Empirical Performance Assessment Using Soft-Core Processors on Reconfigurable Hardware
... instrumentation of such descriptions, and the addition of logic to log events reliably, execution details at the microarchitectural level can be captured at full (FPGA) speed for an application’s entire execution [11]. While much of a program’s observed behavior is intrinsic to the application and i ...
... instrumentation of such descriptions, and the addition of logic to log events reliably, execution details at the microarchitectural level can be captured at full (FPGA) speed for an application’s entire execution [11]. While much of a program’s observed behavior is intrinsic to the application and i ...
Bringing Virtualization to the x86 Architecture with the Original
... virtualization support, and the industry around it had disaggregated into an ecosystem, with different vendors controlling the computers, CPUs, peripherals, operating systems, and applications, none of them asking for virtualization. We chose to build our solution independently of these vendors. As ...
... virtualization support, and the industry around it had disaggregated into an ecosystem, with different vendors controlling the computers, CPUs, peripherals, operating systems, and applications, none of them asking for virtualization. We chose to build our solution independently of these vendors. As ...
Bringing Virtualization to the x86 Architecture with
... virtualization support, and the industry around it had disaggregated into an ecosystem, with different vendors controlling the computers, CPUs, peripherals, operating systems, and applications, none of them asking for virtualization. We chose to build our solution independently of these vendors. As ...
... virtualization support, and the industry around it had disaggregated into an ecosystem, with different vendors controlling the computers, CPUs, peripherals, operating systems, and applications, none of them asking for virtualization. We chose to build our solution independently of these vendors. As ...
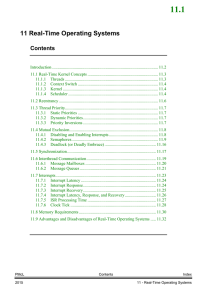
a. Real Time Operating Systems Notes
... Application code using a preemptive kernel should not use non-reentrant functions, unless exclusive access to these functions is ensured through the use of mutual exclusion semaphores, because both a low- and a high-priority thread can use a common function. Corruption of data may occur if the highe ...
... Application code using a preemptive kernel should not use non-reentrant functions, unless exclusive access to these functions is ensured through the use of mutual exclusion semaphores, because both a low- and a high-priority thread can use a common function. Corruption of data may occur if the highe ...
Operating System Concepts
... Convenient for the user! Efficient operation of the computer system! ...
... Convenient for the user! Efficient operation of the computer system! ...
PPT
... Stack (for function calls and temporary variables) 5. Program counter (current instruction) 6. CPU registers 7. Open files table (including sockets) To better distinguish between a program and a process, note that a single Word processor program may have 10 different processes running simultaneous ...
... Stack (for function calls and temporary variables) 5. Program counter (current instruction) 6. CPU registers 7. Open files table (including sockets) To better distinguish between a program and a process, note that a single Word processor program may have 10 different processes running simultaneous ...
1.01 - BRAUDE
... Stack (for function calls and temporary variables) 5. Program counter (current instruction) 6. CPU registers 7. Open files table (including sockets) To better distinguish between a program and a process, note that a single Word processor program may have 10 different processes running simultaneous ...
... Stack (for function calls and temporary variables) 5. Program counter (current instruction) 6. CPU registers 7. Open files table (including sockets) To better distinguish between a program and a process, note that a single Word processor program may have 10 different processes running simultaneous ...
Thread Scheduling - EECG Toronto
... (in kernel), kernel switches user threads (associated with the to another thread corresponding kernel thread) block, so overlap of I/O and computation is not possible ...
... (in kernel), kernel switches user threads (associated with the to another thread corresponding kernel thread) block, so overlap of I/O and computation is not possible ...
Operating system hardware reconfiguration
... change occurs when most if not all of the hardware is no longer the same. This will happen, for example, if the operating system is migrated to a new system. Through empirical experimentation it has been determined that most (if not all) modern Linux-based operating systems can successfully undergo ...
... change occurs when most if not all of the hardware is no longer the same. This will happen, for example, if the operating system is migrated to a new system. Through empirical experimentation it has been determined that most (if not all) modern Linux-based operating systems can successfully undergo ...
Dancing with Giants: Wimpy Kernels for On-demand Isolated I/O
... and complexity of trusted code and undermines assurance. For example, including only the Linux USB bus subsystem in the XMHF micro-hypervisor[66] would more than double its code-base size and increase its complexity significantly; e.g., it would introduce concurrency in serial micro-hypervisor code ...
... and complexity of trusted code and undermines assurance. For example, including only the Linux USB bus subsystem in the XMHF micro-hypervisor[66] would more than double its code-base size and increase its complexity significantly; e.g., it would introduce concurrency in serial micro-hypervisor code ...
Operating System - GH Raisoni College Of Engineering Nagpur
... 9) Explain segmentation memory management techniques? 10) Explain demand paged memory management techniques? 11) Explain segmentation with paging memory management techniques? 12) Explain virtual memory management techniques? 13) Explain following memory allocation strategies with example A)First- f ...
... 9) Explain segmentation memory management techniques? 10) Explain demand paged memory management techniques? 11) Explain segmentation with paging memory management techniques? 12) Explain virtual memory management techniques? 13) Explain following memory allocation strategies with example A)First- f ...
using complete machine simulation to understand computer system
... hardware typically found in a computer system. As a result, it can boot, run, and investigate the behavior of machines running a fully functional operating system as well as any application designed to run on this operating system. This includes database management systems, web servers, and other op ...
... hardware typically found in a computer system. As a result, it can boot, run, and investigate the behavior of machines running a fully functional operating system as well as any application designed to run on this operating system. This includes database management systems, web servers, and other op ...
Operating Systems Concepts with Java
... • I/O systems: Chapters 13 and 14 describe the devices that attach to a computer and the multiple dimensions on which they vary. Because these devices differ so widely, the operating system needs to provide a wide range of functionality to applications to allow them to control all aspects of the de ...
... • I/O systems: Chapters 13 and 14 describe the devices that attach to a computer and the multiple dimensions on which they vary. Because these devices differ so widely, the operating system needs to provide a wide range of functionality to applications to allow them to control all aspects of the de ...
The Architecture of a Worldwide Distributed System
... period of learning as much as you can in as many different subjects that are interesting. In this respect I took full advantage of my Ph.D.: I did work ranging from programming my own EEPROMs, to secure network objects, digital video on demand, and a full blown new operating system with its own TCP/ ...
... period of learning as much as you can in as many different subjects that are interesting. In this respect I took full advantage of my Ph.D.: I did work ranging from programming my own EEPROMs, to secure network objects, digital video on demand, and a full blown new operating system with its own TCP/ ...
NonStop System Glossary
... Confidential computer software. Valid license from HP required for possession, use or copying. Consistent with FAR 12.211 and 12.212, Commercial Computer Software, Computer Software Documentation, and Technical Data for Commercial Items are licensed to the U.S. Government under vendor’s standard com ...
... Confidential computer software. Valid license from HP required for possession, use or copying. Consistent with FAR 12.211 and 12.212, Commercial Computer Software, Computer Software Documentation, and Technical Data for Commercial Items are licensed to the U.S. Government under vendor’s standard com ...
A Virtual Machine Introspection Based Architecture for Intrusion
... exploitable bugs in the OS, a serious problem in our world of complex operating systems written in unsafe languages, where new buffer overflows are discovered with disturbing frequency. In a host-based IDS, an IDS crash will generally cause the system to fail open. In a user-level IDS it is impossib ...
... exploitable bugs in the OS, a serious problem in our world of complex operating systems written in unsafe languages, where new buffer overflows are discovered with disturbing frequency. In a host-based IDS, an IDS crash will generally cause the system to fail open. In a user-level IDS it is impossib ...
Course ”Operating System Security”
... Thomaon Course Technology, 2004 Discussion based not on concepts, but more on administrative security measures in some operating systems ...
... Thomaon Course Technology, 2004 Discussion based not on concepts, but more on administrative security measures in some operating systems ...
Systematic setup of compartmentalised systems on the seL4
... compartment communications. The microkernel does not control buses and I/O devices of the system. They are controlled by bus managers and user level device drivers. The system architecture grants those compartments access to their hardware and connects them to client applications that require servic ...
... compartment communications. The microkernel does not control buses and I/O devices of the system. They are controlled by bus managers and user level device drivers. The system architecture grants those compartments access to their hardware and connects them to client applications that require servic ...
Linux - PUC-Rio
... processes and threads; a thread is simply a new process that happens to share the same address space as its parent A distinction is only made when a new thread is created by the clone system call ...
... processes and threads; a thread is simply a new process that happens to share the same address space as its parent A distinction is only made when a new thread is created by the clone system call ...
SGG - UTSA CS
... A bound must exist on the number of times that other processes are allowed to enter their critical sections after a process has made a request to enter its critical section and before that request is granted. ...
... A bound must exist on the number of times that other processes are allowed to enter their critical sections after a process has made a request to enter its critical section and before that request is granted. ...
Linux+ Guide to Linux Certification Chapter Nine System Initialization
... Using FIPS • Guidelines/limitations to using FIPS: – Version 2.0 of FIPS supports the FAT16 and FAT32 filesystems only – FIPS will only work with primary Windows partition and will not resize logical drives within extended partitions – FIPS works by splitting the Windows partition into two primary ...
... Using FIPS • Guidelines/limitations to using FIPS: – Version 2.0 of FIPS supports the FAT16 and FAT32 filesystems only – FIPS will only work with primary Windows partition and will not resize logical drives within extended partitions – FIPS works by splitting the Windows partition into two primary ...
Virtual Machine Monitors Dr. Marc E. Fiuczynski Research Scholar Princeton University
... Guest OS is responsible for allocating and managing hardware page table Xen involvement is limited to ensure safety and isolation Xen exists in the top 64 MB section at the top of every address space to avoid TLB flushes when entering and leaving the VMM ...
... Guest OS is responsible for allocating and managing hardware page table Xen involvement is limited to ensure safety and isolation Xen exists in the top 64 MB section at the top of every address space to avoid TLB flushes when entering and leaving the VMM ...
Eliminating Receive Livelock in an Interrupt-Driven Kernel
... hundred times per second. Polling can also increase the latency of response to an event. Modern systems can respond to an interrupt in a few tens of microseconds; to achieve the same latency using polling, the system would have to poll tens of thousands of times per second, which would create excess ...
... hundred times per second. Polling can also increase the latency of response to an event. Modern systems can respond to an interrupt in a few tens of microseconds; to achieve the same latency using polling, the system would have to poll tens of thousands of times per second, which would create excess ...
OS3e_04
... – Occurs when the operating system calls a user-level threading library that determines if any of its threads need rescheduling ...
... – Occurs when the operating system calls a user-level threading library that determines if any of its threads need rescheduling ...
Quick UNIX Tutorial
... Access rights on directories. r: allows users to list files in the directory; w: means that users may delete files from the directory or move files into it. Never give write permission to others to your home directory or any of its subdirectories. x: means the right to access files in the d ...
... Access rights on directories. r: allows users to list files in the directory; w: means that users may delete files from the directory or move files into it. Never give write permission to others to your home directory or any of its subdirectories. x: means the right to access files in the d ...