniffers and protocol analyzers provide an in depth look at what traffic is on the network and may reveal security issues. Microsoft Message Analyzer and Wireshark are both free packet sniffing tools. Wireless monitoring tools. Wireless monitoring tools should be used to determine the overall health of a wireless network environment. Some of the common tools used for this purpose are outlined below. Wi-Fi analyzer. A Wi-Fi analyzer is a tool that is similar to a protocol analyzer, but for wireless networks. It sniffs out packets on wireless networks and provides statistics on the packets that it sees. Just like a packet sniffer, a Wi-Fi analyzer can check for bandwidth usage, channel usage, top talkers, top listeners, etc. Wi-Fi analyzers can identify networks by passively scanning the radio frequencies (RFs) to determine where traffic is coming from. Given enough time, a Wi-Fi analyzer can also identify hidden networks or those that administrators don't know about. They can also infer nonbeaconing networks based on data traffic over the RFs. They may not be able to discover the SSID of the network, but they can alert the network administrator that an unknown wireless network is present. Highlights: ● ● ● ● A WI-Fi analyzer is a similar tool to the protocol analyzer, but for wireless networks. Can check for bandwidth usage, channel usage, top talkers, etc. Can identify networks by passively scanning the RFs. Can identify hidden networks if given enough time and can infer non-beaconing networks based on data traffic. Wireless survey tools. Wireless survey tools are most commonly used as a design tool for setting up high quality wireless networks. When used in conjunction with mapping tools, these survey tools can help to establish the required number of access points (APs) to get the necessary amount of coverage, the ideal antenna placement, and the optimum amount of channel overlap. Wireless survey tools can also help to identify possible sources of radio frequency interference (RFI). These tools are often used to prevent wireless network performance and security issues before they ever have a chance to occur. Highlights: ● ● ● Wireless survey tools are most commonly used as design tools for setting up high quality wireless networks. The survey tools, when used in conjunction with mapping tools, can help to establish the required amount of APs, ideal antenna placement, and optimum channel overlap. Used to prevent wireless network performance and security issues before they even occur. Environmental monitoring tools. A network’s health can be affected by more than just a network interface failing or a possible security breach. Network and system administrators also need to be concerned about environmental factors. Some of those factors include electrical power, heat, and humidity. Power monitoring. Power monitoring tools are systems and tools that can be used to evaluate the amount of and the quality of the electrical power being delivered to a system. These tools are often deployed with or alongside an uninterruptible power supply (UPS). The monitor will issue an alert when an issue with electrical power has been identified, giving the network or system administrator a chance to rectify the problem before any equipment is damaged. Highlights: ● ● ● Power monitoring systems and tools can be used to evaluate the amount of and quality of the electrical power being delivered to a system. Power monitoring is often deployed with, or alongside, a UPS. They issue an alert when an issue with electrical power is identified. Environmental monitoring. Heat monitors. All electrical components are designed to operate within a specific heat range. Not only are they designed to operate within that heat range, but all electrical equipment will also generate some heat while in operation. The harder that equipment works, the more heat it will generate. This is where heat monitors come into play. Heat monitors allow an administrator to control the temperature levels before they become an issue. Highlights: ● ● All electrical components are designed to operate within a specified heat range and also generate heat when in use. Monitors allow administrators to control temperature levels. Humidity monitors. Humidity is another item that network administrators need to keep in mind. Too little humidity increases the risk of electrostatic discharge (ESD) and too much humidity increases the risk of condensation on equipment (and electrical components do not like condensation). Humidity monitors allow administrators to control humidity levels through the proper means before it becomes an issue. Highlights: ● ● Too little humidity increases the risk of ESD and too much humidity increases the risk of condensation. Humidity monitors allow administrators to control humidity levels. What was covered. The why of network monitoring. As network administrators are responsible for keeping the network up and running, they hate to be surprised by network failures—especially ones they could have foreseen and forestalled. To prevent this, they will deploy a variety of tools to keep track of a network’s health and behavior. Logging tools for monitoring a network. Log files are one means by which network administrators can track how their network and systems are running. Almost all operating systems are capable of generating log files, which are usually a more passive and after-the-fact type of monitoring. Event Viewer is a Microsoft tool used to track and organize log files. Syslog was created in the 1980s to provide a method of communication between devices that would not normally communicate. Syslog events are rated on a scale of zero to seven, based on their severity (with zero being the most severe). SNMP is a protocol that takes a more active approach in monitoring the network and systems. With SNMP, a trap is set on a device. When the trap is tripped, a message is sent to the NMS, which stores the event in the MIB. Depending on the severity, a message may be sent to an administrator via SMS or email. Active network monitoring tools. Port scanners are used to scan for unsecured ports and protocols. The information gathered by port scanners is used to harden networks and make them less vulnerable to security breaches. Packet sniffers/protocol analyzers evaluate network traffic at the packet level. Packet sniffers can help to identify issues on the network that can then be mitigated. Wireless monitoring tools. A Wi-Fi analyzer is similar to a packet sniffer, but checks wireless network packets instead. Analyzers can also identify which RF channels are in use. The analyzer can help to identify wireless networks, even ones that are hidden. Wireless survey tools are used to help design efficient and secure wireless networks. Environmental monitoring tools. A network’s function and health can be affected by environmental factors. Power monitors are used to evaluate the electrical supply being delivered to the system. Heat and humidity monitors are used to help maintain the correct levels of heat and humidity.