CC2
... Before locking an item, Xact must set “intention locks” on all its ancestors. For unlock, go from specific to general (i.e., bottom-up). SIX mode: Like S & IX at the same time. Scanning the table but ...
... Before locking an item, Xact must set “intention locks” on all its ancestors. For unlock, go from specific to general (i.e., bottom-up). SIX mode: Like S & IX at the same time. Scanning the table but ...
Introduction to Object Oriented Databases
... whenever a process tries to access unallocated memory. The database runtime support library intercepts the signal, looks to see if the address in question was a database address, and, if so, loads the object into memory and makes the address be legal by changing permission on the corresponding page. ...
... whenever a process tries to access unallocated memory. The database runtime support library intercepts the signal, looks to see if the address in question was a database address, and, if so, loads the object into memory and makes the address be legal by changing permission on the corresponding page. ...
Chapter 12
... Classes are complex user-defined data types that combine traditional concept of data with processes (methods) to manipulate data ...
... Classes are complex user-defined data types that combine traditional concept of data with processes (methods) to manipulate data ...
Management of Data with Uncertainties
... RFID Data Management is an emerging class of applications whose goal is to manage readings of RFID tags. The RFID Ecosystem deployed at the University of Washington is based on a building-wide RFID infrastructure with 80 RFID readers, 300 antennas, tens of tagged people, and thousands of tagged obje ...
... RFID Data Management is an emerging class of applications whose goal is to manage readings of RFID tags. The RFID Ecosystem deployed at the University of Washington is based on a building-wide RFID infrastructure with 80 RFID readers, 300 antennas, tens of tagged people, and thousands of tagged obje ...
ADVANCED SQL AND PL/SQL TOPICS
... • Multiple instances can run concurrently on the same computer, each accessing its own physical database • Security for database startup and shutdown is controlled through connections to Oracle with administrator privileges. Normal users do not have control over the current status of an Oracle datab ...
... • Multiple instances can run concurrently on the same computer, each accessing its own physical database • Security for database startup and shutdown is controlled through connections to Oracle with administrator privileges. Normal users do not have control over the current status of an Oracle datab ...
V. Inference Control Schemes in Multilevel
... Abstract—When users have different security clearances to access data that is highly secure, single-level relational database is not sufficient. U.S Department of Defense (DoD) addresses some of the drawbacks of using single-level database in such an environment. Keeping that in sight DoD funded num ...
... Abstract—When users have different security clearances to access data that is highly secure, single-level relational database is not sufficient. U.S Department of Defense (DoD) addresses some of the drawbacks of using single-level database in such an environment. Keeping that in sight DoD funded num ...
basic-oracle-database
... • Specifies amount of disk space that user’s database objects can occupy in default tablespace • Must be assigned • Quota Size value: – None, default – Unlimited Guide to Oracle 10g – Value Advanced Databases ...
... • Specifies amount of disk space that user’s database objects can occupy in default tablespace • Must be assigned • Quota Size value: – None, default – Unlimited Guide to Oracle 10g – Value Advanced Databases ...
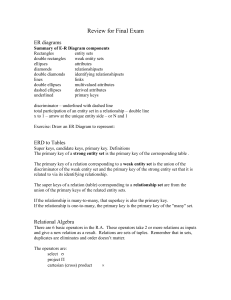
Review for Final Exam
... --depends on group by [order by] ;
includes aggregates: avg, min, max, sum, count
can have derived relation --subquery assigned name with as
select <> from <> where<> as r1
where
... --depends on group by [order by