computer science - SCSA - School Curriculum and Standards
... Database management systems There is no prescribed database management system for the Computer Science ATAR course. However, to meet the assessment requirements for this syllabus, it is required that students use a database management system that enables the: ...
... Database management systems There is no prescribed database management system for the Computer Science ATAR course. However, to meet the assessment requirements for this syllabus, it is required that students use a database management system that enables the: ...
Chapter 7
... Information is available via a company’s intranet and the Internet. HTML (hypertext markup language), the language used to construct most Web pages, wasn’t designed to build database queries. XML (extensible markup language), a newer, more powerful data description language, is designed with i ...
... Information is available via a company’s intranet and the Internet. HTML (hypertext markup language), the language used to construct most Web pages, wasn’t designed to build database queries. XML (extensible markup language), a newer, more powerful data description language, is designed with i ...
branch-name
... Vertically partition relations to isolate the data that is accessed most often -- only fetch needed information. • E.g., split account into two, (account-number, branch-name) and (account-number, balance). • Branch-name need not be fetched unless required Improve performance by storing a denorma ...
... Vertically partition relations to isolate the data that is accessed most often -- only fetch needed information. • E.g., split account into two, (account-number, branch-name) and (account-number, balance). • Branch-name need not be fetched unless required Improve performance by storing a denorma ...
IC52C4: Introduction
... User interface handler interprets user commands and formats the result data as it is sent to the user. Semantic data controller checks the integrity constraints and authorization requirements. Global query optimizer and decomposer determines execution strategy, translates global queries to local ...
... User interface handler interprets user commands and formats the result data as it is sent to the user. Semantic data controller checks the integrity constraints and authorization requirements. Global query optimizer and decomposer determines execution strategy, translates global queries to local ...
An integrated intranet and dynamic database Postgraduate School
... These databases, while minimally acceptable in the past to simply track personnel and classified material, are obsolete and no longer fully support the staff’s expanding information needs. ...
... These databases, while minimally acceptable in the past to simply track personnel and classified material, are obsolete and no longer fully support the staff’s expanding information needs. ...
An Overview of Business Intelligence Technology
... for enabling novel and rich BI applications for knowledge workers on mobile devices. In this short article, we are not able to provide comprehensive coverage of all technologies used in BI (see Chaudhuri et al.5 for additional details on some of these technologies). We therefore chose to focus on te ...
... for enabling novel and rich BI applications for knowledge workers on mobile devices. In this short article, we are not able to provide comprehensive coverage of all technologies used in BI (see Chaudhuri et al.5 for additional details on some of these technologies). We therefore chose to focus on te ...
Transactions
... Deadlock Deadlock: two transactions are each waiting on a resource that the other transaction holds Preventing deadlock Allow users to issue all lock requests at one time Require all application programs to lock resources in the same order ...
... Deadlock Deadlock: two transactions are each waiting on a resource that the other transaction holds Preventing deadlock Allow users to issue all lock requests at one time Require all application programs to lock resources in the same order ...
An Overview of Business Intelligence Technology
... for enabling novel and rich BI applications for knowledge workers on mobile devices. In this short article, we are not able to provide comprehensive coverage of all technologies used in BI (see Chaudhuri et al.5 for additional details on some of these technologies). We therefore chose to focus on te ...
... for enabling novel and rich BI applications for knowledge workers on mobile devices. In this short article, we are not able to provide comprehensive coverage of all technologies used in BI (see Chaudhuri et al.5 for additional details on some of these technologies). We therefore chose to focus on te ...
Normalizing Database Files
... database to see the new table May need to right-click Tables>Refresh for the database used to see table that was just created ...
... database to see the new table May need to right-click Tables>Refresh for the database used to see table that was just created ...
Oracle Database as a Service (DBaaS)
... Our advanced monitoring platform combines the best of breed commercial tools with internally developed technology. Having managing customer databases for over 17 years our highly tuned platform contains all our experience, base-lining the optimal threshold alerts and performance criteria. The highly ...
... Our advanced monitoring platform combines the best of breed commercial tools with internally developed technology. Having managing customer databases for over 17 years our highly tuned platform contains all our experience, base-lining the optimal threshold alerts and performance criteria. The highly ...
Query-based Data Warehousing Tool
... system. To keep updating these guidelines is a very hard task, especially with different versions of guidelines. To update the mapping of an attribute in the system, one should include an update for the paper document guideline as well. Thus, it is extremely difficult to maintain such tasks especial ...
... system. To keep updating these guidelines is a very hard task, especially with different versions of guidelines. To update the mapping of an attribute in the system, one should include an update for the paper document guideline as well. Thus, it is extremely difficult to maintain such tasks especial ...
Database System Architectures
... Architecture provides a degree of fault-tolerance — if a processor fails, the other processors can take over its tasks since the database is resident on disks that are accessible from all processors. ...
... Architecture provides a degree of fault-tolerance — if a processor fails, the other processors can take over its tasks since the database is resident on disks that are accessible from all processors. ...
How In-Memory Affects Database Design
... The Difficulty of Data Integrity • With on-disk structures, we used constraints for most issues (Uniqueness, Foreign Key, Simple Predicates) • With in-memory code, we have to implement in stored procedures –Uniqueness on > 1 column set suffers from timing (If N connections are inserting the same da ...
... The Difficulty of Data Integrity • With on-disk structures, we used constraints for most issues (Uniqueness, Foreign Key, Simple Predicates) • With in-memory code, we have to implement in stored procedures –Uniqueness on > 1 column set suffers from timing (If N connections are inserting the same da ...
UIC Data Conversion and Submission
... • Can be used to convert from three source database platforms: – MS Access (database) – Oracle (database/view) – SQL Server (database/view) ...
... • Can be used to convert from three source database platforms: – MS Access (database) – Oracle (database/view) – SQL Server (database/view) ...
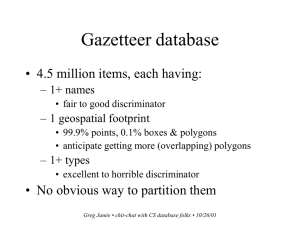
CS chit-chat - ERI people pages
... Query translation • Gazetteer is an instance of a much more general problem • To wit: – how to describe the automatic translation of dynamic queries written in an abstract query language to SQL – in an easy, powerful, flexible way – making as few assumptions as possible about the underlying schema ...
... Query translation • Gazetteer is an instance of a much more general problem • To wit: – how to describe the automatic translation of dynamic queries written in an abstract query language to SQL – in an easy, powerful, flexible way – making as few assumptions as possible about the underlying schema ...
1 - Wseas.us
... mining algorithms are analyzed for side effect that might invade data privacy. The objective in privacy-preserving data mining is to develop algorithms for modifying the original data in some way, so that private data and knowledge remain private even after mining process. Given specific rules to be ...
... mining algorithms are analyzed for side effect that might invade data privacy. The objective in privacy-preserving data mining is to develop algorithms for modifying the original data in some way, so that private data and knowledge remain private even after mining process. Given specific rules to be ...
An Overview of Data Warehousing, Data mining, OLAP and
... granularities, which facilitates effective data mining. The functional and performance requirements of OLAP are quite different from those of the on-line transaction processing applications traditionally supported by the operational databases. Data can now be stored in many different types of databa ...
... granularities, which facilitates effective data mining. The functional and performance requirements of OLAP are quite different from those of the on-line transaction processing applications traditionally supported by the operational databases. Data can now be stored in many different types of databa ...
Slides PPT
... SchemaEvolver tool compares generated schema with those previously stored. Depending on similarity weighting of closest match the outcome is: Exact match – Metadata conforms to an existing XML Schema Similar – Existing XML Schema modified to include differences No match – Metadata conforms to a new ...
... SchemaEvolver tool compares generated schema with those previously stored. Depending on similarity weighting of closest match the outcome is: Exact match – Metadata conforms to an existing XML Schema Similar – Existing XML Schema modified to include differences No match – Metadata conforms to a new ...
White Paper
... query languages that are widely in use—that can easily interface with existing back-office databases, messaging systems, and application servers—and that exploits the full performance potential of today’s networked, memoryrich computing platforms. This is the generation of infrastructure software fo ...
... query languages that are widely in use—that can easily interface with existing back-office databases, messaging systems, and application servers—and that exploits the full performance potential of today’s networked, memoryrich computing platforms. This is the generation of infrastructure software fo ...
Data Models - Assignment Point
... A database cannot contain a tuple with a value for a foreign key that does not match a primary key value in the referenced relation. Or, a foreign key must refer to a tuple that exists. Motivation: If referential integrity were violated, we could have relationships between entities that we do not ha ...
... A database cannot contain a tuple with a value for a foreign key that does not match a primary key value in the referenced relation. Or, a foreign key must refer to a tuple that exists. Motivation: If referential integrity were violated, we could have relationships between entities that we do not ha ...
while($row=mysql_fetch_array($result))
... webpage, which usually is dynamically built. This means that there is a database with many records, and the server side files will run some specifically lines “query”, interacting with the database, and the returned data will be sent to the user browser. In this paper we try to analyze and improve t ...
... webpage, which usually is dynamically built. This means that there is a database with many records, and the server side files will run some specifically lines “query”, interacting with the database, and the returned data will be sent to the user browser. In this paper we try to analyze and improve t ...
Views-Your Window on Data
... Kthe data upon which the view is based are not in the same DBMS, your options are limited. Some DBMSs can support views of data in heterogeneous systems: You could create- a DBMS view in this fashion. then access that view with SAS/ACCESS software. The other alternative is to create a SAS/ACCESS vie ...
... Kthe data upon which the view is based are not in the same DBMS, your options are limited. Some DBMSs can support views of data in heterogeneous systems: You could create- a DBMS view in this fashion. then access that view with SAS/ACCESS software. The other alternative is to create a SAS/ACCESS vie ...
Database Modeling and Design - Lecture Notes
... * One-to-many binary relationship – primary key on “one” side entity copied as a foreign key in the “many” side entity’s table * Recursive binary relationship – same rules as other binary relationships * Ternary relationship – directly to a SQL table, taking the 3 primary keys of the 3 entities asso ...
... * One-to-many binary relationship – primary key on “one” side entity copied as a foreign key in the “many” side entity’s table * Recursive binary relationship – same rules as other binary relationships * Ternary relationship – directly to a SQL table, taking the 3 primary keys of the 3 entities asso ...
OODBMS
... It’s not hard to see why many are encouraged by the bright future and potential of the ObjectOriented Database management system model. However, there have been some issues that have prevented it from achieving the early success that many had foreseen. Let’s have a look at some unresolved issues tha ...
... It’s not hard to see why many are encouraged by the bright future and potential of the ObjectOriented Database management system model. However, there have been some issues that have prevented it from achieving the early success that many had foreseen. Let’s have a look at some unresolved issues tha ...