Public Keys and Private Keys Quantum Cryptography
... Quantum cryptography and classical cryptography essentially deal with the same tasks, such as, just to mention a few, private communication, message authentication, zero knowledge proofs etc. The big difference is that the communication is done using qubits instead of classical bits. Due to the basi ...
... Quantum cryptography and classical cryptography essentially deal with the same tasks, such as, just to mention a few, private communication, message authentication, zero knowledge proofs etc. The big difference is that the communication is done using qubits instead of classical bits. Due to the basi ...
1 Path Integrals and Their Application to Dissipative Quantum Systems
... these two effects occur both for classical as well as quantum systems, there exists a third phenomenon which is specific to the quantum world. As a consequence of the entanglement between system and environmental degrees of freedom a coherent superposition of quantum states may be destroyed in a proce ...
... these two effects occur both for classical as well as quantum systems, there exists a third phenomenon which is specific to the quantum world. As a consequence of the entanglement between system and environmental degrees of freedom a coherent superposition of quantum states may be destroyed in a proce ...
43-4.pdf
... 65th birthday of Grzegorz Rozenberg. The editors describe their reasons for choosing the title Algorithmic Bioprocesses: “the workshop did not cover the whole spectrum of natural computing research, but rather it was mostly focused on the interactions between computer science on the one hand and bio ...
... 65th birthday of Grzegorz Rozenberg. The editors describe their reasons for choosing the title Algorithmic Bioprocesses: “the workshop did not cover the whole spectrum of natural computing research, but rather it was mostly focused on the interactions between computer science on the one hand and bio ...
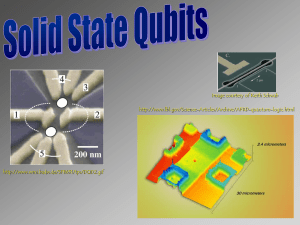
superconducting qubits solid state qubits
... “Charge qubits” and “spin qubits” The qubits levels can be formed by either the energy levels of an electron in a potential well (such as a quantum dot or an impurity ion) or by the spin states of the electron (or the nucleus). The former are examples of charge qubits. The charge qubits have high e ...
... “Charge qubits” and “spin qubits” The qubits levels can be formed by either the energy levels of an electron in a potential well (such as a quantum dot or an impurity ion) or by the spin states of the electron (or the nucleus). The former are examples of charge qubits. The charge qubits have high e ...
What the Humean Should Say About Entanglement
... As before, systems can use vocabulary that refers to perfectly natural properties (the properties that make up the mosaic) – what we’ve called the “base language”. But in addition to this they can introduce and use any other vocabulary so long as it comes in uninterpreted.5 How does such uninterpret ...
... As before, systems can use vocabulary that refers to perfectly natural properties (the properties that make up the mosaic) – what we’ve called the “base language”. But in addition to this they can introduce and use any other vocabulary so long as it comes in uninterpreted.5 How does such uninterpret ...
Overture - Center for Nonlinear Science
... elucidating problems of fully developed turbulence, quantum field theory of strong interactions and early cosmology have been modest at best. Even that is a caveat with qualifications. There are applications–such as spatially extended (non-equilibrium) systems, plumber’s turbulent pipes, etc.,–where t ...
... elucidating problems of fully developed turbulence, quantum field theory of strong interactions and early cosmology have been modest at best. Even that is a caveat with qualifications. There are applications–such as spatially extended (non-equilibrium) systems, plumber’s turbulent pipes, etc.,–where t ...
Carbon nanotube quantum dots on hexagonal boron nitride
... Suspended devices, however, su↵er from limitations in resolution, the contrast in scanning electron microscopy the scalability, geometry and in the choice of the conThe next step, however, namely the use hBN as substrate for independent, more complex (SEM) images can beof poor (see below) and AFM im ...
... Suspended devices, however, su↵er from limitations in resolution, the contrast in scanning electron microscopy the scalability, geometry and in the choice of the conThe next step, however, namely the use hBN as substrate for independent, more complex (SEM) images can beof poor (see below) and AFM im ...
A Selective History of the Stone-von Neumann Theorem
... The first observation to make is that (1) has no solutions if H is finite-dimensional and ~ 6= 0, since the trace of any commutator must vanish, but Tr(−i~) = −i~ dim H does not. But (1) also has no solutions with either P or Q bounded. 8 (P and Q play symmetrical roles, since interchanging them amo ...
... The first observation to make is that (1) has no solutions if H is finite-dimensional and ~ 6= 0, since the trace of any commutator must vanish, but Tr(−i~) = −i~ dim H does not. But (1) also has no solutions with either P or Q bounded. 8 (P and Q play symmetrical roles, since interchanging them amo ...
Squeezed light
... [2]. EPR argued that by choosing to perform either a position or momentum measurement on her portion of the TMSV, Alice remotely prepares either a state with a certain position or one with a certain momentum at Bob’s location. But according to the uncertainty principle, certainty of position implies ...
... [2]. EPR argued that by choosing to perform either a position or momentum measurement on her portion of the TMSV, Alice remotely prepares either a state with a certain position or one with a certain momentum at Bob’s location. But according to the uncertainty principle, certainty of position implies ...
Statics - Chabotcollege.edu
... If you received a Course ID from your instructor, click Yes, enter your Course ID and click Continue. ...
... If you received a Course ID from your instructor, click Yes, enter your Course ID and click Continue. ...
The Two-Stage Model of Free Will: How biological freedom in lower
... thinking with William James’s 1884 two-stage model of free will,4 first chance generation of alternative possibilities, followed by a willed decision. Long before twentieth-century behaviorism and logical empiricism had limited the study of the mind to externally observable phenomena, James had argu ...
... thinking with William James’s 1884 two-stage model of free will,4 first chance generation of alternative possibilities, followed by a willed decision. Long before twentieth-century behaviorism and logical empiricism had limited the study of the mind to externally observable phenomena, James had argu ...
PHYS - University of New Brunswick
... subsequently applied in other courses. In all future experimental work, we will treat experimental limitations properly and fully. In all future courses involving reports, written work will meet or exceed the standards established in the Research Skills course. The title of this course emphasises th ...
... subsequently applied in other courses. In all future experimental work, we will treat experimental limitations properly and fully. In all future courses involving reports, written work will meet or exceed the standards established in the Research Skills course. The title of this course emphasises th ...
Single component and binary mixtures of BECs in double
... •For small N (here 10), clear deviations are quickly seen (less than a Rabi time here) between the mean-field/semiclassics results and the full quantum behavior •Correspondingly, the cloud is far from condensed as time evolves ...
... •For small N (here 10), clear deviations are quickly seen (less than a Rabi time here) between the mean-field/semiclassics results and the full quantum behavior •Correspondingly, the cloud is far from condensed as time evolves ...
Classical Simulation of Quantum Systems
... space and not just in its classical states [Fey85], would be a tool of tremendous value. While the realization of a quantum computer is still very far away, considerable progress has been made since the first mentioning of this idea by Feynman: First, Deutsch [Deu85] noticed a quantum computer may v ...
... space and not just in its classical states [Fey85], would be a tool of tremendous value. While the realization of a quantum computer is still very far away, considerable progress has been made since the first mentioning of this idea by Feynman: First, Deutsch [Deu85] noticed a quantum computer may v ...
Quantum computation and quantum information (PDF
... measurements we make. Taken to its limit, the Copenhagen interpretation denies the reality of an individual photon or electron until it has been observed. Let us see how different interpretations of quantum mechanics can explain the result of the double-slit experiment. It was first conducted by Tho ...
... measurements we make. Taken to its limit, the Copenhagen interpretation denies the reality of an individual photon or electron until it has been observed. Let us see how different interpretations of quantum mechanics can explain the result of the double-slit experiment. It was first conducted by Tho ...
Non-exponential and oscillatory decays in quantum mechanics
... The amplitudes Ac1 ≡ hc, E|H|1i are the matrix elements of the original Hamiltonian between an intrinsic state |1i and the channel state |c, Ei. The channel state is labeled here by the asymptotic energy E and all additional quantum numbers are combined in label c. For convenience, in this formalism ...
... The amplitudes Ac1 ≡ hc, E|H|1i are the matrix elements of the original Hamiltonian between an intrinsic state |1i and the channel state |c, Ei. The channel state is labeled here by the asymptotic energy E and all additional quantum numbers are combined in label c. For convenience, in this formalism ...