Computer System Arch..
... • Overlays - Keep in memory only those instructions and data that are needed at any given time • Swapping - A process can be swapped temporarily out of memory to a backing store and then brought back into memory for continued execution ...
... • Overlays - Keep in memory only those instructions and data that are needed at any given time • Swapping - A process can be swapped temporarily out of memory to a backing store and then brought back into memory for continued execution ...
PPT - CS
... The main OS file tables • The i-node table - each file may appear at most once in this table. • The open files table – an entry in this table is allocated every time a file is opened. Each entry contains a pointer to the inode table and a position within the file. There can be multiple open file en ...
... The main OS file tables • The i-node table - each file may appear at most once in this table. • The open files table – an entry in this table is allocated every time a file is opened. Each entry contains a pointer to the inode table and a position within the file. There can be multiple open file en ...
Introduction to Operating System
... Operating System: Network operating system Allows users to share printer, Internet access, files, and programs on a network Administers security by establishing user name and password for each user ...
... Operating System: Network operating system Allows users to share printer, Internet access, files, and programs on a network Administers security by establishing user name and password for each user ...
Implementing File Systems
... Some system uses contiguous allocation for small files and automatically switching to an index allocation if the file grows large ...
... Some system uses contiguous allocation for small files and automatically switching to an index allocation if the file grows large ...
LESSON PLAN PCCS4304 OPERATING SYSTEM (3-0-0)
... system be bounded from the retrieval of stored data to time that it takes the OS to finish the request. In soft real time system is a less restrictive one where a critical real time task gets priority over other tasks & retains the property until it completes. Soft real time system is achievable g ...
... system be bounded from the retrieval of stored data to time that it takes the OS to finish the request. In soft real time system is a less restrictive one where a critical real time task gets priority over other tasks & retains the property until it completes. Soft real time system is achievable g ...
Chapter 19 Real
... ◦ Time required to translate logical address to physical address especially in case of Translation Look aside Buffer(TLB) miss – may be prohibited in hard real time systems. ...
... ◦ Time required to translate logical address to physical address especially in case of Translation Look aside Buffer(TLB) miss – may be prohibited in hard real time systems. ...
CS540_Ch19
... ◦ Time required to translate logical address to physical address especially in case of Translation Look aside Buffer(TLB) miss – may be prohibited in hard real time systems. ...
... ◦ Time required to translate logical address to physical address especially in case of Translation Look aside Buffer(TLB) miss – may be prohibited in hard real time systems. ...
Slide Set 7
... The position value in an fsetpos must have been obtained in a previous fgetpos call. ...
... The position value in an fsetpos must have been obtained in a previous fgetpos call. ...
Discovering Computers Fundamentals 3rd Edition
... What are other program management features of operating systems? multiprocessing Can support two or more processors running programs at same time ...
... What are other program management features of operating systems? multiprocessing Can support two or more processors running programs at same time ...
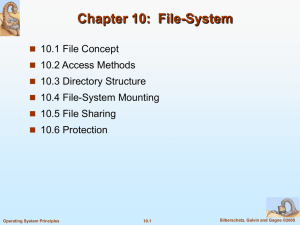
File-System
... File Locking Example – Java API (cont) // this locks the second half of the file - shared sharedLock = ch.lock(raf.length()/2+1, raf.length(), SHARED); /** Now read the data . . . */ // release the lock ...
... File Locking Example – Java API (cont) // this locks the second half of the file - shared sharedLock = ch.lock(raf.length()/2+1, raf.length(), SHARED); /** Now read the data . . . */ // release the lock ...
Chapter 4
... picture” of the files on your computer. Although file management utilities vary from one operating system to another, they rely on the same basic principles. Use Figure 4-36 to compare the Windows and Mac OS file management utilities. As students become familiar with the concepts of device letters a ...
... picture” of the files on your computer. Although file management utilities vary from one operating system to another, they rely on the same basic principles. Use Figure 4-36 to compare the Windows and Mac OS file management utilities. As students become familiar with the concepts of device letters a ...
Unix Intro PowerPoint
... Microsoft DOS and Microsoft Windows adopted original UNIX design concepts, such as the idea of a shell--an interface between the user and the operating system--and the hierarchical structure of directories and subdirectories The kernel is the base operating system, which interacts directly with ...
... Microsoft DOS and Microsoft Windows adopted original UNIX design concepts, such as the idea of a shell--an interface between the user and the operating system--and the hierarchical structure of directories and subdirectories The kernel is the base operating system, which interacts directly with ...
Powerpoint format - Computer and Information Sciences
... swap out a thread while the other thread is still running on a different processor • In short-term scheduling (pick and dispatch), the overly complicated scheduling schemes may not be necessary ...
... swap out a thread while the other thread is still running on a different processor • In short-term scheduling (pick and dispatch), the overly complicated scheduling schemes may not be necessary ...
Towards High-Performance Application-Level Storage
... traditional slow data path to storage is made even worse by the widespread deployment of virtual machines, since both the hypervisor and the guest operating systems must be traversed on every operation. SR-IOV and the IOMMU make it possible to bypass the hypervisor to deliver I/O events directly to ...
... traditional slow data path to storage is made even worse by the widespread deployment of virtual machines, since both the hypervisor and the guest operating systems must be traversed on every operation. SR-IOV and the IOMMU make it possible to bypass the hypervisor to deliver I/O events directly to ...
ppt - Stanford Crypto group
... – System extension via dynamically loaded kernel modules • Environment Variables – System variables such as LIBPATH that are shared state across applications. An attacker can change LIBPATH to load an attackerprovided file as a dynamic library ...
... – System extension via dynamically loaded kernel modules • Environment Variables – System variables such as LIBPATH that are shared state across applications. An attacker can change LIBPATH to load an attackerprovided file as a dynamic library ...
3. Operating Systems - Informática Ingeniería en Electrónica y
... a virtual or extended machine with a much simpler use. It hides fine working details the user does not need to know (e.g. how to manage the read/write head of a magnetic disc) It provides an extra set of instructions, the System Calls They can be used by other programs or by the programmer working ...
... a virtual or extended machine with a much simpler use. It hides fine working details the user does not need to know (e.g. how to manage the read/write head of a magnetic disc) It provides an extra set of instructions, the System Calls They can be used by other programs or by the programmer working ...
Fundamental Concepts of Operating Systems
... Fundamental Concepts of Operating Systems Prof. Lixin Tao Pace University December 4, 2002 Chapter 1: Introduction ...
... Fundamental Concepts of Operating Systems Prof. Lixin Tao Pace University December 4, 2002 Chapter 1: Introduction ...
ppt
... • Basic scheduling unit is a thread • Priority based scheduling per thread • Preemptive operating system • No shortest job first, no quotas ...
... • Basic scheduling unit is a thread • Priority based scheduling per thread • Preemptive operating system • No shortest job first, no quotas ...
AppGuard - UTSA CS
... component in the guest kernel; 3) AppGuard directly traps the events that need to be intercepted without going through the guest kernel as in AppShield, thus not relying on any trusted components of the guest OS. This makes AppGuard backward compatiable. Secure processor based protection. A secure p ...
... component in the guest kernel; 3) AppGuard directly traps the events that need to be intercepted without going through the guest kernel as in AppShield, thus not relying on any trusted components of the guest OS. This makes AppGuard backward compatiable. Secure processor based protection. A secure p ...
Operating Systems and File Management
... Boot and Recovery Disks • You can create a custom recovery CD that contains your computer’s current settings and device drivers • Norton Ghost is a product of Symantec, which also provides a more specialized recovery disk called the Symantec Recovery Disk • Certain PC manufacturers have pre-install ...
... Boot and Recovery Disks • You can create a custom recovery CD that contains your computer’s current settings and device drivers • Norton Ghost is a product of Symantec, which also provides a more specialized recovery disk called the Symantec Recovery Disk • Certain PC manufacturers have pre-install ...
OS 2200

OS 2200 is the operating system for the Unisys ClearPath Dorado family of mainframe systems. The operating system kernel of OS 2200 is a lineal descendant of Exec 8 for the UNIVAC 1108. Documentation and other information on current and past Unisys systems can be found on the Unisys public support website.See Unisys 2200 Series system architecture for a description of the machine architecture and its relationship to the OS 2200 operating system.