Modeling C preprocessor metaprograms using purely functional
... Each constructor creates a sequence, where the first item is the name of the constructor function itself that can be used as a tag later. This makes pattern matching possible, which is explained in the next subsection. The rest of the sequence is simply holding the actual arguments provided to the c ...
... Each constructor creates a sequence, where the first item is the name of the constructor function itself that can be used as a tag later. This makes pattern matching possible, which is explained in the next subsection. The rest of the sequence is simply holding the actual arguments provided to the c ...
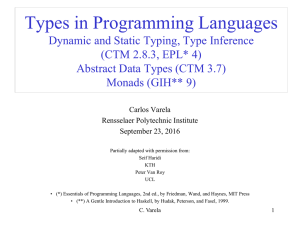
ppt - Rensselaer Polytechnic Institute: Computer Science
... properties, independent of the existence of other (possibly malicious) entities (either computations or humans) in the system • What properties must a language have to be secure? • One way to make a language secure is to base it on capabilities – A capability is an unforgeable language entity (« tic ...
... properties, independent of the existence of other (possibly malicious) entities (either computations or humans) in the system • What properties must a language have to be secure? • One way to make a language secure is to base it on capabilities – A capability is an unforgeable language entity (« tic ...
Type-indexed data types - School of Computer Science
... but rather complex languages not intended for programmers but for compiler writers; typed intermediate languages are not built on top of an existing programming language, so there is no integration problem; and, most importantly, typed intermediate languages interpret (a representation of a) type ar ...
... but rather complex languages not intended for programmers but for compiler writers; typed intermediate languages are not built on top of an existing programming language, so there is no integration problem; and, most importantly, typed intermediate languages interpret (a representation of a) type ar ...
Post Systems in Programming Languages Pr ecis 1 Introduction
... A term is provable in a Post system if we can nd a proof of it. The set of words provable from a Post system forms the language derived by the system. Sometimes it is necessary to consider the language derived by a Post system to be the set of strings from a subset of the signs which are provable. ...
... A term is provable in a Post system if we can nd a proof of it. The set of words provable from a Post system forms the language derived by the system. Sometimes it is necessary to consider the language derived by a Post system to be the set of strings from a subset of the signs which are provable. ...
Constructive Mathematics in Theory and Programming Practice
... later in this paper). When working in any axiomatic system, we must take care to use only intuitionistic logic, and therefore to ensure that we do not adopt a classical axiom that implies LEM or some other nonconstructive principle. For example, in IZF we cannot adopt the common classical form of th ...
... later in this paper). When working in any axiomatic system, we must take care to use only intuitionistic logic, and therefore to ensure that we do not adopt a classical axiom that implies LEM or some other nonconstructive principle. For example, in IZF we cannot adopt the common classical form of th ...
The Clean programming language
... Clean is a general purpose functional programming language, it is widely used in scientific research all over the world. Featuring lazy evaluation, unique type inferencing system, and graph rewriting semantics, Clean is useful for writing relatively bugfree programs in fewer lines of code. Clean ...
... Clean is a general purpose functional programming language, it is widely used in scientific research all over the world. Featuring lazy evaluation, unique type inferencing system, and graph rewriting semantics, Clean is useful for writing relatively bugfree programs in fewer lines of code. Clean ...
Concepts of Programming Languages A Brief Intro to Programming
... - Lisp with its quoting and EVAL was the first meta programming ...
... - Lisp with its quoting and EVAL was the first meta programming ...
Formal Foundations of Computer Security
... P1 , P2 , P3 , and the events - all the actions taken, say e1 , e2 , e3 , ... Each action has a location apparent from its definition, say loc(e). Some of the events are comparable ei < ej and others aren’t, e.g. imagine two processes that never communicate e1 , e2 , ... at i and e0i , e02 , ... at ...
... P1 , P2 , P3 , and the events - all the actions taken, say e1 , e2 , e3 , ... Each action has a location apparent from its definition, say loc(e). Some of the events are comparable ei < ej and others aren’t, e.g. imagine two processes that never communicate e1 , e2 , ... at i and e0i , e02 , ... at ...
Programming Language Semantics with Isabelle/HOL
... especially conditional, let and case expressions. Formulas are terms of type bool. There are the basic constants True and False and the usual logical connectives (in decreasing order of precedence): ¬, ∧, ∨, −→. Equality is available in the form of the infix function = of type 0a ⇒ 0a ⇒ bool. It als ...
... especially conditional, let and case expressions. Formulas are terms of type bool. There are the basic constants True and False and the usual logical connectives (in decreasing order of precedence): ¬, ∧, ∨, −→. Equality is available in the form of the infix function = of type 0a ⇒ 0a ⇒ bool. It als ...
Functional Programming
... Functional programming languages are carefully designed to support problem solving. There are many features in these languages which help the user to design clear, concise, abstract, modular, correct and reusable solutions to problems. The functional Style of Programming allows the formulation of so ...
... Functional programming languages are carefully designed to support problem solving. There are many features in these languages which help the user to design clear, concise, abstract, modular, correct and reusable solutions to problems. The functional Style of Programming allows the formulation of so ...
Register Allocation
... • Properties of functions defined using foldr can be proved using algebraic properties of foldr, such as fusion and the banana split rule; • Advanced program optimisations can be simpler if foldr is used in place of explicit recursion. ...
... • Properties of functions defined using foldr can be proved using algebraic properties of foldr, such as fusion and the banana split rule; • Advanced program optimisations can be simpler if foldr is used in place of explicit recursion. ...
A constructive approach to nonstandard analysis*
... metamathematical results on nonarchimedean extensions, e.g. Martin-Lof’s interpretation of infinity symbols. We also indicate how such theories might be used. Unfortunately, they have no useful external notions, such as being infinitesimal. In Section 3 we introduce a new theory, internal HA”‘, whic ...
... metamathematical results on nonarchimedean extensions, e.g. Martin-Lof’s interpretation of infinity symbols. We also indicate how such theories might be used. Unfortunately, they have no useful external notions, such as being infinitesimal. In Section 3 we introduce a new theory, internal HA”‘, whic ...
Dedukti
... 1. Predicate logic does not allow the use of bound variables, except those bound by the quantifiers ∀ and ∃. For instance, it is not possible to define, in predicate logic, a unary function symbol 7→ that would bind a variable in its argument. 2. Predicate logic ignores the propositions-as-types pri ...
... 1. Predicate logic does not allow the use of bound variables, except those bound by the quantifiers ∀ and ∃. For instance, it is not possible to define, in predicate logic, a unary function symbol 7→ that would bind a variable in its argument. 2. Predicate logic ignores the propositions-as-types pri ...
1 Salient Features of Functional Programming
... – The last thing to do in the function call is to recurse. – It is called a tail call. – The compiler implements such tail recursion as loops. In particular: If the call is tail, then it will not consume stack. • Recursive thinking extends to data types: – E.g. a binary tree is either the empty tree ...
... – The last thing to do in the function call is to recurse. – It is called a tail call. – The compiler implements such tail recursion as loops. In particular: If the call is tail, then it will not consume stack. • Recursive thinking extends to data types: – E.g. a binary tree is either the empty tree ...
Algol and Haskell
... Successful syntax, BNF -- used by many successors statement oriented begin … end blocks (like C { … } ) if … then … else ...
... Successful syntax, BNF -- used by many successors statement oriented begin … end blocks (like C { … } ) if … then … else ...
Algebraic Data Types - University of Edinburgh
... Algebraic types are the most important component of functional programming that I haven't covered yet. We've seen lots of types: integers, floating point numbers, characters, booleans. Also ways of building types: lists, functions, tuples. All very useful, built in to Haskell. We get lists of intege ...
... Algebraic types are the most important component of functional programming that I haven't covered yet. We've seen lots of types: integers, floating point numbers, characters, booleans. Also ways of building types: lists, functions, tuples. All very useful, built in to Haskell. We get lists of intege ...
Chapter 2
... type from Int to tuple and the length of list is not fixed. This is in contrast to the arrays in traditional imperative languages that have fixed lengths. What is exciting about lists in Haskell is that there are a lot of functions defined for accessing and manipulation of lists as well as defining ...
... type from Int to tuple and the length of list is not fixed. This is in contrast to the arrays in traditional imperative languages that have fixed lengths. What is exciting about lists in Haskell is that there are a lot of functions defined for accessing and manipulation of lists as well as defining ...