Week 7 - Software Tools
... collector to reclaim unused memory " Other languages (e.g., C, C++) require programmers to manage their own memory ...
... collector to reclaim unused memory " Other languages (e.g., C, C++) require programmers to manage their own memory ...
投影片 1
... embedded systems as well as in ordinary PC systems. In multi-core embedded processors, however, a processor may consist of heterogeneous CPU cores that are not configured with a shared memory and do not have a communication mechanism for inter-core communication. MCAPI is a highly portable API stand ...
... embedded systems as well as in ordinary PC systems. In multi-core embedded processors, however, a processor may consist of heterogeneous CPU cores that are not configured with a shared memory and do not have a communication mechanism for inter-core communication. MCAPI is a highly portable API stand ...
Furman - Languages Slides
... • Executable statements that occur when leaving a scope • Difference statements occur based on successful, failure, or abnormal exits out of the scope • Useful in conjunction with error handling ...
... • Executable statements that occur when leaving a scope • Difference statements occur based on successful, failure, or abnormal exits out of the scope • Useful in conjunction with error handling ...
answer sheet - B.S. Abdur Rahman University
... b. A busy-wait loop is easier to code than an interrupt handler. c. There is no other work for the processor to do. d. The task must meet some hard real-time deadlines. e. The program executes on a time-sharing system. 20. The problem of fragmentation arises in a. static storage Allocation b. stack ...
... b. A busy-wait loop is easier to code than an interrupt handler. c. There is no other work for the processor to do. d. The task must meet some hard real-time deadlines. e. The program executes on a time-sharing system. 20. The problem of fragmentation arises in a. static storage Allocation b. stack ...
ppt
... Certain bugs like buffer overflows may be avoided by use of a type-safe language or use of boundschecking libraries Another class of security bugs involve misuse of higher level semantics ...
... Certain bugs like buffer overflows may be avoided by use of a type-safe language or use of boundschecking libraries Another class of security bugs involve misuse of higher level semantics ...
Linux kernel security enhancements
... Plain vanilla Linux kernel and system is very vulnerable compared to specialized router operating systems because of the basic Unix kernel security features. Linux kernel has no encryption support for securing communications or data in plain vanilla kernel (at least yet) Thus there is a need for har ...
... Plain vanilla Linux kernel and system is very vulnerable compared to specialized router operating systems because of the basic Unix kernel security features. Linux kernel has no encryption support for securing communications or data in plain vanilla kernel (at least yet) Thus there is a need for har ...
Presentation3
... parallelism of the NPU, They do not know how to exploit it at best – New (proprietary) languages – Portability among different network processors families ...
... parallelism of the NPU, They do not know how to exploit it at best – New (proprietary) languages – Portability among different network processors families ...
JavaIO
... operating system “I will never write anything to this stream ever again” and the operating system can reclaim any resources associated with the stream ...
... operating system “I will never write anything to this stream ever again” and the operating system can reclaim any resources associated with the stream ...
Searching with Privacy: a survey
... k-bit string to the message The sum of two or more such strings will be another such string with negligible probability in k Specifically, partition k bits into triples of bits, and set exactly one bit from each triple to 1 ...
... k-bit string to the message The sum of two or more such strings will be another such string with negligible probability in k Specifically, partition k bits into triples of bits, and set exactly one bit from each triple to 1 ...
Lecture 19
... You’re responsible for saving any variables that are shared by the original program and the interrupt routine. You should then restore these values before you return from the interrupt. But check whether the compiler takes care of this… ...
... You’re responsible for saving any variables that are shared by the original program and the interrupt routine. You should then restore these values before you return from the interrupt. But check whether the compiler takes care of this… ...
lecture1 2016 - UWC Computer Science
... Index Registers • SI Source Index used by string operations as source • DI Destination Index used by string operations as destination ...
... Index Registers • SI Source Index used by string operations as source • DI Destination Index used by string operations as destination ...
lecture1 v2 - UWC Computer Science
... Index Registers • SI Source Index used by string operations as source • DI Destination Index used by string operations as destination ...
... Index Registers • SI Source Index used by string operations as source • DI Destination Index used by string operations as destination ...
Hands-On Ethical Hacking and Network Security
... Configure OS to not allow code in the stack to run any other executable code in the stack Some compilers like gcc warn programmers when dangerous functions are used ...
... Configure OS to not allow code in the stack to run any other executable code in the stack Some compilers like gcc warn programmers when dangerous functions are used ...
Assembly Programming - University of the Western Cape
... – .model small : Lines that start with a "." are used to provide the assembler with information. The word(s) behind it say what kind of info. In this case it just tells the assembler the program is small and doesn't need a lot of memory. I'll get back on this later. – .stack : Another line with info ...
... – .model small : Lines that start with a "." are used to provide the assembler with information. The word(s) behind it say what kind of info. In this case it just tells the assembler the program is small and doesn't need a lot of memory. I'll get back on this later. – .stack : Another line with info ...
Optical Burst Switching.pdf
... buffer may be used when moving data between processes within a computer. This is comparable to buffers in telecommunication. Buffers can be implemented in either hardware or software, but the vast majority of buffers are implemented in software. Buffers are typically used when there is a difference ...
... buffer may be used when moving data between processes within a computer. This is comparable to buffers in telecommunication. Buffers can be implemented in either hardware or software, but the vast majority of buffers are implemented in software. Buffers are typically used when there is a difference ...
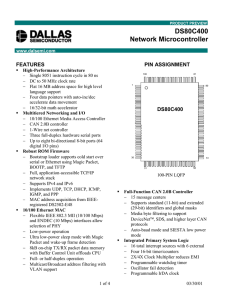
DS80C400-FCS - Maxim Integrated Products, Inc.
... times faster than the original for the same crystal speed. The DS80C400 supports a maximum crystal speed of 50 MHz, resulting in a minimum instruction cycle time of 80 ns. The DS80C400 utilizes an internal 24-bit program counter to achieve a flat 16MB address space, alleviating the bank switching me ...
... times faster than the original for the same crystal speed. The DS80C400 supports a maximum crystal speed of 50 MHz, resulting in a minimum instruction cycle time of 80 ns. The DS80C400 utilizes an internal 24-bit program counter to achieve a flat 16MB address space, alleviating the bank switching me ...
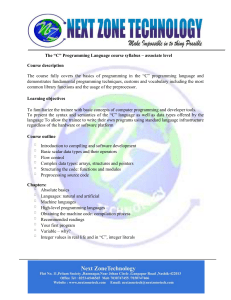
C Syllabus - Next Zone Technology
... Typecast and its operators Loops – while, do and for Controlling the loop execution – break and continue Logical and bitwise operators Arrays Switch: different faces of ‘if’ Arrays (vectors) – why do you need them? Sorting in real life and in a computer memory Initiators: a simple way to set an arra ...
... Typecast and its operators Loops – while, do and for Controlling the loop execution – break and continue Logical and bitwise operators Arrays Switch: different faces of ‘if’ Arrays (vectors) – why do you need them? Sorting in real life and in a computer memory Initiators: a simple way to set an arra ...
Poster - The University of Manchester
... receiver to slide a window (Cwnd) over the data to regulate the transmission rate. If a packet has been lost, TCP interprets this as congestion on the network, and the standard (New Reno) congestion avoidance algorithm decreases the window by half and then slowly increases it by one packet per round ...
... receiver to slide a window (Cwnd) over the data to regulate the transmission rate. If a packet has been lost, TCP interprets this as congestion on the network, and the standard (New Reno) congestion avoidance algorithm decreases the window by half and then slowly increases it by one packet per round ...
Scalable Parallel Computers
... Scalable computers • Almost all computers allow the capability of the systems to be increased – Add memory, add disk, upgrade processor, etc. ...
... Scalable computers • Almost all computers allow the capability of the systems to be increased – Add memory, add disk, upgrade processor, etc. ...
Security “Tidbits” - The Stanford University InfoLab
... Don’t shut down mail servers: did prevent worm from spreading but also shut down defense CERT was created to respond to attacks ...
... Don’t shut down mail servers: did prevent worm from spreading but also shut down defense CERT was created to respond to attacks ...
Lecture 09 - Software Tools
... " Dangling pointers # Memory has been freed, but part of the code is still trying to use it ...
... " Dangling pointers # Memory has been freed, but part of the code is still trying to use it ...
Network Security
... non-variable part of frame (MD5 hash) • Encapsulation Security Payload (ESP): Encrypts payload (DES) ...
... non-variable part of frame (MD5 hash) • Encapsulation Security Payload (ESP): Encrypts payload (DES) ...
Multicore, parallelism, and multithreading
... Takes operation specified in one instruction and applies it to more than 1 set of data elements at 1 time Suitable for graphics and image processing ...
... Takes operation specified in one instruction and applies it to more than 1 set of data elements at 1 time Suitable for graphics and image processing ...
PPT - CS
... – Mobile code security flaws (Java, ActiveX) • Knowledge spreads faster than remedy – Hacker bulletins – Advisories: • Flaws/fixes repositories, e.g., CERT • Publicly available software kits to detect known vulnerabilities, e.g., SATAN, ISS • But they are not always followed readily, and are often u ...
... – Mobile code security flaws (Java, ActiveX) • Knowledge spreads faster than remedy – Hacker bulletins – Advisories: • Flaws/fixes repositories, e.g., CERT • Publicly available software kits to detect known vulnerabilities, e.g., SATAN, ISS • But they are not always followed readily, and are often u ...