Physical layer continued
... • User – base station – Telephone network • FDMA – Frequency division multiplexing – How to make sure that you are using this band, not that band? ...
... • User – base station – Telephone network • FDMA – Frequency division multiplexing – How to make sure that you are using this band, not that band? ...
WiMAX Protocol - London South Bank University
... diffused in broad-casting 360 degrees This limits its range and ultimately signal strength ...
... diffused in broad-casting 360 degrees This limits its range and ultimately signal strength ...
Lecture-01: Course Introduction - University of Colorado Boulder
... – Type of communication would involve many short messages ...
... – Type of communication would involve many short messages ...
Wireless data transfer – GSM
... Data transfer in GSM • The "data over cellular" bearer services are part of the Phase 2 implementation of GSM • The basic data transfer technology is called CSD (Circuit Switched Data) • A GSM network’s data transfer facility allows the digital equivalent of modem transmissions - known as data stre ...
... Data transfer in GSM • The "data over cellular" bearer services are part of the Phase 2 implementation of GSM • The basic data transfer technology is called CSD (Circuit Switched Data) • A GSM network’s data transfer facility allows the digital equivalent of modem transmissions - known as data stre ...
arubaos xsec module - SecureWirelessWorks.com
... in the form of IPsec. IPsec uses 3DES or AES encryption and can encrypt the IP packet including the source and destination IP addresses in the header. IPsec provides a commonly accepted, secure method of communication over untrusted networks since the only information left unencrypted are packet hea ...
... in the form of IPsec. IPsec uses 3DES or AES encryption and can encrypt the IP packet including the source and destination IP addresses in the header. IPsec provides a commonly accepted, secure method of communication over untrusted networks since the only information left unencrypted are packet hea ...
View
... signals to a higher level without disturbing human ears. • With wireless networks, the air medium supports the propagation of radio and light waves that travel from one point to another. ...
... signals to a higher level without disturbing human ears. • With wireless networks, the air medium supports the propagation of radio and light waves that travel from one point to another. ...
Chapter 5: Telecommunications
... • Peer-to-peer networks – Allow any computer or device to provide and request services ...
... • Peer-to-peer networks – Allow any computer or device to provide and request services ...
PowerPoint Presentation - Staffordshire University
... infrastructure Even if two people bring together laptops for a game, there will be a cable and a device to repeat the signal ...
... infrastructure Even if two people bring together laptops for a game, there will be a cable and a device to repeat the signal ...
From Analog to Digital - Multi
... Although implementing any type of new service or process co mpan ies in dat a t ra nsm i ssi on. Ana l og l i n e s , a l s o comes with a price tag, the price of passivity is much steeper referred to as “Plain Old Telephone Service” (POTS), than moving forward with new technology. For instance, tra ...
... Although implementing any type of new service or process co mpan ies in dat a t ra nsm i ssi on. Ana l og l i n e s , a l s o comes with a price tag, the price of passivity is much steeper referred to as “Plain Old Telephone Service” (POTS), than moving forward with new technology. For instance, tra ...
Convergence Technology Chapter Objectives
... Recognize physical topologies in data networks Describe Ethernet and CSMA/CD network access method Describe the different types of Ethernet access methods Describe the techniques used in Token Ring, ATM, & FDDI network access Main characteristics of network transmission methods – X.25, Fra ...
... Recognize physical topologies in data networks Describe Ethernet and CSMA/CD network access method Describe the different types of Ethernet access methods Describe the techniques used in Token Ring, ATM, & FDDI network access Main characteristics of network transmission methods – X.25, Fra ...
Master of Science (Telecommunication
... field. As the reliance of every organization network based computer systems increases so does the number and importance of System Administrators. This course is an attempt to provide a practical problem-solving approach to the field of computer and network system administration. Students will gain h ...
... field. As the reliance of every organization network based computer systems increases so does the number and importance of System Administrators. This course is an attempt to provide a practical problem-solving approach to the field of computer and network system administration. Students will gain h ...
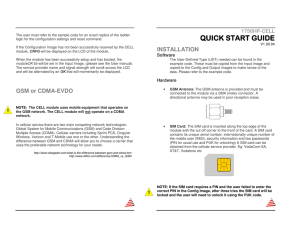
1756HP-CELL QuickStart v1.00.04
... contains its unique serial number, internationally unique number of the mobile user (IMSI), security information and two passwords (PIN for usual use and PUK for unlocking) A SIM card can be obtained from the cellular service provider. Eg. VodaCom-SA, AT&T, Vodafone etc ...
... contains its unique serial number, internationally unique number of the mobile user (IMSI), security information and two passwords (PIN for usual use and PUK for unlocking) A SIM card can be obtained from the cellular service provider. Eg. VodaCom-SA, AT&T, Vodafone etc ...
Hands-on Networking Fundamentals
... • Frequency ranges of various transmission types – AM: 535–1605 kilohertz (kHz) – FM: 88–108 megahertz (MHz) – Network: 902-928 MHz, 2.4-2.4835 GHz, 5-5.825 GHz ...
... • Frequency ranges of various transmission types – AM: 535–1605 kilohertz (kHz) – FM: 88–108 megahertz (MHz) – Network: 902-928 MHz, 2.4-2.4835 GHz, 5-5.825 GHz ...
Fiber optic cable
... broadcast by a radio tower, although this will usually not affect standard wired Ethernet networks. ...
... broadcast by a radio tower, although this will usually not affect standard wired Ethernet networks. ...
Biological Signals Communication System through the
... Our simple theoretical model has found significant coherence with simulations and with (not so idealistic) experimental setup results. The model can be used to predict the working range of capacitive coupled systems tested in controlled setup environment. Practical system showed that with 3x5x5cm tr ...
... Our simple theoretical model has found significant coherence with simulations and with (not so idealistic) experimental setup results. The model can be used to predict the working range of capacitive coupled systems tested in controlled setup environment. Practical system showed that with 3x5x5cm tr ...
How hiSky Leverages High-Throughput
... We believe that HTS is the answer to meeting the needs of heavy data users who are already covered by 4G networks – soon to be 5G networks – and need continuous communication, at reasonable rates. Recently, hiSky, an Israeli start-up revealed its newly developed Smartellite – a portable satellite te ...
... We believe that HTS is the answer to meeting the needs of heavy data users who are already covered by 4G networks – soon to be 5G networks – and need continuous communication, at reasonable rates. Recently, hiSky, an Israeli start-up revealed its newly developed Smartellite – a portable satellite te ...
Basic Concepts
... send the packet back out Complex B Made at each switch B? D? Switch A D Packet ...
... send the packet back out Complex B Made at each switch B? D? Switch A D Packet ...
CIS 1140 Network Fundamentals
... The Wireless Access Points or bridges must use non-adjacent, nonoverlapping radio channels to prevent interference from the adjacent bridge or Access Point When using multiple bridges to cover a large area, you should ensure that the channels are configured in such a way that there is no ...
... The Wireless Access Points or bridges must use non-adjacent, nonoverlapping radio channels to prevent interference from the adjacent bridge or Access Point When using multiple bridges to cover a large area, you should ensure that the channels are configured in such a way that there is no ...
What is the convergence in the field of information and
... characteristic impedance, crosstalk…)? What are the main applications of twisted pair cables? Twisted pair cable: Twisted pair cabling is a type of wiring in which two conductors of a single circuit are twisted together for the purposes of canceling out electromagnetic interference (EMI) from extern ...
... characteristic impedance, crosstalk…)? What are the main applications of twisted pair cables? Twisted pair cable: Twisted pair cabling is a type of wiring in which two conductors of a single circuit are twisted together for the purposes of canceling out electromagnetic interference (EMI) from extern ...
Ch05
... IP-based data packet switching networks to transmit voice communications. VoIP over WLANs holds tremendous potential by providing workers who are not regularly at their desks more flexibility. It can also reduce operating costs associated with use of cell phones and private radio walkie-talkie syste ...
... IP-based data packet switching networks to transmit voice communications. VoIP over WLANs holds tremendous potential by providing workers who are not regularly at their desks more flexibility. It can also reduce operating costs associated with use of cell phones and private radio walkie-talkie syste ...
Page 1 Transceiver Controls
... Squelch > The squelch control is used to mute receiver output noise when no signal is being received Channel Memory > A way to enable quick access to a favorite frequency on your transceiver Repeater Offset > The difference between the repeater’s transmit and receive frequencies Noise Blanker > Turn ...
... Squelch > The squelch control is used to mute receiver output noise when no signal is being received Channel Memory > A way to enable quick access to a favorite frequency on your transceiver Repeater Offset > The difference between the repeater’s transmit and receive frequencies Noise Blanker > Turn ...