(1) OS: Operating System
... Directory handling and navigation (mkdir, rmdir,pwd and cd) The Path variable - Absolute and relative pathnames – The directories – Creating - Viewing (cat) - copying (cp) - renaming (mv) and deleting (rm) files - Listing files(ls) - Viewing through pg - tail and head command. File Attributes: Struc ...
... Directory handling and navigation (mkdir, rmdir,pwd and cd) The Path variable - Absolute and relative pathnames – The directories – Creating - Viewing (cat) - copying (cp) - renaming (mv) and deleting (rm) files - Listing files(ls) - Viewing through pg - tail and head command. File Attributes: Struc ...
lect_1
... Creation and deletion of user and system processes. Suspension and resumption of processes. A mechanism for process synchronization. A mechanism for process communication. A mechanism for deadlock handling. ...
... Creation and deletion of user and system processes. Suspension and resumption of processes. A mechanism for process synchronization. A mechanism for process communication. A mechanism for deadlock handling. ...
Operating Systems
... It should point out that the operating system handles more than one process at a time. This is called multi-tasking. Therefore, an operating system always needs to frequent update the status of many tasks and their related information. The CPU needs to swap from one process to another. Even when you ...
... It should point out that the operating system handles more than one process at a time. This is called multi-tasking. Therefore, an operating system always needs to frequent update the status of many tasks and their related information. The CPU needs to swap from one process to another. Even when you ...
Language Based Operating Systems
... segmented memory models. Hardware memory controllers (MMUs) and protection was embedded within CPUs. With the advent of 32-bit computing, memory protection schemes were also implemented in hardware. The flat memory model was adopted. Monolithic kernels were (and still are) the norm. These schemes su ...
... segmented memory models. Hardware memory controllers (MMUs) and protection was embedded within CPUs. With the advent of 32-bit computing, memory protection schemes were also implemented in hardware. The flat memory model was adopted. Monolithic kernels were (and still are) the norm. These schemes su ...
OS/2 API
... or until the program specifically requests the operating system to link dynamically to a dynamic link library (DLL). •Two types of dynamic linking - load-time dynamic linking, and run-time dynamic linking. •There are two executable modes in OS/2 environment: EXE modules for programs and DLL modules ...
... or until the program specifically requests the operating system to link dynamically to a dynamic link library (DLL). •Two types of dynamic linking - load-time dynamic linking, and run-time dynamic linking. •There are two executable modes in OS/2 environment: EXE modules for programs and DLL modules ...
ppt
... to assure exclusivity Interposition on all DMA requests allows to share disk and memory resources among virtual machines and allows VMs to communicate with each other ...
... to assure exclusivity Interposition on all DMA requests allows to share disk and memory resources among virtual machines and allows VMs to communicate with each other ...
Tools: Compilers and Operating Systems
... knowledge of the state of the parallel machine. Their primary goal is to integrate the computing resources and processors into one unified, cohesive system. In order of increasing complexity: Operating systems for the parallel architectures can be classified into one of three categories: 1. Simple m ...
... knowledge of the state of the parallel machine. Their primary goal is to integrate the computing resources and processors into one unified, cohesive system. In order of increasing complexity: Operating systems for the parallel architectures can be classified into one of three categories: 1. Simple m ...
Introduction to Operating Systems - Seneca
... It has become a standard on which many other operating systems are modelled We will be using a command-line interface to communicate with UNIX ...
... It has become a standard on which many other operating systems are modelled We will be using a command-line interface to communicate with UNIX ...
System Programs - Bilkent University Computer Engineering
... • In some cases, may be more parameters than registers – 2) Parameters stored in a block, or table, in memory, and address of block passed as a parameter in a register – 3) Parameters placed, or pushed, onto the stack by the program and popped off the stack by the operating system Last two methods d ...
... • In some cases, may be more parameters than registers – 2) Parameters stored in a block, or table, in memory, and address of block passed as a parameter in a register – 3) Parameters placed, or pushed, onto the stack by the program and popped off the stack by the operating system Last two methods d ...
COS 318: Operating Systems OS Structures and System Calls
... Allocates “pages” with hardware protection Allocates a big chunk (many pages) to library Does not care about small allocs ...
... Allocates “pages” with hardware protection Allocates a big chunk (many pages) to library Does not care about small allocs ...
oslecture2old
... Device controller transfers blocks of data from buffer storage directly to main memory without CPU ...
... Device controller transfers blocks of data from buffer storage directly to main memory without CPU ...
A Reflective Middleware Framework for Communication in
... Device controller transfers blocks of data from buffer storage directly to main memory without CPU ...
... Device controller transfers blocks of data from buffer storage directly to main memory without CPU ...
ch2
... ensure correct and consistent computing • Debugging facilities can greatly enhance the user’s and programmer’s abilities to efficiently use the system ...
... ensure correct and consistent computing • Debugging facilities can greatly enhance the user’s and programmer’s abilities to efficiently use the system ...
Introduction to Linux/Unix
... Output can be redirected to other commands via a pipe “|” Eg. 1. If the output of a command is longer than the screen size, you can pipe it to less or more so that one screen full can be viewed at a time ls –l | more Eg. 2. If you want to peruse a many concatenated documents spanning more than one s ...
... Output can be redirected to other commands via a pipe “|” Eg. 1. If the output of a command is longer than the screen size, you can pipe it to less or more so that one screen full can be viewed at a time ls –l | more Eg. 2. If you want to peruse a many concatenated documents spanning more than one s ...
ITS 225 (Operating Systems) Lecture Notes
... Protection architecture: with resource sharing, processes and their data must be protected from other processes. Also, errors detected by hardware (e.g. divide by 0) should not crash the system. Instead trap to the kernel: – Kernel logs an error message, dumps process memory, and so on. – Kernel fre ...
... Protection architecture: with resource sharing, processes and their data must be protected from other processes. Also, errors detected by hardware (e.g. divide by 0) should not crash the system. Instead trap to the kernel: – Kernel logs an error message, dumps process memory, and so on. – Kernel fre ...
Run Standard Diagnostic Tests
... system could not find a bootable device; the most likely cause is the hard disk drive. Things to consider: 1. Missing boot files — they may have been deleted by the user. 2. A virus has caused damage to the boot files or has corrupted the file system or Master Boot Record (MBR). 3. A common mistake ...
... system could not find a bootable device; the most likely cause is the hard disk drive. Things to consider: 1. Missing boot files — they may have been deleted by the user. 2. A virus has caused damage to the boot files or has corrupted the file system or Master Boot Record (MBR). 3. A common mistake ...
Operating System: A Software Engineering Perspective
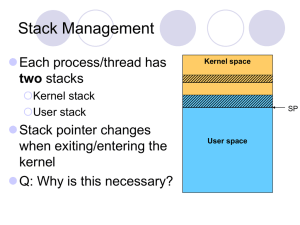
... The user stack pointer is under the control of the (untrusted) application. A buggy or malicious application could set the stack pointer to a bogus value For example, a nonexistent address or an address inside the kernel ...
... The user stack pointer is under the control of the (untrusted) application. A buggy or malicious application could set the stack pointer to a bogus value For example, a nonexistent address or an address inside the kernel ...
PDF
... m Every programmer did not write code to manage each device m Each application when compiled contained the OS m Load into memory and execute • By who? People = Operators • How? By mechanical switches at first, then punch cards ...
... m Every programmer did not write code to manage each device m Each application when compiled contained the OS m Load into memory and execute • By who? People = Operators • How? By mechanical switches at first, then punch cards ...
Introduction
... Debugging facilities can greatly enhance the user’s and programmer’s abilities to efficiently use the system ...
... Debugging facilities can greatly enhance the user’s and programmer’s abilities to efficiently use the system ...
Intro - Stanford Secure Computer Systems Group
... Please, please, please turn in working code, or no credit - Remaining 50% based on design, outlined in document ...
... Please, please, please turn in working code, or no credit - Remaining 50% based on design, outlined in document ...
OS Components and Structure
... process that handles interpretation of user input commands from keyboard (or script files) on some systems, command interpreter is a standard part of the OS on others, it’s simply a non-privileged process that interfaces to the user, permitting replacement of interpreter with others on others, there ...
... process that handles interpretation of user input commands from keyboard (or script files) on some systems, command interpreter is a standard part of the OS on others, it’s simply a non-privileged process that interfaces to the user, permitting replacement of interpreter with others on others, there ...
Operating System
... One set of services provides functions that are helpful to the user. Another set of services for ensuring the efficient operation of the system itself. Systems with multiple users can gain efficiency by sharing the computer resources among the users. ...
... One set of services provides functions that are helpful to the user. Another set of services for ensuring the efficient operation of the system itself. Systems with multiple users can gain efficiency by sharing the computer resources among the users. ...
Overview of Operating Systems
... ❚ Some operating systems do not have well-defined structures. Often, they started as simple systems and grew beyond their original scope. ❚ MS-DOS – written to provide the most functionality in the least space Ø not divided into modules Ø Although MS-DOS has some structure, its interfaces and le ...
... ❚ Some operating systems do not have well-defined structures. Often, they started as simple systems and grew beyond their original scope. ❚ MS-DOS – written to provide the most functionality in the least space Ø not divided into modules Ø Although MS-DOS has some structure, its interfaces and le ...
Module 3: Operating
... System development is done on the virtual machine, instead of on a physical machine and so does not disrupt normal system operation. The virtual machine concept is difficult to implement due to the effort required to provide an exact duplicate to the underlying machine. ...
... System development is done on the virtual machine, instead of on a physical machine and so does not disrupt normal system operation. The virtual machine concept is difficult to implement due to the effort required to provide an exact duplicate to the underlying machine. ...
Acorn MOS

Acorn's Machine Operating System (MOS) or OS was a computer operating system used in the Acorn BBC computer range. It included support for four-channel sound and graphics, file system abstraction, and digital and analogue I/O including a daisy-chained fast expansion bus. The implementation was single-tasking, monolithic and non-reentrant.Versions 0.10 to 1.20 were used on the BBC Micro, version 1.00 on the Electron, version 2 was used on the B+, and versions 3 to 5 were used in the BBC Master Series range.The final BBC computer, the BBC A3000, was 32-bit and ran RISC OS. Its operating system used portions of the Acorn MOS architecture and shared a number of characteristics (commands, VDU system) with the earlier 8-bit MOS.Versions 0 and 1 of the MOS were 16KiB in size, written in 6502 machine code, and held in ROM on the motherboard. The upper quarter of the 16-bit address space (0xC000 to 0xFFFF) is reserved for its ROM code and I/O space.Versions 2 to 5 were still restricted to a 16KiB address space but managed to hold more code and hence more complex routines, partly because of the alternative 65C102 CPU with its denser instruction set plus the careful use of paging.