FILE
... 2. Unix can be ported to any CPU * (with C**) 3. Unix can talk with any HW(running UNIX) ...
... 2. Unix can be ported to any CPU * (with C**) 3. Unix can talk with any HW(running UNIX) ...
Chapter 8 Input/Output
... • This type of “device writes to or reads from memory” interface • Allows large amounts of data to move without intervention from the processor (for example, an entire disk block) • Status register changes upon completion • Network interfaces also use DMA • Used by all high-speed, high-performance d ...
... • This type of “device writes to or reads from memory” interface • Allows large amounts of data to move without intervention from the processor (for example, an entire disk block) • Status register changes upon completion • Network interfaces also use DMA • Used by all high-speed, high-performance d ...
OS_Structure
... • Each executable unit of an OS may be restricted to making use of other program and data units only in limited ways. • This technique often results in a structure based on levels, in which a few components control critical hardware resources and provide essential services. Other components access t ...
... • Each executable unit of an OS may be restricted to making use of other program and data units only in limited ways. • This technique often results in a structure based on levels, in which a few components control critical hardware resources and provide essential services. Other components access t ...
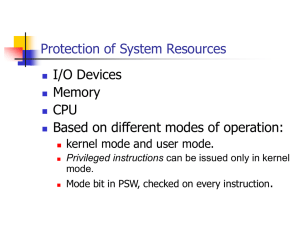
Protection of System Resources
... Keep user from monopolizing CPU. Ensure OS regains control of CPU. ...
... Keep user from monopolizing CPU. Ensure OS regains control of CPU. ...
PowerPoint Presentation - Interfaces By: Ben Griffin and
... visual prompt by typing in a command on a specified line, receives a response back from the system, and then enters another command, and so forth. The MS-DOS Prompt application in a Windows operating system is an example of the provision of a command line interface. Today, most users prefer the grap ...
... visual prompt by typing in a command on a specified line, receives a response back from the system, and then enters another command, and so forth. The MS-DOS Prompt application in a Windows operating system is an example of the provision of a command line interface. Today, most users prefer the grap ...
Chap-2-Architecture
... – Can be moved from one place to another – It considers even directories and devices as a single file system The Process is an entity, name given to a file wen its executed as a program – IT also belongs to a separate hierarchical tree structure ...
... – Can be moved from one place to another – It considers even directories and devices as a single file system The Process is an entity, name given to a file wen its executed as a program – IT also belongs to a separate hierarchical tree structure ...
Microsoft`s Disk Operating System CS-550
... Beginning with version 2 of MS-DOS, the operating system began supporting dynamic allocation, modification, and release of main memory blocks. The amount of memory allocated depended on several factors. Significantly, the language used to write an application is a determining factor in the ability ...
... Beginning with version 2 of MS-DOS, the operating system began supporting dynamic allocation, modification, and release of main memory blocks. The amount of memory allocated depended on several factors. Significantly, the language used to write an application is a determining factor in the ability ...
PDF
... into the CPU in order to be executed m To access memory, address placed in memory address register and command register written m Range of memory addresses? Size of data register? ...
... into the CPU in order to be executed m To access memory, address placed in memory address register and command register written m Range of memory addresses? Size of data register? ...
system call - efreidoc.fr
... As we saw last week in a operating system programs are not allowed direct access to any of the resources except CPU and memory and even then the use has limits placed on it. Thus 1. OS handles requests from programs for various resources to do things e.g. input or output something and enforces the l ...
... As we saw last week in a operating system programs are not allowed direct access to any of the resources except CPU and memory and even then the use has limits placed on it. Thus 1. OS handles requests from programs for various resources to do things e.g. input or output something and enforces the l ...
operating systems structures
... I/O Operations: A running program may require I/O, which may involve a file or an I/O device. For efficiency and protection user usually cannot control I/O devices directly. The OS provides a means to do I/O. ƒ File System Manipulation: Programs need to read, write files. Also they should be able to ...
... I/O Operations: A running program may require I/O, which may involve a file or an I/O device. For efficiency and protection user usually cannot control I/O devices directly. The OS provides a means to do I/O. ƒ File System Manipulation: Programs need to read, write files. Also they should be able to ...
Lesson 1 Communicating with the System - people
... platform, functionally rich set of programs. It Controls traditional computer system functions. Primarily Green Screen/text-based presentation iSeries Model 820 supports Logical Partitioning ...
... platform, functionally rich set of programs. It Controls traditional computer system functions. Primarily Green Screen/text-based presentation iSeries Model 820 supports Logical Partitioning ...
Slides(PowerPoint)
... their code, data and stack The total amount of memory used by currently running programs usually exceed the available main memory Solution: paging Temporarily unused pages are stored on disk (swapped out) When they are needed again, they are brought back into the memory (swapped in) OS Spring’03 ...
... their code, data and stack The total amount of memory used by currently running programs usually exceed the available main memory Solution: paging Temporarily unused pages are stored on disk (swapped out) When they are needed again, they are brought back into the memory (swapped in) OS Spring’03 ...
1: Welcome and Overview COM S 414
... functional units to carry out tasks • PC = program counter contains memory address of instruction being processed • IR – instruction register – copy of the current instruction ...
... functional units to carry out tasks • PC = program counter contains memory address of instruction being processed • IR – instruction register – copy of the current instruction ...
OPERATING SYSTEM
... Timesharing (multitasking) is logical extension in which CPU switches jobs so frequently that users can interact with each job while it is running, creating interactive computing Response time should be < 1 second Each user has at least one program executing in memory process If several job ...
... Timesharing (multitasking) is logical extension in which CPU switches jobs so frequently that users can interact with each job while it is running, creating interactive computing Response time should be < 1 second Each user has at least one program executing in memory process If several job ...
Operating System
... Ability to use GNU/Linux operating system for coding, compile, execute and test C programming in simulating issues in Operating System. Understand the analysis of proceses, file management, processor scheduler and memory management Develop life long learning attitude within oneself ...
... Ability to use GNU/Linux operating system for coding, compile, execute and test C programming in simulating issues in Operating System. Understand the analysis of proceses, file management, processor scheduler and memory management Develop life long learning attitude within oneself ...
Chapter 6 An Introduction to System Software
... In most OS, access control is handled by requiring a user to enter a legal user name and password before any other requests are accepted . The password file is maintained by superuser. ...
... In most OS, access control is handled by requiring a user to enter a legal user name and password before any other requests are accepted . The password file is maintained by superuser. ...
Chapter 6 An Introduction to System Software and
... In most OS, access control is handled by requiring a user to enter a legal user name and password before any other requests are accepted . The password file is maintained by superuser. ...
... In most OS, access control is handled by requiring a user to enter a legal user name and password before any other requests are accepted . The password file is maintained by superuser. ...
Frequently Asked Questions - Operating System Concepts
... 9. Explain Memory Partitioning, Paging, Segmentation. 10. Explain Scheduling. 11. Operating System Security. 12. What is Semaphore? 13. Explain the following file systems : NTFS, Macintosh(HPFS), FAT . 14. What are the different process states? 15. What is Marshalling? 16. Define and explain COM? 17 ...
... 9. Explain Memory Partitioning, Paging, Segmentation. 10. Explain Scheduling. 11. Operating System Security. 12. What is Semaphore? 13. Explain the following file systems : NTFS, Macintosh(HPFS), FAT . 14. What are the different process states? 15. What is Marshalling? 16. Define and explain COM? 17 ...
Protection in General-Purpose Operating Systems
... This technique is not wide spread because of the market consideration (compatible). ...
... This technique is not wide spread because of the market consideration (compatible). ...
Chapter 3: Operating
... does not allow system calls to be made directly, because a system call is specific to an OS and results in platform-specific code. 本土 However, Java can call the “native” method, written in another language such as C or C++, to make the system call. ...
... does not allow system calls to be made directly, because a system call is specific to an OS and results in platform-specific code. 本土 However, Java can call the “native” method, written in another language such as C or C++, to make the system call. ...
390aLecture01_12wi
... • shell: An interactive program that uses user input to manage the execution of other programs. bash : the default shell program on most Linux/Unix systems ...
... • shell: An interactive program that uses user input to manage the execution of other programs. bash : the default shell program on most Linux/Unix systems ...
Summary for chapter 2 OPERATING SYSTEM nAJWA kNEFATI
... The functions that make up an API typically invoke the actual system calls . EX: Function CreateProcess () (create a new process) actually invokes the NTCreateProcess () system call in the Windows kernel. Why would an application programmer prefer programming according to an API rather than invoking ...
... The functions that make up an API typically invoke the actual system calls . EX: Function CreateProcess () (create a new process) actually invokes the NTCreateProcess () system call in the Windows kernel. Why would an application programmer prefer programming according to an API rather than invoking ...
PPT - CSE Home
... • CSE391 Collection of tools and topics not specifically addressed in other courses that CSE majors should know CSE 351 may be the first course you take that uses Linux Course Topics: Linix command line interface (CLI), Shell scripting, compilation tools (makefiles), version control… Credit ...
... • CSE391 Collection of tools and topics not specifically addressed in other courses that CSE majors should know CSE 351 may be the first course you take that uses Linux Course Topics: Linix command line interface (CLI), Shell scripting, compilation tools (makefiles), version control… Credit ...
Quiz 1 - FSU Computer Science
... 21. The name of the Unix shell command that performs the function to change access permissions called ______________ ...
... 21. The name of the Unix shell command that performs the function to change access permissions called ______________ ...
Acorn MOS

Acorn's Machine Operating System (MOS) or OS was a computer operating system used in the Acorn BBC computer range. It included support for four-channel sound and graphics, file system abstraction, and digital and analogue I/O including a daisy-chained fast expansion bus. The implementation was single-tasking, monolithic and non-reentrant.Versions 0.10 to 1.20 were used on the BBC Micro, version 1.00 on the Electron, version 2 was used on the B+, and versions 3 to 5 were used in the BBC Master Series range.The final BBC computer, the BBC A3000, was 32-bit and ran RISC OS. Its operating system used portions of the Acorn MOS architecture and shared a number of characteristics (commands, VDU system) with the earlier 8-bit MOS.Versions 0 and 1 of the MOS were 16KiB in size, written in 6502 machine code, and held in ROM on the motherboard. The upper quarter of the 16-bit address space (0xC000 to 0xFFFF) is reserved for its ROM code and I/O space.Versions 2 to 5 were still restricted to a 16KiB address space but managed to hold more code and hence more complex routines, partly because of the alternative 65C102 CPU with its denser instruction set plus the careful use of paging.