Chapter 7: Relational Database Design
... ©Silberschatz, Korth and Sudarshan See www.db-book.com for conditions on re-use ...
... ©Silberschatz, Korth and Sudarshan See www.db-book.com for conditions on re-use ...
int i
... If the initialization, condition and/or update parts are long, place each on a separate line for clarity. for ( initialization; ...
... If the initialization, condition and/or update parts are long, place each on a separate line for clarity. for ( initialization; ...
Ders 6. Problemler
... 19. Arrays can be declared to hold only primitive data types. Ans: False. An array can be declared to hold almost any data type. 20. Arrays are only designed to hold primitive data types and Strings. Ans: False. Arrays may contain variables of any type. 21. Constants are declared using keyword a) st ...
... 19. Arrays can be declared to hold only primitive data types. Ans: False. An array can be declared to hold almost any data type. 20. Arrays are only designed to hold primitive data types and Strings. Ans: False. Arrays may contain variables of any type. 21. Constants are declared using keyword a) st ...
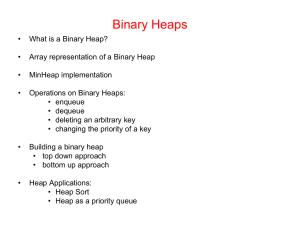
binary heap - K.f.u.p.m ocw
... A binary heap is a complete binary tree with one (or both) of the following heap order properties: • MinHeap property: Each node must have a key that is less or equal to the key of each of its children. • MaxHeap property: Each node must have a key that is greater or equal to the key of each of its ...
... A binary heap is a complete binary tree with one (or both) of the following heap order properties: • MinHeap property: Each node must have a key that is less or equal to the key of each of its children. • MaxHeap property: Each node must have a key that is greater or equal to the key of each of its ...
Chapter 11: Indexing and Hashing
... ©Silberschatz, Korth and Sudarshan See www.db-book.com for conditions on re-use ...
... ©Silberschatz, Korth and Sudarshan See www.db-book.com for conditions on re-use ...
Database System Concepts, 5th Ed
... Leaf Nodes in B+-Trees Properties of a leaf node: For i = 1, 2, . . ., n–1, pointer Pi either points to a file record with search- ...
... Leaf Nodes in B+-Trees Properties of a leaf node: For i = 1, 2, . . ., n–1, pointer Pi either points to a file record with search- ...
Lecture Notes on Unbounded Arrays 1 Introduction
... Since we only save a constant number of tokens on each operation, in addition to the constant time the operation itself takes, we never perform more operations than a constant times the number of operations. So our claim above is true: any sequence of n operations performs at most O(n) steps. We als ...
... Since we only save a constant number of tokens on each operation, in addition to the constant time the operation itself takes, we never perform more operations than a constant times the number of operations. So our claim above is true: any sequence of n operations performs at most O(n) steps. We als ...
Concise Notes on Data Structures and Algorithms
... The Ruby Programming Language. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Review Questions. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . ...
... The Ruby Programming Language. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Review Questions. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . ...
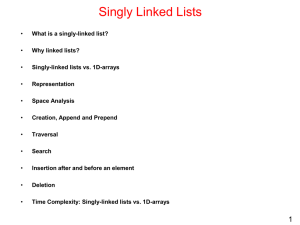
Lecture 3 Linear Data Structures
... • Array: a sequence of indexed components with the following properties: – array size is fixed at the time of array’s construction • int[] numbers = new int [10]; – array elements are placed contiguously in memory • address of any element can be calculated directly as its offset from the beginn ...
... • Array: a sequence of indexed components with the following properties: – array size is fixed at the time of array’s construction • int[] numbers = new int [10]; – array elements are placed contiguously in memory • address of any element can be calculated directly as its offset from the beginn ...
MIT 6.851 Advanced Data Structures
... Slabs that also contain slabs that span either L or R. . . . . . . . . . . . . . . . . . . 77 ...
... Slabs that also contain slabs that span either L or R. . . . . . . . . . . . . . . . . . . 77 ...
Efficiency Improvement of Narrow Range Query - CEUR
... Operations Insert, Delete and Find (or point query) are handled by algorithms of the selected R-tree variant. In the case of the Insert operation (see Algorithm 1), we must update the signature of the MBB which was changed. In this way, we must update signatures for each level of the tree from the c ...
... Operations Insert, Delete and Find (or point query) are handled by algorithms of the selected R-tree variant. In the case of the Insert operation (see Algorithm 1), we must update the signature of the MBB which was changed. In this way, we must update signatures for each level of the tree from the c ...
Starting Out with Java
... 43) A sorting algorithm is used to locate a specific item in a larger collection of data. Answer: True False 44) The binary search algorithm A) Is less efficient than the sequential search algorithm B) Will cut the portion of the array being searched in half each time the loop fails to locate the se ...
... 43) A sorting algorithm is used to locate a specific item in a larger collection of data. Answer: True False 44) The binary search algorithm A) Is less efficient than the sequential search algorithm B) Will cut the portion of the array being searched in half each time the loop fails to locate the se ...
Computational Bounds on Hierarchical Data Processing with
... hash-based authenticated dictionaries of size n incur Θ(log n) complexity. We also present a new hash-based dictionary ADS based on our skip-list structure from Section 3 and show that it has better authentication cost parameters than previous hash-based ADS constructions. Multicast Key Distributio ...
... hash-based authenticated dictionaries of size n incur Θ(log n) complexity. We also present a new hash-based dictionary ADS based on our skip-list structure from Section 3 and show that it has better authentication cost parameters than previous hash-based ADS constructions. Multicast Key Distributio ...
Online Sorted Range Reporting
... We now describe a simple solution that can be used to answer a subset of possible queries, where a query is the computation of the k smallest elements in sorted order of R(x, ℓ) or L(x, ℓ) for some node x and a level ℓ, where ℓ ≥ h(x). The solution works by precomputing answers to queries. We apply ...
... We now describe a simple solution that can be used to answer a subset of possible queries, where a query is the computation of the k smallest elements in sorted order of R(x, ℓ) or L(x, ℓ) for some node x and a level ℓ, where ℓ ≥ h(x). The solution works by precomputing answers to queries. We apply ...
Bloom filter
A Bloom filter is a space-efficient probabilistic data structure, conceived by Burton Howard Bloom in 1970, that is used to test whether an element is a member of a set. False positive matches are possible, but false negatives are not, thus a Bloom filter has a 100% recall rate. In other words, a query returns either ""possibly in set"" or ""definitely not in set"". Elements can be added to the set, but not removed (though this can be addressed with a ""counting"" filter). The more elements that are added to the set, the larger the probability of false positives.Bloom proposed the technique for applications where the amount of source data would require an impractically large amount of memory if ""conventional"" error-free hashing techniques were applied. He gave the example of a hyphenation algorithm for a dictionary of 500,000 words, out of which 90% follow simple hyphenation rules, but the remaining 10% require expensive disk accesses to retrieve specific hyphenation patterns. With sufficient core memory, an error-free hash could be used to eliminate all unnecessary disk accesses; on the other hand, with limited core memory, Bloom's technique uses a smaller hash area but still eliminates most unnecessary accesses. For example, a hash area only 15% of the size needed by an ideal error-free hash still eliminates 85% of the disk accesses, an 85–15 form of the Pareto principle (Bloom (1970)).More generally, fewer than 10 bits per element are required for a 1% false positive probability, independent of the size or number of elements in the set (Bonomi et al. (2006)).