Lecture 11 Operating Systems • Free - VU LMS
... An important part of an RTOS is managing the resources of the computer so that a particular operation executes in precisely the same amount of time every time it ...
... An important part of an RTOS is managing the resources of the computer so that a particular operation executes in precisely the same amount of time every time it ...
Unit OS2: Operating Systems Principles
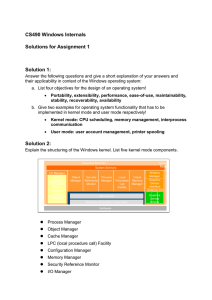
... Explain why Windows NT 4 move windows manager and graphics services from running in the context of the Windows Subsystem process to a set of callable services running in kernel mode. The primary reason for this shift was to improve overall system performance. Having a separate server process that co ...
... Explain why Windows NT 4 move windows manager and graphics services from running in the context of the Windows Subsystem process to a set of callable services running in kernel mode. The primary reason for this shift was to improve overall system performance. Having a separate server process that co ...
presentation6
... Client tools must be installed first, but the link can run with very little bandwidth possible to remotely manage a server thousands of miles away using a phone ...
... Client tools must be installed first, but the link can run with very little bandwidth possible to remotely manage a server thousands of miles away using a phone ...
Windows 2000 OS Introduction
... variations – Introduce key Windows 2000 concepts such as the Win32 API, processes, threads, virtual memory, kernel mode and user mode – Introduce tools that can be used to examine Windows 2000 internal behaviour ...
... variations – Introduce key Windows 2000 concepts such as the Win32 API, processes, threads, virtual memory, kernel mode and user mode – Introduce tools that can be used to examine Windows 2000 internal behaviour ...
download
... variations – Introduce key Windows 2000 concepts such as the Win32 API, processes, threads, virtual memory, kernel mode and user mode – Introduce tools that can be used to examine Windows 2000 internal behaviour ...
... variations – Introduce key Windows 2000 concepts such as the Win32 API, processes, threads, virtual memory, kernel mode and user mode – Introduce tools that can be used to examine Windows 2000 internal behaviour ...
A+ Guide to Managing and Maintaining your PC, 6e
... – 32 bit, same as vista – 64 bit, considerably more, almost double. – 2Gb ram min, 20 Gb hd space min. ...
... – 32 bit, same as vista – 64 bit, considerably more, almost double. – 2Gb ram min, 20 Gb hd space min. ...
evolution of operating systems
... ¾ A protocol originally developed by Sun Microsystems ¾ Allows a user on a client computer to access files over a network as if the they were present on his local disks ¾ The term "network file system“ is often used as a generic term for remotely-accessed file systems ...
... ¾ A protocol originally developed by Sun Microsystems ¾ Allows a user on a client computer to access files over a network as if the they were present on his local disks ¾ The term "network file system“ is often used as a generic term for remotely-accessed file systems ...
Device Drivers - EMU CMPE Home Page
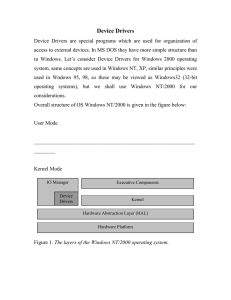
... Device Drivers Device Drivers are special programs which are used for organization of access to external devices. In MS DOS they have more simple structure than in Windows. Let’s consider Device Drivers for Windows 2000 operating system, same concepts are used in Windows NT, XP, similar principles w ...
... Device Drivers Device Drivers are special programs which are used for organization of access to external devices. In MS DOS they have more simple structure than in Windows. Let’s consider Device Drivers for Windows 2000 operating system, same concepts are used in Windows NT, XP, similar principles w ...
A+ Guide to Managing and Maintaining your PC, 6e
... – Adds advanced security, such as Windows Firewall ...
... – Adds advanced security, such as Windows Firewall ...
iWave`s Smarter Medical Devices with Windows Embedded
... systems, the tools and innovative technologies to create consumer, enterprise and medical devices differentiated by an immersive user interface, a rich browsing experience, and a unique connection to Windows PCs, servers, and devices. These supports all four major CPU architectures namely ARM, MIPS, ...
... systems, the tools and innovative technologies to create consumer, enterprise and medical devices differentiated by an immersive user interface, a rich browsing experience, and a unique connection to Windows PCs, servers, and devices. These supports all four major CPU architectures namely ARM, MIPS, ...
Operating Systems
... advantage of the computer's resources, simultaneously • The OS must make sure that the requirements of the various users are balanced, and that the programs they are using each have sufficient and separate resources so that a problem with one user doesn't affect any of the other users • Examples: Li ...
... advantage of the computer's resources, simultaneously • The OS must make sure that the requirements of the various users are balanced, and that the programs they are using each have sufficient and separate resources so that a problem with one user doesn't affect any of the other users • Examples: Li ...
Operating Systems - Glyndwr University
... When the File and Printer Sharing Service is enabled, users on other computers on the network can connect to shared folders and printers. Users connected to those shared resources are not actually utilising the CPU or memory of the computer housing the shares. ...
... When the File and Printer Sharing Service is enabled, users on other computers on the network can connect to shared folders and printers. Users connected to those shared resources are not actually utilising the CPU or memory of the computer housing the shares. ...
Windows NT Operating System
... because each one resides in a separate process whose memory is protected from other processes by the NT executive’s virtual memory system. They communicate with each other by passing messages. • The NT executive is capable of supporting any number of server processes. The servers give the NT executi ...
... because each one resides in a separate process whose memory is protected from other processes by the NT executive’s virtual memory system. They communicate with each other by passing messages. • The NT executive is capable of supporting any number of server processes. The servers give the NT executi ...
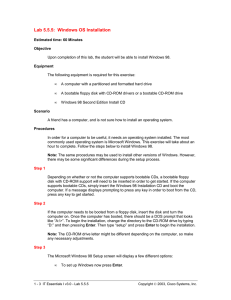
Lab 5.5.5: Windows OS Installation
... A friend has a computer, and is not sure how to install an operating system. Procedures In order for a computer to be useful, it needs an operating system installed. The most commonly used operating system is Microsoft Windows. This exercise will take about an hour to complete. Follow the steps belo ...
... A friend has a computer, and is not sure how to install an operating system. Procedures In order for a computer to be useful, it needs an operating system installed. The most commonly used operating system is Microsoft Windows. This exercise will take about an hour to complete. Follow the steps belo ...
Windows Kernel Internals Overview
... Most code written to work correctly under normal conditions Security design issues are subtle, particularly w.r.t. DoS Constantly evolving threats: Stack-buffer overruns, Heap overruns, Format string overruns One byte overruns, Integer overflows © Microsoft Corporation 2004 ...
... Most code written to work correctly under normal conditions Security design issues are subtle, particularly w.r.t. DoS Constantly evolving threats: Stack-buffer overruns, Heap overruns, Format string overruns One byte overruns, Integer overflows © Microsoft Corporation 2004 ...
Windows Kernel Internals Overview
... Most code written to work correctly under normal conditions Security design issues are subtle, particularly w.r.t. DoS Constantly evolving threats: Stack-buffer overruns, Heap overruns, Format string overruns One byte overruns, Integer overflows © Microsoft Corporation 2004 ...
... Most code written to work correctly under normal conditions Security design issues are subtle, particularly w.r.t. DoS Constantly evolving threats: Stack-buffer overruns, Heap overruns, Format string overruns One byte overruns, Integer overflows © Microsoft Corporation 2004 ...
HomeLab: Shared infrastructure for home technology field studies
... • Unmanaged homes (DIYers) • Homes can volunteer to participate in one or more experiments that different groups are running. ...
... • Unmanaged homes (DIYers) • Homes can volunteer to participate in one or more experiments that different groups are running. ...
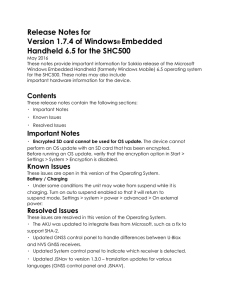
SHC500 OS 1.7.4 Release Notes
... May 2016 These notes provide important information for Sokkia release of the Microsoft Windows Embedded Handheld (formerly Windows Mobile) 6.5 operating system for the SHC500. These notes may also include important hardware information for the device. ...
... May 2016 These notes provide important information for Sokkia release of the Microsoft Windows Embedded Handheld (formerly Windows Mobile) 6.5 operating system for the SHC500. These notes may also include important hardware information for the device. ...
Unit OS1: The Evolution of Operating Systems
... These materials are part of the Windows Operating System Internals Curriculum Development Kit, developed by David A. Solomon and Mark E. Russinovich with Andreas Polze Microsoft has licensed these materials from David Solomon Expert Seminars, Inc. for distribution to academic organizations solely fo ...
... These materials are part of the Windows Operating System Internals Curriculum Development Kit, developed by David A. Solomon and Mark E. Russinovich with Andreas Polze Microsoft has licensed these materials from David Solomon Expert Seminars, Inc. for distribution to academic organizations solely fo ...
Export As PDF - Macrium KB
... You will see this if you are using 64bit Windows Vista or later and you have injected an unsigned driver. Reboot, hitting F8 to get the windows boot options menu. Chose the allow unsigned drivers option and Windows should complete booting. Locate signed drivers from your hardware vendor and either r ...
... You will see this if you are using 64bit Windows Vista or later and you have injected an unsigned driver. Reboot, hitting F8 to get the windows boot options menu. Chose the allow unsigned drivers option and Windows should complete booting. Locate signed drivers from your hardware vendor and either r ...
Introduction to the Windows Operating System
... hardware can understand. It links all different parts of your computer system together. • Most computers come from the factory with an operating system pre-installed. • The Windows OS is called a graphical user interface (GUI) because it uses pictures (icons) to help you communicate with the compute ...
... hardware can understand. It links all different parts of your computer system together. • Most computers come from the factory with an operating system pre-installed. • The Windows OS is called a graphical user interface (GUI) because it uses pictures (icons) to help you communicate with the compute ...
1. Introduction about operating system. 2. What is 32 bit
... Type your product key in the text-box and click Next. You can also skip this step and simply click Next if you want to type the product key later. Windows will run only for 30 days if you do that. ...
... Type your product key in the text-box and click Next. You can also skip this step and simply click Next if you want to type the product key later. Windows will run only for 30 days if you do that. ...
Booting process is in progress
... Type your product key in the text-box and click Next. You can also skip this step and simply click Next if you want to type the product key later. Windows will run only for 30 days if you do that. ...
... Type your product key in the text-box and click Next. You can also skip this step and simply click Next if you want to type the product key later. Windows will run only for 30 days if you do that. ...
Wally Mead - ConfigMgr 2012 SP1 Slidedeck - November
... • For clients, securely save/restore user state and settings (locally or on a file server) ...
... • For clients, securely save/restore user state and settings (locally or on a file server) ...
Operating System and Computer Security
... Linux becomes more popular, but only for advanced users and in server market. Macintosh’s market penetration more based on hardware appeal rather than software ...
... Linux becomes more popular, but only for advanced users and in server market. Macintosh’s market penetration more based on hardware appeal rather than software ...
Windows Phone 8.1
Windows Phone 8.1, rolled out at Microsoft's Build Conference in San Francisco, California, on April 2, 2014, is the third generation of Microsoft's Windows Phone mobile operating system, succeeding Windows Phone 8. It was released in final form to Windows Phone developers on April 14, 2014 and reached general availability on July 15, 2014. All Windows Phones running Windows Phone 8 will be upgraded to Windows Phone 8.1, with release dependent on carrier rollout dates.Windows Phone 8.1 is also the last version that will be under the Windows Phone brand name and will be succeeded by Windows 10 Mobile. Most Windows Phone 8.1 devices will be capable of being upgraded to Windows 10 Mobile, subject to device compatibility.