AMS42/84-LAN - von BMC Messsysteme GmbH
... 6.3 Using AMS42/84-LAN with NextView®4 Install the fully functional trial of the professional software NextView®4 for measurement data acquisition and processing to directly test the features and functions of the AMS42/84-LAN (installed as "iM-AD25a"). The setup program NV4 is available on the produ ...
... 6.3 Using AMS42/84-LAN with NextView®4 Install the fully functional trial of the professional software NextView®4 for measurement data acquisition and processing to directly test the features and functions of the AMS42/84-LAN (installed as "iM-AD25a"). The setup program NV4 is available on the produ ...
CAO - E
... The idea of a stored-program computer was already present in the design of J. Presper Eckert and John William Mauchly's ENIAC, but was initially omitted so the machine could be finished sooner. On June 30, 1945, before ENIAC was even completed, mathematician John von Neumann distributed the paper e ...
... The idea of a stored-program computer was already present in the design of J. Presper Eckert and John William Mauchly's ENIAC, but was initially omitted so the machine could be finished sooner. On June 30, 1945, before ENIAC was even completed, mathematician John von Neumann distributed the paper e ...
I. Ch 4 The System Unit
... very often. Data from secondary storage must be loaded into RAM before it can be used. Flash RAM (aka Flash memory) is a new type of RAM that is nonvolatile and can retain data even if power is switched off. This type of memory is more expensive are used in digital cell phones, digital cameras, and ...
... very often. Data from secondary storage must be loaded into RAM before it can be used. Flash RAM (aka Flash memory) is a new type of RAM that is nonvolatile and can retain data even if power is switched off. This type of memory is more expensive are used in digital cell phones, digital cameras, and ...
Program Method of NOR Flash
... be loaded with data. The number of locations to program cannot exceed the size of the write buffer or the operation will abort. The fifth cycle writes the first address location and data to be programmed. In case that the device supports maximum 32 words program in one programming operation, he writ ...
... be loaded with data. The number of locations to program cannot exceed the size of the write buffer or the operation will abort. The fifth cycle writes the first address location and data to be programmed. In case that the device supports maximum 32 words program in one programming operation, he writ ...
Locknetics Upgrade Project Preliminary Design Review
... • Palmtop Synchronization Software – Shall synchronize the database on the Palmtop Device with the database on the Host Computer – Shall package and send data to the IO Ports on the computer ...
... • Palmtop Synchronization Software – Shall synchronize the database on the Palmtop Device with the database on the Host Computer – Shall package and send data to the IO Ports on the computer ...
File
... were first developed in 1947 They. Transistors are most often used to regulate the flow of an electrical current and to switch electricity on and ...
... were first developed in 1947 They. Transistors are most often used to regulate the flow of an electrical current and to switch electricity on and ...
PowerPoint slides from ACMS 2007
... • We believe that our approach very much reflects the observation: • “When we look at high-quality programs, we see coherent programs that are driven and developed from within. Faculty and local administrators contribute because they have looked beyond the boundaries of conventional subject-matter a ...
... • We believe that our approach very much reflects the observation: • “When we look at high-quality programs, we see coherent programs that are driven and developed from within. Faculty and local administrators contribute because they have looked beyond the boundaries of conventional subject-matter a ...
The Future of Computing: Challenges and Opportunities
... Multithreaded Processors If the red thread requests data from main memory and this data isn't present in the cache, then this thread could stall for many CPU cycles while waiting for the data to arrive. In the meantime, however, the processor could execute the yellow thread while the red one is sta ...
... Multithreaded Processors If the red thread requests data from main memory and this data isn't present in the cache, then this thread could stall for many CPU cycles while waiting for the data to arrive. In the meantime, however, the processor could execute the yellow thread while the red one is sta ...
Part4-(CASE(EMI
... Zero-clock skew trend naturally supported by today’s design tools, but clock smearing concept for the sake of reduced RF emission to perform clock distribution must be done manually, since today’s tools do not support directly non-zero clock signal design. ...
... Zero-clock skew trend naturally supported by today’s design tools, but clock smearing concept for the sake of reduced RF emission to perform clock distribution must be done manually, since today’s tools do not support directly non-zero clock signal design. ...
Computer Organization And Architecture Srm
... temporarily. Multiple registers are needed to facilitate the operation of the CPU. Some of these registers are Two registers-MAR (Memory Address Register) and MDR (Memory Data Register) : To handle the data transfer between main memory and processor. MARHolds addresses, MDR-Holds data Instructio ...
... temporarily. Multiple registers are needed to facilitate the operation of the CPU. Some of these registers are Two registers-MAR (Memory Address Register) and MDR (Memory Data Register) : To handle the data transfer between main memory and processor. MARHolds addresses, MDR-Holds data Instructio ...
Programming and Controls Workshop
... concern is the current draw which is much lower then the speed controllers. ...
... concern is the current draw which is much lower then the speed controllers. ...
UNIT-I - CSE Department B
... hardware, software and their interconnection, and it also discusses concepts like computer types, evolution of computers, functional units, basic operations, RISC and CISC systems. ...
... hardware, software and their interconnection, and it also discusses concepts like computer types, evolution of computers, functional units, basic operations, RISC and CISC systems. ...
Chapter 1
... Although it is difficult to distinguish between the ideas belonging to computer organization and those ideas belonging to computer architecture, it is impossible to say where hardware issues end and software issues begin. Computer scientists design algorithms that usually are implemented as programs ...
... Although it is difficult to distinguish between the ideas belonging to computer organization and those ideas belonging to computer architecture, it is impossible to say where hardware issues end and software issues begin. Computer scientists design algorithms that usually are implemented as programs ...
Braun
... 1 – mathematical operators, 2 – programming structures, 3 – data acquisition functions, 4 – existing or created subVI, 5 – functions for the sinusoidal signal generation, 6 – complex mathematical functions [2] A LabVIEW application is characterized by the aspect that all the defined object in the pa ...
... 1 – mathematical operators, 2 – programming structures, 3 – data acquisition functions, 4 – existing or created subVI, 5 – functions for the sinusoidal signal generation, 6 – complex mathematical functions [2] A LabVIEW application is characterized by the aspect that all the defined object in the pa ...
Agent Architectures and Hierarchical Control, covering
... • Let T be the set of time points • A percept trace is a function from T into P, where P is the set of all possible percepts • A command trace is a function from T into C, where C is the set of all commands • A transduction is a function from percept traces into command traces that's causal: the com ...
... • Let T be the set of time points • A percept trace is a function from T into P, where P is the set of all possible percepts • A command trace is a function from T into C, where C is the set of all commands • A transduction is a function from percept traces into command traces that's causal: the com ...
CSCE 330 Programming Language Structures
... • Let T be the set of time points • A percept trace is a function from T into P, where P is the set of all possible percepts • A command trace is a function from T into C, where C is the set of all commands • A transduction is a function from percept traces into command traces that's causal: the com ...
... • Let T be the set of time points • A percept trace is a function from T into P, where P is the set of all possible percepts • A command trace is a function from T into C, where C is the set of all commands • A transduction is a function from percept traces into command traces that's causal: the com ...
Agent Architectures and Hierarchical Control, covering
... reaction time needed to avoid obstacles. • The output of the perception depends on what you will do with it UNIVERSITY OF SOUTH CAROLINA ...
... reaction time needed to avoid obstacles. • The output of the perception depends on what you will do with it UNIVERSITY OF SOUTH CAROLINA ...
Agent Architectures and Hierarchical Control, covering chapter 2 of
... reaction time needed to avoid obstacles. • The output of the perception depends on what you will do with it UNIVERSITY OF SOUTH CAROLINA ...
... reaction time needed to avoid obstacles. • The output of the perception depends on what you will do with it UNIVERSITY OF SOUTH CAROLINA ...
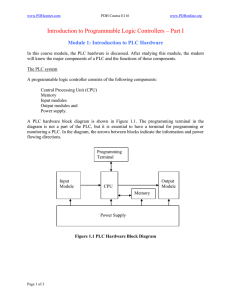
Introduction to PLC Hardware
... Performing logic and arithmetic operations. A CPU conducts all the mathematic and logic operations involved in a PLC. ...
... Performing logic and arithmetic operations. A CPU conducts all the mathematic and logic operations involved in a PLC. ...
MACH3 Interface Specification - Pennybuying Offical Blog | The
... analog quantity control, it is not suitable for MACH3. 5. The connection to the limit switch, tool detection and origin switch These switches shall be controlled by any one of the 5 input ports of MACH3 interface board. And they can be made by all kinds of the mechanical switches. Otherwise, they ca ...
... analog quantity control, it is not suitable for MACH3. 5. The connection to the limit switch, tool detection and origin switch These switches shall be controlled by any one of the 5 input ports of MACH3 interface board. And they can be made by all kinds of the mechanical switches. Otherwise, they ca ...
download
... XEN-5320-Burst v3.0.exe (and 2 supporting files) If you have done the first 3 files already for other LabView software, these can be skipped. You only need to place the Burst LabView program somewhere on your PC and start it. The first two programs have to be installed, and the computer has to be ...
... XEN-5320-Burst v3.0.exe (and 2 supporting files) If you have done the first 3 files already for other LabView software, these can be skipped. You only need to place the Burst LabView program somewhere on your PC and start it. The first two programs have to be installed, and the computer has to be ...
Slide 1
... Distribution of injected hard-faults that manifest as architectural across latencies Thus, a faultystate core mismatches cannot be trusted todifferent provide correct o Based on number of committed instructions before mismatch functionality even for short periods of program execution. happening when ...
... Distribution of injected hard-faults that manifest as architectural across latencies Thus, a faultystate core mismatches cannot be trusted todifferent provide correct o Based on number of committed instructions before mismatch functionality even for short periods of program execution. happening when ...
appendix f - Federal Judicial Center
... The first step in drafting a warrant to search and seize computers or computer data is to describe the property to be seized for the warrant itself. This requires a particularized description of the evidence, contraband, fruits, or instrumentality of crime that the agents hope to obtain by conductin ...
... The first step in drafting a warrant to search and seize computers or computer data is to describe the property to be seized for the warrant itself. This requires a particularized description of the evidence, contraband, fruits, or instrumentality of crime that the agents hope to obtain by conductin ...
The Analytical Engine
... complete documentation. After 1975, on the other hand, software development for microcomputers aroused considerable public interest, and several books-notably Doug Carlston's Software Peoplewere written about the founders and activities of micro software companies. The years in between are a largely ...
... complete documentation. After 1975, on the other hand, software development for microcomputers aroused considerable public interest, and several books-notably Doug Carlston's Software Peoplewere written about the founders and activities of micro software companies. The years in between are a largely ...
Computer program

A computer program or app is a sequence of instructions, written to perform a specified task on a computer. A computer requires programs to function, typically executing the program's instructions in a central processor. The program has an executable form that the computer can use directly to execute the instructions. The same program in its human-readable source code form, from which executable programs are derived (e.g., compiled), enables a programmer to study and develop its algorithms. A collection of computer programs and related data is referred to as the software.Computer source code is typically written by computer programmers. Source code is written in a programming language that usually follows one of two main paradigms: imperative or declarative programming. Source code may be converted into an executable file (sometimes called an executable program or a binary) by a compiler and later executed by a central processing unit. Alternatively, computer programs may be executed with the aid of an interpreter, or may be embedded directly into hardware.Computer programs may be ranked along functional lines: system software and application software. Two or more computer programs may run simultaneously on one computer from the perspective of the user, this process being known as multitasking.A computer program can be deemed an industrial or commercial product when that is useful for the concerns of a business model, which involves such aspects as labor, markets, profitability, and quality-control. This is how most proprietary software is classified, though open-source software can also be regarded as a product if a commercial entity specializes in it; e.g. Red Hat, Inc. or SUSE, as both which develop and maintain open-source software products.