TimesTen SQL Reference
... any programs installed on the hardware, and/or documentation, delivered to U.S. Government end users are "commercial computer software" pursuant to the applicable Federal Acquisition Regulation and agency-specific supplemental regulations. As such, use, duplication, disclosure, modification, and ada ...
... any programs installed on the hardware, and/or documentation, delivered to U.S. Government end users are "commercial computer software" pursuant to the applicable Federal Acquisition Regulation and agency-specific supplemental regulations. As such, use, duplication, disclosure, modification, and ada ...
Oracle Essbase Technical Reference
... adaptation shall be subject to the restrictions and license terms set forth in the applicable Government contract, and, to the extent applicable by the terms of the Government contract, the additional rights set forth in FAR 52.227-19, Commercial Computer Software License (December 2007). Oracle USA ...
... adaptation shall be subject to the restrictions and license terms set forth in the applicable Government contract, and, to the extent applicable by the terms of the Government contract, the additional rights set forth in FAR 52.227-19, Commercial Computer Software License (December 2007). Oracle USA ...
Application Development Guide: Building and Running Applications IBM
... you need to know about coding, debugging, building, and running DB2 applications: v Application Development Guide: Programming Client Applications contains what you need to know to code standalone DB2 applications that run on DB2 clients. It includes information on: – Programming interfaces that are ...
... you need to know about coding, debugging, building, and running DB2 applications: v Application Development Guide: Programming Client Applications contains what you need to know to code standalone DB2 applications that run on DB2 clients. It includes information on: – Programming interfaces that are ...
SAP Adaptive Server Enterprise 16.0 ®
... Some software products marketed by SAP AG and its distributors contain proprietary software components of other software vendors. National product specifications may vary. These materials are provided by SAP AG and its affiliated companies ("SAP Group") for informational purposes only, without repre ...
... Some software products marketed by SAP AG and its distributors contain proprietary software components of other software vendors. National product specifications may vary. These materials are provided by SAP AG and its affiliated companies ("SAP Group") for informational purposes only, without repre ...
Avaya Call Management System Database Items
... necessarily endorse the products, services, or information described or offered within them. Avaya does not guarantee that these links will work all the time and has no control over the availability of the linked pages. Warranty Avaya provides a limited warranty on Avaya hardware and software. Refer ...
... necessarily endorse the products, services, or information described or offered within them. Avaya does not guarantee that these links will work all the time and has no control over the availability of the linked pages. Warranty Avaya provides a limited warranty on Avaya hardware and software. Refer ...
DB2 10.1 LUW - Troubleshooting and Tuning Database Performance
... problems with your DB2 database software, the troubleshooting and support information contains instructions for using the problem determination resources that are provided with your DB2 database products. Part 1. Tuning database performance As a database administrator, you might encounter a situatio ...
... problems with your DB2 database software, the troubleshooting and support information contains instructions for using the problem determination resources that are provided with your DB2 database products. Part 1. Tuning database performance As a database administrator, you might encounter a situatio ...
SQL The Complete Reference - Vedant College of Engineering
... How this Book Is Organized The book is divided into six parts that cover various aspects of the SQL language: • Part One, "An Overview of SQL," provides an introduction to SQL and a market perspective of its role as a database language. Its four chapters describe the history of SQL, the evolution of ...
... How this Book Is Organized The book is divided into six parts that cover various aspects of the SQL language: • Part One, "An Overview of SQL," provides an introduction to SQL and a market perspective of its role as a database language. Its four chapters describe the history of SQL, the evolution of ...
SESAM/SQL-Server V8.0 BS2000/OSD Core Manual
... RECOVER CATALOG_SPACE USING REPLICATION . . RECOVER SPACE USING REPLICATION . . . . . . . . Reset the original database using replications . . . . . . . . . RECOVER CATALOG TO REPLICATION . . . . . . . . . Reset using RECOVER CATALOG USING REPLICATION RECOVER CATALOG_SPACE TO REPLICATION . . . . . R ...
... RECOVER CATALOG_SPACE USING REPLICATION . . RECOVER SPACE USING REPLICATION . . . . . . . . Reset the original database using replications . . . . . . . . . RECOVER CATALOG TO REPLICATION . . . . . . . . . Reset using RECOVER CATALOG USING REPLICATION RECOVER CATALOG_SPACE TO REPLICATION . . . . . R ...
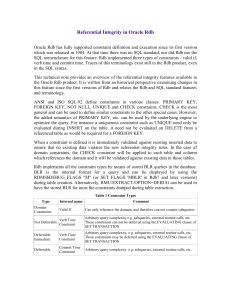
Referential Integrity in Oracle Rdb
... RDO. The database administrator can also force evaluation of all constraints using the /CONSTRAINT qualifier with the RMU/VERIFY command. This is a useful tool for checking the referential integrity of the entire database. Note that domain constraints are not currently evaluated by RMU/VERIFY. In Rd ...
... RDO. The database administrator can also force evaluation of all constraints using the /CONSTRAINT qualifier with the RMU/VERIFY command. This is a useful tool for checking the referential integrity of the entire database. Note that domain constraints are not currently evaluated by RMU/VERIFY. In Rd ...
SQL Server 2012 T-SQL Recipes: A Problem
... The asterisk symbol (*) returns all columns of the table or view you are querying. All other details are as explained in the previous recipe. Please remember that, as good practice, it is better to reference the columns you want to retrieve explicitly instead of using SELECT *. If you write an appli ...
... The asterisk symbol (*) returns all columns of the table or view you are querying. All other details are as explained in the previous recipe. Please remember that, as good practice, it is better to reference the columns you want to retrieve explicitly instead of using SELECT *. If you write an appli ...
ORACLE: PL/SQL
... Datafiles • Every Oracle database has one or more physical datafiles. • The datafiles contain all the database data. • The data of logical database structures, such as tables and indexes, is physically stored in the datafiles allocated for a database. The characteristics of datafiles are: ■ A datafi ...
... Datafiles • Every Oracle database has one or more physical datafiles. • The datafiles contain all the database data. • The data of logical database structures, such as tables and indexes, is physically stored in the datafiles allocated for a database. The characteristics of datafiles are: ■ A datafi ...
Teradata Archive/Recovery Utility Reference
... Corporation will be free to use any ideas, concepts, know-how, or techniques contained in such Feedback for any purpose whatsoever, including developing, manufacturing, or marketing products or services incorporating Feedback. Copyright © 1997-2016 by Teradata. All Rights Reserved. ...
... Corporation will be free to use any ideas, concepts, know-how, or techniques contained in such Feedback for any purpose whatsoever, including developing, manufacturing, or marketing products or services incorporating Feedback. Copyright © 1997-2016 by Teradata. All Rights Reserved. ...
RFID Malware: Design Principles and Examples,
... RFID tags, contactless smart cards (more storage space allows more complex attacks), or resource rich RFID tag simulating devices (which are fully fledged computers). 3.2. RFID worms A worm is a program that self-propagates across a network, exploiting security flaws in widely used services. A worm ...
... RFID tags, contactless smart cards (more storage space allows more complex attacks), or resource rich RFID tag simulating devices (which are fully fledged computers). 3.2. RFID worms A worm is a program that self-propagates across a network, exploiting security flaws in widely used services. A worm ...
Completeness of Queries over Incomplete Databases
... the presence of the same unknown value in different tuples. The c-tables allow a further refinement of the unknown information by enhancing it with conditions, e.g., comparisons or range restrictions. The basic idea of the semantics of all three formalisms is the same: It is the set of all databases ...
... the presence of the same unknown value in different tuples. The c-tables allow a further refinement of the unknown information by enhancing it with conditions, e.g., comparisons or range restrictions. The basic idea of the semantics of all three formalisms is the same: It is the set of all databases ...