Generations of Computers
... data used in calculations Instruction Pointer - sometimes referred to as the program counter, the pointer is responsible for retaining the memory address of the next instruction to be executed Address Registers - are used for storing the memory location of data or instructions to be ...
... data used in calculations Instruction Pointer - sometimes referred to as the program counter, the pointer is responsible for retaining the memory address of the next instruction to be executed Address Registers - are used for storing the memory location of data or instructions to be ...
DAS - Grid`5000
... - Applications can change the topology of the wide-area network, possibly even at sub-second timescale ...
... - Applications can change the topology of the wide-area network, possibly even at sub-second timescale ...
Config OS - UNM Computer Science
... ultrascale high-end computing systems based on both conventional and advanced hardware architectures and in support of diverse, current and emerging parallel programming models. • Devise and implement a prototype system that provides a framework for automatically configuring and building lightweight ...
... ultrascale high-end computing systems based on both conventional and advanced hardware architectures and in support of diverse, current and emerging parallel programming models. • Devise and implement a prototype system that provides a framework for automatically configuring and building lightweight ...
The Link Between Robots and Computers.
... the technologies of wireless communication networks make it possible to access the internet from nearly any place on the planet. The reason that you are sitting in front of a computer and learning about robots is primarily because of the advent of these technologies. While robots are not quite as co ...
... the technologies of wireless communication networks make it possible to access the internet from nearly any place on the planet. The reason that you are sitting in front of a computer and learning about robots is primarily because of the advent of these technologies. While robots are not quite as co ...
Chapter 3 - Csulb.edu
... Client-Server Architecture Defn: A server is an application program that waits for contact from another application. Defn: A client is an application program that initiates contact with a server. ...
... Client-Server Architecture Defn: A server is an application program that waits for contact from another application. Defn: A client is an application program that initiates contact with a server. ...
mpirun
... – LAM (Local Area Multicomputer) is an MPI programming environment and development system for heterogeneous computers on a network . – With a LAM/MPI , a dedicated cluster or an existing network computing infrastructure can act as a single parallel computer. – LAM/MPI is considered to be a “cluster ...
... – LAM (Local Area Multicomputer) is an MPI programming environment and development system for heterogeneous computers on a network . – With a LAM/MPI , a dedicated cluster or an existing network computing infrastructure can act as a single parallel computer. – LAM/MPI is considered to be a “cluster ...
K-means
... All of the cases involving an attorney were assigned to Cluster #4, involved much higher prior claims. Interestingly, the presence of an attorney also seems to be associated with lower claim amounts. Cluster #3 and #4 are very similar, except for gender. Cluster #1 is distinguished by a much younger ...
... All of the cases involving an attorney were assigned to Cluster #4, involved much higher prior claims. Interestingly, the presence of an attorney also seems to be associated with lower claim amounts. Cluster #3 and #4 are very similar, except for gender. Cluster #1 is distinguished by a much younger ...
FileStore - Symantec
... Directories are not supported as shares (1 share per fs) Multiple file systems can be used for home directories For regular (non home-directory) shares – User visible share is a proxy share w/ single target DFS referral – Load balancing is done by moving a VIP w/ its shares to another node For home- ...
... Directories are not supported as shares (1 share per fs) Multiple file systems can be used for home directories For regular (non home-directory) shares – User visible share is a proxy share w/ single target DFS referral – Load balancing is done by moving a VIP w/ its shares to another node For home- ...
History of Computer Science
... Magnetic tapes and disks for storage Reductions in size and heat generation Increase in processing speed and reliability Increased use of high-level languages ...
... Magnetic tapes and disks for storage Reductions in size and heat generation Increase in processing speed and reliability Increased use of high-level languages ...
CPS120 - Washtenaw Community College
... – and the operating system, which decides which programs – to run and when. Separation between Users and Hardware Computer programmers now created programs to ...
... – and the operating system, which decides which programs – to run and when. Separation between Users and Hardware Computer programmers now created programs to ...
Discrete Mathematics
... Her doctoral research work is based on Analysis and Design of Wireless ad-hoc networks with low Forwarding Index. For efficient communication between nodes, ad-hoc networks are typically grouped into clusters, where each cluster has a cluster head (or Master). Cluster head nodes are also responsible ...
... Her doctoral research work is based on Analysis and Design of Wireless ad-hoc networks with low Forwarding Index. For efficient communication between nodes, ad-hoc networks are typically grouped into clusters, where each cluster has a cluster head (or Master). Cluster head nodes are also responsible ...
ANTHONY MAIYO 22nd FEBRUARY 2013 F21/1946/2012
... This generation also saw the development of devices such as keyboards and monitors and interfaced with an operating system, which allowed the device to run many different applications at one time with a central program that, monitored the memory. ...
... This generation also saw the development of devices such as keyboards and monitors and interfaced with an operating system, which allowed the device to run many different applications at one time with a central program that, monitored the memory. ...
Inside LiveJournal`s Backend
... easy at this point; APIs already exist multiple databases per real cluster ...
... easy at this point; APIs already exist multiple databases per real cluster ...
Intro to computers
... run on another system than the original C – originally used for developing operating systems, but became very popular C++ and other object-oriented languages – enabled creation of reusable programs Java – like C++, but can be run on any computer without recompiling ...
... run on another system than the original C – originally used for developing operating systems, but became very popular C++ and other object-oriented languages – enabled creation of reusable programs Java – like C++, but can be run on any computer without recompiling ...
A parallel database system seeks to improve performance through
... A parallel database system seeks to improve performance through parallelization of various operations, such as loading data, building indexes and evaluating queries. Although data may be stored in a distributed fashion, the distribution is governed solely by performance considerations. Parallel data ...
... A parallel database system seeks to improve performance through parallelization of various operations, such as loading data, building indexes and evaluating queries. Although data may be stored in a distributed fashion, the distribution is governed solely by performance considerations. Parallel data ...
Advances in Natural and Applied Sciences
... infrastructure since, they are self – configuring networks and does not require any central administrator. Due to the unstable nature of nodes challenges occur during routing a packet from source to destination. As discussed previously the nodes are not stable in nature so the path between the nodes ...
... infrastructure since, they are self – configuring networks and does not require any central administrator. Due to the unstable nature of nodes challenges occur during routing a packet from source to destination. As discussed previously the nodes are not stable in nature so the path between the nodes ...
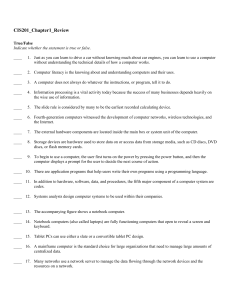
CIS201_Chapter1_Review True/False Indicate whether the
... 41. The ____________________ being used with a computer determine the tasks the computer is able to perform. 42. The progression of input, processing, output, and storage is sometimes referred to as the ____________________ cycle or the information processing cycle. 43. ____________________—technica ...
... 41. The ____________________ being used with a computer determine the tasks the computer is able to perform. 42. The progression of input, processing, output, and storage is sometimes referred to as the ____________________ cycle or the information processing cycle. 43. ____________________—technica ...
Bridging the Gap
... ~= 600 racks ! (just for the cpu blades…what about disks, comms, etc) – How do you protect the investment? @$1000/node* 50K nodes = $50,000,000 USD ...
... ~= 600 racks ! (just for the cpu blades…what about disks, comms, etc) – How do you protect the investment? @$1000/node* 50K nodes = $50,000,000 USD ...
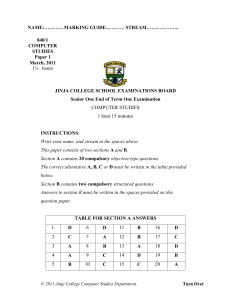
S1_43_2016-01-01-6-39
... protection, business, entertainment and education, which make a positive difference in the world. To create awareness in a learner about the developments and emerging issues concerning computing and society. To get jobs. Computer studies provides a foundation that serves as a competitive advanta ...
... protection, business, entertainment and education, which make a positive difference in the world. To create awareness in a learner about the developments and emerging issues concerning computing and society. To get jobs. Computer studies provides a foundation that serves as a competitive advanta ...
Subject Review - The CLOUDS Lab
... Microsoft (HPC Specialist) Sun (Senior Director of Grid Computing) Amazon (Architect, Amazon Cloud Computing) ...
... Microsoft (HPC Specialist) Sun (Senior Director of Grid Computing) Amazon (Architect, Amazon Cloud Computing) ...
The California Institute for Telecommunications and
... – Selects from Virtual Grid Resources – Negotiates with Resource Managers and Brokers – Executor and Monitor for DVC – Acquires and Configures – Monitors for Failures and Performance – Adapts and Reconfigures ...
... – Selects from Virtual Grid Resources – Negotiates with Resource Managers and Brokers – Executor and Monitor for DVC – Acquires and Configures – Monitors for Failures and Performance – Adapts and Reconfigures ...
A scalable file distribution and operating system installation toolkit
... has just installed. In order to avoid restarting the whole installation procedure, a status file located on the TFTP server and updated by the installation program tells the computer to perform its post-installation phase. ...
... has just installed. In order to avoid restarting the whole installation procedure, a status file located on the TFTP server and updated by the installation program tells the computer to perform its post-installation phase. ...
Computer cluster

A computer cluster consists of a set of loosely or tightly connected computers that work together so that, in many respects, they can be viewed as a single system. Unlike grid computers, computer clusters have each node set to perform the same task, controlled and scheduled by software.The components of a cluster are usually connected to each other through fast local area networks (""LAN""), with each node (computer used as a server) running its own instance of an operating system. In most circumstances, all of the nodes use the same hardware and the same operating system, although in some setups (i.e. using Open Source Cluster Application Resources (OSCAR)), different operating systems can be used on each computer, and/or different hardware.They are usually deployed to improve performance and availability over that of a single computer, while typically being much more cost-effective than single computers of comparable speed or availability.Computer clusters emerged as a result of convergence of a number of computing trends including the availability of low-cost microprocessors, high speed networks, and software for high-performance distributed computing. They have a wide range of applicability and deployment, ranging from small business clusters with a handful of nodes to some of the fastest supercomputers in the world such as IBM's Sequoia. The applications that can be done however, are nonetheless limited, since the software needs to be purpose-built per task. It is hence not possible to use computer clusters for casual computing tasks.