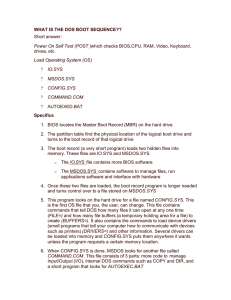
WHAT IS THE DOS BOOT SEQUENCE??
... Manager (Smss.exe). It will run the programs listed in its BootExecute Registry entry, as well as starting the required subsystems. The Win32 subsystem will then start Winlogon.exe, which starts the Local Security Administration (Lsass.exe), and the Ctrl+Alt+Delete window appears. The Service Contro ...
... Manager (Smss.exe). It will run the programs listed in its BootExecute Registry entry, as well as starting the required subsystems. The Win32 subsystem will then start Winlogon.exe, which starts the Local Security Administration (Lsass.exe), and the Ctrl+Alt+Delete window appears. The Service Contro ...
Chapter 10 File System Interface
... 5) Delete – from the OpSys perspective, remove file and all of its contents from device on which it is stored. Also removes directory entry on device. On some OpSys, e.g. UNIX., processes do not delete files; they remove the names of the files from the parent directory and nothing more. When a f ...
... 5) Delete – from the OpSys perspective, remove file and all of its contents from device on which it is stored. Also removes directory entry on device. On some OpSys, e.g. UNIX., processes do not delete files; they remove the names of the files from the parent directory and nothing more. When a f ...
OPERATINGSYSTEMS 2015
... WHAT IS THE COURSE ABOUT ? Operating system (OS) is the most important type of system software in a computer system. Without an operating system, a user cannot run an application program on their computer. Operating systems are found on almost any device that contains a computer – from cellular phon ...
... WHAT IS THE COURSE ABOUT ? Operating system (OS) is the most important type of system software in a computer system. Without an operating system, a user cannot run an application program on their computer. Operating systems are found on almost any device that contains a computer – from cellular phon ...
1.01 - Kau
... System Calls Programming interface to the services provided by the OS Typically written in a high-level language (C or C++) Mostly accessed by programs via a high-level Application Program Interface ...
... System Calls Programming interface to the services provided by the OS Typically written in a high-level language (C or C++) Mostly accessed by programs via a high-level Application Program Interface ...
Introduction to Programming Methodology Notes
... place, a bank account, a table of data or any item that the program has to handle. They may also represent user-defined data such as vectors, time and lists. Programming problem is analyzed in terms of objects and the nature of communication between them. Program objects should be chosen such that t ...
... place, a bank account, a table of data or any item that the program has to handle. They may also represent user-defined data such as vectors, time and lists. Programming problem is analyzed in terms of objects and the nature of communication between them. Program objects should be chosen such that t ...
Chapter 2
... a shared memory area used for passing information between different components of the spacecraft. ran frequently with high priority to move certain kinds of data in and out of the information bus. Access to the bus ...
... a shared memory area used for passing information between different components of the spacecraft. ran frequently with high priority to move certain kinds of data in and out of the information bus. Access to the bus ...
Delimited continuations in operating systems
... operating-system research, continuations are poorly known and seldom used explicitly. In this paper, we cross the boundary between operating systems and programming languages to argue by examples that continuations, especially delimited ones, pervade operating systems—if only implicitly. We contend ...
... operating-system research, continuations are poorly known and seldom used explicitly. In this paper, we cross the boundary between operating systems and programming languages to argue by examples that continuations, especially delimited ones, pervade operating systems—if only implicitly. We contend ...
rtos-concepts
... 1) It sorts the tasks from the shortest period to the longest period. Then it defines the critical set as the first N tasks such that the total CPU load factor does not exceed 100%. These tasks are guaranteed not to fail even during a transient ...
... 1) It sorts the tasks from the shortest period to the longest period. Then it defines the critical set as the first N tasks such that the total CPU load factor does not exceed 100%. These tasks are guaranteed not to fail even during a transient ...
No Slide Title
... existing one, by receiving a duplicated handle from another process, or by inheriting a handle from a parent process Each object is protected by an access control list ...
... existing one, by receiving a duplicated handle from another process, or by inheriting a handle from a parent process Each object is protected by an access control list ...
Operating Systems
... Blocking - process suspended until I/O completed – Easy to use and understand – Insufficient for some needs Nonblocking - I/O call returns as much as available – E.g., User interface that received keyboard input while processing and displaying data on the screen – One approach: Implemented via multi ...
... Blocking - process suspended until I/O completed – Easy to use and understand – Insufficient for some needs Nonblocking - I/O call returns as much as available – E.g., User interface that received keyboard input while processing and displaying data on the screen – One approach: Implemented via multi ...
Operating-System Structures
... A process is a program in execution. It is the unit of work in a system. It can be running a program or job (e.g., word-processing program, compiler program, sending output to a printer, simulation program) System consists of a collection of processes related to OS and user A process needs r ...
... A process is a program in execution. It is the unit of work in a system. It can be running a program or job (e.g., word-processing program, compiler program, sending output to a printer, simulation program) System consists of a collection of processes related to OS and user A process needs r ...
Embedding Object Files in an Existing Operating System: A Practical Approach
... specialization and code reuse. It is developed following the methodology as project progressed, adopting many useful ideas from the Object-Oriented programming and software engineering research communities. Choices supports an Object-Oriented API based on encapsulation, inheritance and polymorphism. ...
... specialization and code reuse. It is developed following the methodology as project progressed, adopting many useful ideas from the Object-Oriented programming and software engineering research communities. Choices supports an Object-Oriented API based on encapsulation, inheritance and polymorphism. ...
File System Management
... The file system is used not only to store users’ programs and data, but also to support and represent significant portions of the operating system itself. Stallings introduces the traditional file system concepts of: fields represent the smallest logical item of data “understood” by a file-system: e ...
... The file system is used not only to store users’ programs and data, but also to support and represent significant portions of the operating system itself. Stallings introduces the traditional file system concepts of: fields represent the smallest logical item of data “understood” by a file-system: e ...
Operating Systems and File Management
... 042200 Today’s popular operating systems include Windows, Mac OS, Linux, Android, and iOS. Each has strengths and weaknesses that are important to understand. Which of the following statements is correct? A. iOS is built on the Windows kernel, so it is ideal for smartphones because it has good r ...
... 042200 Today’s popular operating systems include Windows, Mac OS, Linux, Android, and iOS. Each has strengths and weaknesses that are important to understand. Which of the following statements is correct? A. iOS is built on the Windows kernel, so it is ideal for smartphones because it has good r ...
Slide 1
... that are important to understand. Which of the following statements is correct? A. iOS is built on the Windows kernel, so it is ideal for smartphones because it has good resistance to malware. B. If you don’t like the user interface for Windows but want to run the vast variety of Windows softwar ...
... that are important to understand. Which of the following statements is correct? A. iOS is built on the Windows kernel, so it is ideal for smartphones because it has good resistance to malware. B. If you don’t like the user interface for Windows but want to run the vast variety of Windows softwar ...
Towards Protecting Sensitive Files in a Compromised System
... on these files. The trails of many intrusions can also be discovered from the system logs, if the log file is protected from being scrubbed. However, protecting sensitive files in a compromised system is not easy. Most existing file protection mechanisms reside in the same space as the victim OS. If ...
... on these files. The trails of many intrusions can also be discovered from the system logs, if the log file is protected from being scrubbed. However, protecting sensitive files in a compromised system is not easy. Most existing file protection mechanisms reside in the same space as the victim OS. If ...
Week-2
... Group identifier (group ID) allows set of users to be defined and controls managed, then also associated with each process, file Privilege escalation allows user to change to effective ID with ...
... Group identifier (group ID) allows set of users to be defined and controls managed, then also associated with each process, file Privilege escalation allows user to change to effective ID with ...
Operating Systems
... provides a virtual machine: – share CPU (in time) and provide each app with a virtual processor, – allocate and protect memory, and provide applications with their own virtual address space, – present a set of (relatively) hardware independent virtual devices, – divide up storage space by using fili ...
... provides a virtual machine: – share CPU (in time) and provide each app with a virtual processor, – allocate and protect memory, and provide applications with their own virtual address space, – present a set of (relatively) hardware independent virtual devices, – divide up storage space by using fili ...
Slide 1
... Answer A for True and B for False 041200 A file specification is also called a path. 041300 Windows Explorer is a file management utility. 041400 Disks are formatted into tracks and sectors. 041500 Time Machine is synchronization software used for backup on Macs. 041600 To repopulate a new ...
... Answer A for True and B for False 041200 A file specification is also called a path. 041300 Windows Explorer is a file management utility. 041400 Disks are formatted into tracks and sectors. 041500 Time Machine is synchronization software used for backup on Macs. 041600 To repopulate a new ...
Introduction
... LINUX is a free UNIX-type operating system originally created by Linus Torlvads with the assistance of developers around the world. The source code for Linux is freely available to everyone. The commands of linux are similar to unix. ...
... LINUX is a free UNIX-type operating system originally created by Linus Torlvads with the assistance of developers around the world. The source code for Linux is freely available to everyone. The commands of linux are similar to unix. ...
REF Chapter 3: Windows NT System Specifics
... and its components. Screen mode is not available. Therefore, these modules, which on other operating systems have both a screen and a statement mode, are supported in BASIS on Windows in statement mode only: DMDBA, Thesaurus Manager, and FQM. And these modules, which use screen mode exclusively, are ...
... and its components. Screen mode is not available. Therefore, these modules, which on other operating systems have both a screen and a statement mode, are supported in BASIS on Windows in statement mode only: DMDBA, Thesaurus Manager, and FQM. And these modules, which use screen mode exclusively, are ...
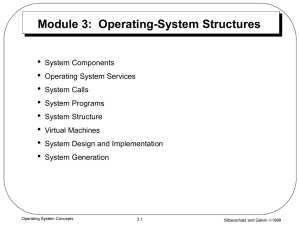
Module 3: Operating
... The program that reads and interprets control statements is called variously: – control-card interpreter – command-line interpreter – shell (in UNIX) Its function is to get and execute the next command statement. ...
... The program that reads and interprets control statements is called variously: – control-card interpreter – command-line interpreter – shell (in UNIX) Its function is to get and execute the next command statement. ...
OS 2200

OS 2200 is the operating system for the Unisys ClearPath Dorado family of mainframe systems. The operating system kernel of OS 2200 is a lineal descendant of Exec 8 for the UNIVAC 1108. Documentation and other information on current and past Unisys systems can be found on the Unisys public support website.See Unisys 2200 Series system architecture for a description of the machine architecture and its relationship to the OS 2200 operating system.