School of Computing CS 5530: Database Systems Spring 2017
... logical language in the relational data model and its relationship to the practical relational query language: SQL. Examine in depth how to design and implement a database application. Understand how various programs are able to connect to the database through ODBC. Briefly cover indexing and hashin ...
... logical language in the relational data model and its relationship to the practical relational query language: SQL. Examine in depth how to design and implement a database application. Understand how various programs are able to connect to the database through ODBC. Briefly cover indexing and hashin ...
Business analytics as an undergraduate introductory course
... BUSINESS ANALYTICS Business analytics is the practice of iterative, methodical exploration of an organization's data with emphasis on statistical analysis. Business analytics is used by companies committed to data-driven decision making. ...
... BUSINESS ANALYTICS Business analytics is the practice of iterative, methodical exploration of an organization's data with emphasis on statistical analysis. Business analytics is used by companies committed to data-driven decision making. ...
XML and database technology
... An instance of XML is a language An instance of an XML language is a document Documents are hierarchical & list-oriented XML documents can be parsed in a single, linear pass There is do notion of a fixed schema Does not leverage meta data for set-oriented queries Order matters in a set of documents ...
... An instance of XML is a language An instance of an XML language is a document Documents are hierarchical & list-oriented XML documents can be parsed in a single, linear pass There is do notion of a fixed schema Does not leverage meta data for set-oriented queries Order matters in a set of documents ...
A Robust System Architecture For Mining Semi
... Algorithm used for rule generation • Get Document ids of documents containing structured data value - using SQL statements. ( set ‘A’ ). • Get Document ids of documents containing unstructured concept - using ECH. ( set ‘B’ ). • C = A B. • Get document ids of concept Cr where Cr is related to C1 ...
... Algorithm used for rule generation • Get Document ids of documents containing structured data value - using SQL statements. ( set ‘A’ ). • Get Document ids of documents containing unstructured concept - using ECH. ( set ‘B’ ). • C = A B. • Get document ids of concept Cr where Cr is related to C1 ...
Database Management issues from Hoffer - Moodle
... Chapter 11 © 2013 Pearson Education, Inc. Publishing as Prentice Hall ...
... Chapter 11 © 2013 Pearson Education, Inc. Publishing as Prentice Hall ...
Developing a Database
... • Need space to store web content • The web server need not be local – Locally-created WWW pages can be uploaded to a remote server • e.g., field station can use server at main university campus and use a modem or even floppy disks to ...
... • Need space to store web content • The web server need not be local – Locally-created WWW pages can be uploaded to a remote server • e.g., field station can use server at main university campus and use a modem or even floppy disks to ...
The Relational Model
... Formal Relational Query Languages Two mathematical Query Languages form the basis for “real” languages (e.g. SQL), and for implementation: Relational Algebra: More operational, very useful for representing execution plans. Relational Calculus: Lets users describe what they want, rather than how ...
... Formal Relational Query Languages Two mathematical Query Languages form the basis for “real” languages (e.g. SQL), and for implementation: Relational Algebra: More operational, very useful for representing execution plans. Relational Calculus: Lets users describe what they want, rather than how ...
relational database management
... RELATIONAL DATABASE MANAGEMENT Paper: BCC606 Max. Marks: 35T + 15P PPW: 5 (3T & 2P) Exam Duration: 3 Hrs. Objectives: to acquire the basic conceptual background necessary to design and develop simple database system, Relational database mode, ER model and distributed databases, and to write good que ...
... RELATIONAL DATABASE MANAGEMENT Paper: BCC606 Max. Marks: 35T + 15P PPW: 5 (3T & 2P) Exam Duration: 3 Hrs. Objectives: to acquire the basic conceptual background necessary to design and develop simple database system, Relational database mode, ER model and distributed databases, and to write good que ...
Trusteddb:A Trusted Hardware Based Database With Privacy And
... Trusted hardware is generally impractical due to its performance limitations and higher acquisition costs. As a result, with very few exceptions, these efforts have stopped short of proposing or building full - fledged database processing engines. Computation inside secure processors is orders of ma ...
... Trusted hardware is generally impractical due to its performance limitations and higher acquisition costs. As a result, with very few exceptions, these efforts have stopped short of proposing or building full - fledged database processing engines. Computation inside secure processors is orders of ma ...
TrustedDB A Trusted Hardware based Database with Privacy and
... outsourcing. Once encrypted however, inherent limitations in the types of primitive operations that can be performed on encrypted data lead to fundamental expressiveness and practicality constraints. Recent theoretical cryptography results provide hope by proving the existence of universal homeomorp ...
... outsourcing. Once encrypted however, inherent limitations in the types of primitive operations that can be performed on encrypted data lead to fundamental expressiveness and practicality constraints. Recent theoretical cryptography results provide hope by proving the existence of universal homeomorp ...
Optimized data interpretation through reliable database integration
... click away; from local database to international database OR to make use of ‘viewing’ instead of copying data. Could that be realized? What about national and international security measures? 12.Informed consent: the submitter’s reliability? 13. Data on control individuals: gender and age are import ...
... click away; from local database to international database OR to make use of ‘viewing’ instead of copying data. Could that be realized? What about national and international security measures? 12.Informed consent: the submitter’s reliability? 13. Data on control individuals: gender and age are import ...
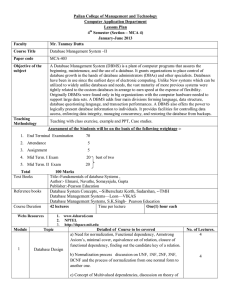
Database System Concepts, --Silberschatz Korth, Sudarshan, -
... beginning, maintenance, and the use of a database. It grants organizations to place control of database growth in the hands of database administrators (DBAs) and other specialists. Databases have been in use since the earliest days of electronic computing. Unlike New systems which can be utilized to ...
... beginning, maintenance, and the use of a database. It grants organizations to place control of database growth in the hands of database administrators (DBAs) and other specialists. Databases have been in use since the earliest days of electronic computing. Unlike New systems which can be utilized to ...
Conceptual and Logical Database Design
... • Conceptual database design – Constructing an information model, independent from all physical consideration for an enterprise ...
... • Conceptual database design – Constructing an information model, independent from all physical consideration for an enterprise ...
database systems: dis 308
... Databases are part of our day to day lives. When we are registering as students, we are interacting with databases, when we go to the bank, pay our electricity bills or pay water bills our accounts are on a database, even when we are browsing the net; information is coming from several databases. Th ...
... Databases are part of our day to day lives. When we are registering as students, we are interacting with databases, when we go to the bank, pay our electricity bills or pay water bills our accounts are on a database, even when we are browsing the net; information is coming from several databases. Th ...
Database - WVU CS101
... Field – is a basic entry or a data element, such as the name or a book or the telephone number. A field that uniquely identifies a record is called a Primary Key. Record – is a complete set of all of the data (fields) pertaining to one person, place, etc Table – is a collection of records, every tab ...
... Field – is a basic entry or a data element, such as the name or a book or the telephone number. A field that uniquely identifies a record is called a Primary Key. Record – is a complete set of all of the data (fields) pertaining to one person, place, etc Table – is a collection of records, every tab ...
scopedatabase
... – A defined file syntax which is used to express the metric data output by tools in a text file – Easily readable and the language is flexible to allow new metrics to be added or old metrics to be removed ...
... – A defined file syntax which is used to express the metric data output by tools in a text file – Easily readable and the language is flexible to allow new metrics to be added or old metrics to be removed ...
Dennis G. Allard mobile: 310.399.4740
... assay iodination counts. The system has been in operation since release in 1998, recording over one million assay iodination counts. USC/Information Sciences Institute o Lead Database architect for a web search engine prototype. Novel feature was ability to search a lattice of Yahoo-like hierarchies ...
... assay iodination counts. The system has been in operation since release in 1998, recording over one million assay iodination counts. USC/Information Sciences Institute o Lead Database architect for a web search engine prototype. Novel feature was ability to search a lattice of Yahoo-like hierarchies ...