Fast random number generator based on quantum uncertainty
... machines, one other way is to collect random numbers from the environment. Parameters of complex classical systems can be considered as good source of randomness as they very often behaves chaotically and in practical cannot be predicted. However, classical systems are still governed by classical me ...
... machines, one other way is to collect random numbers from the environment. Parameters of complex classical systems can be considered as good source of randomness as they very often behaves chaotically and in practical cannot be predicted. However, classical systems are still governed by classical me ...
Entanglement of Atoms via Cold Controlled Collisions
... even determine the sign of the scattering length by applying laser pulses with a pulse area different from py2 [15]. (b) In a similar way, one can also measure the spatial correlation function by applying the second laser pulse (iii) and population detection (iv) without moving the potential back to ...
... even determine the sign of the scattering length by applying laser pulses with a pulse area different from py2 [15]. (b) In a similar way, one can also measure the spatial correlation function by applying the second laser pulse (iii) and population detection (iv) without moving the potential back to ...
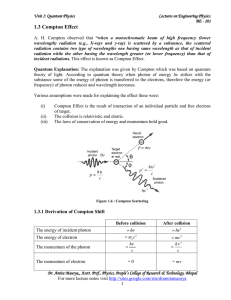
1.3 Compton Effect - IndiaStudyChannel.com
... wavelength) radiation (e.g., X-rays and γ-ray) is scattered by a substance, the scattered radiation contains two type of wavelengths one having same wavelength as that of incident radiation while the other having the wavelength greater (or lower frequency) than that of incident radiations. This effe ...
... wavelength) radiation (e.g., X-rays and γ-ray) is scattered by a substance, the scattered radiation contains two type of wavelengths one having same wavelength as that of incident radiation while the other having the wavelength greater (or lower frequency) than that of incident radiations. This effe ...
The Feynman Problem-Solving Algorithm: (1)
... Feynman was fond of saying that all of quantum mechanics can be gleaned from carefully thinking through the implications of this single experiment. The most baffling part of this experiment comes when only one photon at a time is fired at the barrier with both slits open. The pattern of interferenc ...
... Feynman was fond of saying that all of quantum mechanics can be gleaned from carefully thinking through the implications of this single experiment. The most baffling part of this experiment comes when only one photon at a time is fired at the barrier with both slits open. The pattern of interferenc ...
Quantum Relaxation after a Quench in Systems with Boundaries Ferenc Iglo´i *
... used standard free-fermionic techniques [19,21]. For the surface site, l ¼ 1, most of the calculations are analytical, whereas for l > 1 numerical calculations have been made for large finite systems up to L ¼ 384. We have performed quenches for various pairs of transverse fields, h0 and h and calcu ...
... used standard free-fermionic techniques [19,21]. For the surface site, l ¼ 1, most of the calculations are analytical, whereas for l > 1 numerical calculations have been made for large finite systems up to L ¼ 384. We have performed quenches for various pairs of transverse fields, h0 and h and calcu ...
ABSTRACT PHOTON PAIR PRODUCTION FROM A HOT ATOMIC ENSEMBLE IN THE DIAMOND CONFIGURATION
... the distribution of entanglement over large distances. The best known technology to share entanglement is pairs of entangled photons. Unfortunately, terrestrial communication relies on light transmission through optical fibers, which attenuate the signals in distances of just a few tens of kilometer ...
... the distribution of entanglement over large distances. The best known technology to share entanglement is pairs of entangled photons. Unfortunately, terrestrial communication relies on light transmission through optical fibers, which attenuate the signals in distances of just a few tens of kilometer ...
Quantum Langevin model for exoergic ion
... conventional approach to a few simple systems such as D + H2 , with little hope for more complex systems. The multichannel quantum-defect theory for reactions (MQDTR), as outlined in Ref. [12], with important motivations and ingredients that came before it [5,16–19], offers a different perspective o ...
... conventional approach to a few simple systems such as D + H2 , with little hope for more complex systems. The multichannel quantum-defect theory for reactions (MQDTR), as outlined in Ref. [12], with important motivations and ingredients that came before it [5,16–19], offers a different perspective o ...
BLIND QUANTUM COMPUTATION 1. Introduction and Background
... can only observe a maximally mixed state, since he has no knowledge of which Pauli operators have been applied. If Bob subsequently applies some operation U (such as X ⊗n or Z ⊗n ), then there is a known commutation relation with the Pauli operators. Therefore, when Bob returns the modified state ba ...
... can only observe a maximally mixed state, since he has no knowledge of which Pauli operators have been applied. If Bob subsequently applies some operation U (such as X ⊗n or Z ⊗n ), then there is a known commutation relation with the Pauli operators. Therefore, when Bob returns the modified state ba ...
Quantum key distribution
Quantum key distribution (QKD) uses quantum mechanics to guarantee secure communication. It enables two parties to produce a shared random secret key known only to them, which can then be used to encrypt and decrypt messages. It is often incorrectly called quantum cryptography, as it is the most well known example of the group of quantum cryptographic tasks.An important and unique property of quantum key distribution is the ability of the two communicating users to detect the presence of any third party trying to gain knowledge of the key. This results from a fundamental aspect of quantum mechanics: the process of measuring a quantum system in general disturbs the system. A third party trying to eavesdrop on the key must in some way measure it, thus introducing detectable anomalies. By using quantum superpositions or quantum entanglement and transmitting information in quantum states, a communication system can be implemented which detects eavesdropping. If the level of eavesdropping is below a certain threshold, a key can be produced that is guaranteed to be secure (i.e. the eavesdropper has no information about it), otherwise no secure key is possible and communication is aborted.The security of encryption that uses quantum key distribution relies on the foundations of quantum mechanics, in contrast to traditional public key cryptography which relies on the computational difficulty of certain mathematical functions, and cannot provide any indication of eavesdropping at any point in the communication process, or any mathematical proof as to the actual complexity of reversing the one-way functions used. QKD has provable security based on information theory, and forward secrecy.Quantum key distribution is only used to produce and distribute a key, not to transmit any message data. This key can then be used with any chosen encryption algorithm to encrypt (and decrypt) a message, which can then be transmitted over a standard communication channel. The algorithm most commonly associated with QKD is the one-time pad, as it is provably secure when used with a secret, random key. In real world situations, it is often also used with encryption using symmetric key algorithms like the Advanced Encryption Standard algorithm. In the case of QKD this comparison is based on the assumption of perfect single-photon sources and detectors, that cannot be easily implemented.