Introduction to quantum statistical thermodynamics by Armen
... including a pure state |ψ⟩⟨ψ|, describes an ensemble of identically prepared systems. For instance, in an ideal SternGerlach experiment all particles of the upper beam together are described by the wavefunction | ↑⟩ or the pure density matix | ↑⟩⟨↑ |. The description is optimal, in the sense that al ...
... including a pure state |ψ⟩⟨ψ|, describes an ensemble of identically prepared systems. For instance, in an ideal SternGerlach experiment all particles of the upper beam together are described by the wavefunction | ↑⟩ or the pure density matix | ↑⟩⟨↑ |. The description is optimal, in the sense that al ...
Introduction to quantum spin systems
... suppressed and the Hamiltonian is effectively described only by the exchange term which represents the interaction between the spin of frozen electrons. Apart from a constant this is the Heisenberg Hamiltonian ...
... suppressed and the Hamiltonian is effectively described only by the exchange term which represents the interaction between the spin of frozen electrons. Apart from a constant this is the Heisenberg Hamiltonian ...
Chapter 10.
... But they could be solved if a classical Satisfiability or one of other similar Decision Functions were solvable. This can be done using Grover Algorithm. This chapter will present quantum algorithms: Deutsch, Deutsch-Jozsa, BernsteinVazirani and their modifications and next the Grover algorithm. Nex ...
... But they could be solved if a classical Satisfiability or one of other similar Decision Functions were solvable. This can be done using Grover Algorithm. This chapter will present quantum algorithms: Deutsch, Deutsch-Jozsa, BernsteinVazirani and their modifications and next the Grover algorithm. Nex ...
Aalborg Universitet
... Zc (M/m) := inf{Z > 0, H = H(Z, M/m) has at least one bound state}, it follows from our last theorem that Zc (M/m) ≤ Zcub (M/m). The curve Zcub (M/m) is plotted on figure 2, where we used θ1,2 instead of the ratio M/m. Remarks 8. (a) Rosenthal found numerically Zcub ( π2 ), i.e. Zcub for M = ∞ to be ...
... Zc (M/m) := inf{Z > 0, H = H(Z, M/m) has at least one bound state}, it follows from our last theorem that Zc (M/m) ≤ Zcub (M/m). The curve Zcub (M/m) is plotted on figure 2, where we used θ1,2 instead of the ratio M/m. Remarks 8. (a) Rosenthal found numerically Zcub ( π2 ), i.e. Zcub for M = ∞ to be ...
The next stage: quantum game theory
... and that information theory is inseparable from both applied and fundamental physics. Attention to the very physical aspects of information processing revealed new perspectives of computation, cryptography and communication methods. In most of the cases quantum description of the system provides adv ...
... and that information theory is inseparable from both applied and fundamental physics. Attention to the very physical aspects of information processing revealed new perspectives of computation, cryptography and communication methods. In most of the cases quantum description of the system provides adv ...
Exact quantum query complexity
... We show that exact quantum query complexity is richer than just computing parities. We present some new examples of total boolean functions f such that QE (f ) is a constant multiple of D(f ) (between 1/2 and 2/3). We show that these separations cannot be obtained by just computing parities of pairs ...
... We show that exact quantum query complexity is richer than just computing parities. We present some new examples of total boolean functions f such that QE (f ) is a constant multiple of D(f ) (between 1/2 and 2/3). We show that these separations cannot be obtained by just computing parities of pairs ...
Nature 425, (937
... arrays7,8 to the observation of a Mott insulating state of quantum gases9,10. Important applications of atoms in a Mott insulating state in quantum information processing were envisaged early on. The Mott state itself, with one atom per lattice site, could act as a huge quantum memory, in which info ...
... arrays7,8 to the observation of a Mott insulating state of quantum gases9,10. Important applications of atoms in a Mott insulating state in quantum information processing were envisaged early on. The Mott state itself, with one atom per lattice site, could act as a huge quantum memory, in which info ...
What is “a world”
... All is ( r1, r2 ,...., rN , t ) evolving according to deterministic equation ...
... All is ( r1, r2 ,...., rN , t ) evolving according to deterministic equation ...
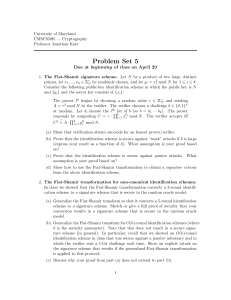
Quantum key distribution
Quantum key distribution (QKD) uses quantum mechanics to guarantee secure communication. It enables two parties to produce a shared random secret key known only to them, which can then be used to encrypt and decrypt messages. It is often incorrectly called quantum cryptography, as it is the most well known example of the group of quantum cryptographic tasks.An important and unique property of quantum key distribution is the ability of the two communicating users to detect the presence of any third party trying to gain knowledge of the key. This results from a fundamental aspect of quantum mechanics: the process of measuring a quantum system in general disturbs the system. A third party trying to eavesdrop on the key must in some way measure it, thus introducing detectable anomalies. By using quantum superpositions or quantum entanglement and transmitting information in quantum states, a communication system can be implemented which detects eavesdropping. If the level of eavesdropping is below a certain threshold, a key can be produced that is guaranteed to be secure (i.e. the eavesdropper has no information about it), otherwise no secure key is possible and communication is aborted.The security of encryption that uses quantum key distribution relies on the foundations of quantum mechanics, in contrast to traditional public key cryptography which relies on the computational difficulty of certain mathematical functions, and cannot provide any indication of eavesdropping at any point in the communication process, or any mathematical proof as to the actual complexity of reversing the one-way functions used. QKD has provable security based on information theory, and forward secrecy.Quantum key distribution is only used to produce and distribute a key, not to transmit any message data. This key can then be used with any chosen encryption algorithm to encrypt (and decrypt) a message, which can then be transmitted over a standard communication channel. The algorithm most commonly associated with QKD is the one-time pad, as it is provably secure when used with a secret, random key. In real world situations, it is often also used with encryption using symmetric key algorithms like the Advanced Encryption Standard algorithm. In the case of QKD this comparison is based on the assumption of perfect single-photon sources and detectors, that cannot be easily implemented.