Database
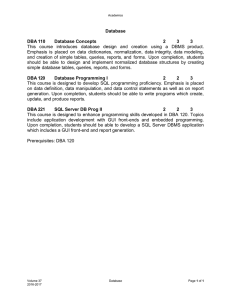
... Emphasis is placed on data dictionaries, normalization, data integrity, data modeling, and creation of simple tables, queries, reports, and forms. Upon completion, students should be able to design and implement normalized database structures by creating simple database tables, queries, reports, and ...
... Emphasis is placed on data dictionaries, normalization, data integrity, data modeling, and creation of simple tables, queries, reports, and forms. Upon completion, students should be able to design and implement normalized database structures by creating simple database tables, queries, reports, and ...
Access methods for time
... A better solution is to store the history of each key separately, i.e., cluster data by key only. Access to a key’s (transaction time) history can be implemented by a hashing function or B tree. The list of versions of each key can be further organized in a separate array indexed by transactio ...
... A better solution is to store the history of each key separately, i.e., cluster data by key only. Access to a key’s (transaction time) history can be implemented by a hashing function or B tree. The list of versions of each key can be further organized in a separate array indexed by transactio ...
Basic Access Training
... i. divide data into it’s most basic form EX. Student Name split into first name, middle name or initial, last Name ii. divide information into logical tables EX. Students, Organizations, grades, etc. (one table for each group of information with links to main table 5. Second Step – Creating Tables a ...
... i. divide data into it’s most basic form EX. Student Name split into first name, middle name or initial, last Name ii. divide information into logical tables EX. Students, Organizations, grades, etc. (one table for each group of information with links to main table 5. Second Step – Creating Tables a ...
Application Development Concepts
... • Disk Storage / File System • DBMS Application – Server – Instance – Schema ...
... • Disk Storage / File System • DBMS Application – Server – Instance – Schema ...
Centerfield`s HomeRun suite of database tools let IT easily improve
... changes or deep database expertise. AutoDBA was created with one goal in mind; to provide advanced DB2 advice to administrators. Rather than force administrators to become database experts: gather the right information, analyze that data, make recommendations and implement changes… AutoDBA does it f ...
... changes or deep database expertise. AutoDBA was created with one goal in mind; to provide advanced DB2 advice to administrators. Rather than force administrators to become database experts: gather the right information, analyze that data, make recommendations and implement changes… AutoDBA does it f ...
What`s the Shape of Databases to Come?
... C++/Java O-R tools: tables as backend stores for mapped language objects MSFT: EDM & EntitySQL for ADO.NET++ MDM: tables as backend stores for product data (for example) with a rich & extensible data model SaaS: tables as backend stores for multi-tenant data sets with tenant-extensible schemas ...
... C++/Java O-R tools: tables as backend stores for mapped language objects MSFT: EDM & EntitySQL for ADO.NET++ MDM: tables as backend stores for product data (for example) with a rich & extensible data model SaaS: tables as backend stores for multi-tenant data sets with tenant-extensible schemas ...
Creating Functions
... tables, together with various components of SELECT statement itself, to find most efficient way to retrieve data required by query and satisfy any joins ...
... tables, together with various components of SELECT statement itself, to find most efficient way to retrieve data required by query and satisfy any joins ...
ODBC-101 - LuisGomez.NET
... Slightly Different steps for each release. These steps are for 2003. Import vs. Link. Queries. Reports. ...
... Slightly Different steps for each release. These steps are for 2003. Import vs. Link. Queries. Reports. ...
19. Implementation - University of St. Thomas
... However, indices slow update speed and take disk space. This is further complicated by the fact that you can index combinations of columns in addition to single columns. So if you have a table with 12 columns, there are over 1.3 billion possible column combinations that can be indexed in this one ta ...
... However, indices slow update speed and take disk space. This is further complicated by the fact that you can index combinations of columns in addition to single columns. So if you have a table with 12 columns, there are over 1.3 billion possible column combinations that can be indexed in this one ta ...
Sybase IQ Multiplex - Designed For Analytics (invited)
... enables every column in a Sybase IQ database to be indexed, often with more than one index type. For a column store, the results of the Where clause needs to be a mask of rows to be projected that can be applied to each column and virtual rows created as cells are read in parallel from each column a ...
... enables every column in a Sybase IQ database to be indexed, often with more than one index type. For a column store, the results of the Where clause needs to be a mask of rows to be projected that can be applied to each column and virtual rows created as cells are read in parallel from each column a ...
raghu8
... scan retrieving all records. • Sorted Files: Best if records must be retrieved in some order, or only a `range’ of records is needed. • Hashed Files: Good for equality selections. • File is a collection of buckets. Bucket = primary page plus zero or more overflow pages. • Hashing function h: h(r) = ...
... scan retrieving all records. • Sorted Files: Best if records must be retrieved in some order, or only a `range’ of records is needed. • Hashed Files: Good for equality selections. • File is a collection of buckets. Bucket = primary page plus zero or more overflow pages. • Hashing function h: h(r) = ...
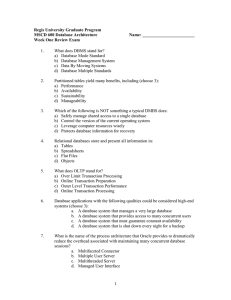
Regis University Graduate Program MSCD 600 Database Architecture Name: ________________________
... a. A database system that manages a very large database b. A database system that provides access to many concurrent users c. A database system that must guarantee constant availability d. A database system that is shut down every night for a backup ...
... a. A database system that manages a very large database b. A database system that provides access to many concurrent users c. A database system that must guarantee constant availability d. A database system that is shut down every night for a backup ...
Database Administration
... DBMS writes a special record called checkpoint record to the log file which is like the snapshot of the database. This record contains information to restart the system. Any dirty data blocks are written to the system ...
... DBMS writes a special record called checkpoint record to the log file which is like the snapshot of the database. This record contains information to restart the system. Any dirty data blocks are written to the system ...
ENTITY RELATIONAL MODEL: • Entities: 1. An object in the mini
... database, and its requirements in a top-down fashion. Diagrams created by this process are called entity-relationship diagrams, ER diagrams, or ERDs. requirements analysis to describe information needs or the type of information that is to be stored in a database. The data modeling technique can be ...
... database, and its requirements in a top-down fashion. Diagrams created by this process are called entity-relationship diagrams, ER diagrams, or ERDs. requirements analysis to describe information needs or the type of information that is to be stored in a database. The data modeling technique can be ...
Access Project 3
... Validation Rules (AC 139) Validation Rules are rules to be followed when entering data Validation text – the message that will appear if a user violates the validation rule Required field – a field in which the user must enter data Range of values – entry must lie within a certain range of ...
... Validation Rules (AC 139) Validation Rules are rules to be followed when entering data Validation text – the message that will appear if a user violates the validation rule Required field – a field in which the user must enter data Range of values – entry must lie within a certain range of ...
TRUNCATE TABLE
... – IDENTITY columns will receive the next identity value – Columns with a timestamp data type will receive the next appropriate values – All other columns will receive a NULL ...
... – IDENTITY columns will receive the next identity value – Columns with a timestamp data type will receive the next appropriate values – All other columns will receive a NULL ...
slides
... unnecessarily distracted by the shiny, new-fangled, NoSQL red buttons just yet. Relational databases may not be hot or sexy but for your important data there is no substitute.” ...
... unnecessarily distracted by the shiny, new-fangled, NoSQL red buttons just yet. Relational databases may not be hot or sexy but for your important data there is no substitute.” ...
The Relational Database Model
... Makes the relational database work Tables within the database share common attributes Enables tables to be linked together Multiple occurrences of values not redundant when required to make the relationship work Redundancy exists only when there is unnecessary duplication of attribute valu ...
... Makes the relational database work Tables within the database share common attributes Enables tables to be linked together Multiple occurrences of values not redundant when required to make the relationship work Redundancy exists only when there is unnecessary duplication of attribute valu ...
COMP 430 Intro. to Database Systems
... Field exists already – no extra data Concise – single short value Human-readable, -searchable Immutable (typically) Data exists ...
... Field exists already – no extra data Concise – single short value Human-readable, -searchable Immutable (typically) Data exists ...
Session Title That is Really Long and Covers Two Lines
... Using Complex types Legacy databases / explicit mappings ...
... Using Complex types Legacy databases / explicit mappings ...
Database Management issues from Hoffer - Moodle
... The process of managing simultaneous operations against a database so that data integrity is maintained and the operations do not interfere with each other in a multi-user environment ...
... The process of managing simultaneous operations against a database so that data integrity is maintained and the operations do not interfere with each other in a multi-user environment ...
Database Systems
... particular user’s needs, used to prevent sensitive data from being accessed by unauthorized personnel ...
... particular user’s needs, used to prevent sensitive data from being accessed by unauthorized personnel ...
SQL Server 2012: Indexing
... One of the most important routes to high performance in a SQL Server database is the index. Indexes speed up the querying process by providing swift access to rows in the data tables, similarly to the way a book’s index helps you find information quickly within that book. The primary reason indexes ...
... One of the most important routes to high performance in a SQL Server database is the index. Indexes speed up the querying process by providing swift access to rows in the data tables, similarly to the way a book’s index helps you find information quickly within that book. The primary reason indexes ...
SQLIntroduction - Free Stuff Jamaica
... when a table is created from an existing table only the structure is copied; the primary, alternate and foreign key definitions is not inherited ...
... when a table is created from an existing table only the structure is copied; the primary, alternate and foreign key definitions is not inherited ...
Slide 1 - Primary Resources
... Database Vocabulary It can be useful to collect information. Information can be put on ...
... Database Vocabulary It can be useful to collect information. Information can be put on ...